
@iAnonymous3000 What about Samsung Knox Security based Mobiles?
null NEU
385 posts


@null_NEU
Official @null0x00 Student Chapter of @Northeastern priv/acc (Privacy Accelerationist)

@iAnonymous3000 What about Samsung Knox Security based Mobiles?



If you want to use AI, Duck.ai lets you do it privately: now with photo editing. Like our text and voice chats, the images you upload are anonymized by us and never used to train the AI. Try it out: Duck.ai > New Image > Start With An Image.

Jolla from Finland has sold their first 10.000 of their new Sailfish OS phone that doesn't use Android. It is the first mobile os that is fully European, yet still lets you download Android apps with Jolla AppSupport. Europe is making progress 🇪🇺



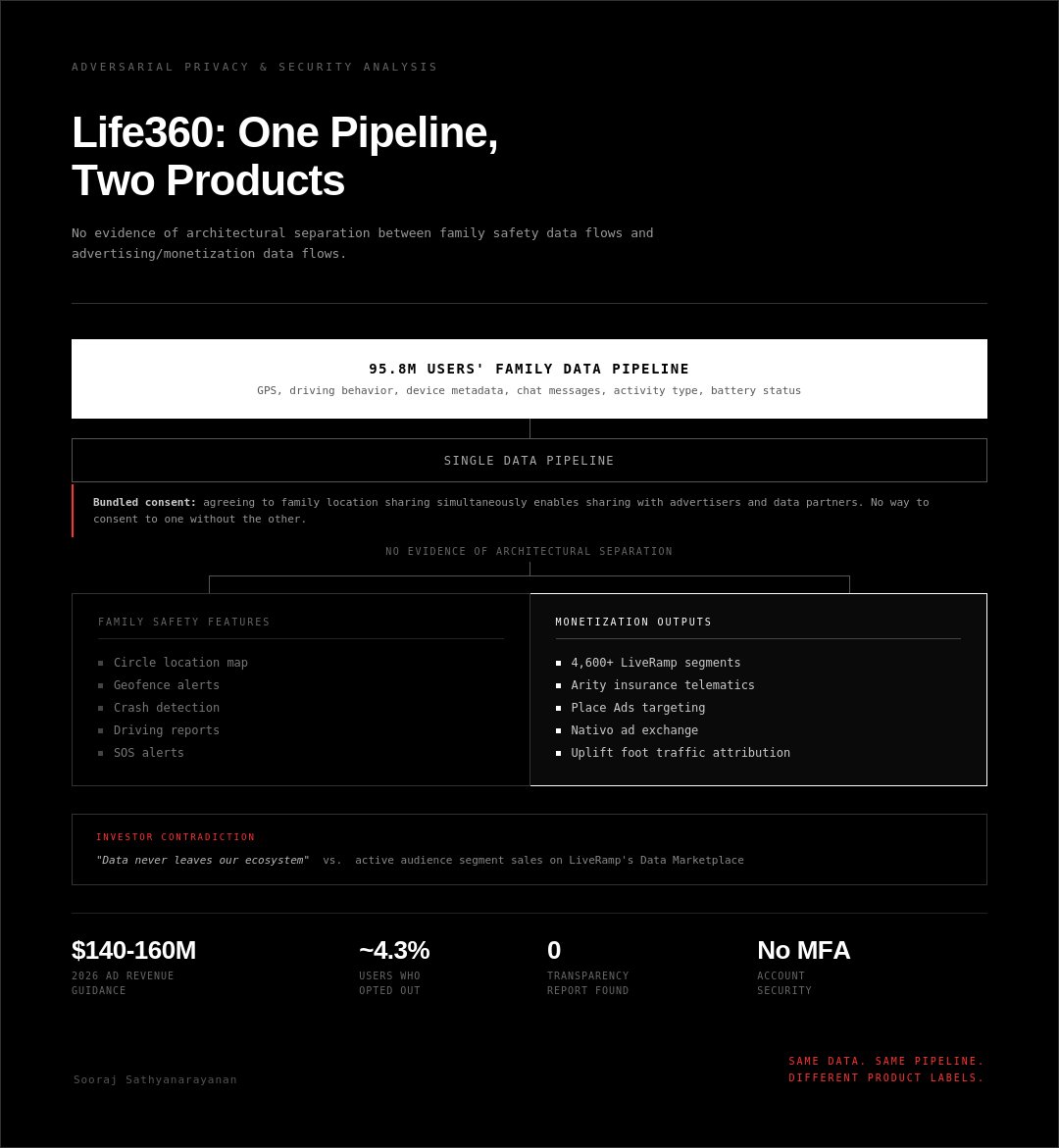
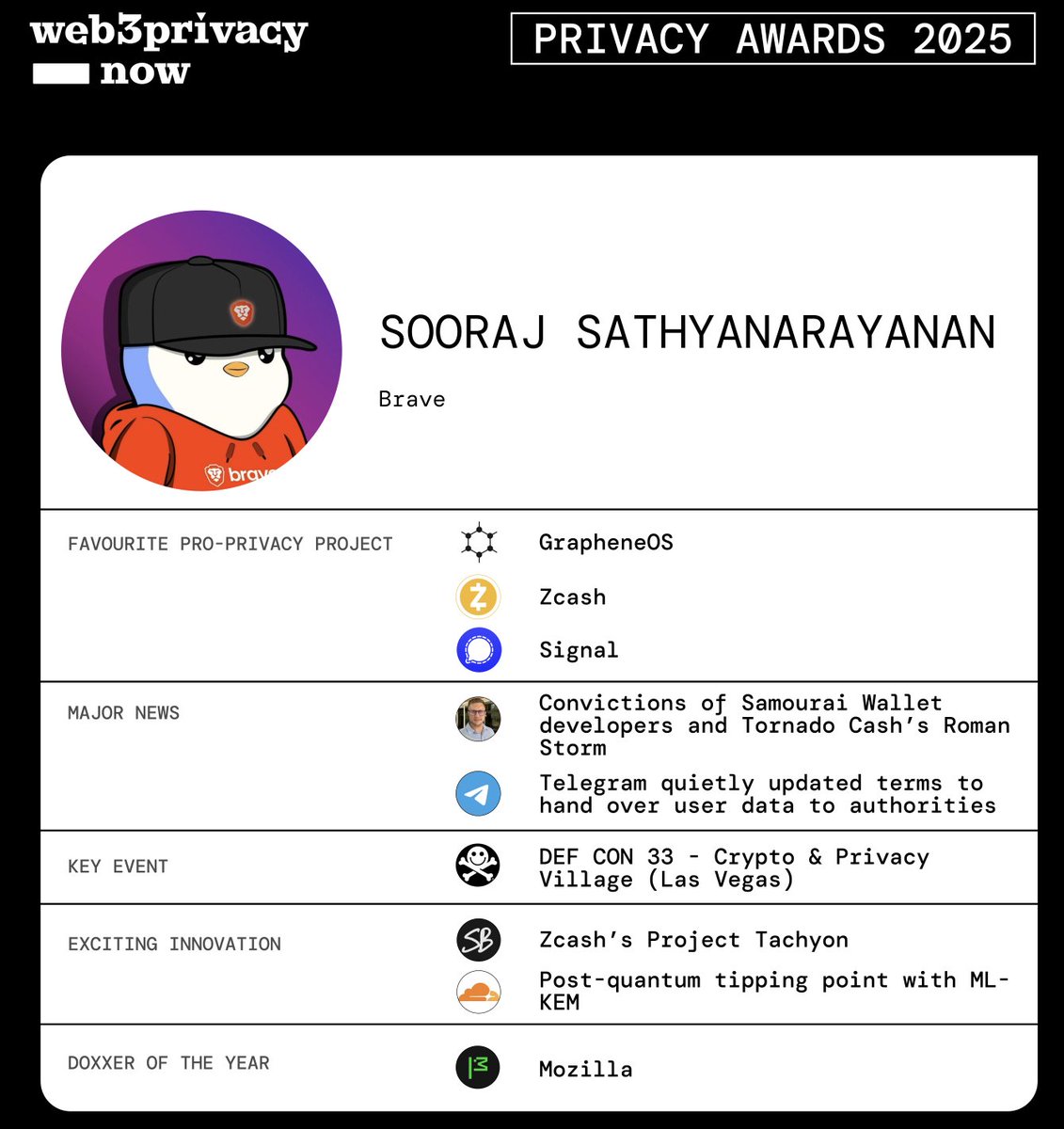
Web3Privacy now Awards 2025 are live! @iAnonymous3000 x @brave submission: Favourite pro-privacy project: + @GrapheneOS - making hardened Android accessible to regular users + @Zcash - continued leadership in on-chain privacy with shielded transactions + @signalapp - still the gold standard for private messaging, post-quantum encryption rollout was significant Major news: + Convictions of @SamouraiWallet developers and @TornadoCash's @rstormsf - set dangerous precedent that writing privacy-preserving code can be criminalized + @telegram quietly updated terms to hand over user data to authorities Key event: + @defcon 33 - Crypto & Privacy Village (Las Vegas) The most exciting innovation (research, protocol