G2 retweetledi

A detailed analysis of the @GMX_IO attack.
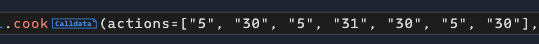
(1) The "refund" logic makes a malicious -> The attacker jail-break the restrictions to perform multiple actions in 1 transaction.
As my previous tweet analyzed, the attacker fooled the frontend (the keeper bot) to hijack the control flow.
When a normal user positions an order, the system works as:
- tx1: user (eoa) send ETH (gas) to keeper;
- tx2: keeper (off-chain bot) calls `decreasePosition`, and refund eoa.
However, in this attack case:
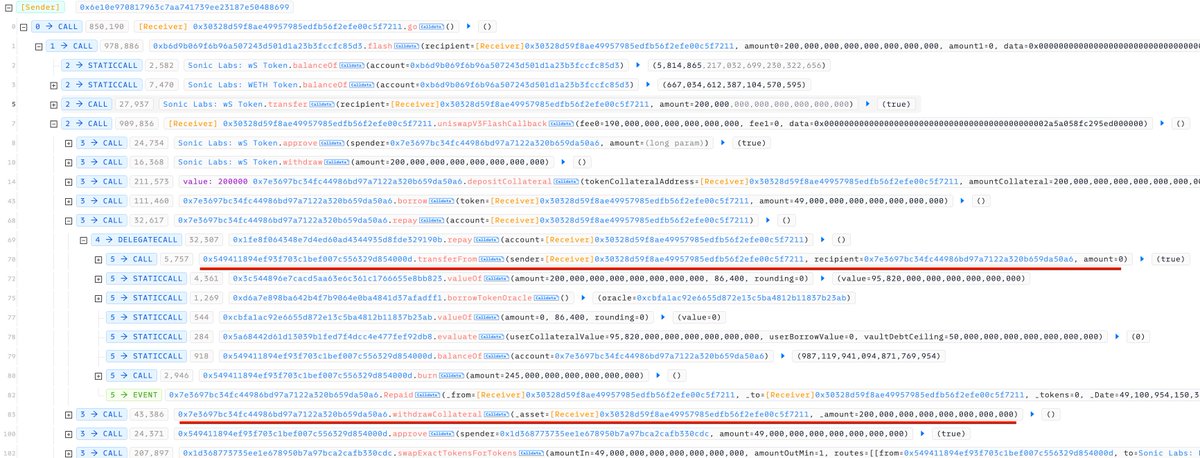
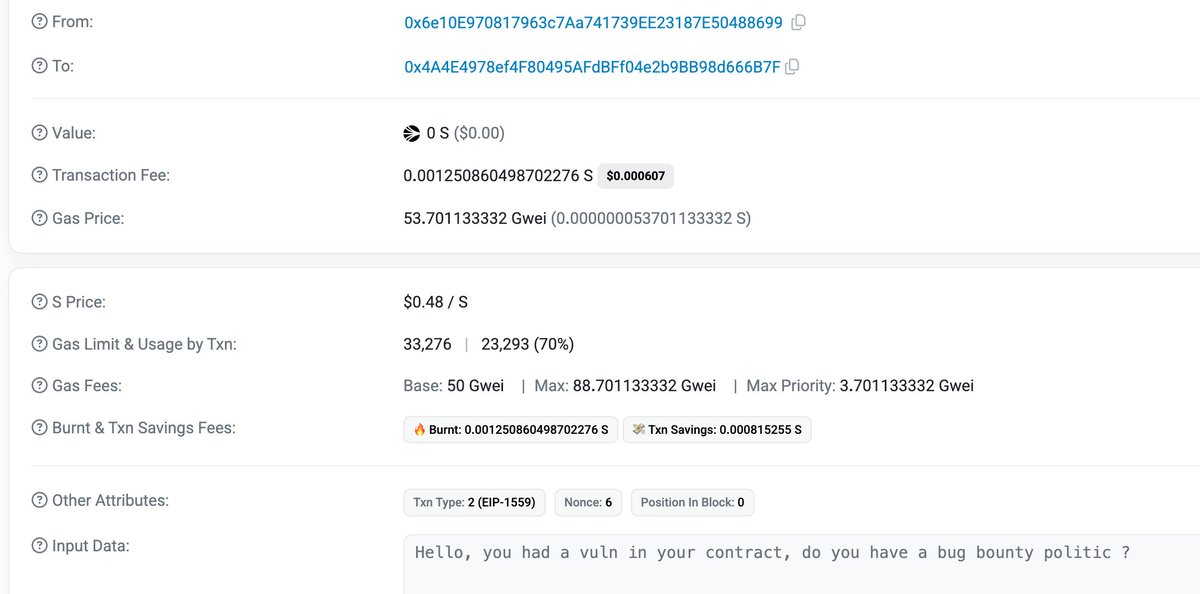
tx1: user (malicious contract) send ETH (gas) to keeper; tx2: keeper calls `decreasePosition`, and refund malicious contract.
