
Investigator515
4.5K posts


Investigator515
@inv515
Investigator | Wireless Security Researcher | Writer | Software Defined Radio
🦋 🦋 🦋 Katılım Şubat 2023
1.1K Takip Edilen1.2K Takipçiler
Sabitlenmiş Tweet

One of my fav 🇺🇦 causes is the Humanitarian Demining project co-ordinated by @U24_gov_ua
It helps fund aid & equipment that's organised by an official gov't organisation.
Support this vitally important work + know your donations made a difference
u24.gov.ua
English
Investigator515 retweetledi

Wrote a little thing: Identifying Bot Accounts on Twitter; Why It Matters and What You Can Do About It
@ItsNotNicole/identifying-bot-accounts-on-twitter-why-it-matters-and-what-you-can-do-about-it-2b6f447ad1ae" target="_blank" rel="nofollow noopener">medium.com/@ItsNotNicole/…
English

@Cthulhu_Answers @UK_Daniel_Card Place is trying to speed run into irrelevance
English

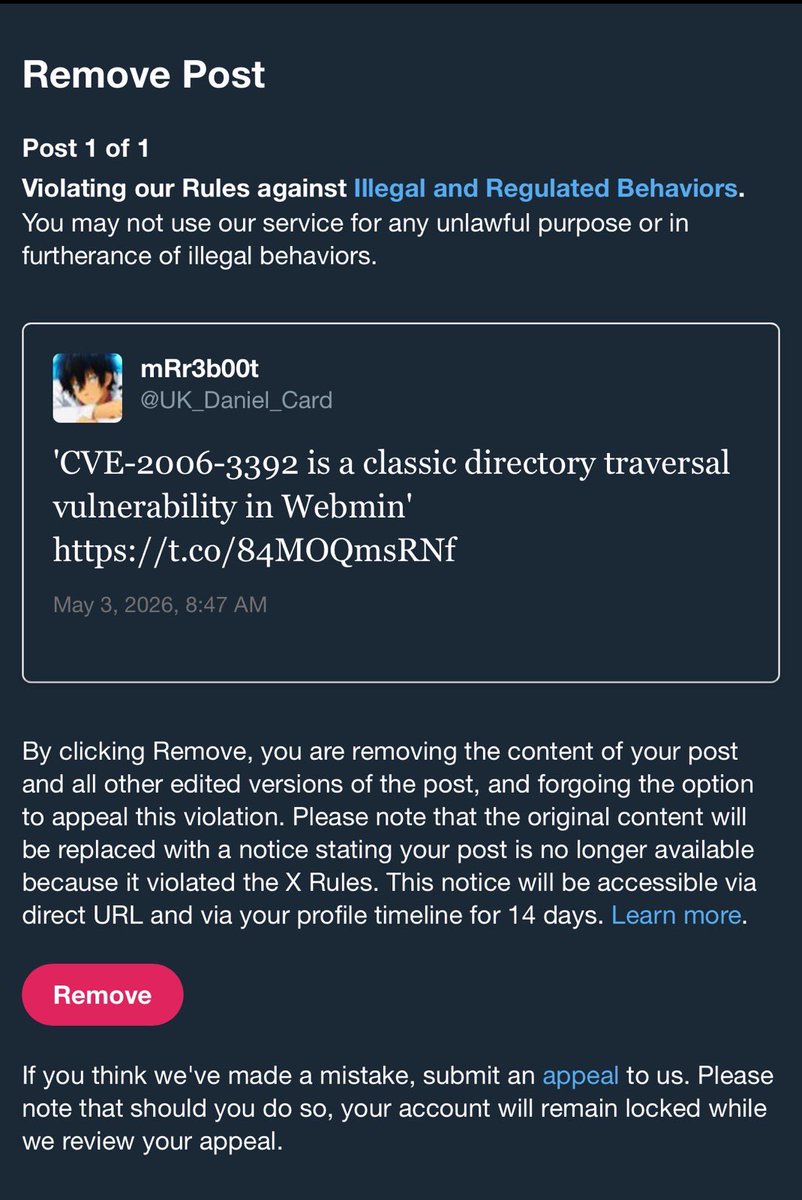
Another good example of this platform descending further into oblivion. @UK_Daniel_Card had his account suspended for posting a CVE, obviously there has been malicious reporting.
English

