Sabitlenmiş Tweet
ikajakam
10K posts


ikajakam
@mechanisedbeat
Indian 🇮🇳 VAPT | GRC | ISO 27001 Lead Implementer
Katılım Mayıs 2009
976 Takip Edilen339 Takipçiler

@HackzYash Program sent you money as crypto on binance?
Un connected dots
English

Got $4,300 bounty from 2 programs 💰
Not a single bug — just connecting dots.
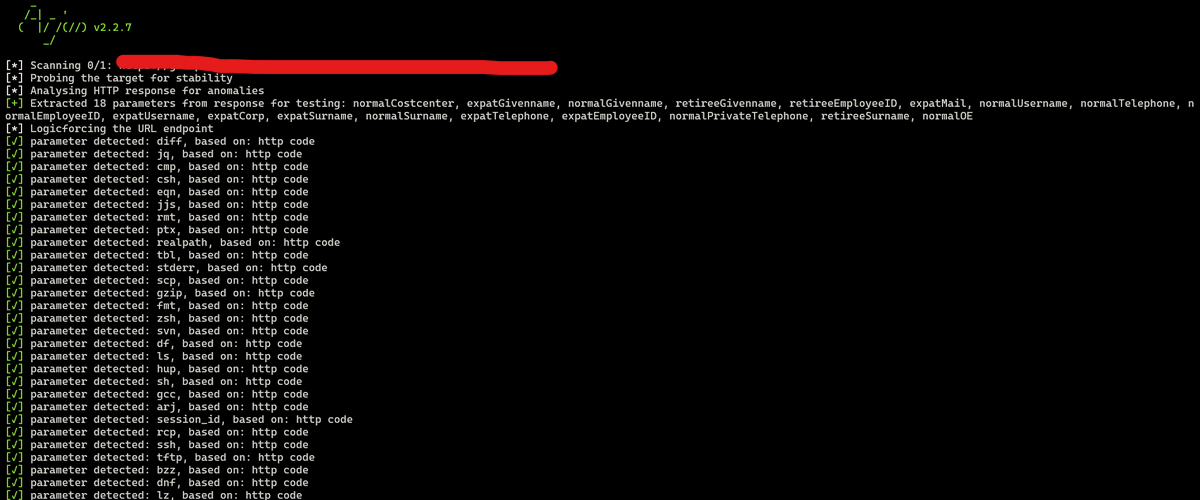
Using GhostJS (TrinetLayer) for recon:
Found
→ AWS secrets in JS
→ Hidden APIs
Then:
•LFI
•IDOR (invoice & profile)
•PII exposed
Small issues → big impact.
#BugBounty #CyberSecurity #
English

sources
portswigger.net/web-security/c…
book.hacktricks.wiki/en/pentesting-…
owasp.org/www-community/…
intigriti.com/researchers/bl…
sec.stealthcopter.com/intigriti-july…
realansgar.dev/writeups/intig…
bugology.intigriti.io/intigriti-mont…
mizu.re/post/intigriti…
sudistark.github.io/2024/12/19/Int…
English

How to automate bug bounty tasks:
- Pick a target.
- Use your methodology and write down every action you take.
- Once you are finished, check the list and ask yourself which actions you repeated multiple times.
- Use AI to write mini-scripts to automate those specific actions.
Thank me later.
English


full credits to @rez0__
Cloned his ffuf Claude skill to use with Gemini CLI
github.com/ikajakam/Gemin…
Also he is doing masterclass on ffuf for critical thinkers @ctbbpodcast
#ai #ffuf #bugbounty #ctbb
English

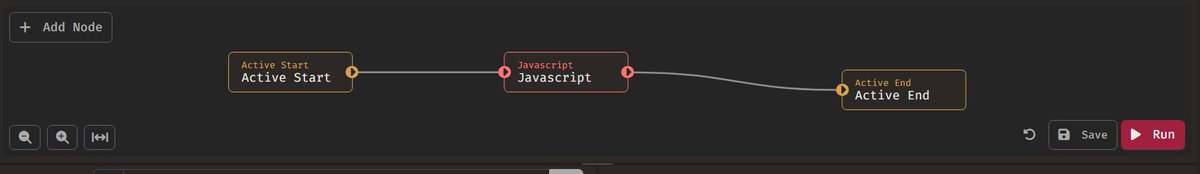
Loving @CaidoIO workflows
Active workflow lets reply same request as ACCOUNT B ON DEMAND (with stored variable token). Testing Cross Tenant IDOR gets super easy. also logs helps with confirming workflow works as desired #bugbounty #idor #accesscontrol #caido #js

English
ikajakam retweetledi
ikajakam retweetledi

How I reverse-engineered an Android app, bypassed custom encryption layer, achieved server-side RCE, and earned a $5000 bounty. read the full story here (TLDR; but worth reading)
blog.voorivex.team/from-an-androi…

English
ikajakam retweetledi

API Pentesting Series — Part 8 is LIVE!
If you can’t discover APIs, you can’t hack them.
Simple as that.
In this chapter, I broke down:
🔸 Passive Recon → GHDB, CT logs, GitHub
🔸 Active Recon → DevTools, JS mining, mobile app analysis
🔸 Swagger/OpenAPI hunting
🔸 Kiterunner + API wordlists
🔸 Discovering hidden versions (v1, v2, internal)
🔸 Mapping & validating endpoints the right way
🔸 Tools, labs, notes, and modern workflows
Most API bugs don’t hide inside the endpoints you see.
They hide in the ones you weren’t meant to find.
This chapter teaches you exactly how to find them.
If you want:
✓ More targets
✓ More bugs
✓ Higher severity
✓ Better methodology
Then Part 8 will change how you hunt APIs.
🔥 Read the full notes here: aacle.notion.site/API-Pentesting…

English
ikajakam retweetledi

Stop looking for id=1. Start looking for the logic flaws scanners miss. 🛑
Basic IDORs are dying. Modern apps use GUIDs (550e8400-e29b...) to hide data. But obscurity isn't security.
Here is the blueprint for finding Advanced Broken Access Control in 2025. 🧵👇 #bugbountytips #infosec
English