Naacbin retweetledi
Naacbin
158 posts

Naacbin
@naacbin
Maldev, forensic and reverse makes me happy.
Katılım Ekim 2018
159 Takip Edilen165 Takipçiler
Naacbin retweetledi

Excited to share my latest article: PgC - a novel approach to disable Patchguard during runtime using basic memory management principles.
It has worked against every version of Patchguard for the last 7 years, without needing any updates!
blog.can.ac/2024/06/28/pgc…
English
Naacbin retweetledi

Didn't check the code yet, but looks like SilverPotato and CertifiedDCOM have a working public weaponized tool by now:
github.com/CICADA8-Resear…
That's huge news from my perspective🔥
English
Naacbin retweetledi

I wrote a blogpost on injecting code into a PPL process on Windows 11, without abusing any vulnerable driver.
blog.slowerzs.net/posts/pplsyste…
English
Naacbin retweetledi

I just published the long-awaited Part 2 to my PCIe blog post series - "All About Memory: MMIO, DMA, TLPs, and more!"
This post also includes a companion experiment where I dive into what pcileech looks like over a PCIe protocol analyzer. Please enjoy!
ctf.re/kernel/pcie/tu…
English
Naacbin retweetledi

Here is my #Friday #giveaways!
Like, retweet and share with your network... I'll randomly choose on Monday 4/1 two winners to get the full "C5W Certified Malware Analysis" course and certification for FREE... You should not miss this! #DFIR #Malware
academy.cyber5w.com/courses/C5W-Ce…

English
Naacbin retweetledi

Exciting news: VolWeb 2.0 is out! This digital forensics memory analysis platform leverages the capabilities of @volatility 3 framework. With significant enhancements, it now offers improved flexibility and scalability! github.com/k1nd0ne/VolWeb.
1/8
English
Naacbin retweetledi

New lab 🏰 for the GOAD project 🥳: SCCM
You can now test the SCCM/MECM attacks locally on Virtualbox or Vmware.
More information here:
mayfly277.github.io/posts/SCCM-LAB…
Repository here : github.com/Orange-Cyberde…
Thx again @KenjiEndo15 for your help to building this !
English
Naacbin retweetledi
I just spent the last few months of my life reverse engineering the Windows 10 parallel loader and figuring out how it does concurrency. Updates have now been published!
github.com/ElliotKillick/…
English

Over the past few months, I've contributed on the github.com/mandiant/VM-Pa… repository to incorporate forensic packages. As a result, I've developed scripts to automate VM installation for reverse, maldev and forensic purposes.
👇
github.com/naacbin/SecLab
English
Naacbin retweetledi

I documented github.com/corkami/docs/b… and made 'low alignment PEs' (PoCs @ github.com/corkami/pocs/b…) around 2009 but I'm pretty sure this was known before.
Any early case of ITW low-align PE ? cc @Hexacorn @a2_qkumba @hasherezade @rwfpl
x86matthew@x86matthew
First blog post in a while! This article describes an undocumented trick to embed executable code within (what appears to be) a read-only PE section. secret.club/2023/06/05/spo…
English
Naacbin retweetledi

Challenge time is now over ⏰
TL;DR
- HTML injection
- Axios DOM Based CSPP
- Axios CSPP response overwrite gadget
- jQuery DOM Clobbering + CSPP selector overwrite gadgets
- Setting src attr to "javascript:" for each HTML node ➝ XSS
Detailed writeup 👇
mizu.re/post/intigriti…
Kévin GERVOT (Mizu)@kevin_mizu
GG to all the solvers! However, no one solved it in the intended way :p Before giving my solution, I'm extending the challenge for another week with a fixed version! If you find the solution, please send me a DM 📮 The challenge is accessible here 👇 mizu.re:3000
English
Naacbin retweetledi
Naacbin retweetledi

OST cannot be stopped. Here is a technique we tested internally 9 months ago: blocking EDR telemetry by leveraging the Windows Filtering Platform. Considered it so evil that we didn't publish it that time. It was pointless, now here it is by @netero_1010: github.com/netero1010/EDR…
English

@vxunderground @whid_ninja Someone I know has it and from what he told me it's awesome!
English

