Niraj Dhalani
449 posts

Niraj Dhalani
@niraj_dhalani
🖥👨💻Computer Engineer | Security Consultant
Katılım Kasım 2014
693 Takip Edilen175 Takipçiler

AI model that has been trained on thousands of cybersecurity reports. 📢
Just try: alterai.me/secgpt
#infosec #ctf #BugBounty #bugbountytips #redteam
English
Niraj Dhalani retweetledi

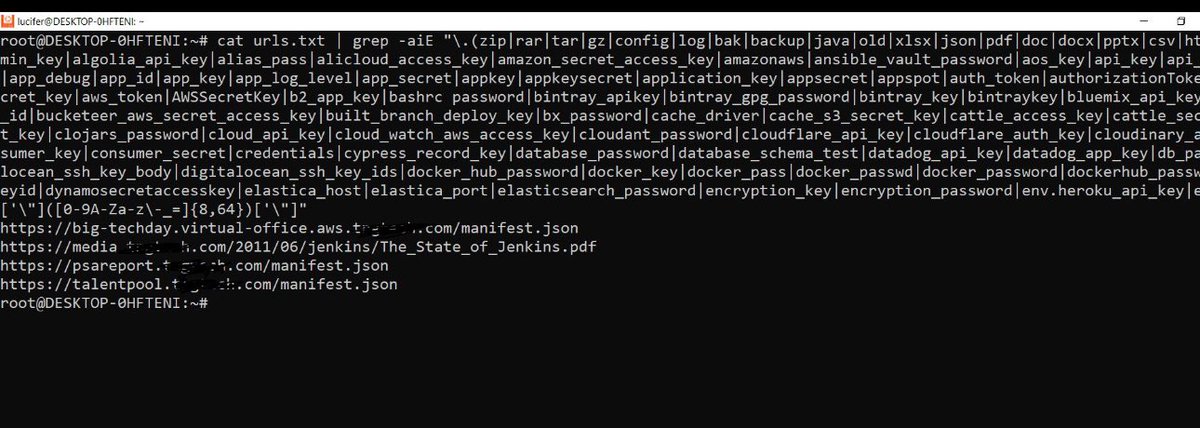
Recon Smarter: Finding Sensitive Files in Large URL Lists
Most bug hunters stop at URLs.
Real impact comes from what those URLs expose.
This workflow combines:
• high-risk file extensions
• real-world secret patterns
• automated URL discovery
Result → fewer URLs, higher signal, better findings.
Step 1: Asset discovery
subfinder -d domains.com | httpx -mc 200,401,403,404 | tee domains.txt
Step 2 URL extraction
cat domains.txt | katana | tee urls.txt
Step 3: Smart grep (FILES + SECRETS)
We combine:
• Sensitive file extensions
• High-signal secret regex
cat urls.txt | grep -aiE "\.(zip|rar|tar|gz|config|log|bak|backup|java|old|xlsx|json|pdf|doc|docx|pptx|csv|htaccess|7z)$|(?i)(?:(?:access_key|access_token|admin_pass|admin_user|algolia_admin_key|algolia_api_key|alias_pass|alicloud_access_key|amazon_secret_access_key|amazonaws|ansible_vault_password|aos_key|api_key|api_key_secret|api_key_sid|api_secret|api.googlemaps AIza|apidocs|apikey|apiSecret|app_debug|app_id|app_key|app_log_level|app_secret|appkey|appkeysecret|application_key|appsecret|appspot|auth_token|authorizationToken|authsecret|aws_access|aws_access_key_id|aws_bucket|aws_key|aws_secret|aws_secret_key|aws_token|AWSSecretKey|b2_app_key|bashrc password|bintray_apikey|bintray_gpg_password|bintray_key|bintraykey|bluemix_api_key|bluemix_pass|browserstack_access_key|bucket_password|bucketeer_aws_access_key_id|bucketeer_aws_secret_access_key|built_branch_deploy_key|bx_password|cache_driver|cache_s3_secret_key|cattle_access_key|cattle_secret_key|certificate_password|ci_deploy_password|client_secret|client_zpk_secret_key|clojars_password|cloud_api_key|cloud_watch_aws_access_key|cloudant_password|cloudflare_api_key|cloudflare_auth_key|cloudinary_api_secret|cloudinary_name|codecov_token|config|conn.login|connectionstring|consumer_key|consumer_secret|credentials|cypress_record_key|database_password|database_schema_test|datadog_api_key|datadog_app_key|db_password|db_server|db_username|dbpasswd|dbpassword|dbuser|deploy_password|digitalocean_ssh_key_body|digitalocean_ssh_key_ids|docker_hub_password|docker_key|docker_pass|docker_passwd|docker_password|dockerhub_password|dockerhubpassword|dot-files|dotfiles|droplet_travis_password|dynamoaccesskeyid|dynamosecretaccesskey|elastica_host|elastica_port|elasticsearch_password|encryption_key|encryption_password|env.heroku_api_key|env.sonatype_password|eureka.awssecretkey)[a-z0-9_.,-]{0,25})[:<>=|]{1,2}.{0,5}['\"]([0-9A-Za-z\-_=]{8,64})['\"]"
#bugbounty
#recon
#infosec
#cybersecurity
#pentesting
#websecurity
#hacking
English

