Socket
2.9K posts


@SocketSecurity
Socket is the #1 software supply chain security platform. Next-gen SCA + SBOM + 0-day prevention. LOVED BY DEVELOPERS. 👀 @npm_malware




Socket is free for open source maintainers. We're launching the @SocketSecurity for Open Source program -- any open source maintainer can get a free Team plan to protect their project from supply chain attacks. Open source is critical infrastructure. Millions of companies depend on packages maintained by small teams and volunteers. These maintainers are high-value targets but rarely have access to enterprise security tooling. That's wrong. We want to fix it. What you get: ✅ Full dependency scanning across your project ✅ Real-time alerts for malicious packages in your dependency tree ✅ Check every PR to make sure no malicious dependencies are added -- including PRs from outside contributors If you maintain an open source project, send an email to support[at]socket[dot]dev and we'll get you set up!

Yesterday the open source community spotted a supply chain attack on PyTorch Lightning and contained it in 42 minutes. Community members flagged unusual behavior, reported it, and stopped it before it spread. Compromised versions (2.6.2, 2.6.3) were live between 12:45–13:27 UTC. This affected distribution only. The GitHub repo was never touched. Thanks to the community for the quick reports, to @pypi for quarantining the packages, and to @SocketSecurity for surfacing detailed analysis. Read the full report → go.lightning.ai/4n5vGTO


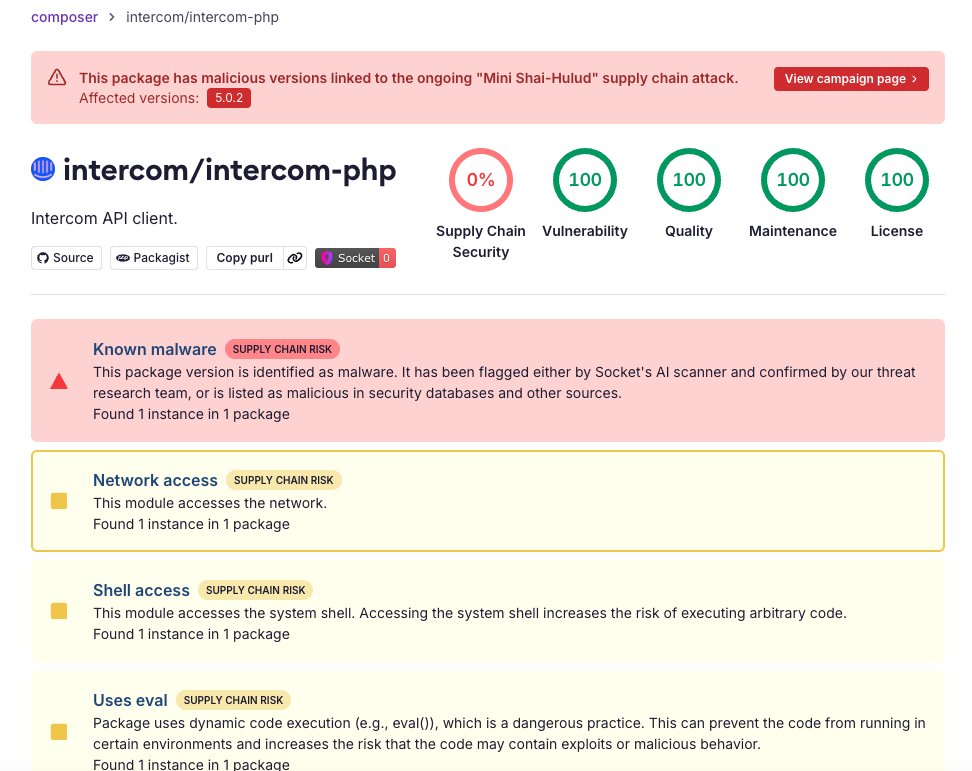
🚨 BREAKING: Mini Shai-Hulud has spread to Packagist. We detected a malicious intercom/intercom-php@5.0.2 package artifact tied to this campaign. The compromised #PHP package used Composer plugin execution to run during install/update, download Bun, and launch an obfuscated router_runtime.js credential-stealing payload. It targeted GitHub, npm, SSH, cloud, Kubernetes, Vault, Docker, .env files, and more. We reported it to @packagist, which removed the malicious version.






