Ivo de Abreu Araujo
412 posts


Ivo de Abreu Araujo
@ivoaabreu
Bug Hunter | Cyber Security
Katılım Ağustos 2011
293 Takip Edilen37 Takipçiler

March dump:
- 1 pentest (solo) + meetings @katrinasecteam
- Chile trip w/ my wife
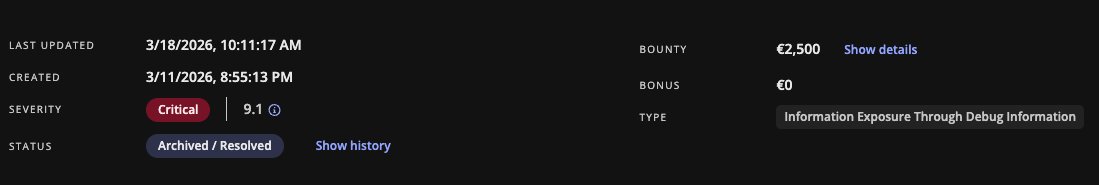
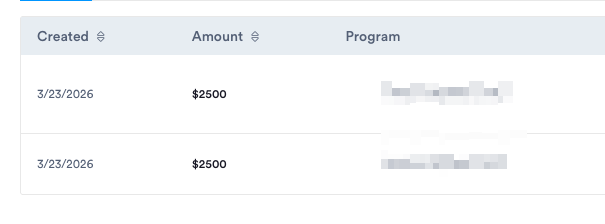
- ~10k in bounties (a few collabs)
Findings:
- 2 IDORs (WordPress)
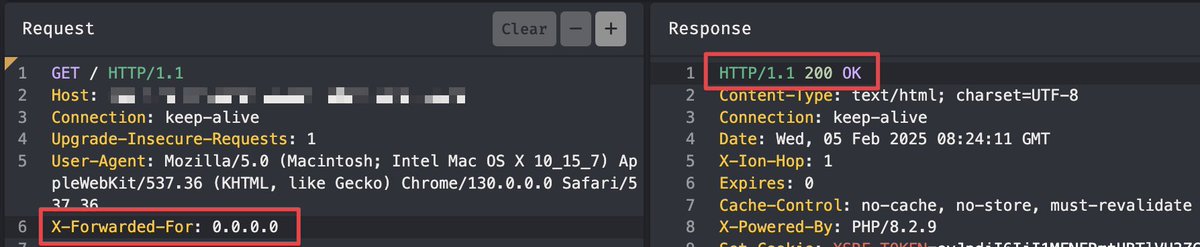
- Symfony Debug Bypass
- DOM XSS via postMessage()
- KYC bypass (iGaming)
- NGINX path traversal
good enough for me 😆


English
Ivo de Abreu Araujo retweetledi

"Sensitive Information Leak & Missing Authorization via API Endpoint"
Join my BugBounty Chennal: t.me/ShellSec
- to find info leak bugs in wordpress use my this quick wordlist:
/api/v1/export/data
/api/v1/config
/api/debug/env
/api/v2/auth/sessions
/api/v1/admin/users
/wp-json/wordfence/v1/config
/api/v1/billing/details
/api/v1/db/stats
/api/v1/logs
/api/v1/health
/api/v1/status
/api/v1/internal/settings
/api/v1/cloud/credentials
/api/v1/user/profile
/api/v1/system/info
/api/v1/backup/list
/wp-json/wp/v2/users
/wp-json/wp/v2/settings
/wp-json/wp/v2/media
/wp-json/wp/v2/posts?status=any
/wp-json/wp/v2/pages?status=private
/wp-json/elementor/v1/system-info

English
Ivo de Abreu Araujo retweetledi

Bypassing 2FA isn’t always about breaking the OTP
Sometimes the weakness is in the implementation
Here are a few common paths worth testing 👇
#bugbountytips #bugbountytip #bugbounty
English


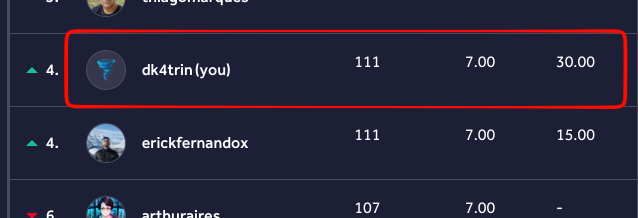
@luq0xss @intigriti Já ultrapassou faz tempo, kkk, so achados top
Português
Ivo de Abreu Araujo retweetledi

🔥Find critical vulnerabilities in js files✨
Looks inside this JS files:
🔍main, app, runtime, bundle, polyfills, auth, config, settings, local, dev, data, api, session, user,core, client, server, utils, base
Read the full method 👇🏼 t.me/ShellSec/176