I’m hiring 🧠 iOS Security Researchers 🍏🔍 — remote-friendly 💻🌍
Not you, but know someone strong? My DMs are open — RT/share 🔁🚀
#hiring #cybersecurity #offsec #ios
English
🚨 New initiative just launched! 🚀
Support matters ❤️
👉 Like • Share • Subscribe • Follow
🎥 YouTube: yt.openinapp.co/6s03k
📘 Facebook: fb.openinapp.co/41ov6
📸 Instagram: insta.openinapp.co/lcty1
🔁 RT to support
#SupportCreators #FollowNow #NewStart #CyberSec
English

Seeking Advice from the Community!
As a security researcher, I recently discovered an exposed AWS AppSync GraphQL endpoint and API key in a public JS file. Using the endpoint and API key, I was able to:
- Introspect the database schema
- Query sensitive user data, including:
- Email addresses
- Phone numbers
- Names
- IDs
After reporting the issue to the client, they removed the file but failed to address the root cause - multiple JS files still contain the exposed credentials.
What's more concerning is that despite my responsible disclosure, the client hasn't acknowledged or rewarded my efforts, citing they're a small startup. Meanwhile, they're generating revenue by selling services to customers.
I'm considering escalating this matter to the UK ICO under GDPR regulations. Have any of you encountered similar situations? What steps would you recommend taking next? Should I:
1. Continue to work with the client to ensure thorough remediation?
2. Escalate the issue to the UK ICO immediately?
3. Document everything and potentially publish a responsible disclosure?
*Poll: What's Your Next Step?*
A) Continue working with the client
B) Escalate to UK ICO
C) Document and publish responsible disclosure
D) Other (share in comments)
The lack of recognition for security researchers' efforts is a concerning trend. Let's discuss!
#Cybersecurity #GDPR #ResponsibleDisclosure #SecurityResearch #DataProtection #Infosec #StartupSecurity #EthicalHacking
English

@Bugcrowd @Hacker0x01
Why not hire people like who have seen the struggle of real hunting? Why not hire people who are working day/night for years, These people are Gems, They know what are the real problems and how to overcome them.
Hire bug hunters instead of Pentesters,
Hire talent instead of certs,
Hire those who would love to build the platform.
90% reports goes to N/A because Triagers (Pentesters) couldn't understand it.
5% goes to invalid priorities.
4% goes to no response.
1% goes to accepted because ur lucky that time.
There were times when triagers (Bug hunters) help hunters to exploit their submissions to escalate the priority (Bug hunters).
vs
We don't have time to check your report, Kindly create a video because it takes time to create a new user (Pentesters).
English