--> This makes the control flow hijacked by the malicious contract at the middle of an execution.
Side note:
Any user can import a smart contract address into rabby wallet to fool the frontend to treat a contract address as a normal user.
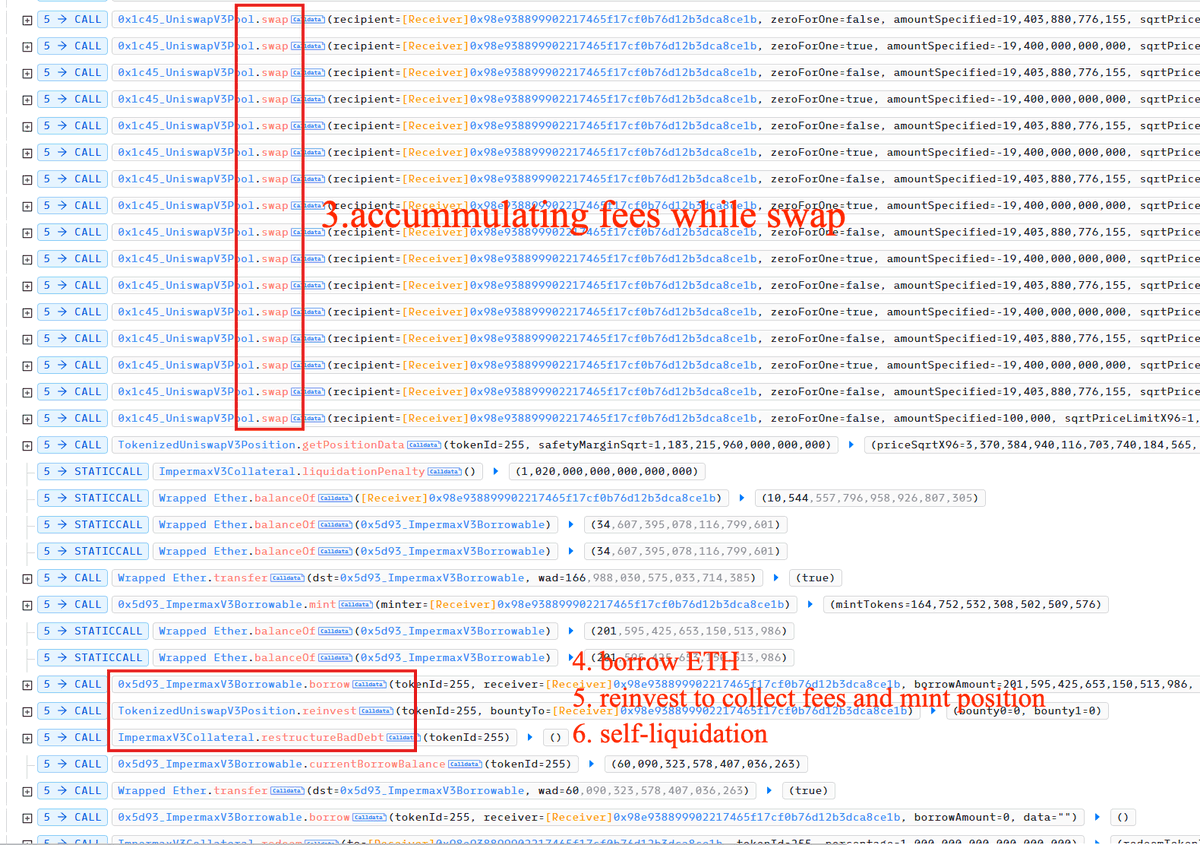
(2) Manipulation of GLP's price
The second part of the attack is simple. there're mainly 3 actions:
- A. mint GLP.
- B. open short position.
- C. withdraw GLP.
