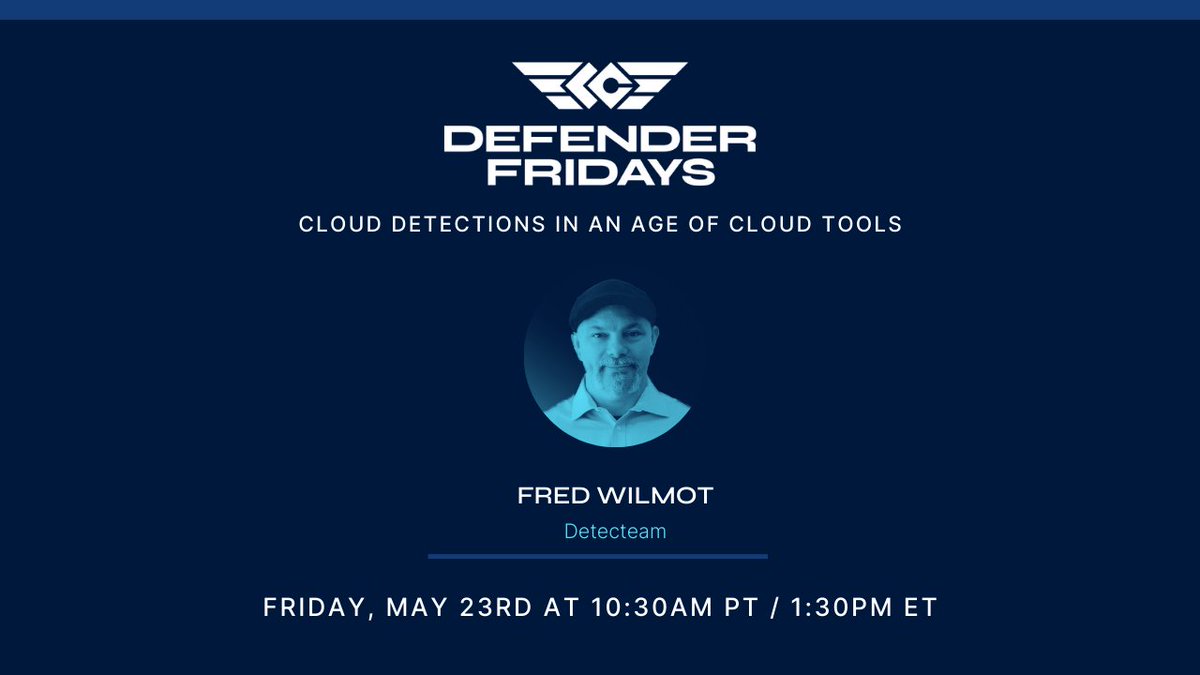
Fred Wilmot
1.6K posts
Fred Wilmot
@fewdisc
Co-founder Detecteam | product builder | practitioner | innovator | Dad | IT/OT apologist. my opinions - make it better


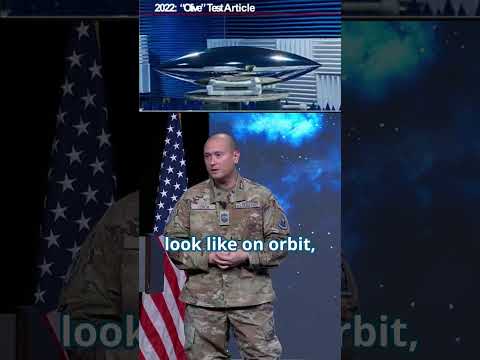
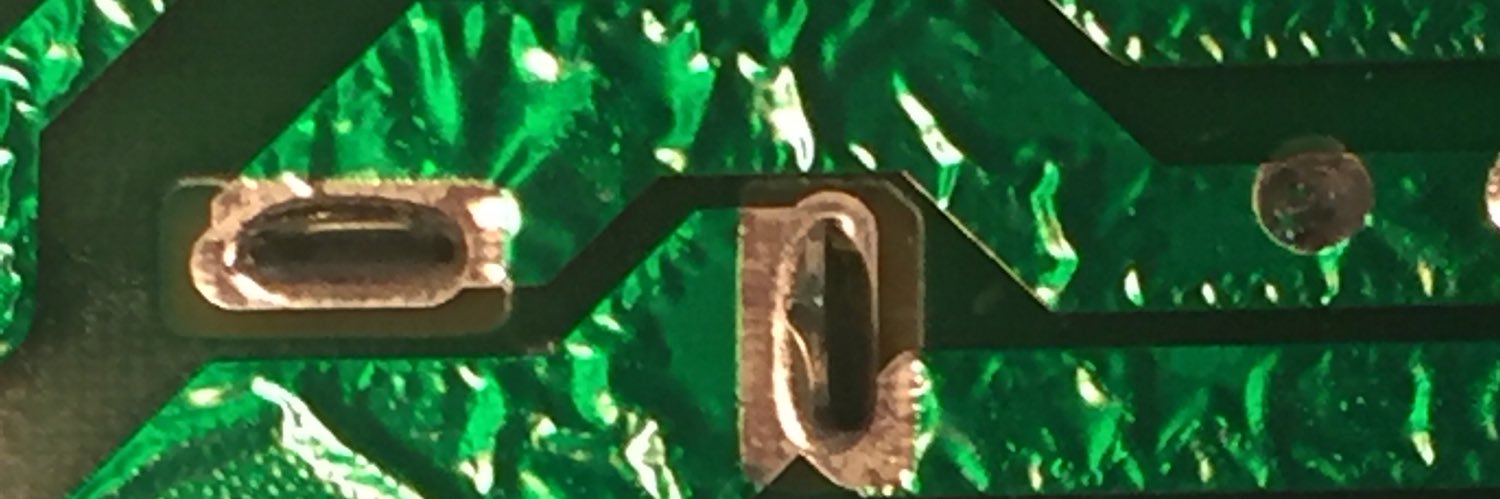
China’s "Olive-B" Stealth Micro-Satellite Link: mdpi.com/2226-4310/9/12…

