Sabitlenmiş Tweet
𝙽𝙴𝚃𝚁𝙴𝚂𝙴𝙲
3.6K posts


𝙽𝙴𝚃𝚁𝙴𝚂𝙴𝙲
@netresec
Creators of #NetworkMiner, #CapLoader, #PolarProxy and #RawCap. https://t.co/CZliuI6WRc https://t.co/vC5XlueXTb
@[email protected] Katılım Kasım 2011
844 Takip Edilen8.8K Takipçiler
𝙽𝙴𝚃𝚁𝙴𝚂𝙴𝙲 retweetledi

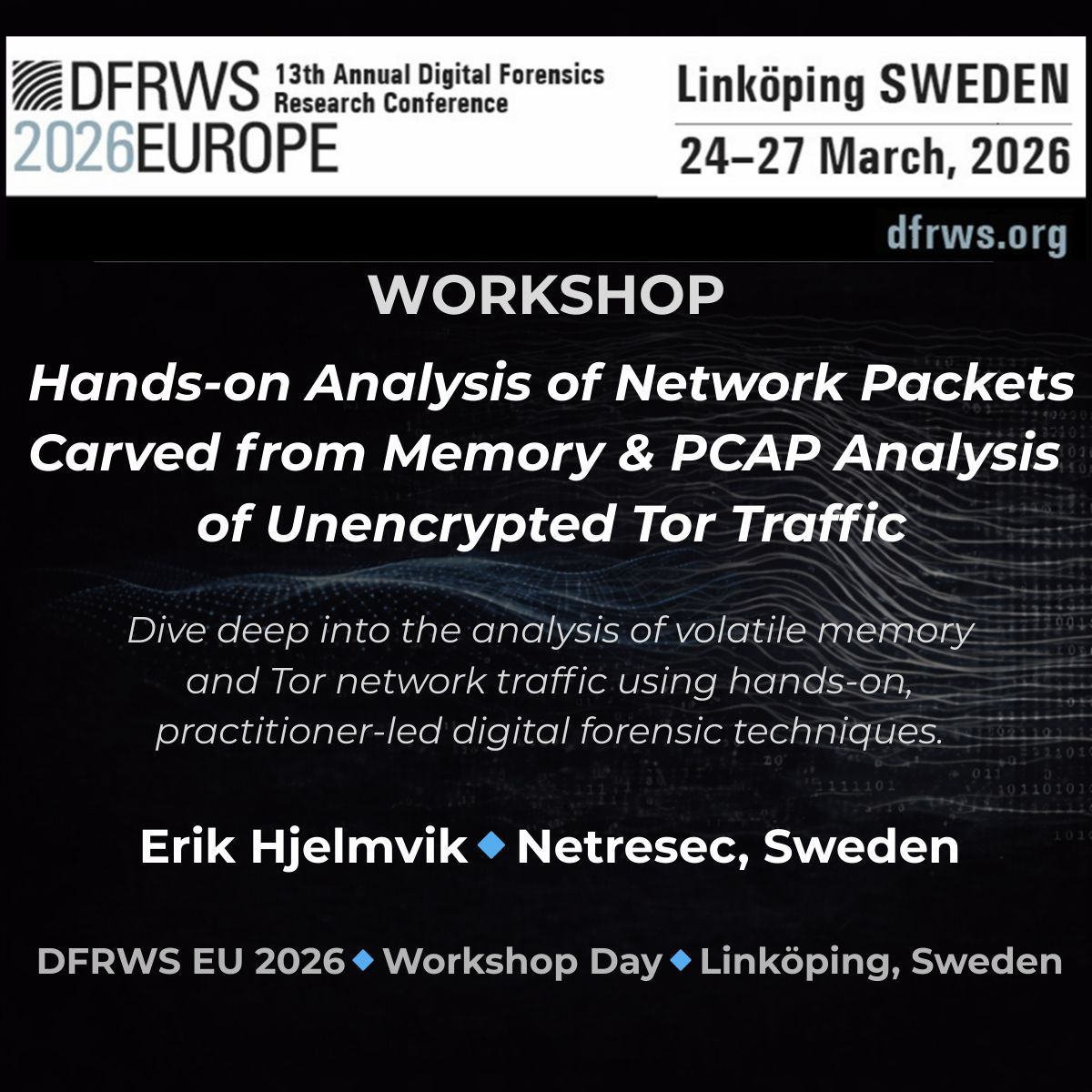
✨ DFRWS EU 2026 Workshops
Led by Erik Hjelmvik (Netresec, Sweden), the session is designed for practitioners and researchers working with network and memory forensics in real-world investigations.
📍 Workshop Dates 23–24 March 2026
🧿 Details here: buff.ly/oT8OtbE
English