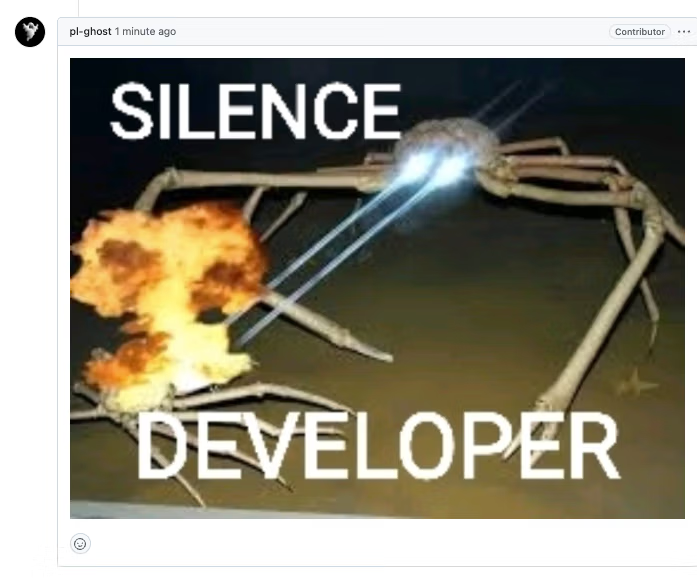
🚨 Two major supply chain attacks today, hitting both PyPI and npm simultaneously. Socket detected and confirmed malicious code in lightning versions 2.6.2 and 2.6.3 on PyPI, and intercom-client version 7.0.4 on npm. Both attacks use nearly identical tooling. Both are live right now. lightning is one of the most popular deep learning frameworks in the Python ecosystem, with millions of downloads per month. intercom-client is Intercom's official Node.js SDK, with roughly 360K weekly downloads. These are not typosquats. These are the real packages. The payloads are almost identical across both attacks: • Both inject an ~11MB obfuscated JavaScript file (router_runtime.js) and a setup script that downloads and executes the Bun runtime from GitHub • Both harvest GitHub tokens, npm tokens, AWS/Azure/GCP credentials, Kubernetes secrets, Vault tokens, and CI/CD environment variables • Both exfiltrate stolen credentials through the GitHub API • Both execute automatically, lightning on import, intercom-client on install The lightning attack goes further. It uses stolen GitHub tokens to commit poisoned files to every branch of every repository the token can write to, impersonating Anthropic's Claude Code as the committer (claude@users.noreply.github.com). It also infects local npm tarballs by injecting a postinstall hook and bumping the patch version, so the next publish silently ships malware to downstream users. In both cases, the attackers appear to have compromised maintainer accounts and used them to suppress disclosure. On the Lightning-AI GitHub, the pl-ghost account closed Socket's disclosure issue within one minute and posted a meme. On the Intercom GitHub, the nhur account closed, redacted, and retitled security reports to "N/A." Both accounts show bursts of suspicious branch-creation activity consistent with the Shai-Hulud worm's credential-probing pattern, including misspelled Dependabot impersonation branches. The attackers posted an onion link in the Lightning-AI issue thread claiming affiliation with "Team PCP" and referencing LAPSUS$. Socket has not verified these claims. The intercom-client attack also shows direct Shai-Hulud hallmarks, including repos created with descriptions reading "A Mini Shai-Hulud has Appeared." Socket's AI scanner flagged the malicious lightning versions 18 minutes after publication. If you use either package: • Remove lightning 2.6.2/2.6.3 and intercom-client 7.0.4 immediately • Downgrade to lightning 2.6.1 / intercom-client 7.0.3 • Rotate all credentials in affected environments • Audit repos for unauthorized commits from claude@users.noreply.github.com and unexpected files in .claude/ or .vscode/ • More advice in our full research posts... This is the same attacker campaign operating across two language ecosystems simultaneously. The playbook is credential theft, repo poisoning, and worm-style propagation. The scope is still being determined. Developing story...

🚨 BREAKING: Mini Shai-Hulud has spread to Packagist. We detected a malicious intercom/intercom-php@5.0.2 package artifact tied to this campaign. The compromised #PHP package used Composer plugin execution to run during install/update, download Bun, and launch an obfuscated router_runtime.js credential-stealing payload. It targeted GitHub, npm, SSH, cloud, Kubernetes, Vault, Docker, .env files, and more. We reported it to @packagist, which removed the malicious version.


🚨 A brand-squatting npm package impersonating TanStack shipped malicious versions that exfiltrate environment variables from developers’ machines during install. We spoke to @tannerlinsley, creator of @tan_stack, who confirmed that the maintainer of the unscoped tanstack package is not associated with TanStack or the official @tanstack/* projects in any way. The package is unrelated to the project's official CLI, and represents an ongoing brandjacking issue. He also said TanStack has filed legal documents related to a pending trademark infringement claim against the maintainer, that the maintainer previously demanded $10,000 from him, and that TanStack has repeatedly tried, unsuccessfully, to get @npmjs to address the situation.

🚨 BREAKING: Mini Shai-Hulud has spread to Packagist. We detected a malicious intercom/intercom-php@5.0.2 package artifact tied to this campaign. The compromised #PHP package used Composer plugin execution to run during install/update, download Bun, and launch an obfuscated router_runtime.js credential-stealing payload. It targeted GitHub, npm, SSH, cloud, Kubernetes, Vault, Docker, .env files, and more. We reported it to @packagist, which removed the malicious version.

🚨 BREAKING: Mini Shai-Hulud has spread to Packagist. We detected a malicious intercom/intercom-php@5.0.2 package artifact tied to this campaign. The compromised #PHP package used Composer plugin execution to run during install/update, download Bun, and launch an obfuscated router_runtime.js credential-stealing payload. It targeted GitHub, npm, SSH, cloud, Kubernetes, Vault, Docker, .env files, and more. We reported it to @packagist, which removed the malicious version.