Bruce Barnett (@grymoire.bsky.social)
16.1K posts

Bruce Barnett (@grymoire.bsky.social)
@grymoire
Maker, magician, security gadabout, doomscroller, etc. @[email protected] @[email protected] https://t.co/pKMn5JBFfS










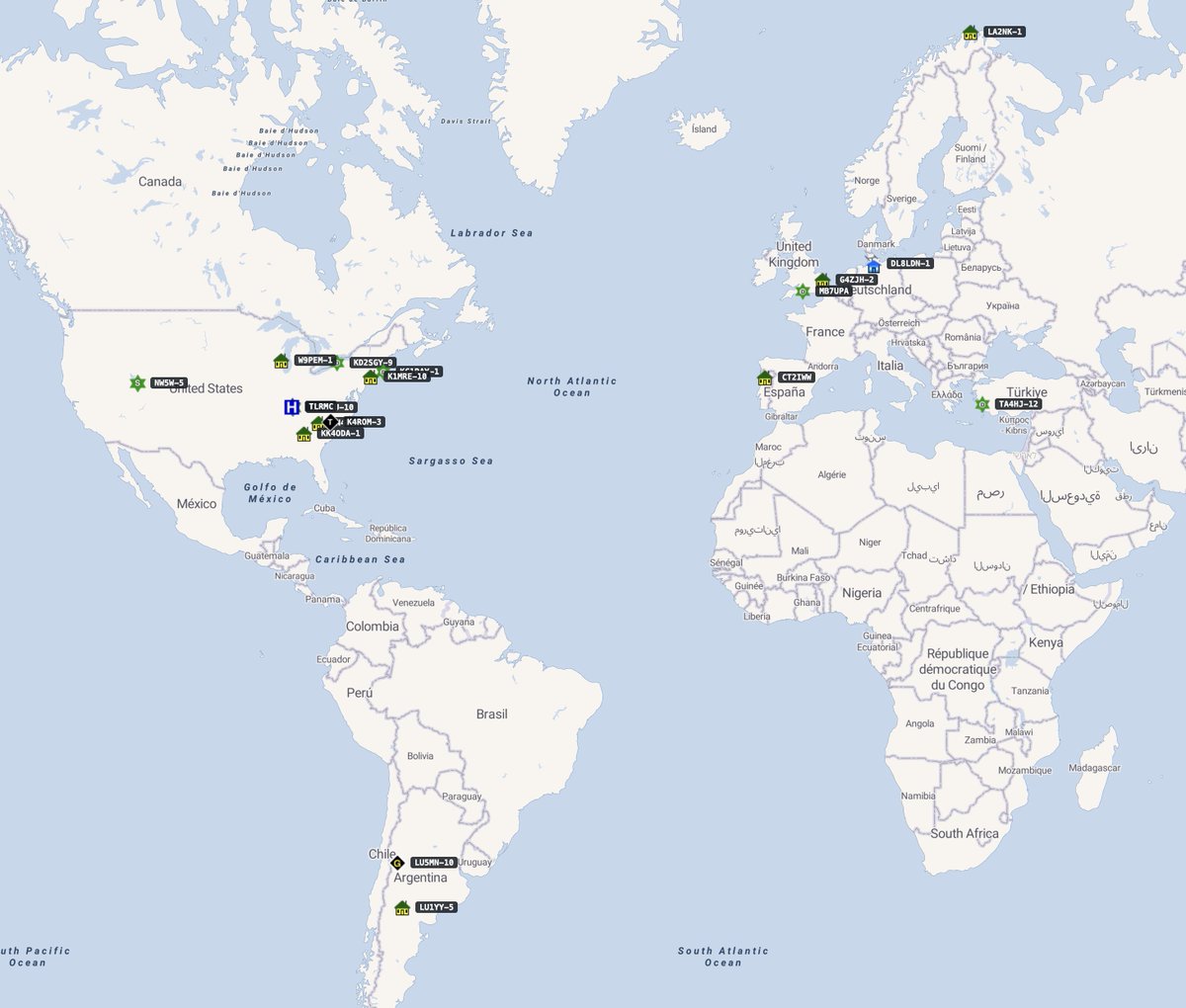
Together with @bzvr_, @2igosha and Anton Kargin, we identified that the DAEMON Tools software has been compromised in a complex supply chain attack since April 8. We see thousands of infections across 100+ countries. If you use DAEMON Tools, run a malware scan immediately! [1/7]


A mathematician has come up with a new way to derive all mathematical operations from merely one. I've had a look at the paper.