@greenplan_it Interesting pivot point!
Those samples behave like "normal" ValleyRAT implants though, communicating with C2 servers like
👾 137.220.153.22:8880
👾 154.82.84.217:8880
👾 206.238.40.106:8880
👾 137.220.154.46:9000
English

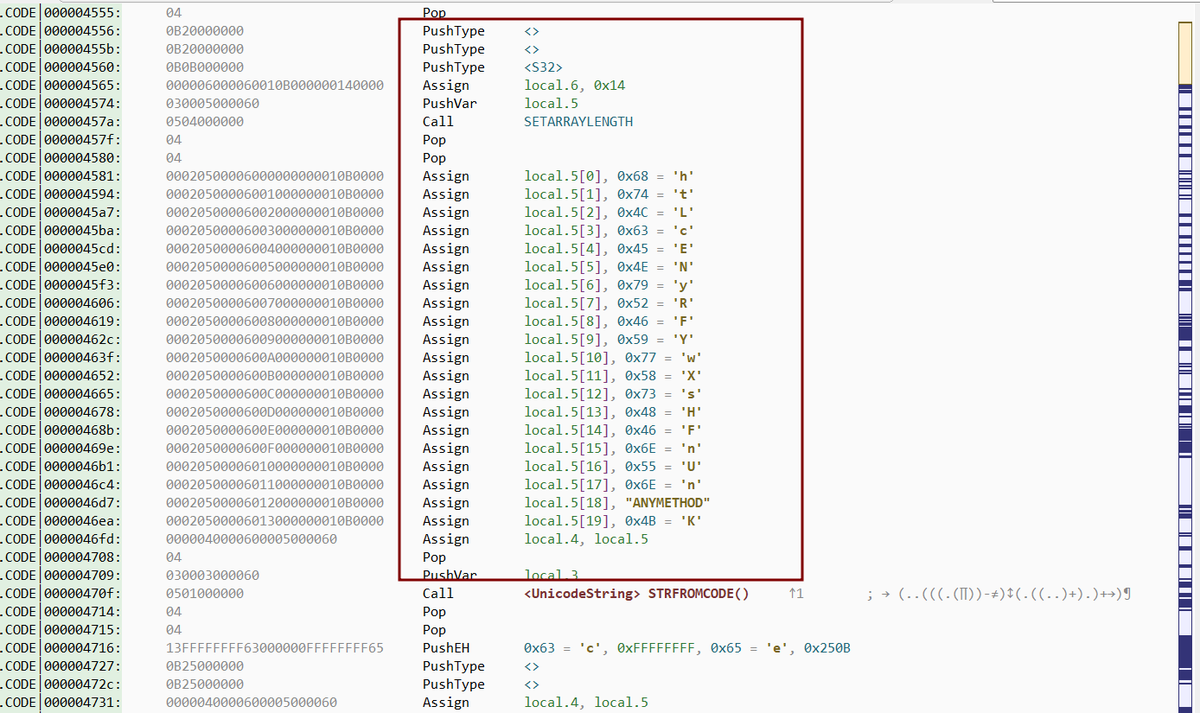
