mHow
1.5K posts



@mh0ward @XorNinja From a friend who found this using LLMs:
"...to be interpreted as actual format
specifiers, resulting in the leakage of information, or in a crash, or possibly in arbitrary memory writes"
cgit.git.savannah.gnu.org/cgit/nano.git/…
English

We asked Claude to find a bug in Vim. It found an RCE. Just open a file, and you’re owned. We joked: fine, we’ll switch to Emacs. Then Claude found an RCE there too.
Full story: blog.calif.io/p/mad-bugs-vim…
English
mHow retweetledi

Huge Anthropic leak just dropped: the entire Claude Code CLI source is now public.
A misconfigured .map file in their npm package exposed a direct download link to the full unobfuscated TypeScript codebase from Anthropic’s own R2 bucket.
Discovered by Chaofan Shou (@Fried_rice), the dump is massive 1,900 files, 512,000+ lines including the complete tool system, 50+ slash commands, multi-agent coordinator, React/Ink terminal UI, IDE bridge, permission engine, and several unreleased features.
Full repo is live on GitHub(@nichxbt ):
github.com/nirholas/claud…
Clean mirrors are already up for easy browsing(@baanditeagle):
cc-poster.vercel.app
cc-hidden-deploy.vercel.app
It’s spreading fast, the entire dev community is already tearing through it.
Chaofan Shou@Fried_rice
Claude code source code has been leaked via a map file in their npm registry! Code: …a8527898604c1bbb12468b1581d95e.r2.dev/src.zip
English
mHow retweetledi
We found a critical vulnerability in @OpenAI Codex affecting all Codex users, allowing exfil of a victim’s GitHub tokens to our C2 server. This granted lateral movement and R/W access to a victim’s entire code base 😈
This was a crazy one by @crew7sec at @btphantomlabs
BeyondTrust Phantom Labs™@btphantomlabs
Breaking: Newly uncovered OpenAI Codex vuln enables command injection via GitHub branch names in task creation requests. Attackers could steal GitHub user access tokens & sensitive data. Full breakdown by Tyler Jespersen: lnkd.in/ewdTaiEa #OpenAI #BTPhantomLabs
English
mHow retweetledi

@amal and @DangerousThings is doing something fun,
proxmark3.app
Interactive webshell, needs #chrome #edge to work
English

So we’ve gone from coal miner scrip to digital miner scrip…
Corey Quinn@QuinnyPig
AWS proposes a compensation model where engineers receive AWS credits on top of their base salary.
English

@Motor1com Any idea if the new Tremec 6spd manual will be a factory option yet?
English
mHow retweetledi

After 5 months of development, I'm releasing EvilWAF v2.4 - a MITM proxy that makes ANY tool bypass WAFs github.com/matrixleons/ev…
English
mHow retweetledi

I finally let Claude do my pentest this week. Full 5-day engagement, zero human input. Here's what the client got: 😏
clawd.it/posts/10-repla…
#bugbounty #pentesting #AI #cybersecurity #infosec #claudeai
English
mHow retweetledi

Look.. it's a Conditional Access policy simulator built by an infra architect guy who got tired of squinting at What If results 🫠 Shiny graphs yay! 🔗ca.haakonwibe.com No sign-in needed, click Sample Data and play around. Or connect to your own data - all's in browser.
GIF
English
mHow retweetledi

@thedawgyg If you’re completely new to exploit dev, this is probably worth taking a look at: corelan.be/index.php/arti…
It’s fairly old at this point and for 32-bit, but still good for learning concepts and bypass techniques. For example, chaining ROP gadgets is still relevant.
English

So maybe this will work lol... I am looking to find some people (or person) that know about exploit dev. I can find the crashes/vulns but I dont know how to take the info and then create an exploit (POC exploits, not looking to make malicious exploits). Anyone out there that has the experience in taking library/software bugs/vulns and turning them into the chains needed willing to work with me to help me learn? Would be down to work out agreements to make sure its worth the time and effort of course for all involved, as i know this is likely something that will take alot of effort. #bugbounty #exploit #exploitdev #0day
English
mHow retweetledi

WSL2 is a powerful attacker hideout because it runs as a separate Hyper-V VM, and defenders rarely monitor it.
Daniel Mayer explains how attackers pivot into WSL2 and what it took to build tooling that works across WSL2 versions.
Read more ⤵️ ghst.ly/45fPUma
English
mHow retweetledi

Today, Project Zero released a 0-click exploit chain for the Pixel 9. While it targets the Pixel, the 0-click bug and exploit techniques we used apply to most other Android devices.
projectzero.google/2026/01/pixel-…
English
mHow retweetledi

Man behind in-flight Evil Twin WiFi attacks gets 7 years in prison bleepingcomputer.com/news/security/…
English
mHow retweetledi

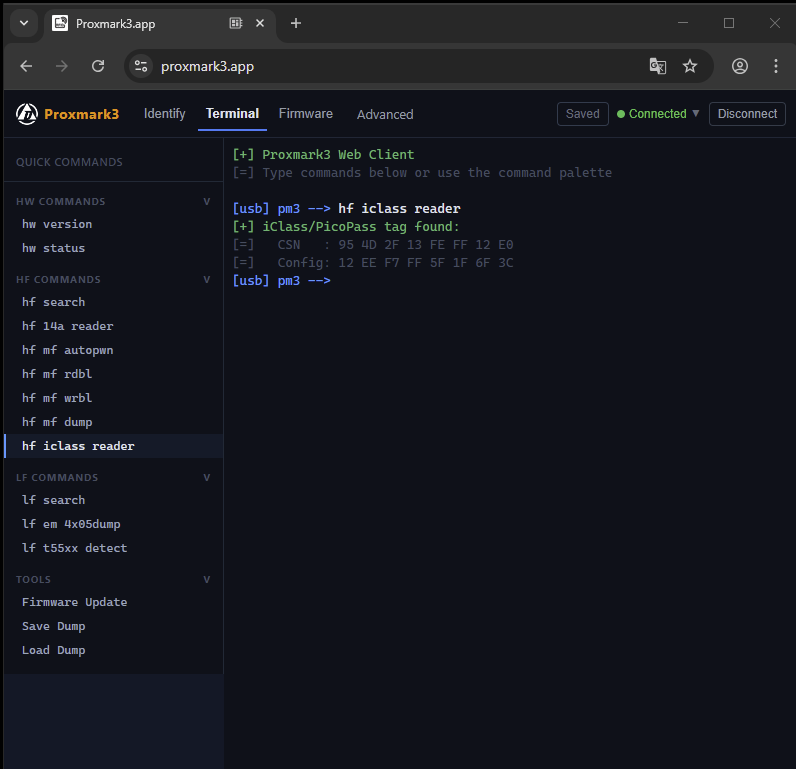
Cloudflare hides 19.3% of all websites—but not perfectly.
CloudRip scans subdomains to find IPs not behind Cloudflare protection, exposing the real origin server:
hackers-arise.com/web-app-hackin…
@three_cube
English
mHow retweetledi

mHow retweetledi
mHow retweetledi

When testing GraphQL APIs make sure to run graphw00f (github.com/dolevf/graphw0…) to fingerprint the specific GraphQL implementation the application is running. Then you can review the Threat Matrix to get likely attack vectors.
English