june
41 posts


june retweetledi

JWT Pentesting 📂
10 Writeups to Hack with JWTs
1. @musab_alharan" target="_blank" rel="nofollow noopener">medium.com/@musab_alharan…
2. cyberw1ng.medium.com/jwt-attack-vul…
3. book.hacktricks.xyz/pentesting-web…
4. portswigger.net/web-security/j… (Labs)
5. github.com/tuhin1729/Bug-… (Checklist/Methdology)
6. bugbase.ai/blog/all-about…
7. youtu.be/dCajB2xnHAU?si… (leaks from JWT)
8. auth0.com/blog/critical-…
9. blog.intigriti.com/2021/07/27/hac…
10. portswigger.net/bappstore/f923… (Burp Plugin)

YouTube
English
june retweetledi

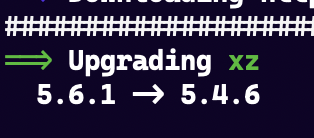
june month open-source journey :
contributed to NixOS organisation
maintaining packages in NixOS/nixpkgs
added 3 new packages in nixpkgs
checkout the awesome package manager github.com/NixOS/nixpkgs
English
june retweetledi

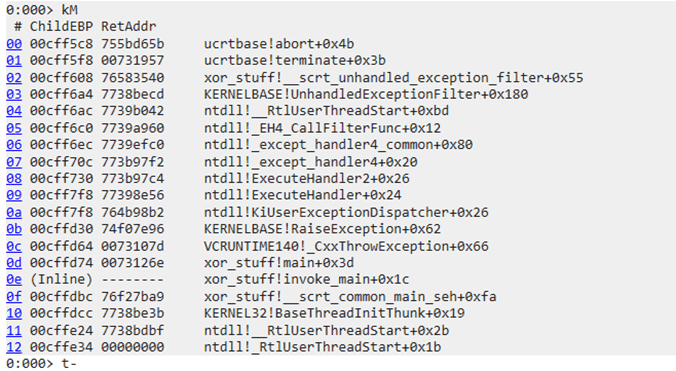
🛠️ How To Use WinDbg For Beginners
🔍 Analyze dumps & trace memory leaks
👀 Ideal for debugging both user & kernel code
🕰️ TTD feature for step-by-step debugging
🧩 Snapshots work even after VM restores
👉guidedhacking.com/threads/how-to…
English
june retweetledi

