APK-47
1K posts

APK-47
@midnight_comms
#osint #android #DFIR
all up in your DEX Katılım Mayıs 2019
282 Takip Edilen1.1K Takipçiler
APK-47 retweetledi

The FLARE team now freely distributes its quality reverse engineering and malware analysis educational content at github.com/mandiant/flare…. Launched with:
- Malware Analysis Crash Course
- Go Reversing Reference
- Intro to TTD
English
APK-47 retweetledi
APK-47 retweetledi

This is going to be a big one.
Dominic Alvieri@AlvieriD
The City of Los Angeles was breached The Los Angeles Metro Transit System has also been breached and is now in shutdown mode 2 Bay Area cities in California are also currently in a states of emergency after separate ransomware attacks 1 hospital breached
English
APK-47 retweetledi

New blog post: Building a Pipeline for Agentic Malware Analysis
Agentic RE + malware analysis with custom skills, MCP tooling, and persistent case state to automate intial triage
Link: synthesis.to/2026/03/18/age…
Github: github.com/mrphrazer/agen…

English
APK-47 retweetledi

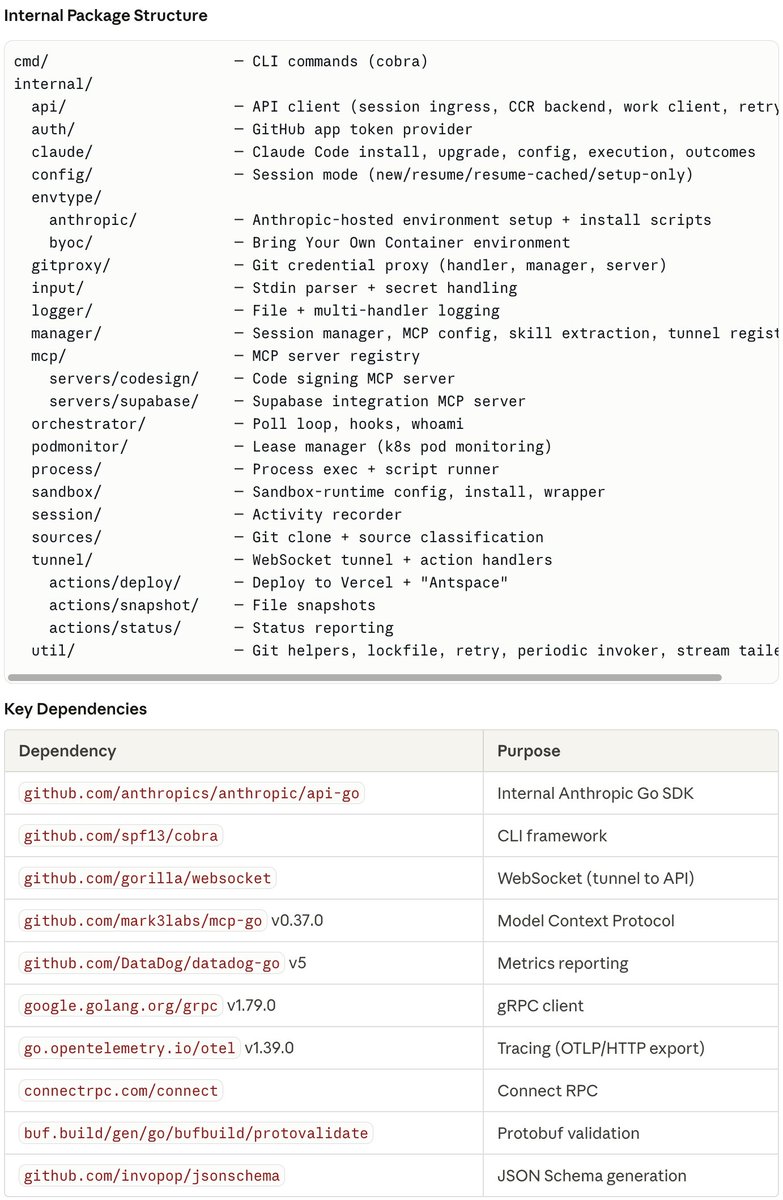
🧵 I just reverse-engineered the binaries inside Claude Code's Firecracker MicroVM and found something wild:
Anthropic is building their own PaaS platform called "Antspace" (Ants + Space).
It's a full deployment pipeline — hidden in plain sight inside the environment-runner binary. Here's what I found 👇
English
APK-47 retweetledi
APK-47 retweetledi

Iran-linked Handala Hack (aka Void Manticore, COBALT MYSTIQUE) is a reported vector for an increase in wiper attacks. This Insights blog details proactive recommendations for security teams, from identity management to enhancing security controls. bit.ly/4rrBVlu