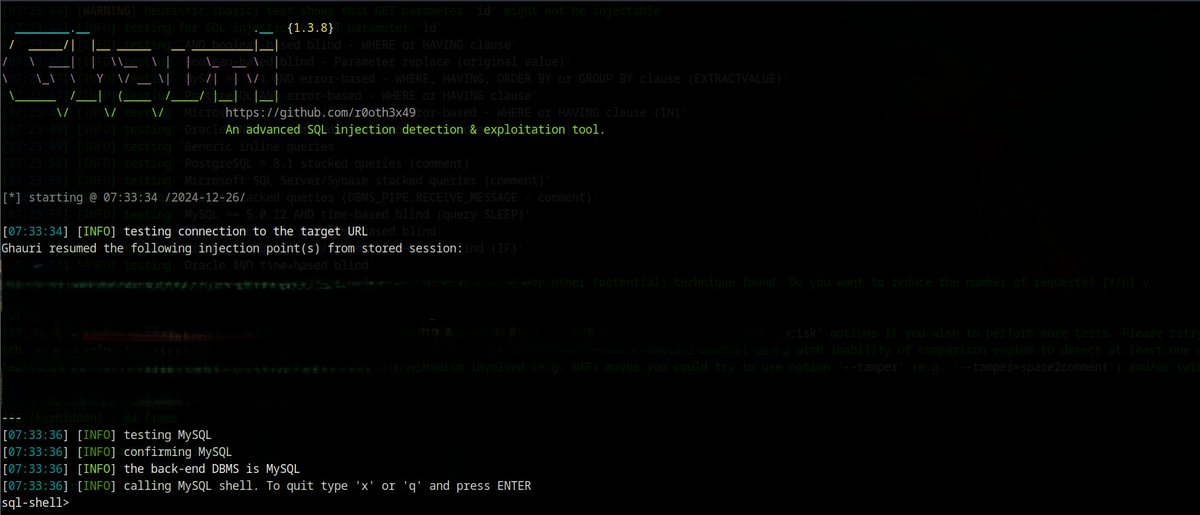
🚨SQL Injection Vulnerability Exploited!!!
Ghauri is better than SQLMap. 🛠️ SQLMap failed to find the SQLi vulnerability; it takes minutes ⏳, but Ghauri finds the SQLi vulnerability in just a minute! ⏱️✨
#BugBounty #bugbountytip #bugbountytips #cybersecuritytips

English

@theSpaghettiSec @Hacker0x01 Thanks for the kind words :) and the collabs from you and all others to reach the milestone :) hope everyone can find some peace in there own way over this holiday season :)
English

Congratulations @codecancare
The king of automation has reached over 200,000 reputation points on @Hacker0x01 🔥
Eric you are doing a great job 🪲


English

Together with my collaborator, @Besho83298755 , we turned a low-impact Blind SSRF into a critical vulnerability. Happy to share our write-up with you!
@DrakenKun/how" target="_blank" rel="nofollow noopener">medium.com/@DrakenKun/how…
#bugbountytips #Pentesting #bugbounty #CyberSecurity #security

English
@ThisIsDK999 Hi @ThisIsDK999 nice thread btw could you give some insights like how you are finding this groovy console like are you using some tool to find these type of panels and other aem related things
English
x.com/ThisIsDK999/st…
Here's the thread on how to achieve RCE via GroovyConsole in AEM even with a heavy dispatcher configuration!
Debangshu 🇮🇳🥷@ThisIsDK999
Just gained RCE on an AEM web server (real world) by exploiting GroovyConsole and an exceptional bounty! In @intigriti ! If you too, want to do super cool hax0r things such as hacking real-world web apps, use my link and sign up today! login.intigriti.com/account/regist… 🧵...(1/n)
English
@kuroOowannafly @GodfatherOrwa @Bugcrowd @ADITYASHENDE17 I checked that, but I'm not getting emails. That's why i asked to x fam..
English

@niraj_dhalani @GodfatherOrwa @Bugcrowd @ADITYASHENDE17 It will be your bugcrowd name alias means, the abc@bugcrowd... Will forward all the email to your connected email in bugcrowd 🙌
English
Received email addresses like abc@bugcrowdninja.com and cba@@bugcrowdninja.com from a client. Any tips on how I can access these mailboxes for testing or verifying? #BugBounty #Cybersecurity #EthicalHacking #InfoSecCommunity @GodfatherOrwa @Bugcrowd @ADITYASHENDE17
English
@bug_vs_me You are lucky as this iframe issue i found in another program but bounty 200$
English
In July, I submitted 12 vulnerabilities to 4 programs on @Hacker0x01. #TogetherWeHitHarder hackerone.com/last-month
English