it can actually already do more than simple challenges. it will automatically solve aeg from pwnable.kr up to control of PC.
the challenge involves a long hex encoded input that must pass many checks after which an unsafe memcpy occurs.
with radius2 it takes no RE
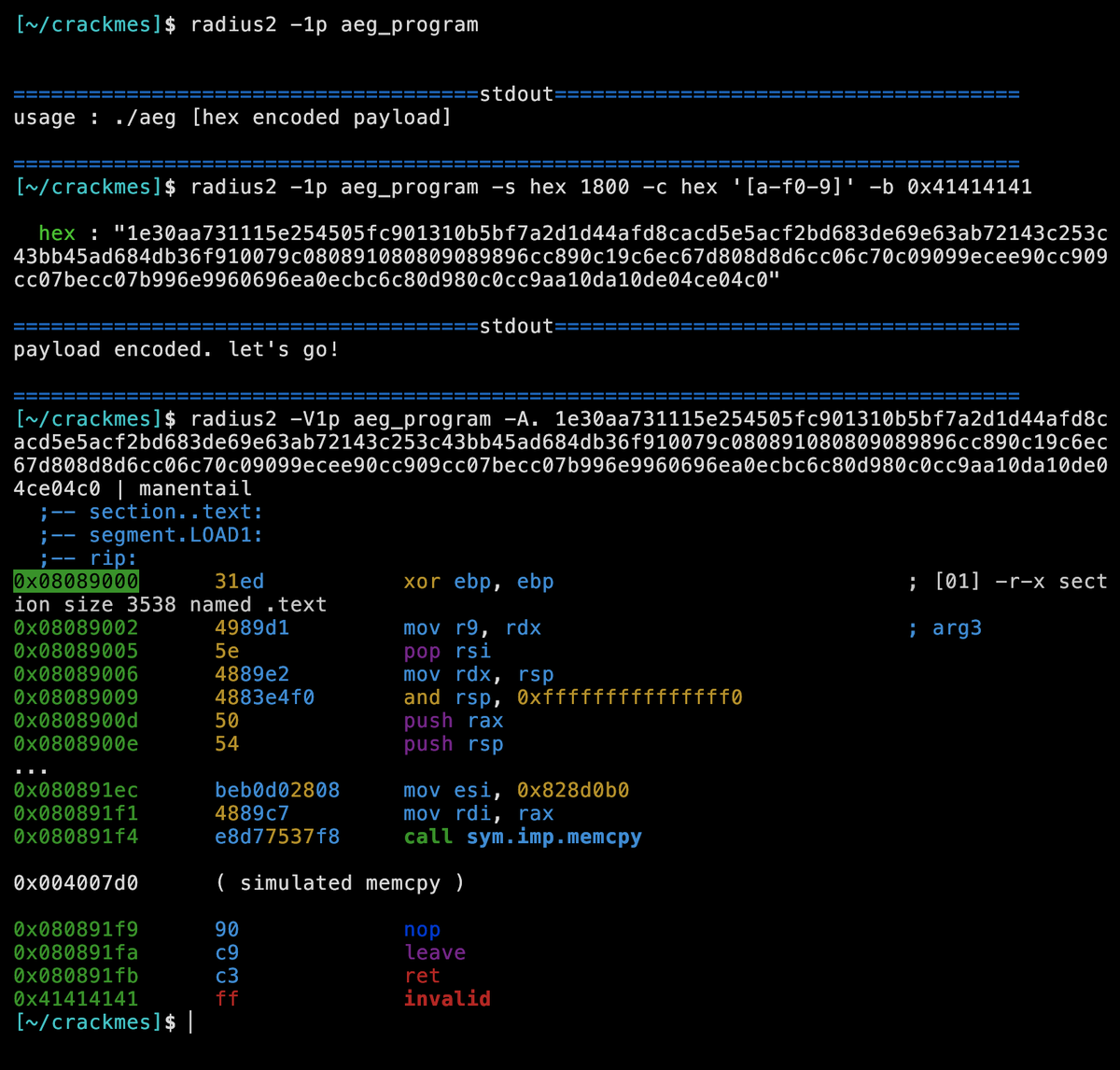
𝚊𝚕𝚔𝚊𝚕𝚒@alkalinesec
havn't worked on radius2 for a bit so i added a line that lets it automatically solve (very) simple pwn challenges
English
june retweetledi
RE tip of the day: When the debugger attaches to the process, it calls the DbgUiRemoteBreakin API. If malware is already running, it can hook this API beforehand to detect the moment the debugger is about to attach.
#infosec #cybersecurity #malware #reverseengineering
English
june retweetledi

june retweetledi

@sunnysora86 @realdiiii Who TF are you then? Listening to Andrew tate and fresh and fit podcast and talk like them? They earned their words and opinions you didn't. Don't be a dick to girls be nice to people
English
june retweetledi
june retweetledi
june retweetledi

My talk, "iObfuscate: Unraveling iOS Obfuscation Techniques" just got accepted at Objective by the Sea! @objective_see
Hope to see you there! #OBTS v6.0

English
june retweetledi

The Complete Cyber Security Course ⚡ #Infosec
~ Part 1
~ Part 2
~ Part 3
~ Part 4
👇FREE Download Link 🖇️ #sR7N0SOy4fz40NpJ4p9AEw" target="_blank" rel="nofollow noopener">mega.nz/folder/j8JzmYj…
English
june retweetledi

Selected as a mentor and project admin of #SpectrumUI in @girlscriptsoc
Do checkout Spectrum UI for contributing in #GSSOC23
github.com/Clueless-Commu…


English
june retweetledi

Found a nice read about malware analysis using #radare2 by my senior @rachejazz
rachejazz.me/2020/03/03/Mal…
Do check out if interested 👇
#malware #cybersecurity
English
june retweetledi