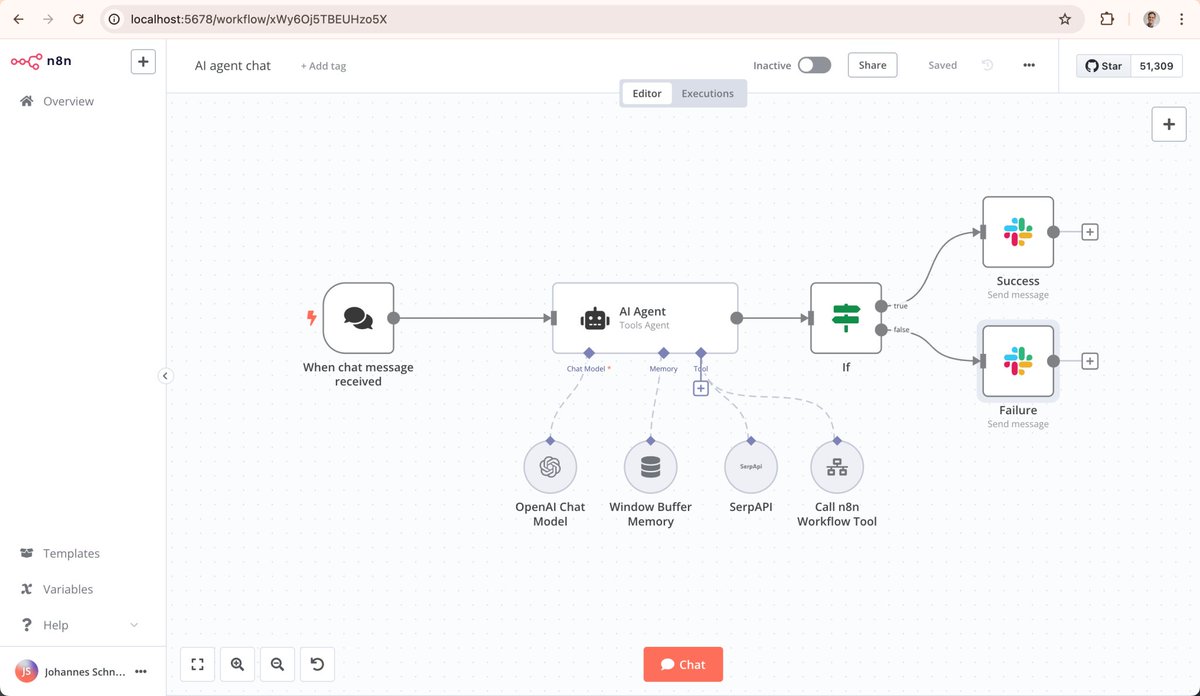



There's no gatekeeping detection rules here. We upload detection rules from the Devo + @DetecteamInc solution into Devo Exchange, our community-based app, so that all of our users can benefit from it and keep their organizations secure. Learn more: bit.ly/4lfEMeA
Tech news alert! The newest episode of the Techstrong Gang is here on this lovely Friday. We unpacked the latest big moves in the world of cybersecurity and discussed Palo Alto Networks’ acquisition of CyberArk for $25B! Plus, we dish on the insecure truth about "vibe coding" and Clorox's lawsuit against Cognizant over shady password reset practices.Ultimately when bad things happen, companies must be accountable and transparent to maintain customer trust and preserve brand reputation. Tune in to the latest Techstrong Gang episode to stay on top of the latest tech news and trends! @TechstrongTV @TechstrongGroup @jswartz @fewdisc @irawinkler #TechstrongGang #Cybersecurity #TechNews #Innovation #PaloAltoNetworks #VibeCoding #Security #Cognizant #Clorox #Crowdstrike


Adversaries are exploiting vulnerabilities in the software that powers essential services like water, transportation, healthcare & communications. These risks can be prevented by securing software from the start. See more: cisa.gov/SecureByDesign