Sreeram KL retweetledi
Sreeram KL
2.1K posts


Sreeram KL
@kl_sree
Infosec enthusiast! | @googlevrp fan boy 😍 | CTF @thehackerscrew1 | Web Security
Republic of India Katılım Ocak 2018
922 Takip Edilen2.5K Takipçiler
Sreeram KL retweetledi

Finding Zero-Days with Any Model provos.org/p/finding-zero…
English
Sreeram KL retweetledi

The takeaway: If you don't account for how your cloud provider handles resources internally, you aren't really in control of your data.
Big thanks to the @GoogleVRP team for the quick patches.
Read the full breakdown here:
focalsecurity.io/blog/kicking-t…
English
Sreeram KL retweetledi

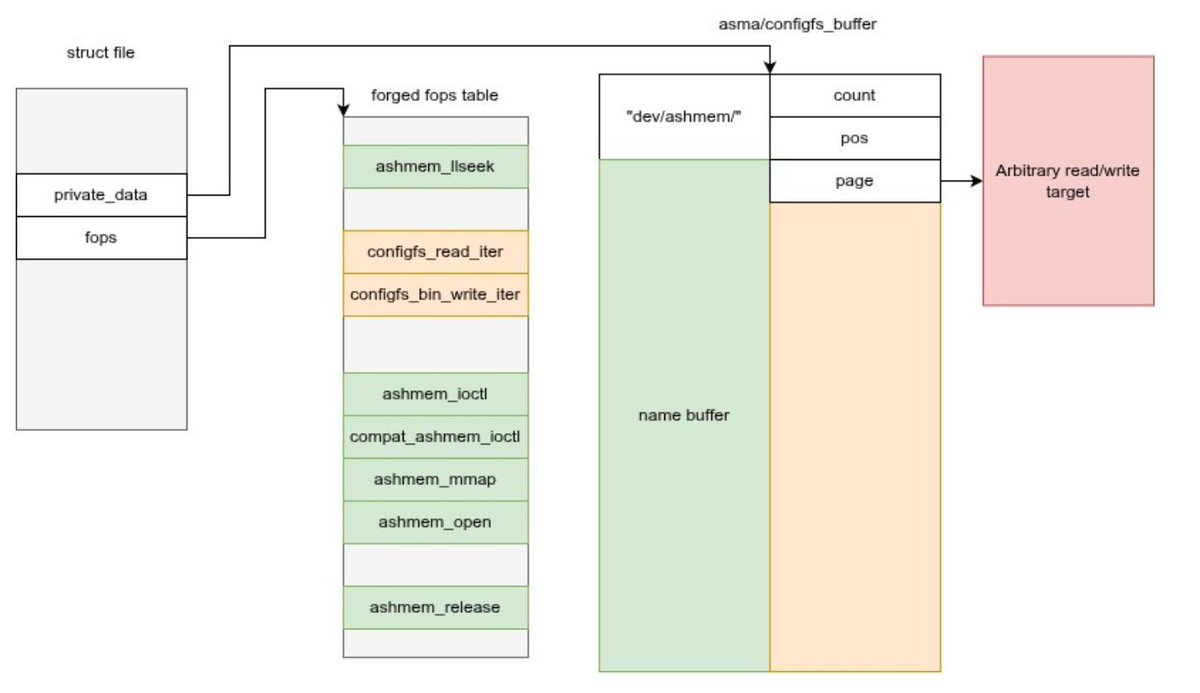
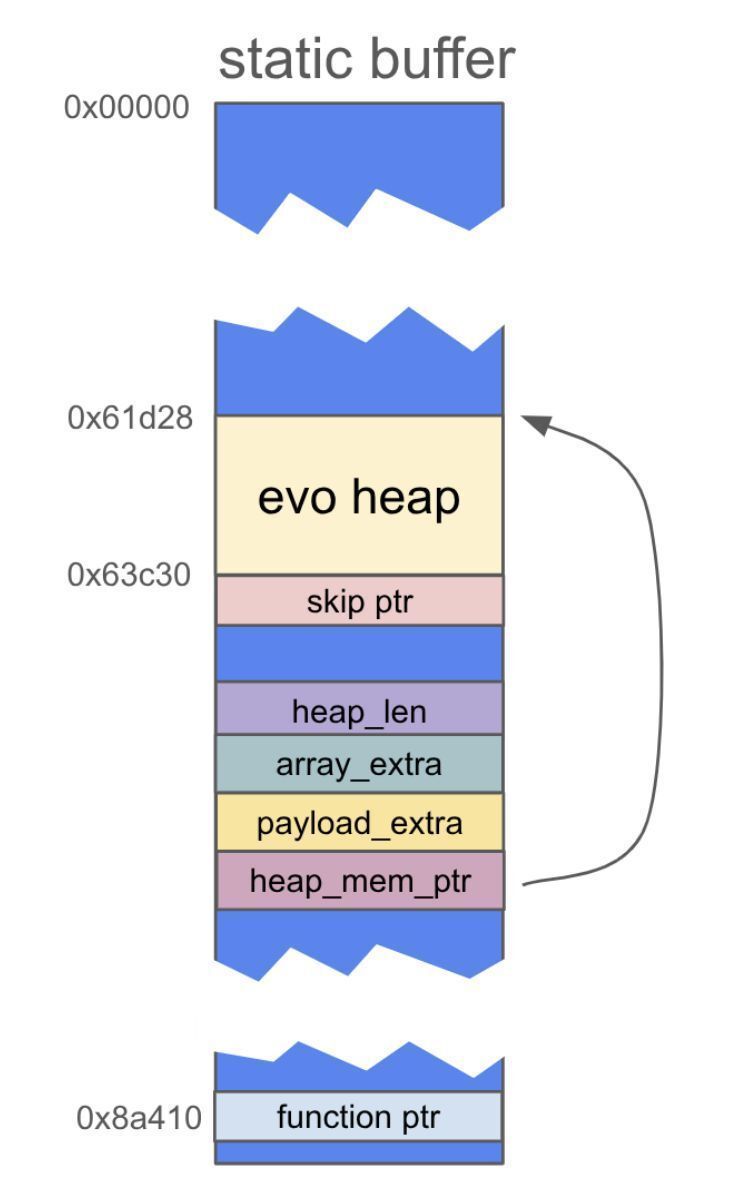
3-parts series on 0-click exploit chain targeting Android Pixel 9
From arbitrary code execution in mediacodec to kernel privilege escalation
Part 1: projectzero.google/2026/01/pixel-…
Part 2: projectzero.google/2026/01/pixel-…
Part 3: projectzero.google/2026/01/pixel-…
Research @natashenka and @__sethJenkins
#infosec
English
Sreeram KL retweetledi
The first version of APIClient has been released chromewebstore.google.com/detail/api-sec… it supports API learning with key tracking based on usage and Google/Swagger discovery documents plus XSS finding also replacement for postLogger extension. It's not perfect, create GitHub issues :)
English
Sreeram KL retweetledi

