Sabitlenmiş Tweet
𝙞𝙣𝙩𝙚𝙡𝙧𝙖𝙩
112 posts

𝙞𝙣𝙩𝙚𝙡𝙧𝙖𝙩
@intelrat
Independent OSINT/threat intel research. Content is for informational purposes only and does not endorse or promote any referenced services or activity.
Deep Underground Katılım Ocak 2026
301 Takip Edilen730 Takipçiler

Instructure confirms data breach, ShinyHunters claims attack.
bleepingcomputer.com/news/security/…
English

Marcus & Millichap Data Breach (alleged ShinyHunters victim)
1.8 million accounts reportedly affected.
haveibeenpwned.com/Breach/MarcusM…
English

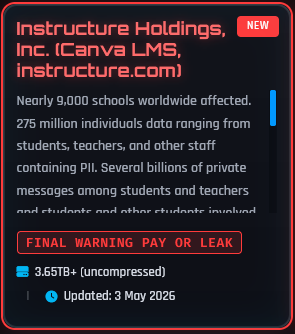
Ransom extortion group ShinyHunters have listed a new alleged victim on their leak site.
Threat actor: ShinyHunters
Alleged victim: Instructure Holdings, Inc.
Claimed data size: 3.65TB+ (uncompressed)
Leak deadline: 6 May 2026
Post date: 3 May 2026
Threat actor claim:
"Nearly 9,000 schools worldwide affected. 275 million individuals data ranging from students, teachers, and other staff containing PII. Several billions of private messages among students and teachers and students and other students involved, containing personal conversations and other PII. Your Salesforce instance was also breached and a lot more other data is involved. Pay or Leak." - ShinyHunters
DISCLAIMER: I am simply reporting on claims made by a known threat actor group (ShinyHunters), these claims should not be taken as fact. The presence of a listing does not necessarily mean a breach has occurred.
English

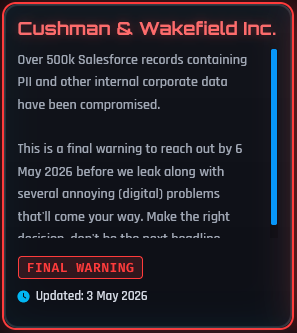
Ransom extortion group ShinyHunters have listed a new alleged victim on their leak site.
Alleged victim: Cushman & Wakefield Inc.
Leak deadline: 6 May 2026
Post date: 3 May 2026
Threat actor claim:
"Over 500k Salesforce records containing PII and other internal corporate data have been compromised." - ShinyHunters
DISCLAIMER: I am simply reporting on claims made by a known threat actor group (ShinyHunters), these claims should not be taken as fact. The presence of a listing does not necessarily mean a breach has occurred.
English

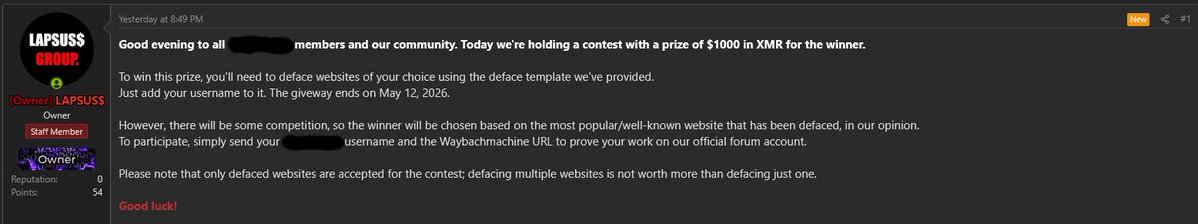
Threat actor LAPSUS$ Group are conducting a huge defacement campaign.
The threat actor LAPSUS$ Group is openly running a $1,000 (XMR) “contest” encouraging participants of a popular cybercrime forum to deface websites and submit proof via archived links.
Winner is reportedly chosen based on the perceived notoriety of the compromised site, not volume.
Deadline listed: May 12, 2026.
This activity highlights ongoing efforts to gamify and normalize cybercrime, posing clear risks to organizations and public facing infrastructure.
English

US ransomware negotiators get 4 years in prison over BlackCat attacks.
bleepingcomputer.com/news/security/…
English

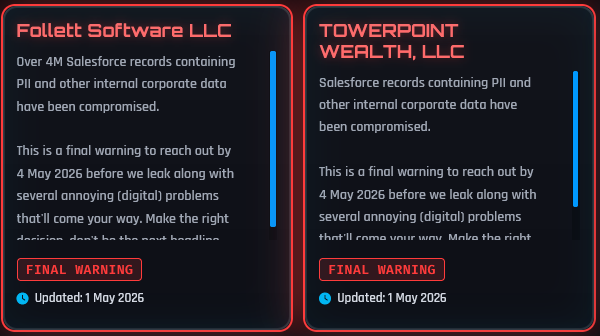
Ransom extortion group ShinyHunters have listed 2 new alleged victims on their leak site.
Alleged victims:
1: TOWERPOINT WEALTH, LLC
2: Follett Software LLC
Both alleged victims have been given a leak deadline of 4 May 2026.
Threat actor claim:
"This is a final warning to reach out by 4 May 2026 before we leak along with several annoying (digital) problems that'll come your way. Make the right decision, don't be the next headline." - ShinyHunters
DISCLAIMER: I am simply reporting on claims made by a known threat actor group (ShinyHunters), these claims should not be taken as fact. The presence of a listing does not necessarily mean a breach has occurred.
English