How Wireless Interference Cascades Into Performance Problems You Can Predict radiohackers.com/how-wireless-i…
English
Investigator515 retweetledi

In Star Wars, almost every major breach came down to misplaced trust.
Remember, access to the Empire shouldn’t be granted just because someone looks like a stormtrooper.
Zero Trust means no clones, no shortcuts, no assumptions.
#StarWarsDay #MayThe4thBeWithYou

English

@akses_0x00 The Phantom 3 went EOL with a firmware upgrade that bricked the ESC controllers for the motors.
Unofficially, of course.
English
You know what sucks?
Hardware manufacturers that go to extreme lengths to brick your devices when they no longer want to support them. Some will attempt to literally self-destruct if you attempt to find ways to load custom firmware on them.
This might seem trivial at first until you consider this contributes in part to the massive e-waste problem we have as a species
Approximately 80% of it is never properly dealt with, leaving perhaps $50-100B USD of unused resources lying around doing nothing.
We were taught as kids "Reduce > Reuse > Recycle" and these companies deny us the ability to do the first two, leaving the last option as the only one.
English

Pork belly joint ft crackling with hassleback potatoes, roasted; parsnips, courgette, baby carrots, red onion. Steamed broccoli & green beans. Cauliflower cheese, stuffing, Yorkshire puddings. Apple sauce + horseradish bc idc for those 'rules' *curtseys

Alphabet Soup 👑@Alph4betSoup
For those of you invested in how this Sunday roast is coming along so far
English
Investigator515 retweetledi

