Jay Bosamiya
1K posts


Jay Bosamiya
@jay_f0xtr0t
🦊 Software security researcher. PhD from CMU. CTFer (PPP). | Inactive here | Find me at https://t.co/l4yhLdJfp0
Somewhere in the Matrix Katılım Ocak 2016
1.5K Takip Edilen1.9K Takipçiler
Sabitlenmiş Tweet

Got my first high severity bug in Chrome!!! CVE-2019-5755.
Fixed in the latest Chrome Stable, that just released. chromereleases.googleblog.com/2019/01/stable…
English
Jay Bosamiya retweetledi

Dust off your boots, grab your hats, and get ready for a showdown — Plaid CTF is headin’ for the frontier! On April 4, we venture westward. But will you have what it takes to rise to the challenge of The Good, The Plaid, and The Ugly? plaidctf.com

English
Jay Bosamiya retweetledi
The Rust verification tool Verus aims to make formal verification more widely available to developers, helping them create software that behaves as intended. Learn about the work, an award winner at SOSP ’24, w/ Chris Hawblitzel & Jay Lorch on “Abstracts”: msft.it/6017WXtX1

English

@ZaneDuffield @pcwalton Thanks, that’s quite helpful. Definitely more hits with “unwrapped lines”. I guess I’m gonna dive into reading the source code soon to see if that design could have eliminated some of the issues we’ve faced in our formatter.
English

@pcwalton @ZaneDuffield Our current approach builds an AST (with comments + certain whitespace tracked only in certain positions but ignored elsewhere; eg b/w stmts), and then use a Wadler style pretty printer (via docs.rs/pretty), with some hacky fixes to fix up comment positioning.
English

@pcwalton @ZaneDuffield Do either of you have any suggested reading for the logical line based design? Or should I just dive into the clang-format source?
Context: I’m one of the creators and maintainers of github.com/verus-lang/ver… and was recently fighting some AST-based formatter annoyances. […]
English
Jay Bosamiya retweetledi

.@CarnegieMellon's hacking team, the Plaid Parliament of Pwning (PPP), won its third consecutive title at the 2024 @DEFCON Capture-the-Flag competition, earning its record eighth victory in 12 years. #DEFCON2024 #DEFCON32 #DC32 cylab.cmu.edu/news/2024/08/1…

English

Adithya Murali@adithyamuralism
I am on the academic market! My long-term goal is to democratize verification, enabling programmers without verification expertise to verify software. My research develops ways to lower the "cognitive burden" for non-experts. Check out my website for more! muraliadithya.github.io
ZXX

Defended my PhD thesis on "A Principled Approach towards Unapologetic Security" yesterday!
Thanks so much to my advisor (Bryan Parno), committee members (@JAldrichPL, Phil Gibbons, and Chris Hawblitzel), and the many others who've helped along the way to here!

English
Jay Bosamiya retweetledi
Jay Bosamiya retweetledi

Prepare your spectral sensors, arm yourselves with arcane knowledge, and rally your team! On April 12, we venture to the eerie confines of Ashwood Hollow. Can you and your team solve the mysteries of The Plaid Phenomenon? plaidctf.com

English
Jay Bosamiya retweetledi

@adamdoupe Same reaction when I first found out about it too :D
Relatedly, you might be interested in taking a look at zsh-autosuggestions. More of a personal preference thing but I quite like it
English

@jay_f0xtr0t @moyix Have you noticed any performance impacts from this?
English

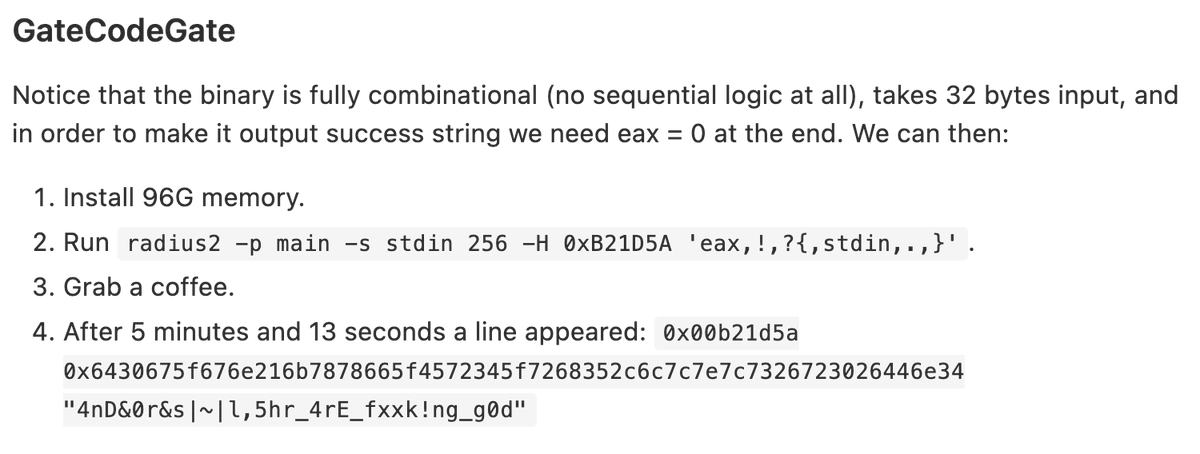
@pr0me @alkalinesec been a while so unclear on details. we had indeed tried simplify in some spots and it hadn’t helped. I don’t recall us trying out too hard applying it, but yeah it was interesting+surprising to see such a stark diff. Def worth investigating. Cool to see radius2 soln tho!
English
@alkalinesec Yea .simplify sounds reasonable, z3 should definitely be capable of finding a solution at some point.
Never worked with boolector myself so I don't have an intuition but the gap seems odd, indeed, might be interesting to investigate
English

wooo someone who isnt me used radius2 to solve a ctf challenge !!! @u4ZhUMkcR7eawpx0VISi8Q/rJ66Pe2v2#GateCodeGate" target="_blank" rel="nofollow noopener">hackmd.io/@u4ZhUMkcR7eaw…
compare this solution to the manual one here github.com/pwning/public-…
English
Jay Bosamiya retweetledi

We just started the #v8CTF: a new exploit bounty program for v8!
* $10,000
* N-day vulnerabilities are in scope, but limited to first submission per deployed v8 version
* unlimited for self-found bugs (on top of regular VRP)
More info here: github.com/google/securit…
English
Jay Bosamiya retweetledi

The Google CTF Finals 2023 are coming! Watch the best CTF teams compete in our custom video game tomorrow, Sunday, 1pm JST. #Hackceler8 #GoogleCTF #Gaming

English

We (@mmm_ctf_team = PPP+TheDuck+MapleBacon) won @defcon CTF again!! Was a fun contest and it was great to play again with MMM friends :) See y’all again next year!

CyLab@CyLab
Carnegie Mellon University’s hacking team, the Plaid Parliament of Pwning, defended its title at the 2023 @DEFCON Capture-the-Flag competition, earning its seventh victory in eleven years. #DEFCON2023 #DEFCON31
English
Jay Bosamiya retweetledi