mr p
51 posts

mr p
@mr_________p
web3 Security Researcher | Bug Bounty Hunter

Security Update: Token Gateway exploit On April 13, 2026, a vulnerability in Hyperbridge’s Token Gateway was exploited, resulting in approximately $237,000 in losses on Ethereum. Bridging operations were paused immediately after detection, and this is an update on the situation. 🧵











Okey, it was fast. We got first company who moved to fee-based submissions. Who will find it first, will get a coupon from me


Security is paramount at @injective and we take our bug bounty program very seriously. First and foremost, the figures referenced in the post are entirely misleading. There was no impact realized from this issue. Zero user funds were affected and zero addresses were compromised. For the stated vulnerability to work in practice, it would require execution of several suspicious transactions that would have an extraordinarily limited impact. Injective has dynamic rate limiting functionalities which are applied automatically based on our live monitoring systems. This functionality has been live on mainnet since last year and is publicly available in our code base. In addition to all of the above, this report was reviewed against the clearly defined terms of our Immunefi program. Based on those terms, issues such as those raised in this report that DO NOT impact block production or consensus are categorized outside of the Blockchain/DLT tier and carry a maximum payout of $50,000. If the poster had requested a mediation we would explain to him the dynamic rate limiters and monitoring systems we have in place and why his stated figures are misleading. However, he did not do so. We always follow the procedures set forth by the Immunefi program and expect the submitter to do so as well. We remain committed to fair, transparent, and consistent handling of all reports, and to maintaining the highest standards of security for the ecosystem. Injective has done so since its mainnet inception in 2021 and will continue to do so in perpetuity, always putting builders and security first.



