Nick Hutton
19K posts


Nick Hutton
@nickdothutton
30 years in Cyber Security, CTO, Product, Investor, Founder, Engineer. Armchair interests: geopolitics, propaganda, persuasion, ideological subversion.




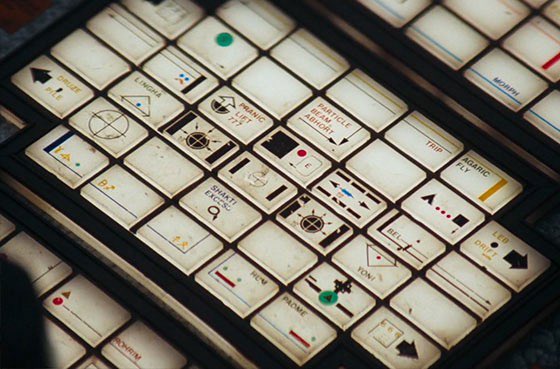
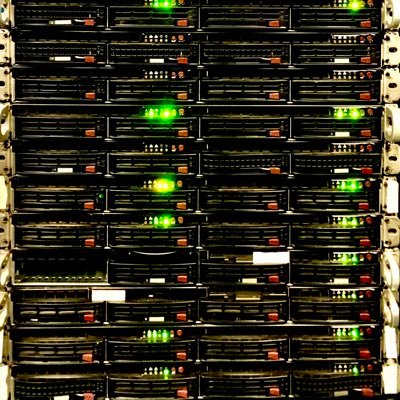
Three Charged with Conspiring to Unlawfully Divert Cutting Edge U.S. Artificial Intelligence Technology to China “The indictment unsealed today details alleged efforts to evade U.S. export laws through false documents, staged dummy servers to mislead inspectors, and convoluted transshipment schemes, in order to obfuscate the true destination of restricted AI technology—China,” said John A. Eisenberg, Assistant Attorney General for National Security. “These chips are the product of American ingenuity, and NSD will continue to enforce our export-control laws to protect that advantage.” 🔗: justice.gov/opa/pr/three-c…


All of our crises (energy, housing, fertility, aging, pensions, immigration, emigration, political Islam, economic stagnation, being an overly service oriented economy, institutional rot, sickness & mental health, Russia, America, Schism in the CoE …. ) were telegraphed decades ago. However it was/is impolitic to do anything about them so here we are.

This government will make the UK the best place in the world for quantum and AI companies to start, scale and stay. In a changing world, our economic plan is the right one. bbc.co.uk/news/articles/…


@tomhfh If the UK built nuclear at the rate the French did and at the cost the Koreans do today, we could supply all our electricity needs for 100 years at roughly half the cost of a single year of NHS spending.



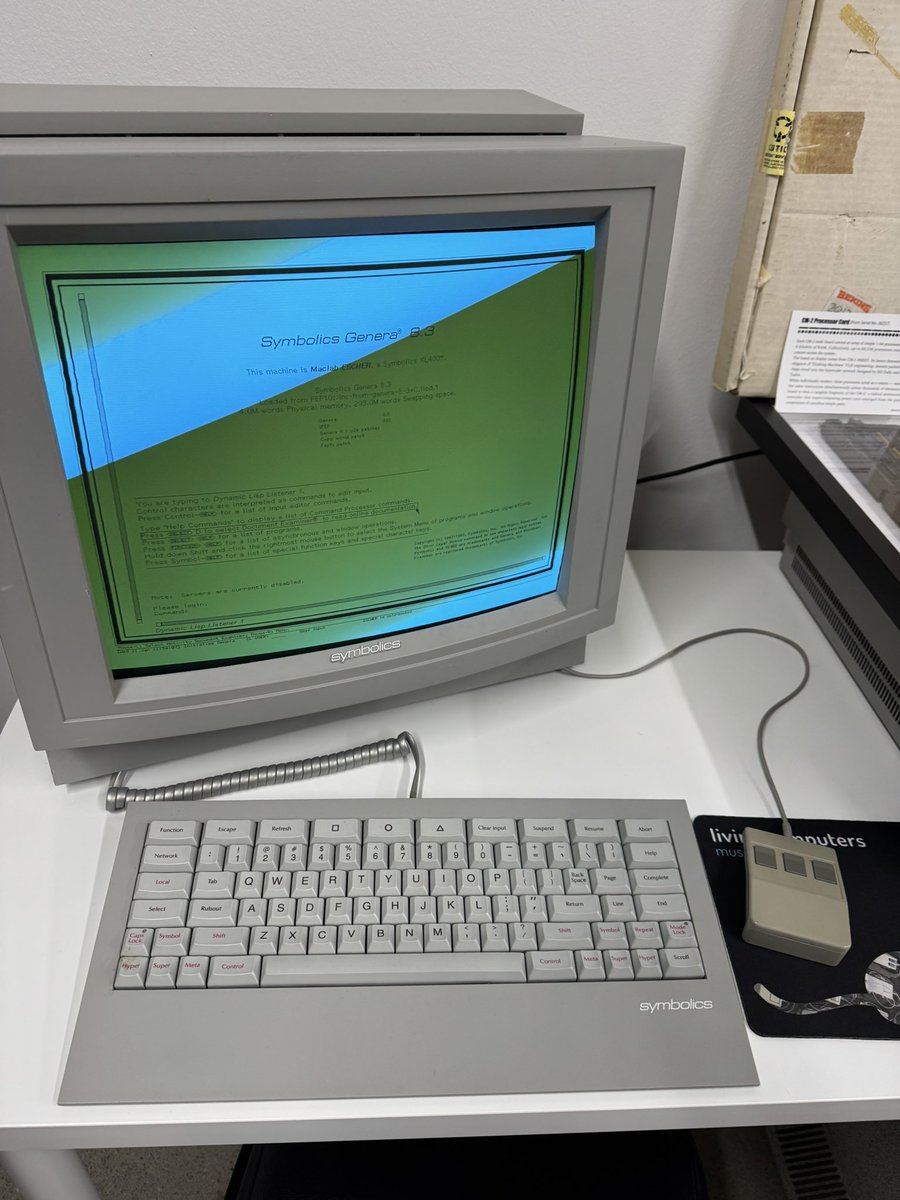


On March 15, 1985, the first internet dot .com domain name, Symbolics . com, was registered to Symbolics Inc., a computer systems company in Cambridge. #InternetHistory




Our WebFiling service is currently unavailable due to a technical issue. We’re working to resolve the issue as quickly as possible. Read more: #service-availability-and-planned-maintenance" target="_blank" rel="nofollow noopener">gov.uk/government/org…

Our WebFiling service is currently unavailable due to a technical issue. We’re working to resolve the issue as quickly as possible. Read more: #service-availability-and-planned-maintenance" target="_blank" rel="nofollow noopener">gov.uk/government/org…



I've published more details about the cyberattack in this piece: zetter-zeroday.com/iranian-hackti…