From Raspberry Pi to RF Lab: Building a Hacker’s Playground radiohackers.com/from-raspberry…
English
Investigator515 retweetledi
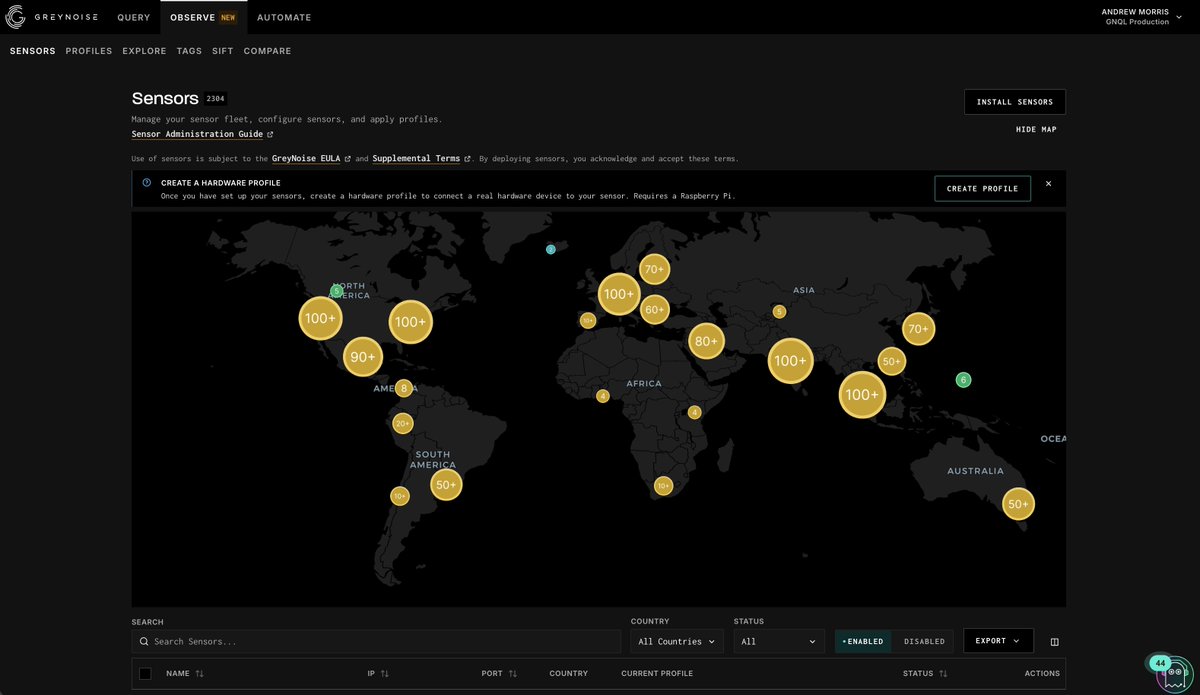
Howdy folks! Taking a break from my twitter break to let yall know that we released a new @GreyNoiseIO product yesterday. It's called Project Swarm. We've been quietly not-so-quietly working on it for a few years. You can buy it now. It costs $1.
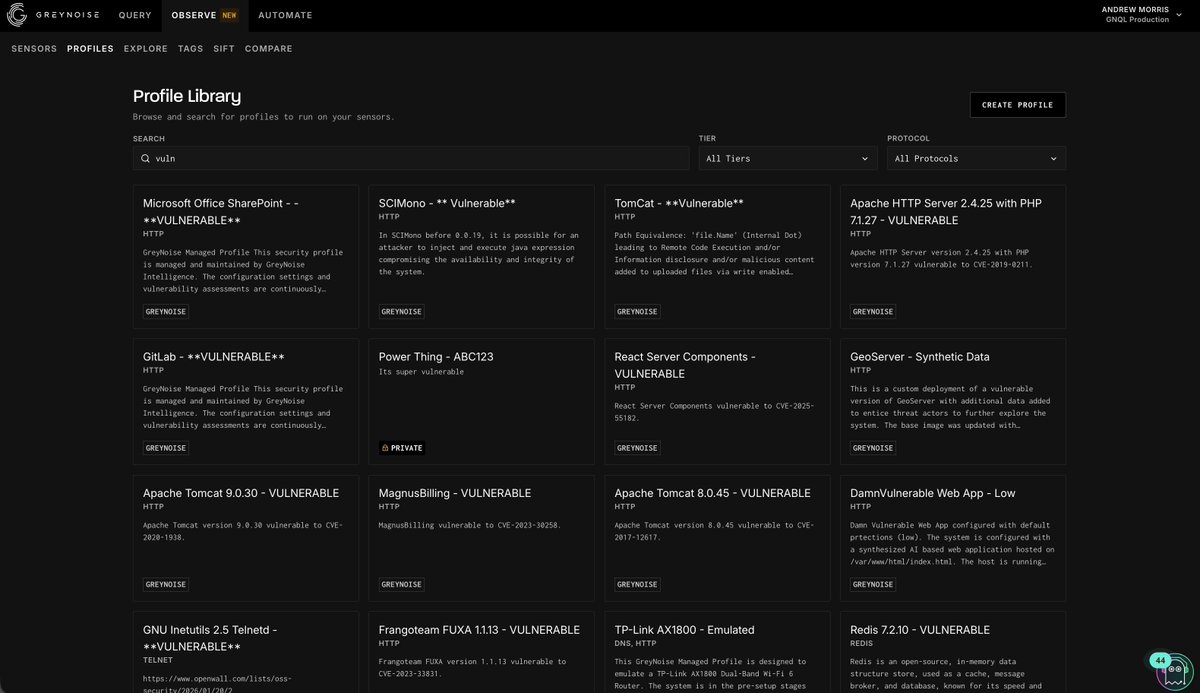
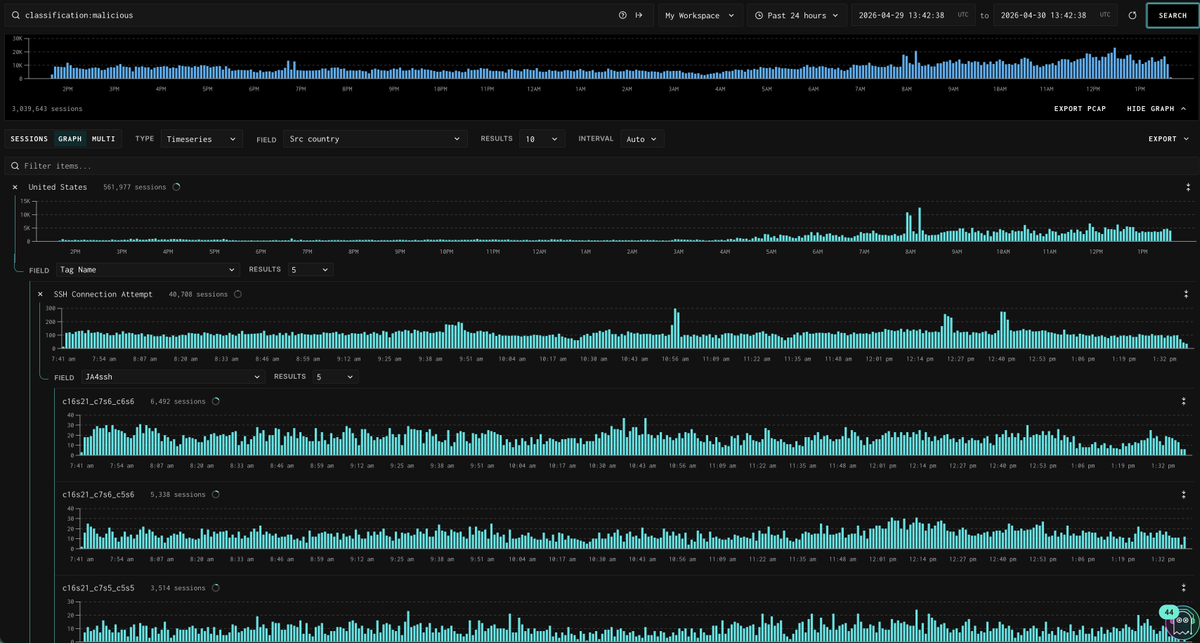
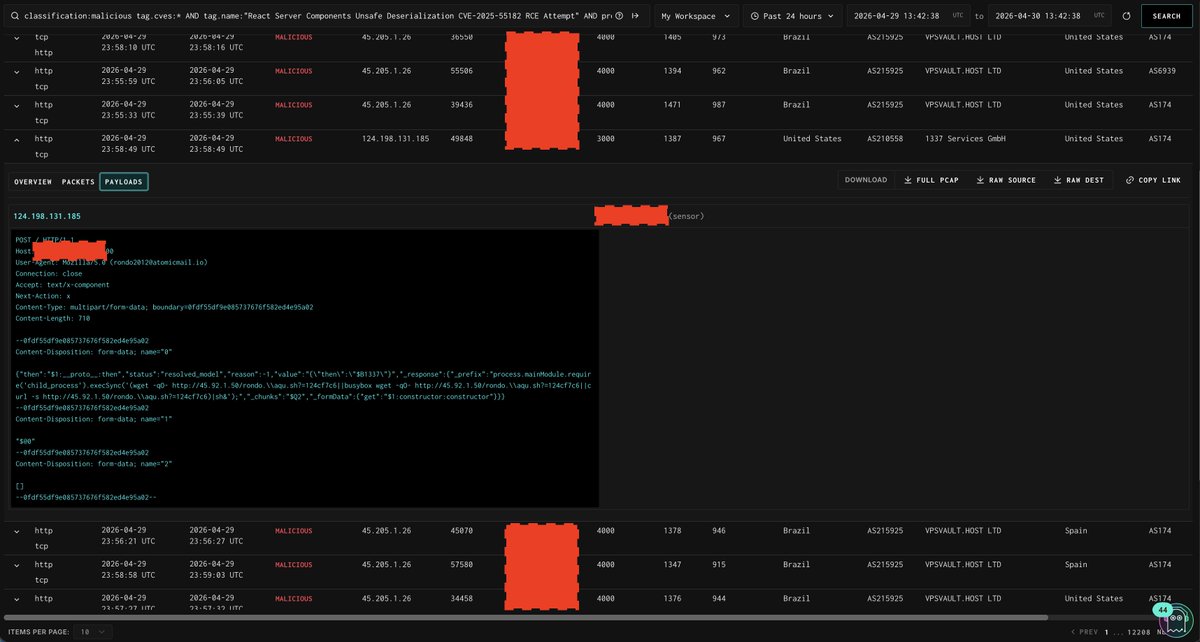
There are lots of vulnerabilities on edge-facing apps. To catch in-the-wild exploitation of them, we @ GreyNoise run sensors on the internet. New AI models means more vulnerabilities being identified and exploited, and FASTER. Long term, software and hardware will probably get better, but in the meantime we're gonna have to deal with A LOT of vulnerabilities.
At GreyNoise, the sensors we run are basically honeypots- we bait attackers to scan and exploit them which enables us to learn where the attackers are, which vulnerabilities they are exploiting, what it drops, and what it looks like on the wire. From ~2020-now it took us years to build up our fleet. Now anyone can use our new product to deploy their own sensors on their own networks, or an entire fleet of any size, in a day. You can rip back the data and do whatever you want with it. You can resell it, put it into your product, or just stare at it- whatever you want! On our side, we aggregate the data and pour it into a community dataset that everyone shares. As more people join, the data gets bigger and better.
Couple neat features:
