iQimpz
627 posts

iQimpz
@iqimpz
Full-Time Bug Bounty | Christian | https://t.co/lqwI4J261E
Katılım Kasım 2020
226 Takip Edilen1.3K Takipçiler

iQimpz retweetledi

I’ve been digging into HTTP Trailers and found some new smuggling techniques:
sebsrt.xyz/blog/trailing-…
English
iQimpz retweetledi

New: I'm sharing the @trailofbits Claude Code defaults. This is how we setup, configure, and use claude code:
github.com/trailofbits/cl…

English
iQimpz retweetledi

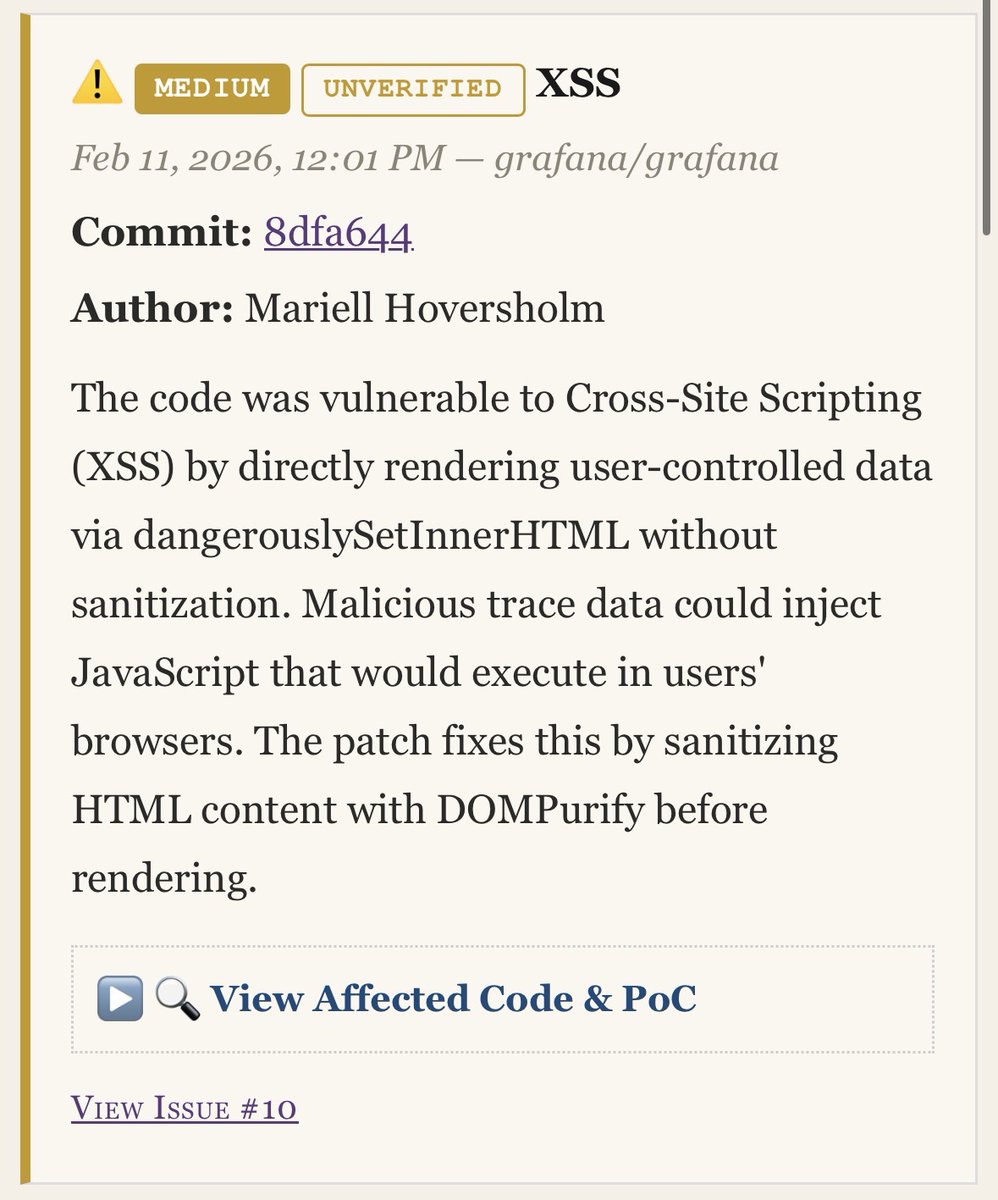
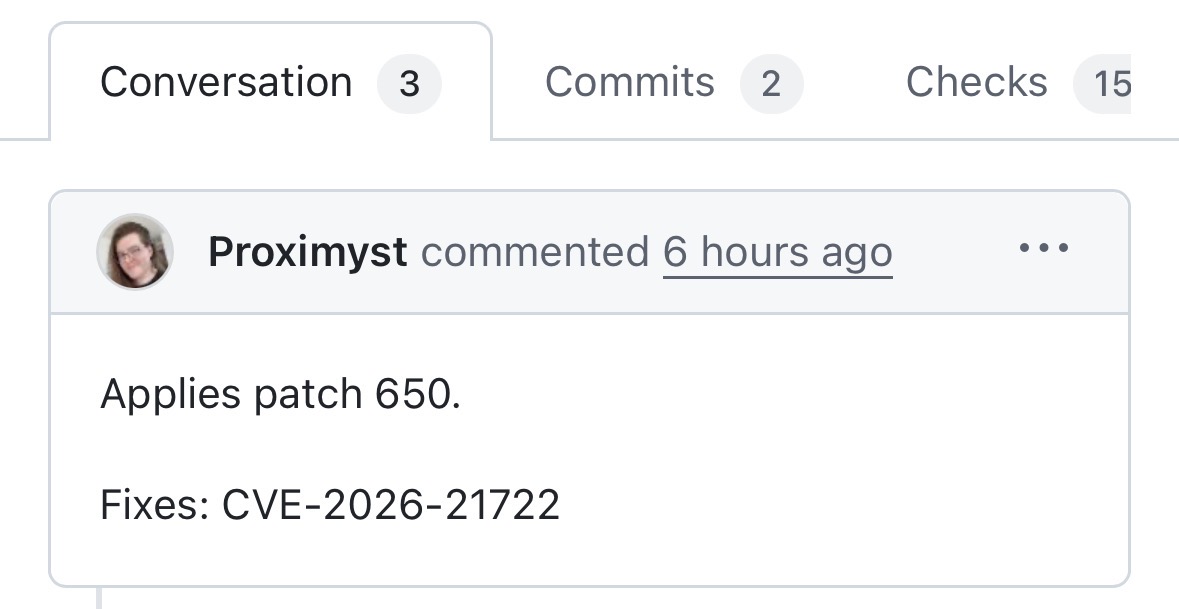
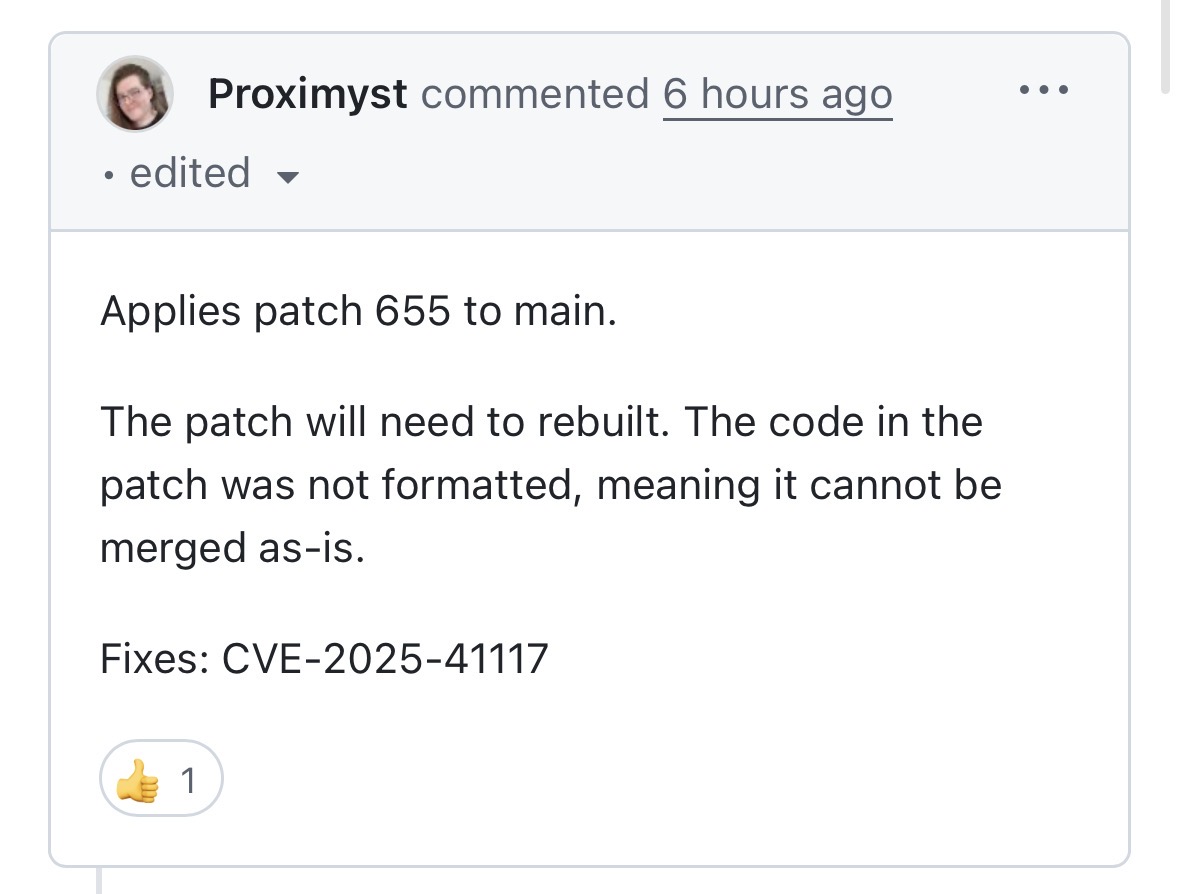
Vulnerability-spoiler-alert has detected its first two live “negative-days” in Grafana! CVE-2025-41117 (XSS) and CVE-2026-21722 (Privesc) are still unpublished right now, but is detectable via commits in the open-source repo. That’s at least 1 hour early. PoCs and more at vulnerabilityspoileralert.com

