Rakan Alotaibi - (hx) retweetledi

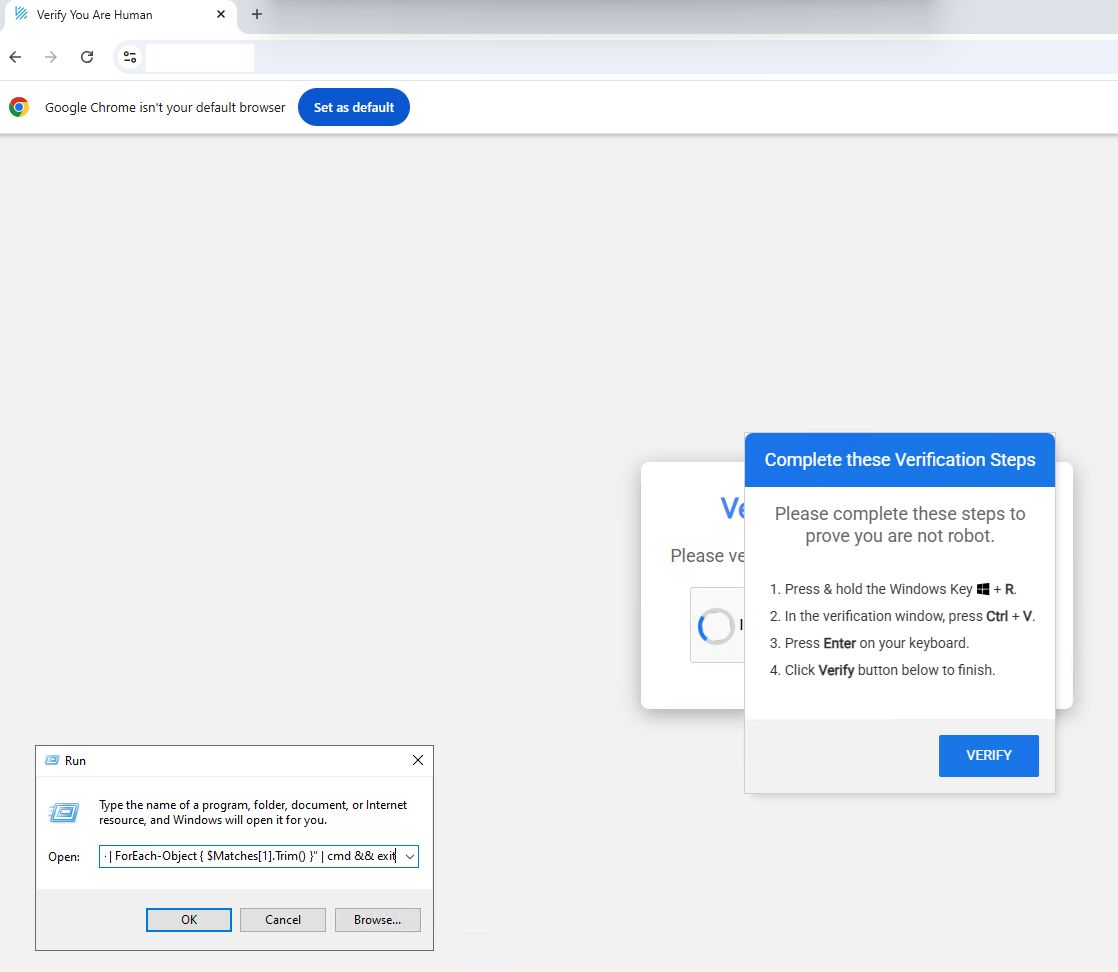
⚡️0-Day Alert: Google Chrome RCE + EoP in the wild
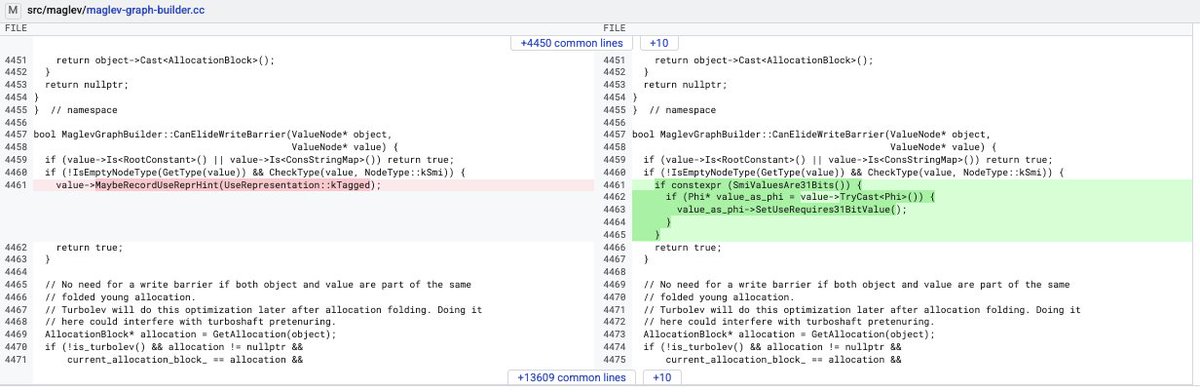
• CVE-2026-3910: v8 Maglev JIT incorrect write barrier elimination for Smi representation in Phi edge cases => UaF or memory corruption
Impact: remote ACE in renderer via JavaScript code.
Same structural pattern invariant as seen in a recent WebKit jsc bug.
• CVE-2026-3909: Skia glyph cache key collision to out-of-bounds write in GPU process
Impact: at least a partial (full on some platforms) Sandbox Escape primitive.
Potentially reachable remotely via renderer media formats.
In the specific exploit it was likely pushed directly to IPC from a compromised renderer via CVE-2026-3910.
Both bugs patched since Chrome 146.0.7680.80 for Windows/Mac and 146.0.7680.80 for Linux



English