English
Ivo de Abreu Araujo retweetledi

bugbounty tip:
[easy to find critical bugs, follow this method]
1. find a api sensitive endpoint (must be leak sensitive info)
2. look headers "Cache-Control, CF-Cache-Status, Via, X-Cache, ETag, Age" confirm they store cache or not. (if stored try web cache deception)
3. change the HTTP request method (like: GET to POST, GET to HEAD, POST to PUT etc.)
4. if you find endpoints like: /api/users/123 use array based iDOR vulnerability (like: /api/users/123,122)
don't forget to join my bugbounty telegram channel: t.me/ShellSec

English
Ivo de Abreu Araujo retweetledi

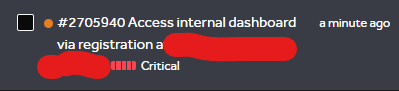
Find a Business Logic Bug
Exploit steps:
1. Register a new account (note the username)
2. Verify & activate it
3. Delete the account
4. Try registering again with the same username
If blocked, it’s a Business Logic bug — deleted usernames shouldn't be reserved!
#bugbountytips
English
Ivo de Abreu Araujo retweetledi
Ivo de Abreu Araujo retweetledi

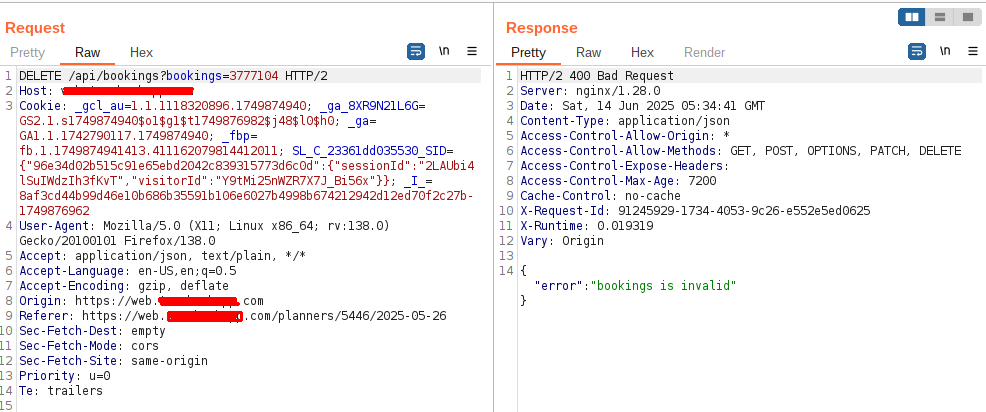
I was able to delete anyone's Bookings. But this was so tricky, not an easy IDOR!
Original Req:
DELETE /api/bookings?bookings=3777104
Response:
Invalid Bookings = > 400 Bad
Modified req:
DELETE /api/bookings?bookings[]=3777104
Response:
200 OK
#bugbountytips

English
Ivo de Abreu Araujo retweetledi

Tip:-
Add to your wordlist:
auth/jwt/register
auth-demo/register/classic
auth-demo/register/modern
My First P1🥳
#bugbountytips #bugbountytip #bugbounty #hackerone #bugcrowd #h1

English
Ivo de Abreu Araujo retweetledi

When a single ID fails, a pair might pass. IDOR bypasses can be that simple 🔥
- Victim's ID: 5200
- Attacker's ID: 5233
GET /api/users/5200/info → Access Denied ❌
GET /api/users/5200,5233/info → Bypassed ✅
#bugbountytips #PenetrationTesting


English
Ivo de Abreu Araujo retweetledi

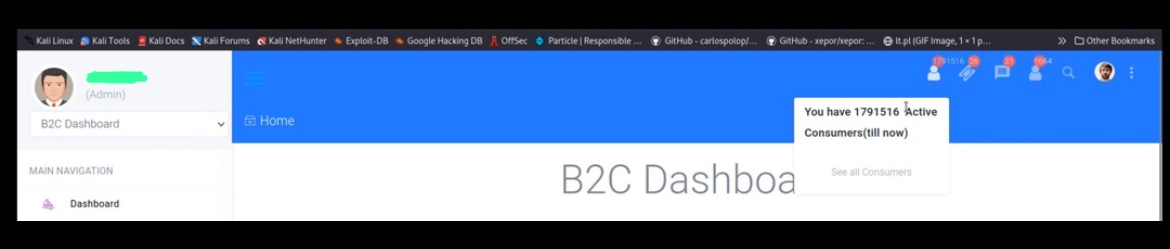
Admin Panel Takeover….
Mr. Admin you are gone babe.. 😁😁
Username: name@target.com
Password: name@target.com
#BugBounty #bugbountytips
English
Ivo de Abreu Araujo retweetledi

⚡ 2FA Bypass leads to impersonation of legimate users
👨🏻💻 dedoxd2 ➟ Drugs.com
🟥 High
💰 None
🔗 hackerone.com/reports/2885636
#bugbounty #bugbountytips #cybersecurity #infosec

English
Ivo de Abreu Araujo retweetledi