Our friend @whid_ninja hooked us up with a Hardware Hacking Offensive Security training + exam. It comes with a bunch of super cool tools too =D
*Winner must disclose their home address to receive the package in the mail
Comment below to win:)
Course: whid.ninja/store/product/…
English
Naacbin retweetledi

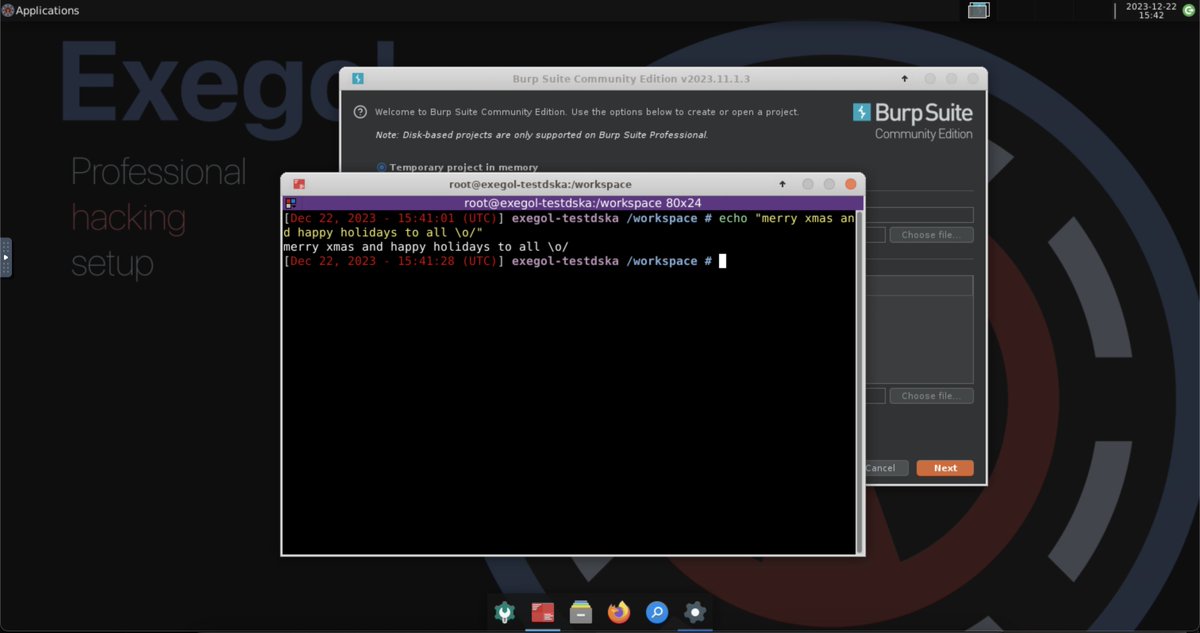
Exegol holiday release is live 🎄🎁🎅
New remote graphical desktop, image entrypoint, container startup script, new tools, improved pipeline, doc, etc. Many big things!
github.com/ThePorgs/Exego…
github.com/ThePorgs/Exego…
gg to the team @Dramelac_ @QU35T_TV 👏 and all contributors.
English
Naacbin retweetledi

Read our latest blog to find out how our Security Research Team reverse-engineered Windows Defender to uncover previously undocumented artefacts, which can now be recovered using Dissect!
blog.fox-it.com/2023/12/14/rev…
English

I have made 2 writeups for #ECSC2023 and #DGhAck. For the 2nd one, I used github.com/naacbin/Covena…
[1] Recovering PDF using DataRun of $LogFile
> naacbin.gitlab.io/data-on-the-ru…
[2] Decrypt empire C2 communication by extracting private key from memory
> naacbin.gitlab.io/empire-c2/
English
Naacbin retweetledi

Time to make @volatility 3 compatible with modern Windows hibernation file analysis.
Blog post : forensicxlab.com/posts/hibernat…
Feature : tinyurl.com/5n8u4nr9
Special thanks to @chadtilbury who gave me the motivation and @jtsylve, @vicomarziale, @nolaforensix for the incredible work
English

Excited to launch my first browser extension, DOMLogger++! Now available for both Firefox and Chromium! 🎉
DOMLogger++ allows you to monitor, intercept, and debug JavaScript sinks based on customizable configurations 🔥
Check it out 👇
github.com/kevin-mizu/dom…
1/5
English





