Sabitlenmiş Tweet
iMoD1998
912 posts


iMoD1998
@iMoD1998
Programmer/PPC Master. Making Hax Since 1998 @the_secret_club
UK Katılım Nisan 2011
348 Takip Edilen446 Takipçiler
iMoD1998 retweetledi

@frizkedblizz Since I don’t understand code, I’m going to chat with Codex for a bit
English
iMoD1998 retweetledi
iMoD1998 retweetledi
iMoD1998 retweetledi

@HatBuster @PrimeTactiks @rileycs_ This is not true. Depending on how its implemented it ca n be compensated or removed in a number of ways.
English
@PrimeTactiks @rileycs_ You can't cheat away the bloom. It's weapon selection.
MP5 and AK-205 are MASSIVELY less bloomy than faster firing alternatives, at the cost of lower damage output over time.
You CAN, however, use those weapons and slap soft aim hax on top, for the best result.
English
iMoD1998 retweetledi

Cool DMA cheating timeline, highlights @nickeverdox's phenomenal work in the space: isdmadead.com
English

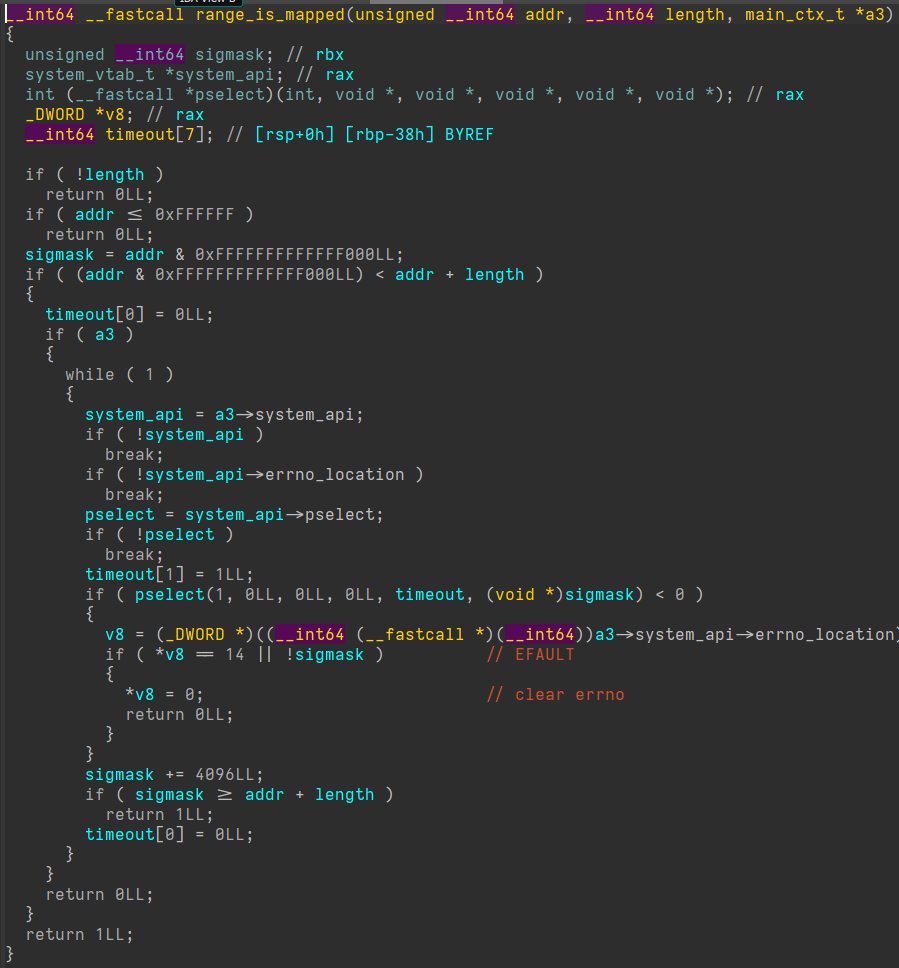
One time I was speaking with @daaximus and he commented on a weird feature in a user mode API I wasn't aware of.
I asked how he learned that. He said he reverse engineered it.
I asked why he reverse engineered it. He said, "Why not?"
You're god damn right, Dax.
English