Nice reading for anyone interested in Linux kernel internals and modules development (updated to 5.x kernels)
"The Linux Kernel Module Programming Guide"
sysprog21.github.io/lkmpg/
#Linux


English
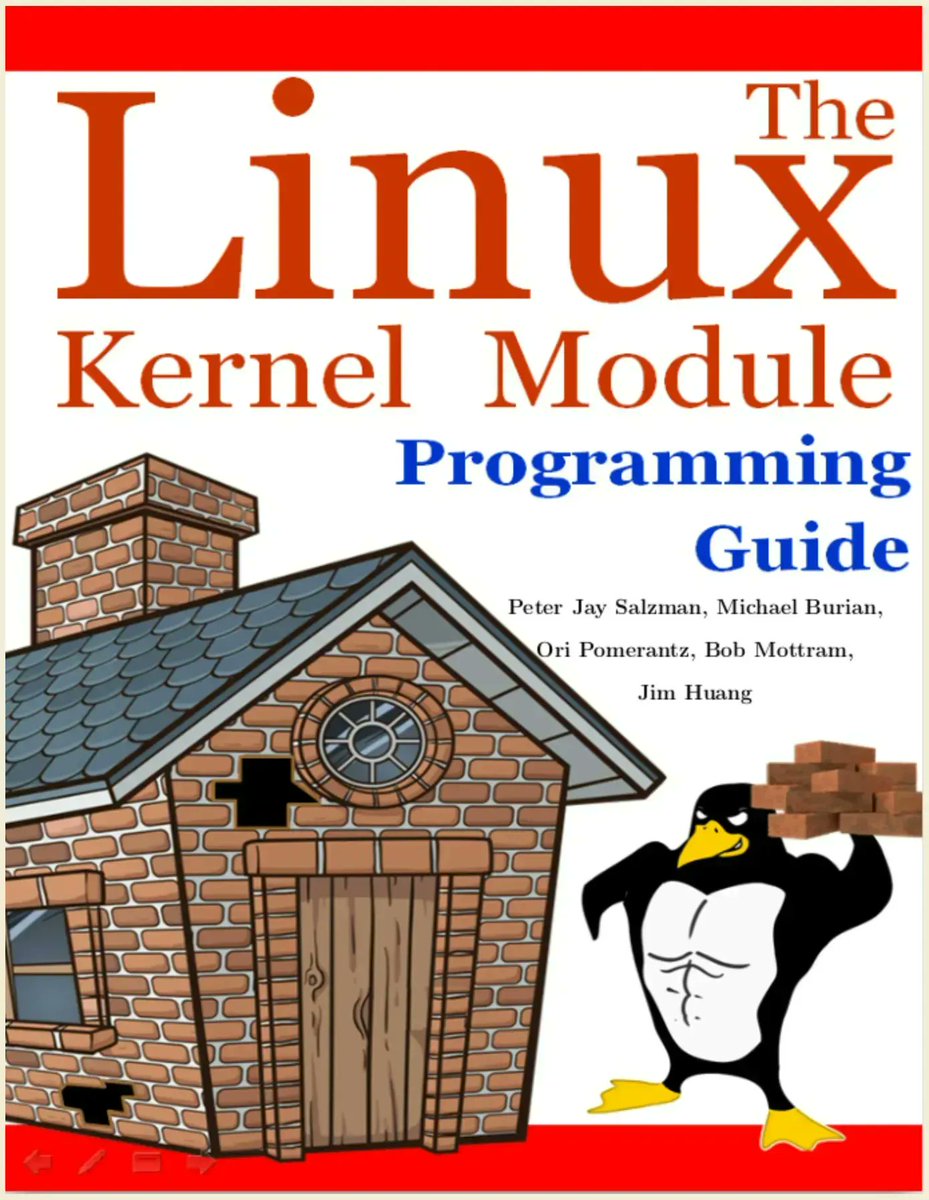
june retweetledi

Very interesting reading on Linux page cache, memory management, mmap and cgroups
(credits @brk0v)
biriukov.dev/docs/page-cach…
#Linux