English
APK-47 retweetledi

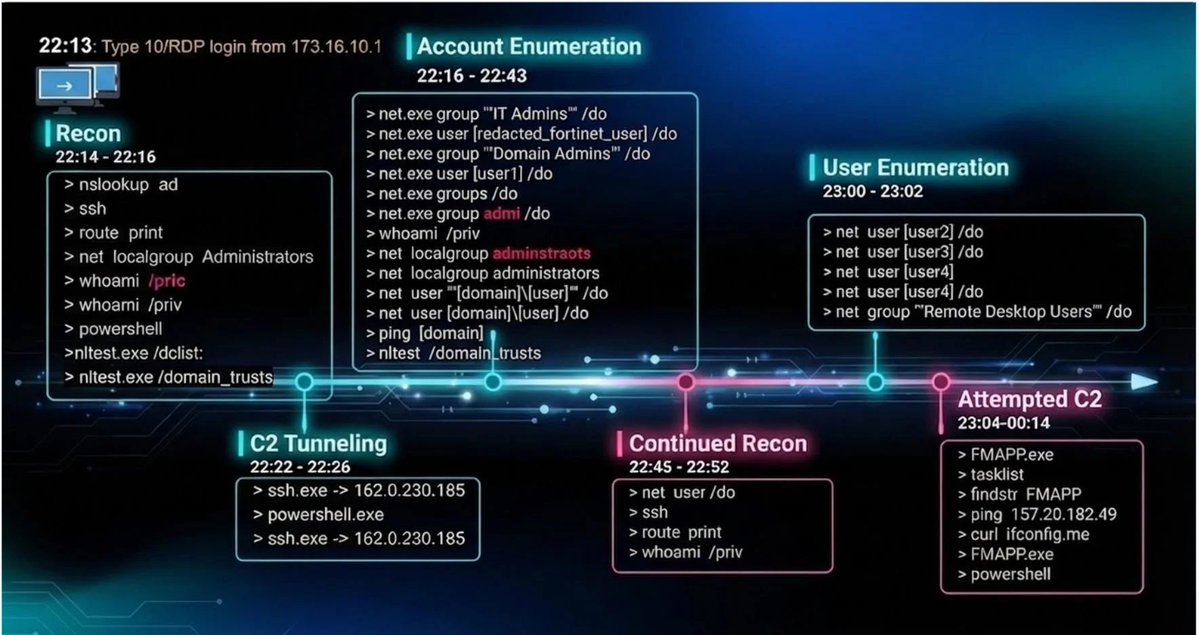
Today I’m launching Threat Hunting Labs.
Over the years I’ve analyzed many real-world intrusions. One thing became obvious: most training platforms don’t resemble how investigations actually happen.
So I built something different.
Threat Hunting Labs focuses on investigation-driven learning using real telemetry and structured investigative paths.
If you want to get better at investigating breaches, you should practice investigating breaches.
More details here:
threathuntinglabs.com/blog/introduci…
English
APK-47 retweetledi
@HackingLZ Should I use cellebrite, axiom, or encase - nah let me spend countless hours troubleshooting something instead of actually getting to the DFIR part
English
@HackingLZ Or, hear me out - just go buy a license for something that is far better than whatever this is, and supported. I’ve never really understood this project - go use something that’s not generally admissible because of how it’s designed??
English
@HackingLZ the next time you're doing an engagement, definitely don't grab these files: C:\Users\Username\AppData\Local\Claude\Logs\*, C:\ProgramData\Claude\Logs\*, C:\Users\Username\AppData\Roaming\Claude\logs\* #ai #infosec
English
APK-47 retweetledi
APK-47 retweetledi

we hijacked perplexity comet by sending a weaponized calendar invite
then used it to takeover victim's 1p account and exfil their local files
call it pleasefix. like clickfix, but instead of social eng'ing a human you just ask their ai real nicely
incredible work by @StAJect0r
English
APK-47 retweetledi

APK-47 retweetledi
@HackingLZ This is pretty bold coming from the company who has the most limited AI capabilities of any of the top contenders. Microsoft AI is actually disproving his point
English

Microsoft already has this issue of people disliking them because of Windows being a mess, AI, and other things perhaps better framing around "tasks" vs "jobs" or find a way to make more positive statements.
x.com/FT/status/2021…
Financial Times@FT
CEO of Microsoft AI Mustafa Suleyman joins FT editor Roula Khalaf to explain why most of the tasks accountants, lawyers and other professionals currently undertake will be fully automated by AI within the next 12 to 18 months ft.trib.al/SZ4Lti1
English