Emanuele Cozzi retweetledi
Emanuele Cozzi
1.6K posts

Emanuele Cozzi retweetledi

Heya! Our new research on client-side game cheating & anti-cheat systems is out: birmingham.ac.uk/news/2024/wind…
Joint work with Sam Collins, Alex Poulopoulos, and @TomChothia.
Full paper: cs.bham.ac.uk/~tpc/Papers/An…
English
Emanuele Cozzi retweetledi

We are very excited to share our last research work: 𝐄𝐔𝐂𝐋𝐄𝐀𝐊, authored by Thomas Roche.
An electromagnetic Side-Channel Vulnerability in the ECDSA implementation of all Infineon security microcontrollers, notably impacting all YubiKey 5 Series.
ninjalab.io/eucleak/
English
Emanuele Cozzi retweetledi

In a few minutes I will present our work on Android evasive malware to @ASIACCS2024 [1].
What better occasion to reveal that DroidDungeon, the sandbox developed for this work, has evolved into a commercial product?
Join the beta -> tnemesis.com
English
Emanuele Cozzi retweetledi

Excited to share (albeit with a little delay) that our @binarly_io talk about #LogoFAIL at BlackHat EU is available! Check it out to see the vulnerabilities we found in UEFI image parsing and their security implications:
youtube.com/watch?v=ch0t2_…

YouTube
English
Emanuele Cozzi retweetledi

We are setting up a user study to measure the impact of LLMs during the Reverse Engineering process.
If you have ever used LLMs for reversing, click here to start the survey (5 mins) 👉 forms.gle/tKBdNjAKE5oyPq…
You can leave your email address for the second phase-with prizes💰
English
Emanuele Cozzi retweetledi

The xz situation is absolutely insane and almost certainly state sponsored.
This is an excellent example of a widely used software being maintained by basically one person.
Read this web article and then frown and become sad.
boehs.org/node/everythin…
English
Emanuele Cozzi retweetledi

🚀 BIG ANNOUNCEMENT! 🚀
The full rev.ng decompiler pipeline is now fully open source!
Also, we'll soon start to invite people to participate in the UI closed beta.
Check out our latest blog post: rev.ng/blog/open-sour…

English
Emanuele Cozzi retweetledi

Fuzzing is hard, evaluating fuzzing is harder 🔥
For our new @IEEESSP paper, we studied 150 fuzzing evals and found issues such as lackluster documentation, bad experiment setups, or questionable CVEs
📄 Paper mschloegel.me/paper/schloege…
🔧 Help us fix this github.com/fuzz-evaluator…
English
Emanuele Cozzi retweetledi

I'm about 50% done integrating SAILR into angr master: github.com/angr/angr/issu… 🎉
P.S.: You can also use angr's decompiler more easily now. Try this out:
```
pip3 install angr && \
angr decompile /bin/true --functions main
```
English
Emanuele Cozzi retweetledi

elfconv: AOT compiler for translating Linux/aarch64 ELF → LLVM bitcode → WASM
By my colleague @ming_rrr
medium.com/nttlabs/elfcon…
English
Emanuele Cozzi retweetledi

Sono lieto di annunciare la disponibilità del primo corso di malware analysis in italiano: "Introduzione alla malware analysis: Un approccio pratico"
Oltre 9 ore di corso: t.ly/WPhap (utilizzate questo link, non cercate il corso su udemy ^^)
condivisione gradita :)
Italiano
Emanuele Cozzi retweetledi

2024 is the year of the decompiler! Start your year off right by reading a post on the last 30 years of decompilation and one of its hardest problems: structuring! mahaloz.re/dec-history-pt1
Part 2 to be released next week.
English
Emanuele Cozzi retweetledi

I just published the code and hardware for Tamarin-C, the iPhone 15 USB-C exploration tool I presented at #37c3.
github.com/stacksmashing/…

English
Emanuele Cozzi retweetledi
As WOOT becomes a more formal Conference, we want to keep receiving industry submissions! WOOT experiments a new model: in addition to the academic submissions, there is a practitioner's track. Submit a draft early, inerract with reviewers to get this written as a paper.
USENIX WOOT Conference on Offensive Technologies@wootsecurity
The USENIX WOOT '24 conference(!) draft CfP is out: usenix.org/conference/woo…. March 12 is the ⏰ for your offensive security papers! Or think academics should know about your work, but no experience writing formal papers? Submit a draft to the new practitioner track by Feb 20!
English
Emanuele Cozzi retweetledi