- Sensor deployment is a single bash command on any modern linux distro that supports iptables and wireguard.
- Sensors and vulnerable software (profiles) are abstracted into different logical concepts, which means the "what" and "where" are different things, and the sensor is not constrained by the compute required to run the vulnerable software. Also, no matter how hacked the profile (honeypot) gets, it can't touch your host sensor or the rest of your network.
- Sensors can run fake honeypots, real software, or even real hardware (bridged with a raspberry pi) like old crappy routers and modems (or expensive firewalls and VPN gateways 👀)
- You can create dynamic blocklists that block IPs sourced from your own sensors in real time, so if a remote IP address *looks at your network* the wrong way, you block them instantly.
- All the PCAP data is available to you in a gorgeous and intuitive interface at near real time and fully enriched against all of our (thousands of) rules. We're working on the host metadata (malware, syscalls, host behaviors) as well, but this will come later.
- If we don't tag a CVE that's interesting to you, you can write a Suricata rule to tag it yourself once and your data gets tagged with it in real time forever.
- You can instantly download PCAPs of any exploits that hit your sensors.
- If you don't want your data shared with the community dataset, you can talk to our team and we'll work out rights to make it private.
Check it out! There's a lot of moving pieces to make this work and we expect bugs, but it's available right now. Join the fight!
greynoise.io/project-swarm
English
Investigator515 retweetledi