English
iQimpz retweetledi

Voting is now live for the top ten web hacking techniques of 2025! Grab a coffee, browse the 61 quality nominations and cast your vote on the most creative and ground-breaking techniques:
portswigger.net/polls/top-10-w…
English
iQimpz retweetledi

.@trailofbits released our first batch of Claude Skills. Official announcement coming later.
github.com/trailofbits/sk…
English
iQimpz retweetledi

We've published a new blog post by RyotaK @ryotkak
He discovered 8 methods to bypass safety mechanisms in Claude Code, leading to arbitrary command execution.
We recommend updating to v1.0.93 or later to fix this vulnerability (CVE-2025-66032).
flatt.tech/research/posts…
English
@monkehack We on the same page this week! I’ve been closing those “open loops” and figuring out where AI fits into my workflows.
English

🐵 MonkeHacks #89
Upgrades, Open Loops, Notetaking
#bugbountytips #hacktheplanet #BugBounty monke.ie/p/monkehacks-89
English
iQimpz retweetledi

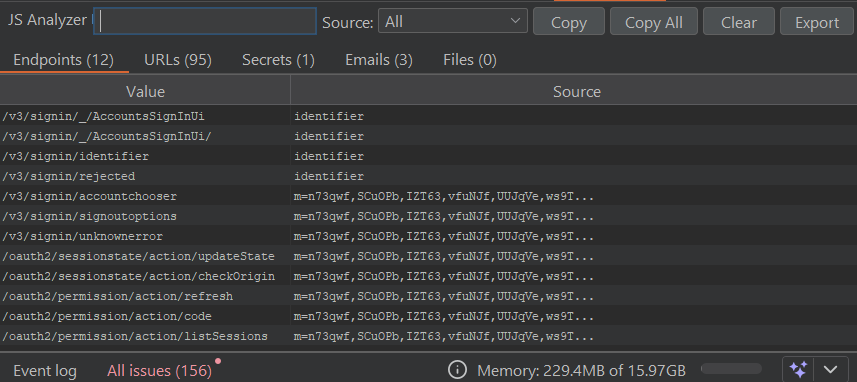
Sharing my Burp Extension that earned me $200k in 2025 while API testing heavy JS-rich targets.
github.com/jenish-sojitra…
The tool helps find endpoints, files, internal emails, and some secrets from minified JS.
Its goal is to achieve maximum efficiency with reduced noise in results. Contributions and feedbacks are welcome.
English

