Sabitlenmiş Tweet
Clarke Thomas
88.3K posts


Clarke Thomas
@needcaffeine
Sporting photo taking wanderlust that geeks out on tech & loves fine food/drink.
Road Not Taken Katılım Ocak 2008
2K Takip Edilen2K Takipçiler
Clarke Thomas retweetledi

MICROSOFT EDGE STORES ALL YOUR PASSWORDS IN PLAIN TEXT
edge password manager security fail
A security researcher just found that Edge decrypts EVERY saved password at startup and keeps them in memory - even if you never visit those sites.
The wild part? Edge still asks for your Windows password to VIEW them in the UI. The passwords are already sitting there, naked in RAM.
Chrome only decrypts passwords when you actually need them. Edge just.. doesn't.
Microsoft's response when reported: "working as intended"
If someone gets admin access on a shared machine, they can dump ALL Edge passwords from ALL logged-in users. Even disconnected ones.
Tom Jøran Sønstebyseter Rønning@L1v1ng0ffTh3L4N
Microsoft Edge loads all your saved passwords into memory in cleartext — even when you’re not using them.
English
Clarke Thomas retweetledi
Clarke Thomas retweetledi
Clarke Thomas retweetledi

In 2015, the Chinese police visited a programmer's home.
They told him to stop working on his code. They told him to delete it from GitHub. He posted one final message before he obeyed:
"Two days ago the police came to me and wanted me to stop working on this. Today they asked me to delete all the code from GitHub. I have no choice but to obey. I hope one day I'll live in a country where I have freedom to write any code I like without fearing."
Then he deleted the repo.
Then he deleted the message.
Then something happened the Chinese government did not plan for.
Within hours, the code was mirrored to thousands of other GitHub accounts. Within days, it became the #1 trending repository on GitHub globally. Within weeks, every Chinese developer who could compile code had a copy.
The government tried to make it disappear. The act of trying made it permanent.
The project is called Shadowsocks. The programmer's username was clowwindy.
He built a tiny piece of software that let anyone in China bypass the Great Firewall and reach the open internet. No subscription. No company. No account. You set up a server somewhere outside China. You connect to it. Your traffic looks like normal encrypted web browsing, so the firewall cannot tell you are using it.
Why this terrified the Chinese government in 2015:
→ It was open source. Anyone could compile it.
→ It was small. The whole protocol fit in a few hundred lines of code.
→ It looked like normal HTTPS traffic. The Great Firewall could not distinguish it.
→ It required no money. No accounts. No central server to seize.
→ It worked on every operating system.
You cannot arrest a protocol. You can only arrest the person who wrote it. So they did. And the protocol kept spreading.
shadowsocks-windows: 59,300+ stars. GPLv3. Still online 11 years later. The 2015 commits the Chinese government wanted deleted are still in the history.
clowwindy was forced to walk away. The code never did.
But DO NOT install it. The Great Firewall has feelings too.
100% Open Source.
(Link in the comments)