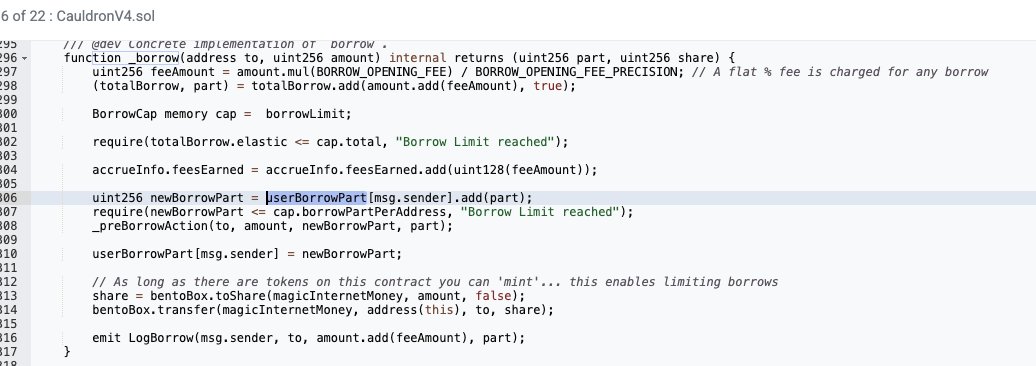
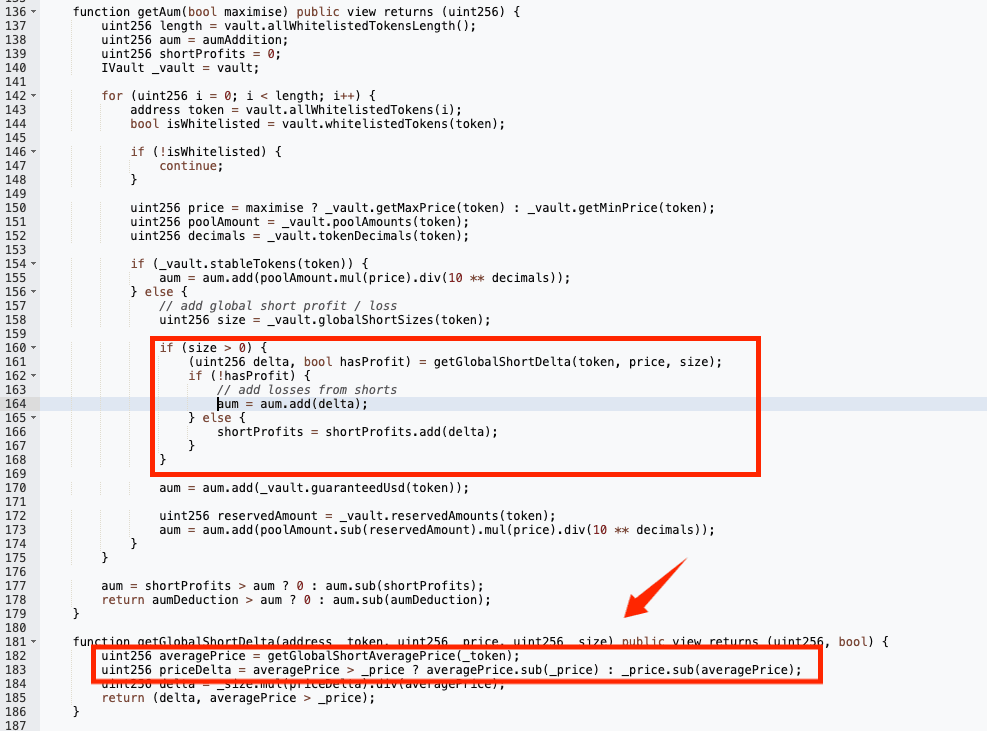
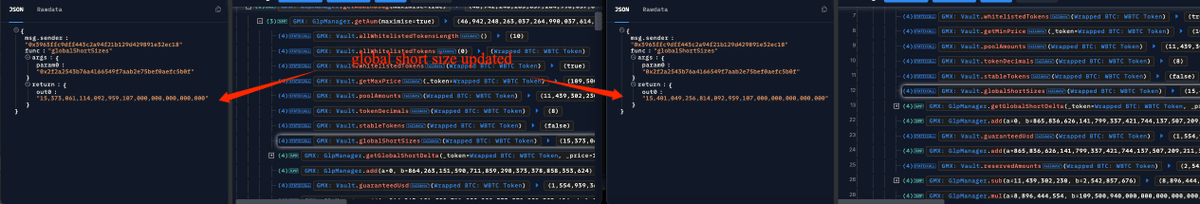
The AUM calculation (P1) also checks the total short position in the markets. Although the total short size is updated in step B (P2), the average short price was not updated. This fools the system to think the short position was opened at the previous average price (a much lower one, P3). and thus the AUM is considered larger.
It's like the attacker was able to open a "virtual" short position at a much lower price to make GLP think it earned a lot (but in fact didn't).
This makes a difference in the price of GLP between minting and withdrawing.
The attacker withdrew multiple times to multiple assets to drain the entire GLP pool.

English