my 2025, in review:
- shattered my income goals by a huge margin
- adopted 2 stupid cats (I love them)
- 5 LHEs, 4 awards at LHEs
- 1600 day duolingo streak with 90 perfect weeks in a row so far
- 2200 day journalling streak
- started taking guitar lessons and going to therapy
- spoke at Nahamcon, Bsides Dublin, HackAICon and the Irish government's conference
- visited Australia, NZ, Mexico, Taiwan, Japan, Vegas, and more
- newsletter almost at 1,000 subs
crazy year. here's to a good 2026!
#bugbounty #rewind
English
iQimpz retweetledi

Windows IPC Deep Dive, by @haider_kabibo
1 sud0ru.ghost.io/windows-inter-…
2 sud0ru.ghost.io/windows-inter-…
3 sud0ru.ghost.io/windows-inter-…
4 sud0ru.ghost.io/windows-inter-…
5 sud0ru.ghost.io/windows-inter-…
6 sud0ru.ghost.io/windows-inter-…
7 sud0ru.ghost.io/windows-inter-…
8 sud0ru.ghost.io/windows-inter-…
9 sud0ru.ghost.io/windows-inter-…
English
iQimpz retweetledi

@G0LDEN_infosec for GUNGNIR the crt log transparency monitor!
github.com/g0ldencybersec…
English
iQimpz retweetledi

Great blog from @elttam's team diving into the ORM leak vulnerability class! I don't see many other writeups about this, but it's super interesting and worth remembering/looking for next time you're looking at code with no manually concatenated SQL - elttam.com/blog/leaking-m…
English
iQimpz retweetledi
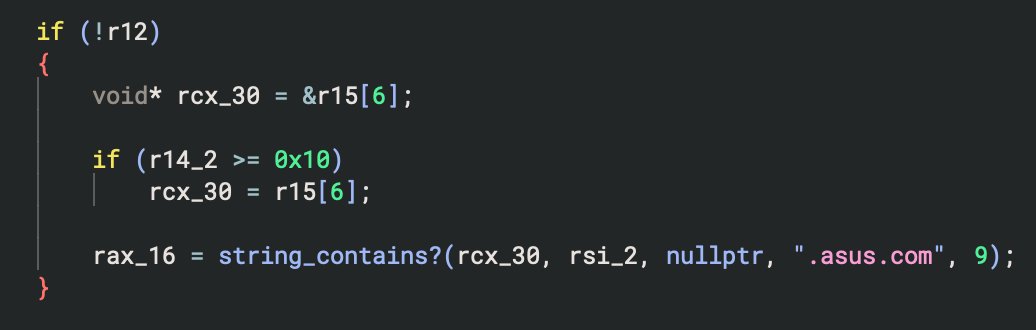
Two blog posts just dropped - one with the details on the bloatware pwning shenanigans I was up to earlier in the year, and another on pipetap, a new Windows named pipe proxy/tool.
sensepost.com/blog/2025/pwni…
sensepost.com/blog/2025/pipe…
English
iQimpz retweetledi

Diffing 7-Zip for CVE-2025-11001
pacbypass.github.io/2025/10/16/dif…
English
iQimpz retweetledi

My very first blog post is live: kiddo-pwn.github.io/blog/2025-11-3…
During research, I've run into and documented a simple universal SQLite Injection RCE trick. Enjoy!
N-day Analysis about Synology Beestation RCE (CVE-2024-50629~50631) by legendary DEVCORE 🎃 🍊
Thanks to @u1f383 @orange_8361 for original finding and allowing to post, and to @the_emmons for the invaluable references 🔥
Enjoy the Demo!
PoC: github.com/kiddo-pwn/CVE-…
English
iQimpz retweetledi

iQimpz retweetledi

The watchTowr Labs team is back, providing our full analysis of the Oracle E-Business Suite Pre-Auth RCE exploit chain (CVE-2025-61882).
Enjoy with us (or cry, your choice..)
labs.watchtowr.com/well-well-well…
English