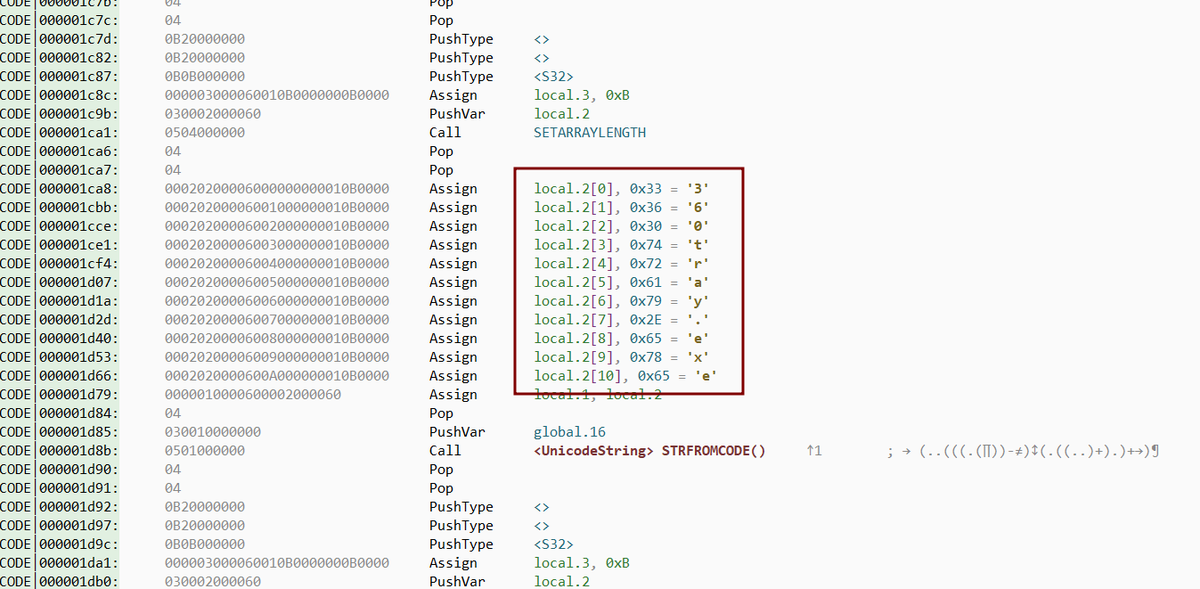
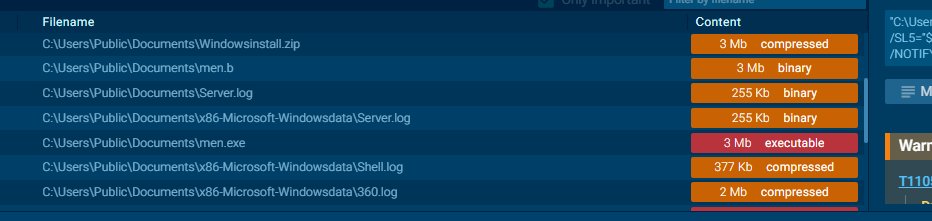
@netresec These should be related, same zip password "htLcENyRFYwXsHFnUnqK" and similar dropped files (men.exe, 360tray.exe, Server.log, sys file)
- nextron-systems.com/2025/11/28/tho…
- vms.drweb-av.it/virus/?i=31075…
English