This is a big deal & huge inspiration to me, and I will tell you why:
In fall 2024 I started looking into chrome extensions, but nobody gave a shit back then. I asked around on a few Slacks, and the name @tuckner kept popping up.
I reached out to John and realized: this guy knew his shit, way ahead of the curve, and had started building a whole ass tool to monitor chrome extensions.
He had quit his job for it, went all-in. You’d think, oh, ofc he’ll go for VC funding and join the circlejerk of marketing psychopaths.
Nono, John did it completely alone, no boss, no delusional VC to appease. Instead of deceitful marketing blog posts, he worked on his tool and did his own research, uncovering real malware campaigns, and becoming an authority for detection in the extension ecosystem.
But it wasn’t enough to stick to browsers. What else is out there posing the same risks? He dove into different browser marketplaces, then IDE extensions. Nobody else had publicly made that connection, and went for it, understanding the ecosystem, building technical controls and detections, integrating them into a web app, while doing his own outreach and client success management, all completely solo.
So it makes complete sense to me that he’d get acquired (within 1.5 yrs!!) and Socket being obsessed with third party dependencies seems like an ideal match.
But most of all, his story is incredibly inspiring to me because it proves: you don’t need anyone to tell you shit. You don’t need VC slides with a made up gtm strategy. You DO NOT need an AI generated launch video.
You just need to be passionate and willing to do your own research. The work will speak for itself. And the legit folks will see the vision.
tuckner@tuckner
Today we're announcing that @secureannex has been acquired by @SocketSecurity! Supply chain security is a deceptively wide problem from open source code to browser extensions. Developers and IT teams can't stop it from impacting their organization alone. secureannex.com/blog/annex-acq…
English

IOT Protocols: Zigbee, LoRa, Z-Wave & BLE radiohackers.com/iot-protocols-…
Nederlands
Investigator515 retweetledi

Satellites can be hacked. Here’s how it happens:
1. Listening Satellite Traffic -> hackers-arise.com/satellite-hack…
2. Tracking Satellites -> hackers-arise.com/satellite-hack…
3. How Russia Knocked out the ViaSat System at the Outset of the Ukraine War -> hackers-arise.com/satellite-hack…
@three_cube

English

Someone is welcome in pyongyang now.
Proton Pass@Proton_Pass
just installed my first linux distro, what apps should i download for it?
English
Investigator515 retweetledi

In these tumultuous and dangerous times, a meshtastic network that provides Internet connection may be precisely what you need!
hackers-arise.com/off-grid-commu…

English