Romanian leader of online swatting ring gets 4 years in prison.
bleepingcomputer.com/news/security/…
English

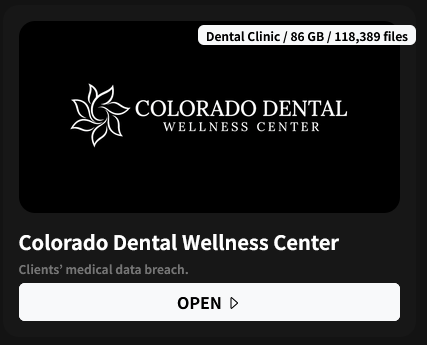
Ransomware group Anubis have just listed a new alleged victim on their leak site.
Listing details:
Threat actor: Anubis
Alleged victim: Colorado Dental Wellness Center
Sector: Dental Clinic
Claimed data size: 86 GB / 118,389 files
DISCLAIMER: I'm simply reporting on claims made by a known threat actor group (Anubis), these claims should not be taken as fact. The presence of a listing does not necessarily mean a breach has occurred.
English

Checkmarx Confirms Data Stolen in Supply Chain Attack
securityweek.com/checkmarx-conf…
English
𝙞𝙣𝙩𝙚𝙡𝙧𝙖𝙩 retweetledi

‼️Hacker Ring Busted in Lviv Oblast After Stealing Gaming Accounts and Selling Them in Russia for Nearly UAH 10 Million
Prosecutors in Lviv Oblast, working with the Cyber Police and the Security Service of Ukraine (SBU), have dismantled a criminal group that hijacked Roblox accounts and resold them on Russian websites for cryptocurrency, generating an estimated UAH 10 million in profit. The scheme was allegedly organized by a 19-year-old resident of Drohobych, who recruited two accomplices aged 21 and 22 and is suspected of compromising more than 610,000 accounts belonging to Ukrainian and foreign players.
The group targeted profiles containing valuable virtual items, rare equipment, and in-game currency balances purchased with real money. To break in, the suspects deployed "stealer" malware disguised as gaming cheats and used stolen cookie files that allowed them to log into accounts without passwords. The hijacked accounts were then sold through closed online communities and a website hosted on a Russian domain, with proceeds funneled into crypto wallets.
Investigators conducted 10 searches and seized computer equipment, storage media, mobile phones, bank cards, handwritten notes, over EUR 2,500, and nearly USD 35,000 in cash. The suspects have been served notices of suspicion under Part 4 of Article 185 and Part 5 of Article 361 of the Criminal Code of Ukraine, face up to 15 years in prison, and have been placed in pretrial detention while the investigation continues.
gp.gov.ua/en/posts/na-lv…




English

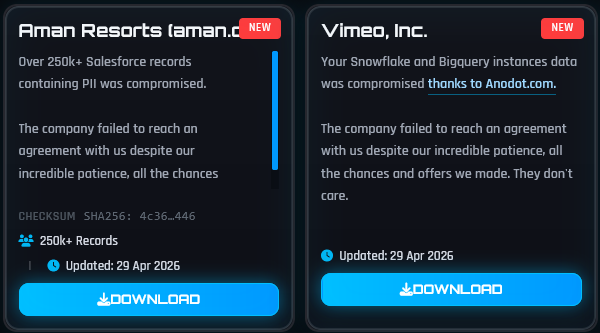
Ransom extortion group ShinyHunters now claim to have published data belonging to Aman Resorts & Vimeo, Inc. after having reached the leak deadline.
ShinyHunters have listed both Aman Resorts & Vimeo, Inc. on their leak site.
Threat actor claim:
"The company failed to reach an agreement with us despite our incredible patience, all the chances and offers we made." - ShinyHunters
DISCLAIMER: I am simply reporting on claims made by a known threat actor group (ShinyHunters), these claims should not be taken as fact. The presence of a listing does not necessarily mean a breach has occurred.
𝙞𝙣𝙩𝙚𝙡𝙧𝙖𝙩@intelrat
Ransom extortion group ShinyHunters claim to have breached Vimeo, Inc. ShinyHunters have listed Vimeo, Inc. on their leak site, and have set a leak deadline of 30 April 2026. Threat actor claim: "Your Snowflake and Bigquery instances data was compromised thanks to Anodot[.]com. Pay or Leak." -ShinyHunters DISCLAIMER: I am simply reporting on claims made by a known threat actor group (ShinyHunters), these claims should not be taken as fact. The presence of a listing does not necessarily mean that a breach has occurred.
English

US reportedly charges Scattered Spider hacker arrested in Finland.
bleepingcomputer.com/news/security/…
English
𝙞𝙣𝙩𝙚𝙡𝙧𝙖𝙩 retweetledi

🚨 PATCH NOW: A Firefox bug let attackers fingerprint your browser and follow you even in Private Browsing, and in Tor browser even after a "New Identity."
The vulnerability made it possible for unrelated websites to independently observe the same fingerprint and quietly link your activity across them.
Mozilla patched CVE-2026-6770
on April 21, 2026 in Firefox 150, ESR 140.10, and Thunderbird. The Tor Project shipped Tor Browser 15.0.10 with the fix.
If you are still on an older build, your Private Browsing wasn't private and your Tor session wasn't either. Update now.


English

ADT confirmed a data breach by ShinyHunters.
Affected Accounts: 5.5 million
haveibeenpwned.com/Breach/ADT
English