mhoste retweetledi

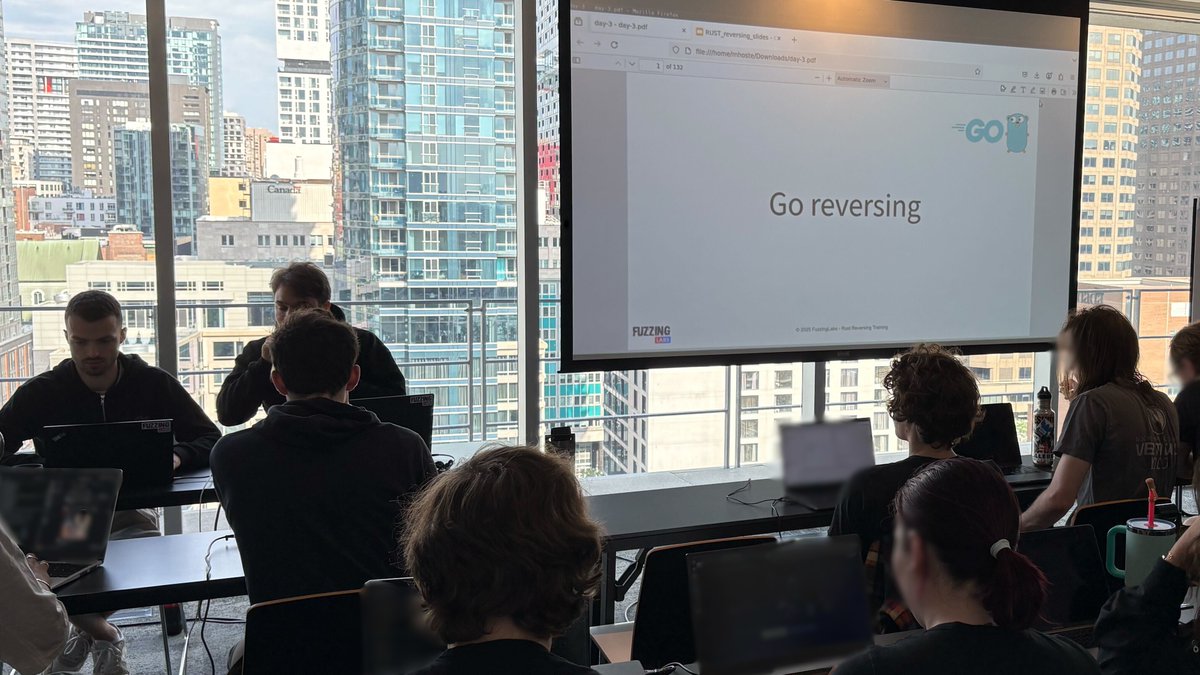
Day 3 (out of 4) of our "Reversing Modern Binaries" training at REcon Montreal is kicking off!
👨🏫The energy and insights from this group have been amazing.
Couldn't join us in Montreal? Your next chance is coming up at the @POC_Crew conference in Seoul this November! 🇰🇷
🚨 FINAL CALL! There are only 5 days left to get the early-bird discount. Register before June 30th to get the discount.
Discover the Seoul training program👉 fuzzinglabs.com/p0c-2025-rever…
Register👉#registration" target="_blank" rel="nofollow noopener">powerofcommunity.net/#registration
#ReverseEngineering #InfoSec #Training #REcon #Montreal #POC2025 #Seoul #Rust #Go
English