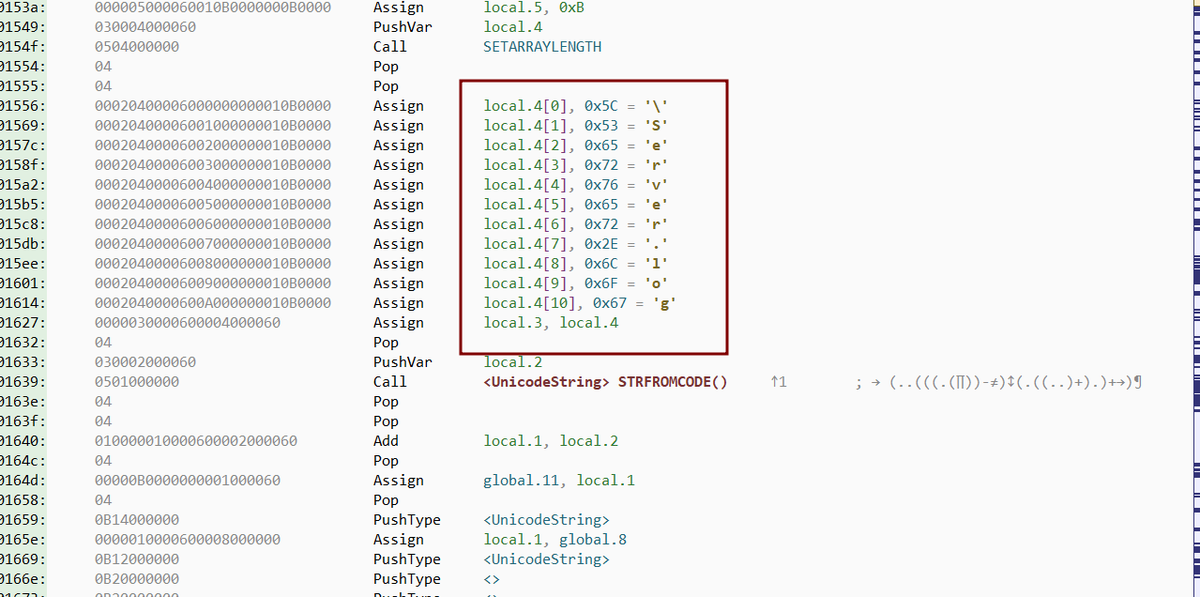
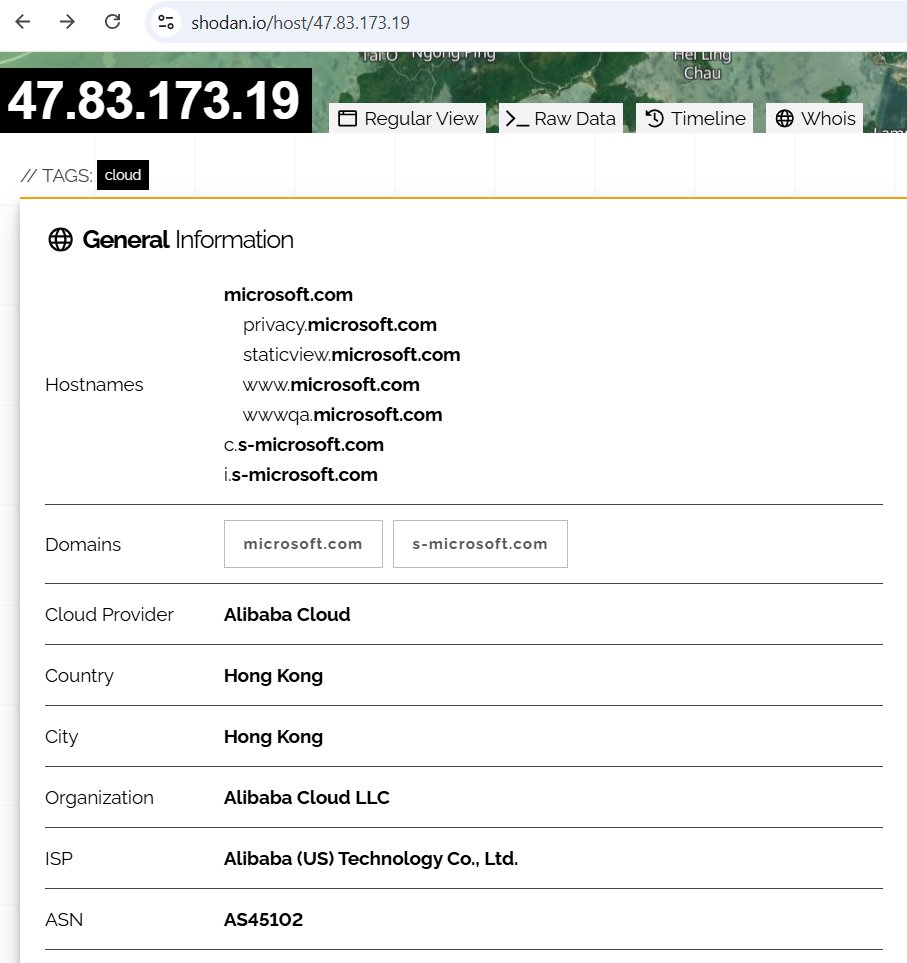
New RAT C2 found. What malware C2 protocol is this is?
🔥 47.83.173.19:5050
🔥 47.84.203.73:5050
🔥 xuanwcai[.]com:5050
🔥 wkaiuahaaxx[.]icu:5050
Links to samples on ANY.RUN and JoeSandbox available via infosec.exchange link.
@netresec/116040288746020333" target="_blank" rel="nofollow noopener">infosec.exchange/@netresec/1160…
English
𝙽𝙴𝚃𝚁𝙴𝚂𝙴𝙲 retweetledi

