Nelson Chinonso
775 posts


@mcloxyventures
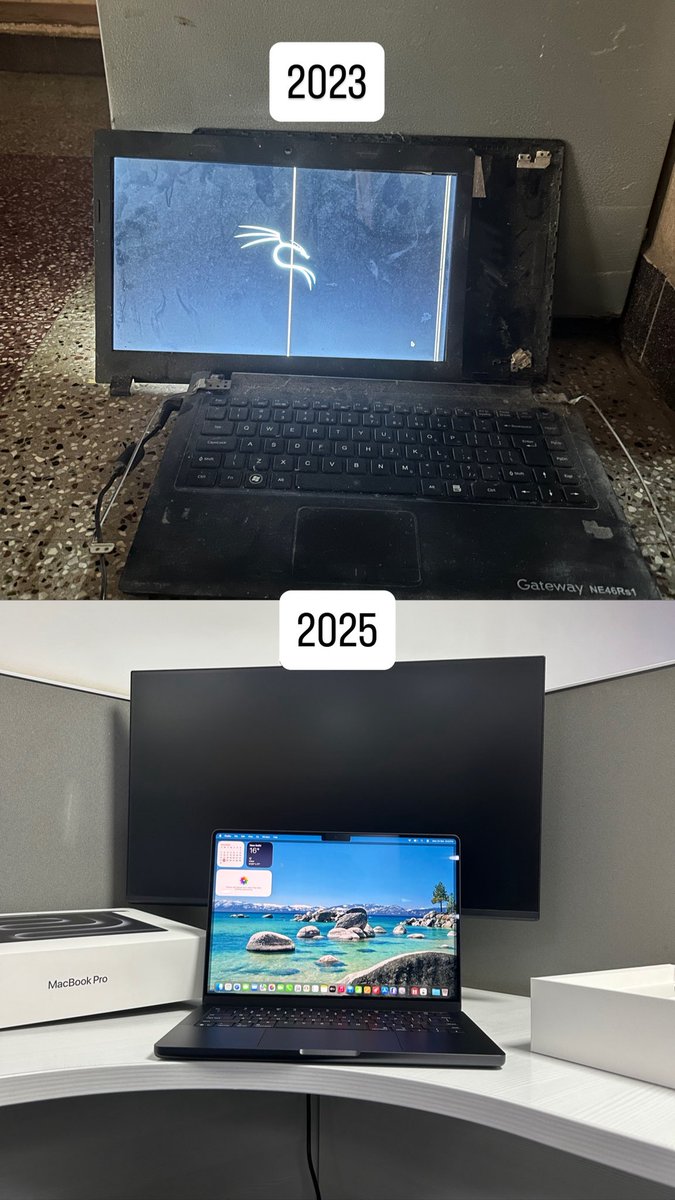
5× Award🏆 winning Interiors Decor brand, Biochemist🧬🩺, cybersecurity instructor.





API Security Person of the Year is trending ke????? LMAOO I NEVER SEE THIS KAIN THING BEFORE🤯🔥 Twitter cyber security community >>>>>>>>>>>>>>>>>>>>>>>


Following yesterday’s Cybersecurity space on X, I have decided to support Jeremiah @cyberjeremiah until he gets his first Cybersecurity job. By God’s grace, you will get a Cybersecurity job in 2026. You will excel and thrive in this field 🙏🏾






One of my goals for next year is to get a fully sponsored scholarship for an MSc in Cybersecurity. Also, if you know of any scholarship opportunities for an MSc in #Cybersecurity, or know of any scholarship that can be beneficial to people, please drop them in the quotes and comments. Let's make this a thread of scholarship opportunities.


How AI Help Hackers Break Companies in Seconds