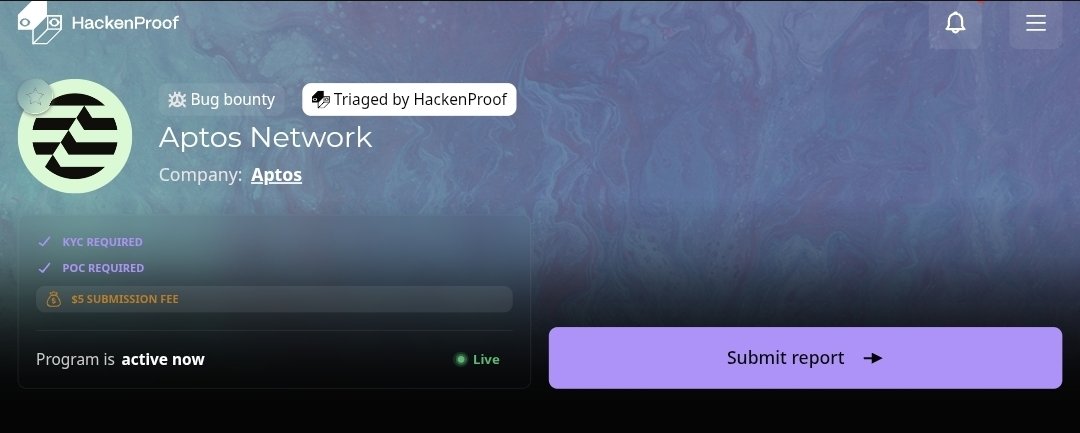
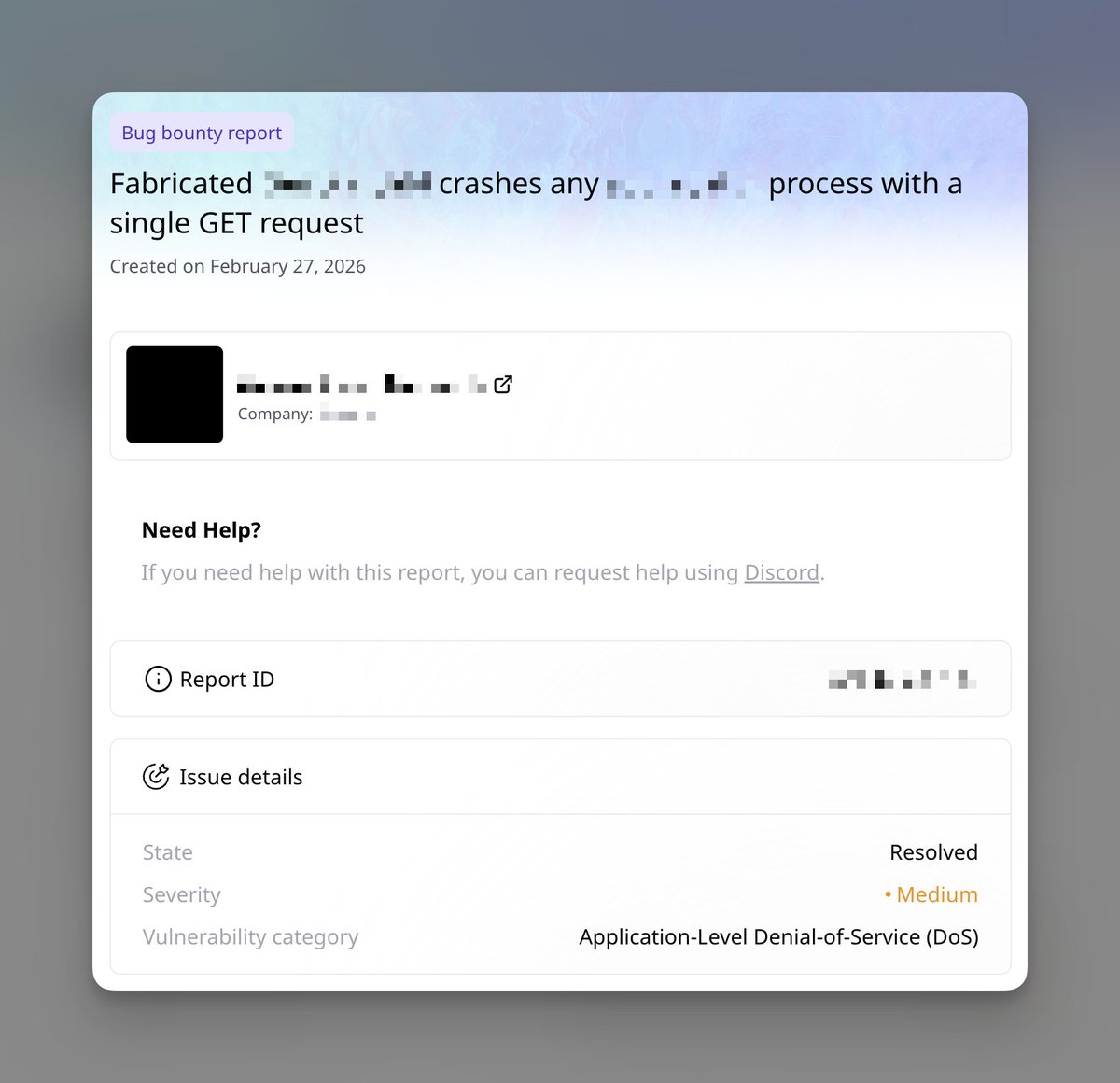
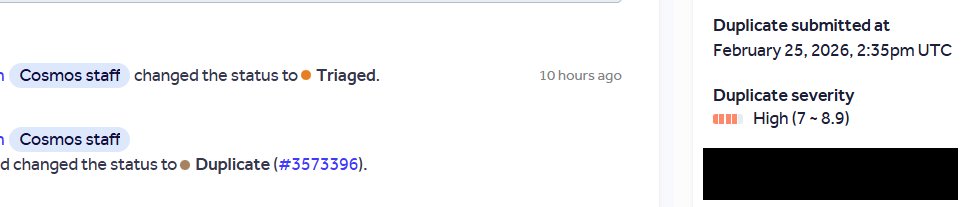
I Saved Injective's $500M. They Pay Me $50K. I like hunting bugs on @immunefi . I'm decent at it. - #1 — Attackathon | Stacks - #2 — Attackathon | Stacks II - #1 — Attackathon | XRPL Lending Protocol - 1 Critical and 1 High from bug bounties (not counting this one) Life was good. Then I found a Critical vulnerability in @injective . This vulnerability allowed any user to directly drain any account on the chain. No special permissions needed. Over $500M in on-chain assets were at risk. I reported it through Immunefi. The next day, a mainnet upgrade to fix the bug went to governance vote. The Injective team clearly understood the severity. Then — silence. For 3 months. No follow up. No technical discussion. Nothing. A few days ago, they notified me of their decision: $50K. The maximum payout for a Critical vulnerability in their bug bounty program is $500K. I disputed it. Silence again. No explanation for the reduced payout. No explanation for the 3 month ghost. No conversation at all. To be clear: the $50K has not been paid either. I've seen others share bad experiences with bug bounty payouts recently. I never thought it would happen to me. I can't force them to do the right thing. But I won't let this be forgotten. I will dedicate 10% of all my future bug bounty earnings to making sure this story stays visible — until Injective pays what I deserve. Full Technical Report: github.com/injective-wall…