munsiwoo retweetledi

thanksgiving 2021: log4shell
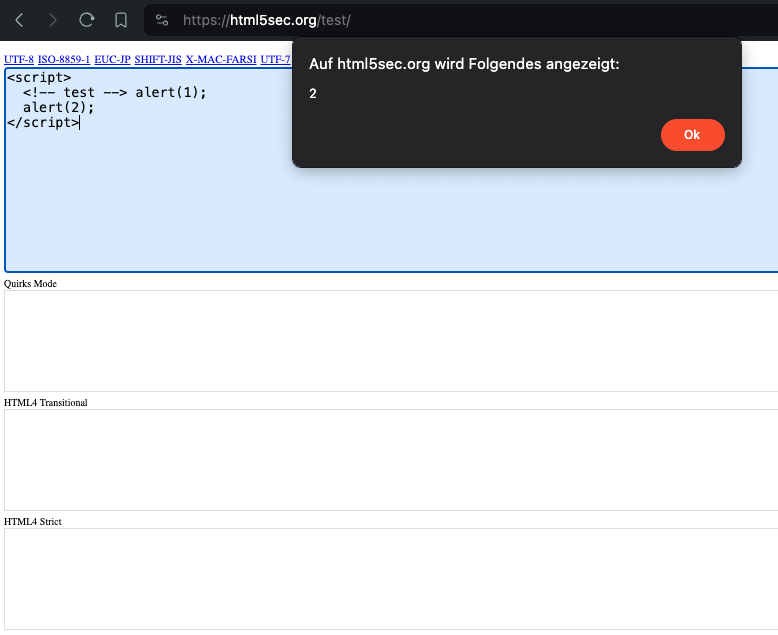
thanksgiving 2025: react2shell
some things never change...

Sylvie@_sy1vi3
react2shell:11/29/25:lachlan2k:sy1vi3 sha256:18571097aedaec16f729c4227e1e508fe161d5d6b4256eec7d0525535ebb3fa0 cve.org/CVERecord?id=C…
English