Joe Orton retweetledi
The problem is not the reporting. There is no indication whatsoever that @FFmpeg discourages bug reports. Or benchmarks for that matter.
If you’re going to use massive AI resources to find bugs in volunteer-maintained code, don’t just drop the reports and run—provide the patches to fix them or fund people to do the work.
@halvarflake keeps on making references to closed source software. My post was specifically about how the whole behaviour is inappropriate for a FFmpeg.
@FFmpeg is not Apple, Microsoft, Google or Amazon.
Making references to what suits the needs of Microsoft is irrelevant to FFmpeg.
Google’s behaviour is rude and violates the open-source culture.
Look at the likes of my post. Lots of people agree with me.
@halvarflake would argue, as you do, that disclosure is speech. Fine. But understand that you can use your free speech and still be a vile individual.
Nobody is calling for censorship. This is not Germany 1933.
What is being demanded is respect for open-source norms.
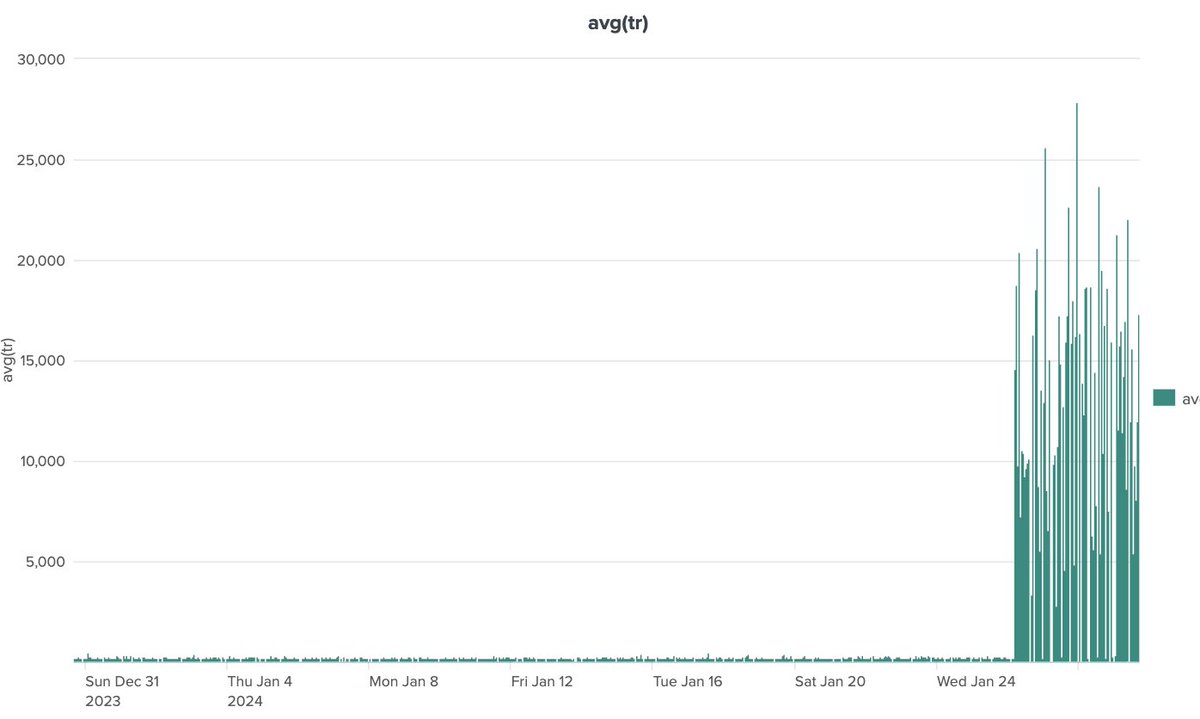
It is like the Internet. You can pull files from my blog. But I am not Google, don’t swarm me with 12 billion requests. If need to issue 12 billion requests to
my blog, build a cache first.
Intensity matters. If you snap a picture of me in passing, that’s fine. If you stalk me, follow me around and publish 100 pictures of me a day, it is harassment.
And please don’t be tone deaf… « there is no pressure ». Again: social norms. Don’t be a jerk.

English