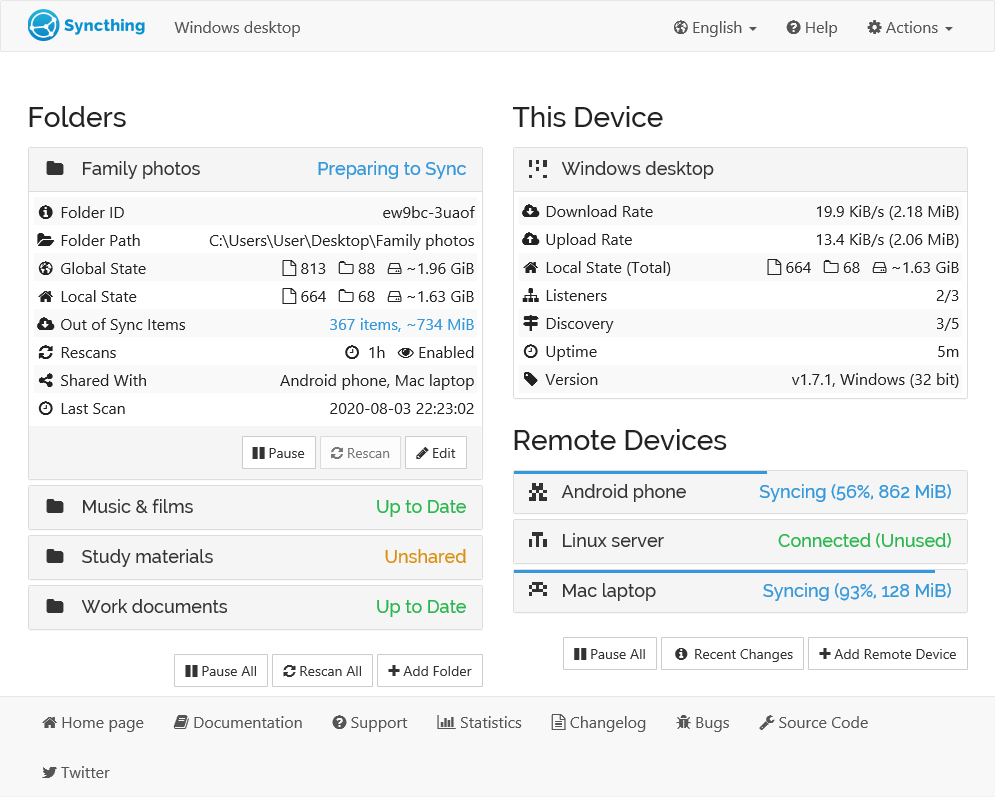
Anyone else seeing Microsoft #Defender flagging #DigiCert root certificate registry keys as malware? We’ve seen reports that Defender signature update from April 30 added a detection called: Trojan:Win32/Cerdigent.A!dha In some environments, Defender apparently detected DigiCert Root CA certificate registry entries and removed them from the trust store. The affected cert hashes mentioned so far: 0563B8630D62D75ABBC8AB1E4BDFB5A899B24D43 DDFB16CD4931C973A2037D3FC83A4D7D775D05E4 Example path: HKLM\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\0563B8630D62D75ABBC8AB1E4BDFB5A899B24D43 There’s also a Reddit comment suggesting Microsoft has started restoring the certs and that admins can check this via Advanced Hunting in Defender: DeviceRegistryEvents | where RegistryKey contains "0563B8630D62D75ABBC8AB1E4BDFB5A899B24D43" or RegistryKey contains "DDFB16CD4931C973A2037D3FC83A4D7D775D05E4" | where ActionType == "RegistryKeyCreated" | where Timestamp > datetime(2026-05-03T04:00:00) | project Timestamp, DeviceName, ActionType, InitiatingProcessFileName | order by Timestamp desc On an affected device, this can also be checked with: certutil -store AuthRoot | findstr -i "digicert" Could become an annoying day for admins if this spreads reddit.com/r/cybersecurit…




SHOCKING: PowerPoint isn’t dead… but it just got outsmarted. Discovered an AI that builds full decks from any doc in 30 seconds. This is how presentations are made now. Here’s how to create stunning presentations with zero effort: 👇





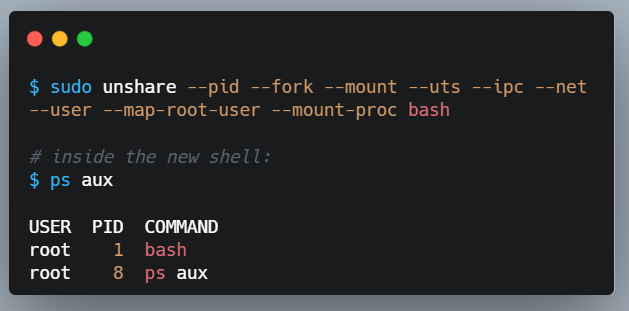
You probably already heard about Copy Fail - the Linux LPE that affects basically every current distro and shared-kernel/container environment I’ll post a few updates here soon copy.fail