English
Clarke Thomas retweetledi

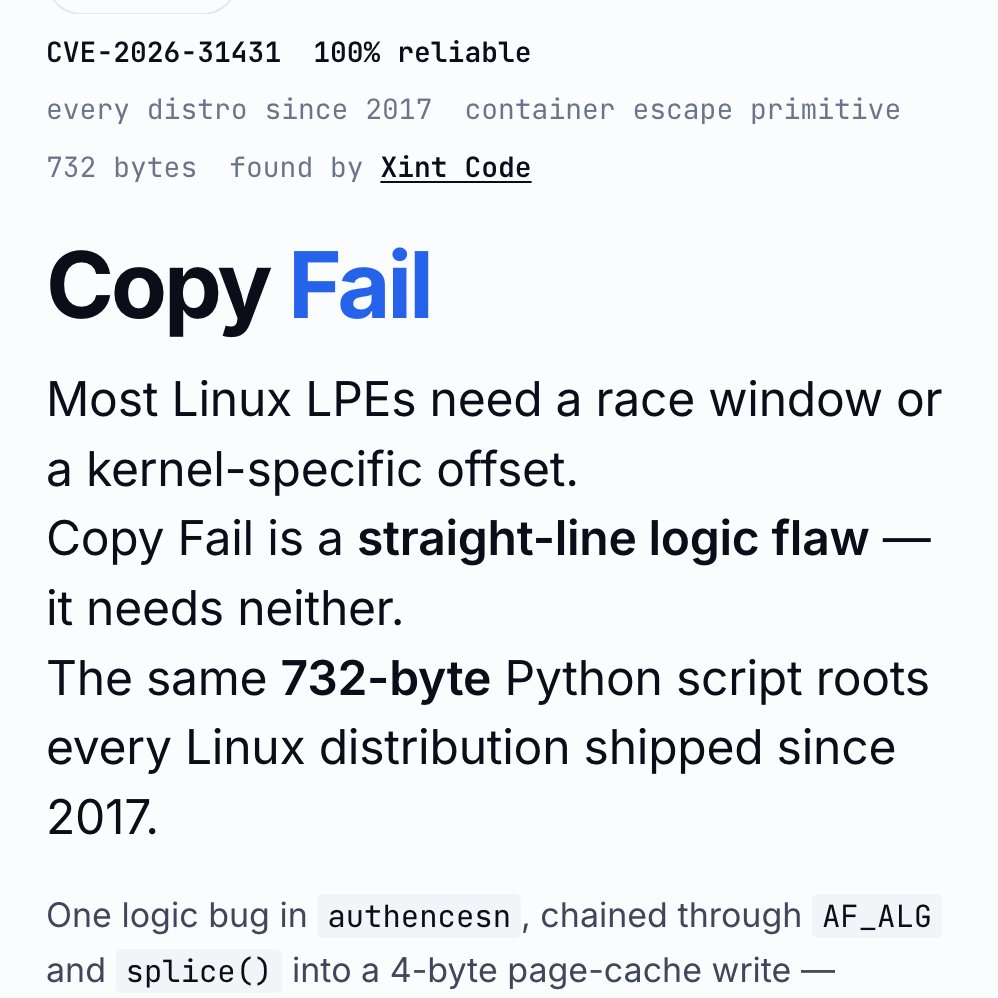
‼️🚨 BREAKING: An AI found a Linux kernel zero-day that roots every distribution since 2017. The exploit fits in 732 bytes of Python. Patch your kernel ASAP.
The vulnerability is CVE-2026-31431, nicknamed "Copy Fail," disclosed today by Theori. It has been sitting quietly in the Linux kernel for nine years.
Most Linux privilege-escalation bugs are picky. They need a precise timing window (a "race"), or specific kernel addresses leaked from somewhere, or careful tuning per distribution. Copy Fail needs none of that. It is a straight-line logic mistake that works on the first try, every time, on every mainstream Linux box.
The attacker just needs a normal user account on the machine. From there, the script asks the kernel to do some encryption work, abuses how that work is wired up, and ends up writing 4 bytes into a memory area called the "page cache" (Linux's high-speed copy of files in RAM). Those 4 bytes can be aimed at any program the system trusts, like /usr/bin/su, the shortcut to becoming root.
Result: the next time anyone runs that program, it lets the attacker in as root.
What should worry most: the corruption never touches the file on disk. It only exists in Linux's in-memory copy of that file. If you imaged the hard drive afterwards, the on-disk file would match the official package hash exactly. Reboot the machine, or just put it under memory pressure (any normal system load that needs the RAM), and the cached copy reloads fresh from disk.
Containers do not help either. The page cache is shared across the whole host, so a process inside a container can use this bug to compromise the underlying server and reach into other tenants.
The original sin was a 2017 "in-place optimization" in a kernel crypto module called algif_aead. It was meant to make encryption slightly faster. The change broke a critical safety assumption, and nobody noticed for nine years. That bug then rode every kernel update from 2017 to today.
This vulnerability affects the following:
🔴 Shared servers (dev boxes, jump hosts, build servers): any user becomes root
🔴 Kubernetes and container clusters: one compromised pod escapes to the host
🔴 CI runners (GitHub Actions, GitLab, Jenkins): a malicious pull request becomes root on the runner
🔴 Cloud platforms running user code (notebooks, agent sandboxes, serverless functions): a tenant becomes host root
Timeline:
🔴 March 23, 2026: reported to the Linux kernel security team
🔴 April 1: patch committed to mainline (commit a664bf3d603d)
🔴 April 22: CVE assigned
🔴 April 29: public disclosure
Mitigation: update your kernel to a build that includes mainline commit a664bf3d603d. If you cannot patch immediately, turn off the vulnerable module:
echo "install algif_aead /bin/false" > /etc/modprobe.d/disable-algif.conf
rmmod algif_aead 2>/dev/null || true
For environments that run untrusted code (containers, sandboxes, CI runners), block access to the kernel's AF_ALG crypto interface entirely, even after patching. Almost nothing legitimate needs it, and blocking it shuts the door on this whole class of bug...

English
Clarke Thomas retweetledi

Today’s Supreme Court decision effectively guts a key pillar of the Voting Rights Act, freeing state legislatures to gerrymander legislative districts to systematically dilute and weaken the voting power of racial minorities - so long as they do it under the guise of “partisanship” rather than explicit “racial bias.” And it serves as just one more example of how a majority of the current Court seems intent on abandoning its vital role in ensuring equal participation in our democracy and protecting the rights of minority groups against majority overreach.
The good news is that such setbacks can be overcome. But that will only happen if citizens across the country who cherish our democratic ideals continue to mobilize and vote in record numbers - not just in the upcoming midterms or in high profile races, but in every election and every level.
English
Clarke Thomas retweetledi
Clarke Thomas retweetledi

Not sure why there is so much confusion around this, but:
1. Cole Allen never reached the ballroom.
2. He never fired a shot.
3. He was not shot.
4. He was going to use buckshot, if he had reached the ballroom, but he didn’t.
5. The shots fired were by Secret Service; one officer took friendly fire, but it was stopped by tactical gear.
6. Allen was apparently subdued (tackled).
7. Officers recovered a handgun, a long-gun, and knives from Allen.
8. The security perimeter was inside the hotel and functioned as designed.
English

The US authorities are asking for hundreds of millions in additional funding not to convert the $300 million luxury 747 jet gifted by Qatar but to rescue Boeing's hopelessly delayed Air Force One program from slipping even further behind schedule share.google/qx5cJ60clTsnzA…
English
Clarke Thomas retweetledi
Clarke Thomas retweetledi
Clarke Thomas retweetledi

How a U.S. soldier made $400,000 from inside knowledge of Maduro capture plan — and clumsily attempted to cover it up marketwatch.com/story/how-a-u-… via @MarketWatch
English
Clarke Thomas retweetledi

‼️ Trump Corruption: Taxpayers paying Ballroom Builder after secret no-bid contract inflates value 3x
- Biden admin estimated $3.3 MILLION for 2 broken fountains in Lafayette Park:
- Trump admin secretly bumped it to $11.9M then $17.4 MILLION with double inflation padding + “schedule compression” magic
Source: NYT

English