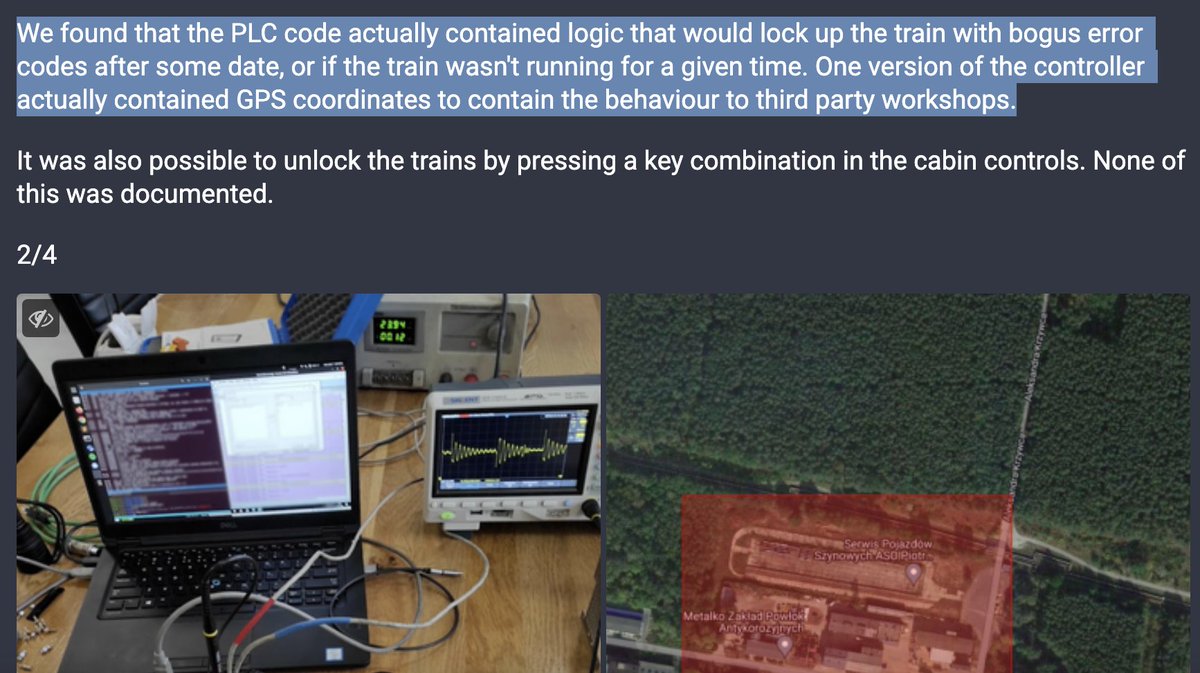
They HACKED A TRAIN. For real. Train operators asked for this to see why their trains didn't run after servicing. Turns out that vendor/producer implemented a geofence lock for trains serviced somewhere else. Amazing story, one of the best hacks in 2023. @q3k/111528165627522619" target="_blank" rel="nofollow noopener">social.hackerspace.pl/@q3k/111528165…
English
Emanuele Cozzi retweetledi
Emanuele Cozzi retweetledi

New write-up on an Intel Ice Lake CPU vulnerability, we can effectively corrupt the RoB with redundant prefixes! 🔥 An updated microcode is available today for all affected products, cloud providers should patch ASAP.
lock.cmpxchg8b.com/reptar.html
English
Emanuele Cozzi retweetledi

I'm excited to announce a new decompilation control flow structuring algorithm, SAILR, which is the first to precisely revert compiler optimizations in decompilation. Find out how in our USENIX 2024 paper: zionbasque.com/files/publicat…. Code, info, and links in the 🧵

English
Emanuele Cozzi retweetledi

Earlier this year @AmnestyTech and @_clem1 from Google TAG found an in-the-wild iPhone zero day full chain. Today I’m publishing my analysis of the Safari sandbox escape component, the first in-the-wild sample to break into the new Safari GPU process.
English