etc): + @Zcash's Project Tachyon - uses proof-carrying data to let wallets sync privately through untrusted servers, solving the scalability problem that has held back private payments + Post-quantum tipping point with ML-KEM - @Cloudflare's October report confirmed over 50% of human web traffic now secured by post-quantum key exchange, effectively mitigating “harvest now, decrypt later” threats at scale Doxxer of the year: + @mozilla - updated their Firefox privacy policy to allow selling user data, a betrayal from an organization that built its reputation on protecting users awards.web3privacy.info #w3pnawards2025


the @baseapp is now open to everyone now the real work begins base.app

Please answer the following questions in detail to help me evaluate @perplexity_ai's privacy practices. Focus on potential red flags and critical privacy concerns. 1. What specific personal information does Perplexity collect? (e.g., names, email addresses, location data, search queries) 2. Does Perplexity share user data with third parties? If yes, what data, with whom, and under what conditions? 3. What is Perplexity's data retention policy? How long is data kept, and what happens after it's no longer needed? 4. Can users request data deletion? If so, how, and are there any limitations? 5. Does Perplexity use hidden tracking technologies (e.g., cookies, pixels)? Can users opt out? 6. Are there any known privacy issues or controversies with Perplexity? (e.g., data breaches, misuse of data, legal disputes) @AskPerplexity