Race conditions in OAuth flows can still happen in custom implementations. Here's how to find it:
During the token exchange, the server is supposed to treat an authorization code as single-use. If you race the token endpoint by sending parallel requests with the same code simultaneously, vulnerable implementations may issue multiple valid access tokens and some won't properly revoke all of them.
Tools like Turbo Intruder or even a simple multi-threaded script sending concurrent requests to the callback URL with different tokens may trigger it.
Further reading here: blog.avuln.com/article/4
English
Sreeram KL retweetledi

I'm excited to finally publish the writeup for my first @GoogleVRP vulnerability, leaking phone numbers and other sensitive information of Google Support customers (rewarded with a $14k bounty).
michaeldalton.au/posts/hacking-…
English
Sreeram KL retweetledi

We've published a new blog post by RyotaK @ryotkak !
He exploited a directory deletion race condition in Google Cloud's Looker, leading to full RCE and K8s privilege escalation.
Read the technical details here:
flatt.tech/research/posts…
English
Sreeram KL retweetledi
Bug write-up for "Google XSS part 3" ndevtk.github.io/writeups/2026/… \^o^/
English
Sreeram KL retweetledi
Sreeram KL retweetledi

Spent a week testing AI for vulnerability research. 14 confirmed bugs in 20 min on one target. 5% hit rate on a hardened one. Same AI, same setup. 4 approaches, what worked, what failed, why target selection matters more than model sophistication. xclow3n.github.io/post/7

English
Sreeram KL retweetledi
Sreeram KL retweetledi

Fascinating account takeover chain discovered in Facebook mobile app by @samm0uda
Multiple vulnerabilities combined:
* Predictable random numbers
* XSS in the JavaScript SDK
* Frame protection bypass
* Login CSRF
One malicious link = full account compromise
Meta paid a $66k bounty for this one.
ysamm.com/uncategorized/…
English
Sreeram KL retweetledi

If you're running AI agents for hacking/research (you should), one of the coolest tips we got from dawgyg is to make them log what failed too. Brain dump it every few minutes to a file, everything it tried, everything that didn't work.
Without it, agents loop back into the same dead ends and you won't notice until you've wasted a ton of time. If the agent cracks something and you only see the result, you've got nothing for next time.
Also: never let them delete files.
For Chrome specifically, dawgyg only uses Gemini because it's the only model with enough context window to trace a code path across hundreds of files without losing state. RCA that used to take 1-2 hours manually now takes about 2 minutes with AI help.
English
Sreeram KL retweetledi

GCP VRP Secrets? 🤫 Hear from the program leads! Michael Cote (linkedin.com/in/michaelpatr…) & Darby Hopkins (linkedin.com/in/darbyhopkins) join @ctbbpodcast to talk shop: killer report tips, program insights & boosting your bounty game on Google Cloud.
🎧 youtu.be/7u6xpVhEpBA
#GoogleVRP #BugBounty #CloudSecurity #GCP

YouTube
English
Sreeram KL retweetledi
Android Vulnerability Reproduction with OpenClaw mp.weixin.qq.com/s/ueEFKrQCKFJp…
English
Sreeram KL retweetledi

Added 3,600+ publicly disclosed HackerOne reports that paid a bounty to the MCP.
👇
github.com/PatrikFehrenba…
This should help Claude to decide where to focus on, what attack surface was looked at before, and where new vulnerabilities could be 👀 (in theory 😏)
English
Sreeram KL retweetledi

alright guys, @Rhynorater made me do it. we break down everything you need to know about claude code skills for hacking in the episode that drops next week on the @ctbbpodcast. you're gonna love it.
English
Sreeram KL retweetledi

Here’s my write-up on a code execution in Google Gemini CLI.
@dhiraj_mishra/code-execution-in-google-gemini-4e5909ec167d" target="_blank" rel="nofollow noopener">medium.com/@dhiraj_mishra…
#infosec

English