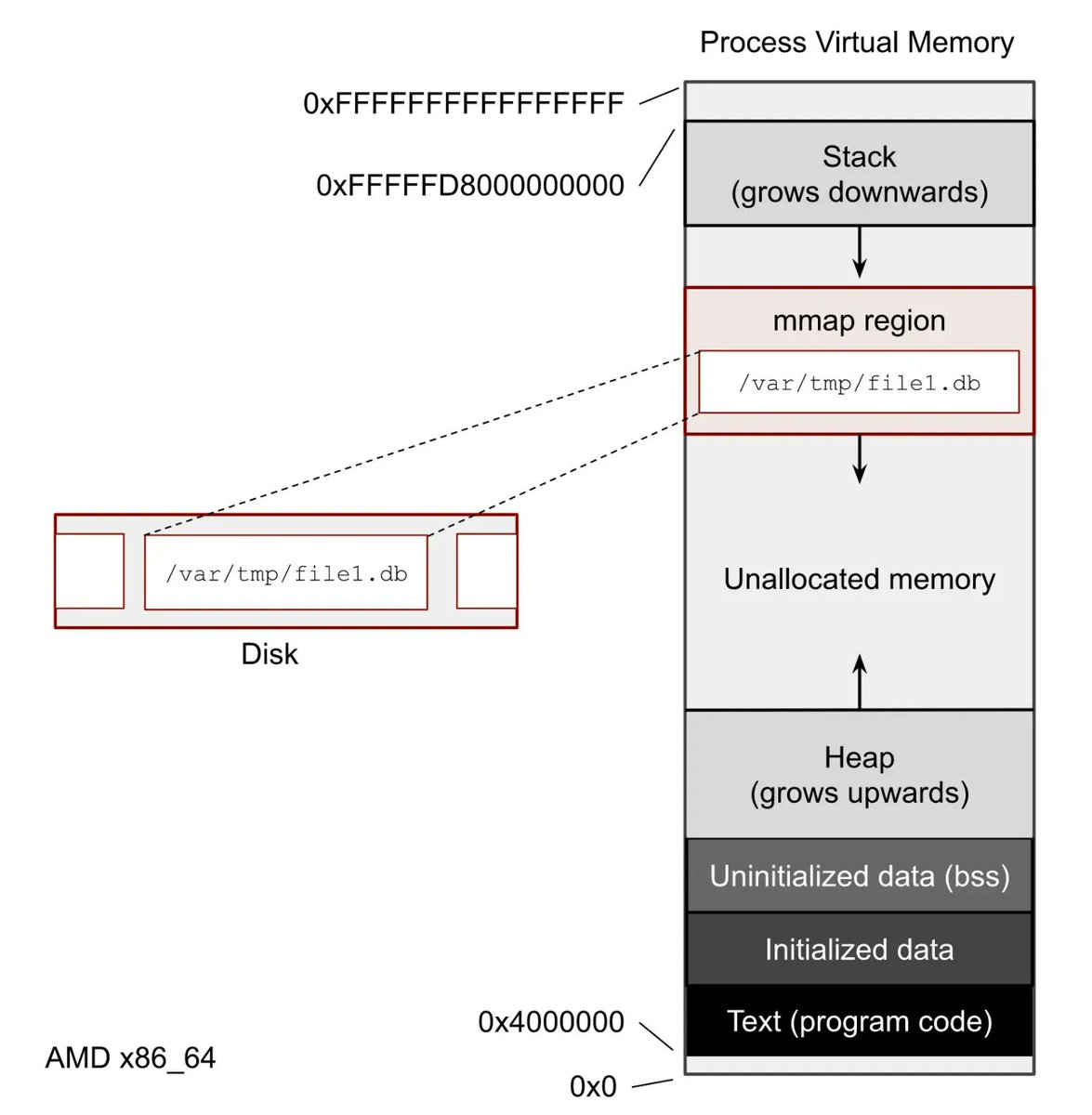
English