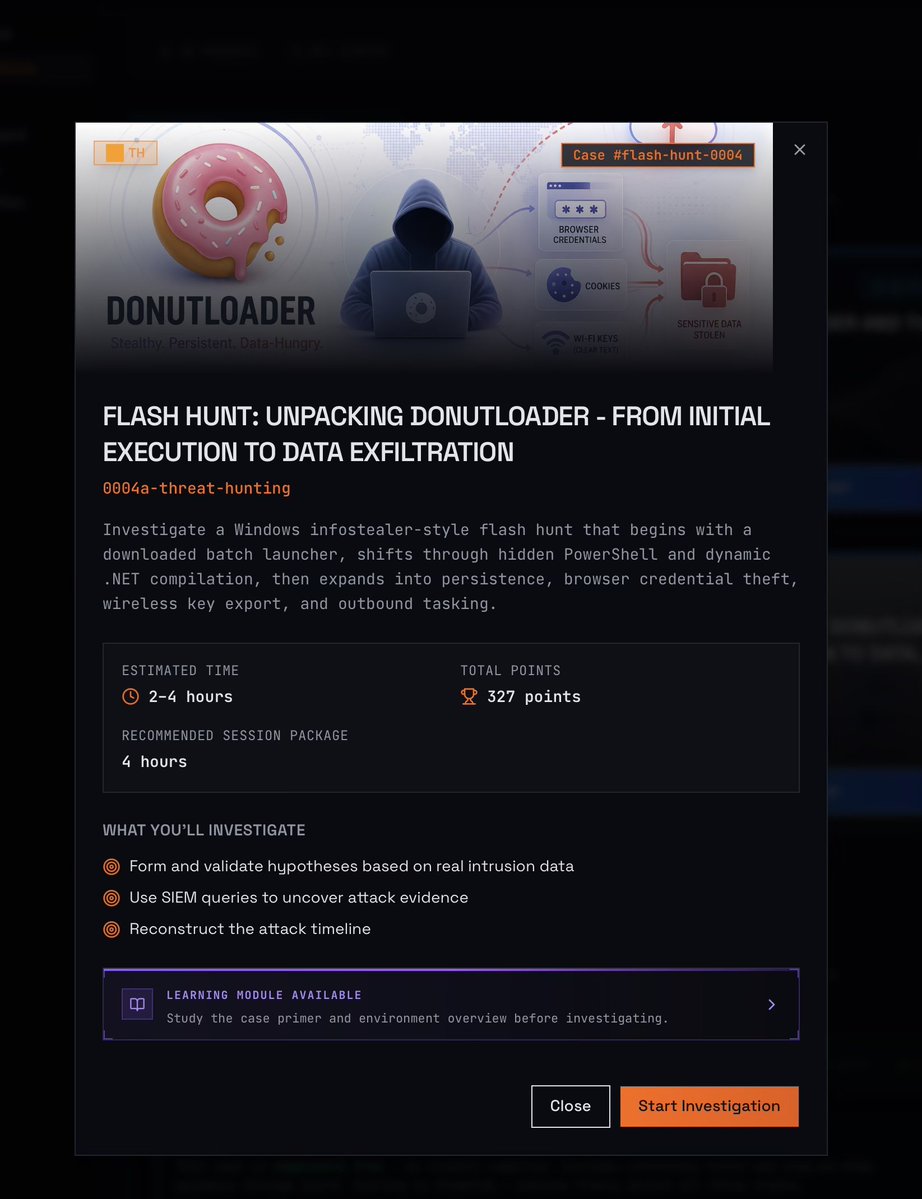
Launching today: Threat Hunting Labs private threat intelligence feed THL enterprise customers now get access to a dedicated intel feed built around high-fidelity IOCs curated by our team, structured in STIX 2.1 and delivered over TAXII 2.1. It integrates directly with your SIEM or security tooling. Signed webhooks if you want push delivery. No noise layers on top. Included free for enterprise customers in year one. If you're already a THL customer, reach out and we'll get you set up. If you're not, this is a good time to ask what that looks like. 👉 intel.threathuntinglabs.com