𝙽𝙴𝚃𝚁𝙴𝚂𝙴𝙲@netresec
New RAT C2 found. What malware C2 protocol is this is? 🔥 47.83.173.19:5050 🔥 47.84.203.73:5050 🔥 xuanwcai[.]com:5050 🔥 wkaiuahaaxx[.]icu:5050 Links to samples on ANY.RUN and JoeSandbox available via infosec.exchange link. @netresec/116040288746020333" target="_blank" rel="nofollow noopener">infosec.exchange/@netresec/1160…
ZXX
𝙽𝙴𝚃𝚁𝙴𝚂𝙴𝙲 retweetledi

✨ DFRWS EU 2026 Workshops
Led by Erik Hjelmvik (Netresec, Sweden), the session is designed for practitioners and researchers working with network and memory forensics in real-world investigations.
📍 Workshop Dates 23–24 March 2026
📍 Details here: 👉 buff.ly/oT8OtbE

English

Erik Hjelmvik will run a hands-on network forensic workshop at the upcoming Digital Forensics Research Conference in Sweden. Participants will get the chance to analyze:
🔪 Packets carved from memory dumps
🧅 Unencrypted Tor traffic
dfrws.org/dfrws-eu-2026-…
English

Decoding njRAT C2 traffic to extract screenshots, commands and transferred files
netresec.com/?b=262adb9
English

Check out our network forensics class if you'd like to spend more time analyzing malware PCAP files.
netresec.com/?b=25A2e4f
English

The early bird discount for our network forensics class expires by the end of this week. Sign up if you’d like to analyze PCAP files together with Erik Hjelmvik (creator of NetworkMiner and PolarProxy).
netresec.com/?b=25A2e4f
English
𝙽𝙴𝚃𝚁𝙴𝚂𝙴𝙲 retweetledi

DFRWS EU 2026 is seeking posters showcasing interesting digital forensics research for presentation in Linköping, Sweden, 24–27th March 2026. 📥 Submit via EasyChair ( as PDF) - Rolling notification until the program is full! #DFRWSEU2026 #DFRWS #DigitalForensics

English

@netresec No, but about the Asyncrat detections in the blogpost (netresec.com/?page=Blog&mon…), I have seen those before. I think its possible related:
recordedfuture.com/research/uncov…
And search for GhostWeaver.
English

Have anyone seen this reverse shell C2 protocol before?
📡Client: key007
📡Server: Authentication successful
@netresec/115865169187266682" target="_blank" rel="nofollow noopener">infosec.exchange/@netresec/1158…
🔥C2: 103.27.157.146:4444
🗝️XOR key: 0x68
❇️Reference: malware-traffic-analysis.net/2026/01/08/ind…
English

The reverse shell traffic is decoded in this video
netresec.com/?b=261f535
English

The output from the finger command is decoded in this video
netresec.com/?b=261f535
English