nick
99 posts

nick
@nicklb_
rust + cryptography · building multiparty computation @Arcium prev. physics @ ETH Zurich 🇬🇷🇨🇭🏳️🌈



Arcium Mainnet Alpha is Live.










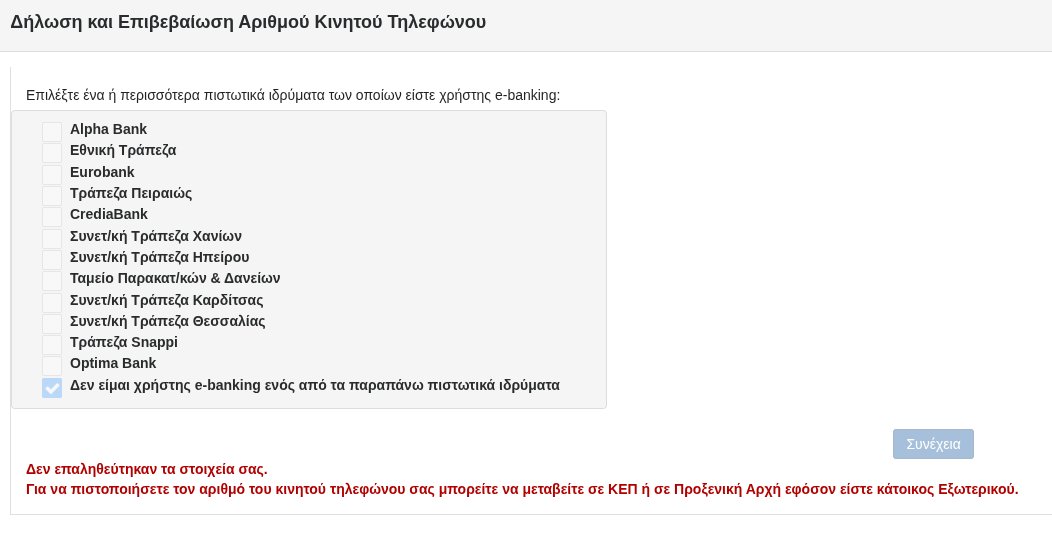
Reality check - crypto fundraise valuations are too high In the last few years you may have been able to get away with a "2 on 20" pre-seed with not much more than a pitch deck and wireframes, then follow that up 6-12 months later with a "5 on 50" seed round well before any true measure of pmf I believe those days are over (for now) The result of raising at these high vals is that teams are incentivized to TGE too soon at even higher vals which removes much of the liquid demand thus leaving very little upside post-TGE The market has a way of finding the correct price over time and for many tokens that number is unfortunately closer to 0 than it is to the opening TGE price You can see from the data below that until 2021, median crypto fundraises were about the same, or slightly lower, than all VC fundraises Then from 2021 onwards, crypto fundraises maintained a healthy valuation premium compared to all VC fundraises Why? If as an investor I can get a quick 2-5x by unloading on secondaries and/or quickly selling unlocks, I can show great IRR and DPI numbers to my LPs to raise bigger funds, so I'm less valuation sensitive as long as I can get in the deal Note: I'm not saying that all funds explicitly operate this way, just that the incentives are present that can drive this type of behavior These high fundraise and TGE valuations also encourage teams to offload as quickly as possible as well - who knows if the price will sustain or if the product/chain will be relevant in 3-4 years after all the unlocks so better to offload whatever you can as early as possible But this year we're seeing those 2-5x quick returns are hard to come by - token prices just aren't cooperating and the secondary demand isn't as robust So the investors still deploying are more valuation sensitive It's much better for everyone involved if all these valuations got a big haircut - from the pre-seed all the way through the opening TGE val Then maybe we'd see more organic liquid demand if more upside remained after TGE, thus encouraging teams to hold longer and stay motivated to building better products that accrued more value, leading to more organic liquid demand Of course there are always exceptions where some teams are so strong that they'll raise at eye-popping levels with everyone trying to get in - this will always happen, I'm referring to the other 99% of deals