Agreed, increased difficulty makes some people more intimated. The primary reason is due to the ever growing base line knowledge requirements to perform actions.
It weeds people out, and sometimes rather quickly.
Conversely, I (as well as others in our research collective) always saw it as inspirational. It is cool seeing new security features introduced. It allows you to learn. Furthermore, it acts as fuel to continue exploring and looking for things to abuse.
Ultimately what sets people apart in the offensive research field is their perception of challenges. Some may seem them as obstacles and feel intimidated. Others may feel excitement and joy because it's an opportunity to learn and explore. It's a lot of fun.
Justin Elze@HackingLZ
People still don't realize that if you look at the last 15-20 years of pentesting, there has been an arc where it was "easy" or easier because of training, free tools, free research, lack of EDR, places not investing in security and everything else you're now slowly seeing the other side of that. The whole point of doing all of this wasn't to keep doing things the same way but to make the job harder.
English
iMoD1998 retweetledi
iMoD1998 retweetledi
iMoD1998 retweetledi

This YouTube Twitch Game Bro says he's been a hacker for 20 years and did anti cheat stuff at Blizzard
He said he pulled it out into assembly, grabbed the code cave (?) and removed "the polymorphic" (?).
What the fuck is this guy talking about
youtube.com/shorts/LY2hG-_…

YouTube
English
iMoD1998 retweetledi
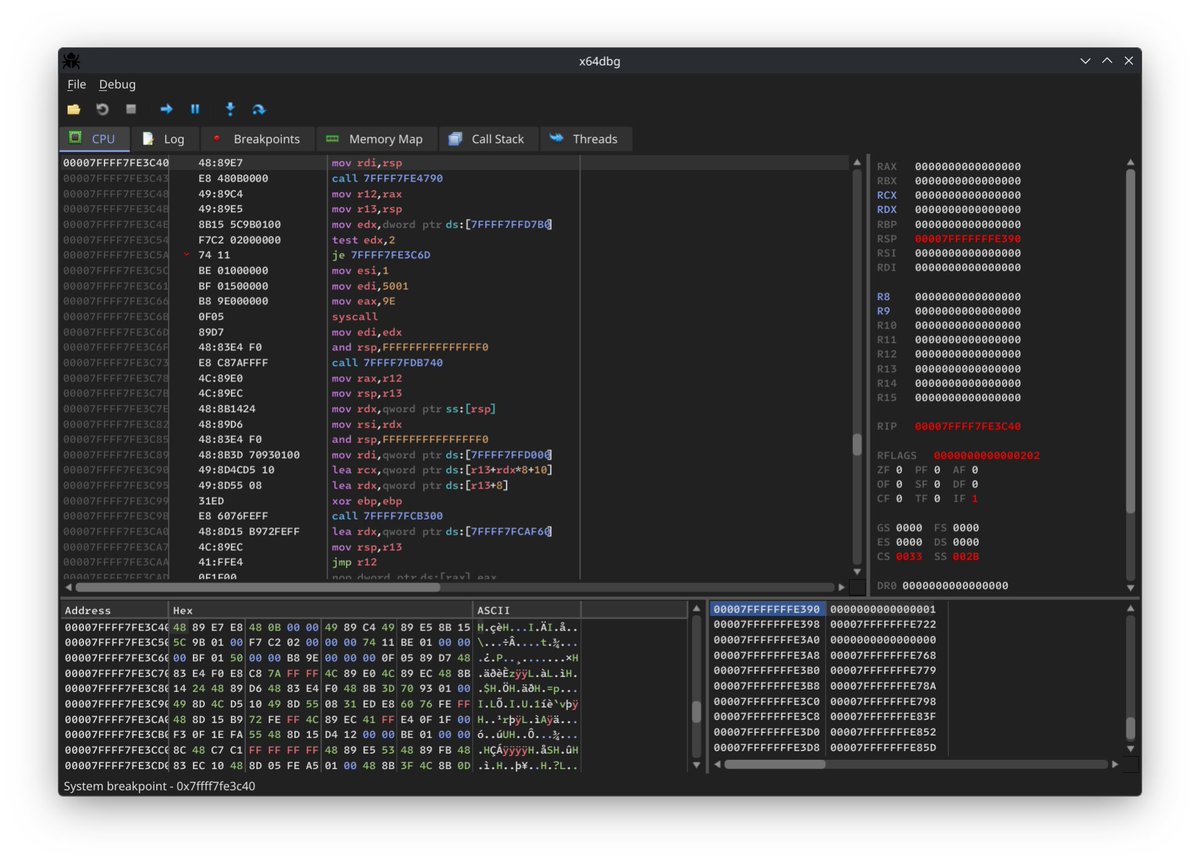
I created a hypervisor-based emulator for Windows x64 binaries. This project uses Windows Hypervisor Platform to build a virtualized user-mode environment, allowing syscalls and memory accesses to be logged or intercepted. elastic.co/security-labs/…
Project:
github.com/x86matthew/Win…
English
iMoD1998 retweetledi
iMoD1998 retweetledi
iMoD1998 retweetledi
iMoD1998 retweetledi