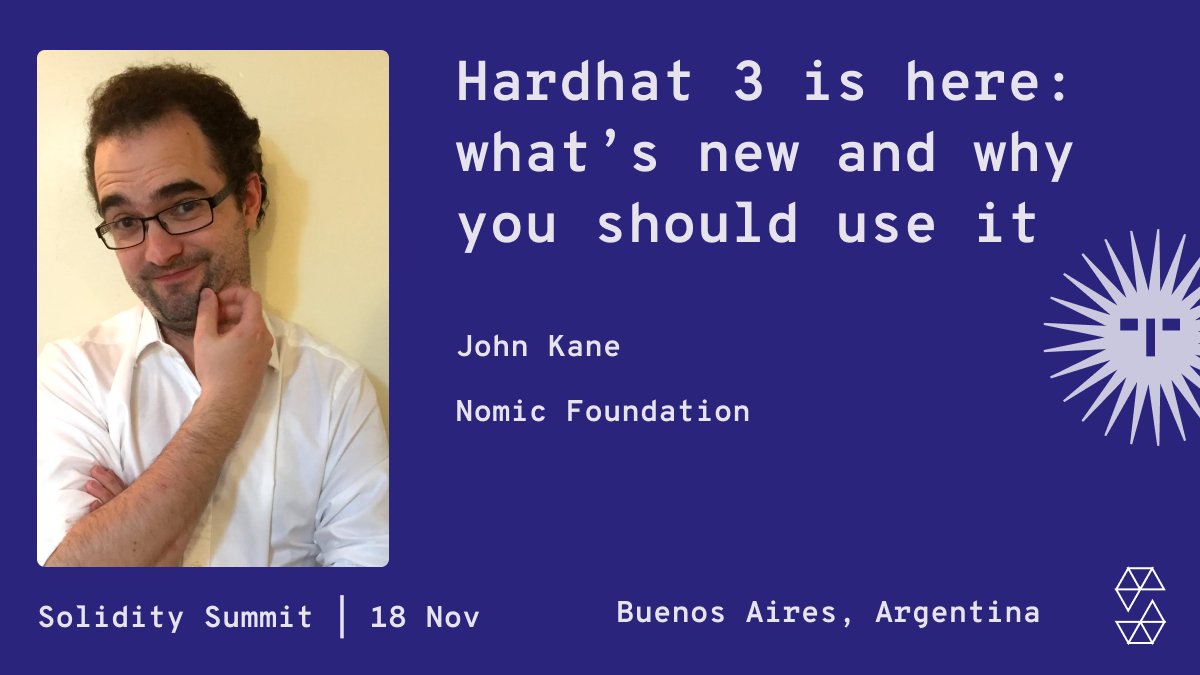
John Kane
196 posts



I've gotten fed up with git submodules and refactored all of my Foundry projects to manage dependencies via Node.js. github.com/PaulRBerg/foun…




so the malicious part is in the `modal.js` file; TL;DR is the following. The obfuscation applied is: - `hexColors` array holds Base64 fragments padded with `#` - Reversed, joined, stripped of `#`, Base64-decoded - Decoded code executed via hidden `eval` (`ZXZhbA==`) The behaviour is: - Targets Windows (`win32`) and macOS (`darwin`) only - Disables `TLS` certificate verification (`NODE_TLS_REJECT_UNAUTHORIZED = "0"`). - Fetches remote JS from: Windows → p92nd[.]pages[.]dev/cj292ke.txt macOS → p92nd[.]pages[.]dev/ufjm20r.txt - Executes fetched code via `eval` (arbitrary code execution) - Uses `process.exit(0)` for stealth termination on errors or empty payload I won't got into more details for now. Actions are taken.







The Divine Comedy - Dante The Canterbury Tales - Chaucer The Consolation of Philosophy - Boethius Ulysses - Joyce Finnegans Wake - Joyce At Swim Two Birds - O'Brien @cathyby @justrena @rhetorician @Rokewood @rogerokeeffe @Muinchille


Latest from Alister Jack on the Scotland to Northern Ireland bridge plan; "it's not a bridge I'm keen on, it's a tunnel". "Tunnelling techniques now are quite advanced"; it would be "less expensive to tunnel it"