Nichrome..
39 posts


@0xOmeiza If you find the entry let me know I’d do it for free i wanna be the minion in a ransomware group..
English

@hetmehtaa 😂😂😂 what the f who talks like that...
May be Ass-lickers.
English

@thedawgyg @_lopseg_ Bug bounty platforms talk about ethics but can’t even handle a $10k payout without delays and excuses
and then wonder why hackers go down the wrong path.
Seriously I have found anything like that I have just exploited them 😜😜
English

Now this does have its caveats tho. For example: If you are selling 0days/vulnerabilities in web apps, then there are laws that would make it illegal. Since even testing in any way violates the CFAA (here in the US), and the only thing that protects you from the CFAA is the Rules of Engagement of the program. All of which will say you cant sell/disclose the info to anyone else without thier permission. So if you do it for a web app (or API) then you can get in trouble. However, when you are talking about 0days in open source software that you download onto your own system, and test on your own system(s) you are not violating any law if you then sell that information to another person, since in order to violate CFAA, you have to attack systems you down own or have permission to attack, and well you have permission to attack your own system since its yours.
English

The assholes patched the bug… and just like that I’m unemployed 💻
My only ATM is gone 🏧☹️😔
#BugBounty #InfoSec #BlackHat #Hacking #CyberSecurity
English

I have been doing bug bounty since 2011 and ran a program for a multinational bank. Put everything I've learned into bugbounty.info. Target selection, recon pipelines, chain patterns, report templates, the business side. Free, no paywall, no course upsell.
English

@0xOmeiza Isn't it super hard to find the bug that have direct fund related impact ??? Like something where a user can steal the money 💰
English

@0xOmeiza Why return.. just take the risk
exploit and take the money..
English

@AegisTrail @Hacker0x01 It’s only a matter of time before we start seeing new blackhat groups emerge and all this AI hype won’t matter then
When systems feel stacked people stop caring about ethics and start thinking about survival
Love to join any blackhat group If i ever have the chance
English

@Hacker0x01 When white hats feel the legal system is rigged against them, the appeal of the "dark side" becomes a matter of anger and survival rather than ethics. Just saying 🫡
English

Point-in-time pentests can’t keep up, while fully autonomous testing creates noise.
The solution? HackerOne Agentic PTaaS pairs specially trained AI agents with elite human validation to deliver results based on real-world exploitability, not theory.
This 50-second video shows you how it works.
English

@bug_vs_me @kairo_security Hackerone is the biggest scam platform..
English

@kairo_security True but what about scam platform like immunefi
English

@thedawgyg The day isn’t far when this will create more black hat hackers, and we’ll start seeing more cyber attacks or even new hacking groups doing some nasty stuff.
After all, it’s all about survival.
English

"HackerOne Agentic PTaaS pairs specially trained AI agents"... specially trained on a decade worth of work from the largest pool of bug hunters on the planet.... without their consent... Maybe its time to find out how class action suits work and see if we have any ability to prevent them from using our work?
HackerOne@Hacker0x01
Point-in-time pentests can’t keep up, while fully autonomous testing creates noise. The solution? HackerOne Agentic PTaaS pairs specially trained AI agents with elite human validation to deliver results based on real-world exploitability, not theory. This 50-second video shows you how it works.
English

@GodfatherOrwa This is what hacking was once meant to be, but now it feels like the mouse has created its own trap.
What once started on the basis of ethics has now gone unethical.
corporations are always the evil ones.
English

To be honest waiting this to happen and then I start testing the AI and will spend very very good time to hack it and then
without reporting will gift the community best and biggest disclosure in history
😊
H4x0r.DZ 🇰🇵@h4x0r_dz
HackerOne is invading privacy by allowing its AI to access researchers’ bug reports without consent. This is unethical and exploits the community that built the platform. It’s time to respect creators and stop data misuse. #BoycottHackerOne
English

@0xlevi_87 Hey is there any way if you can share the target if it's not private invite. Just curious
English
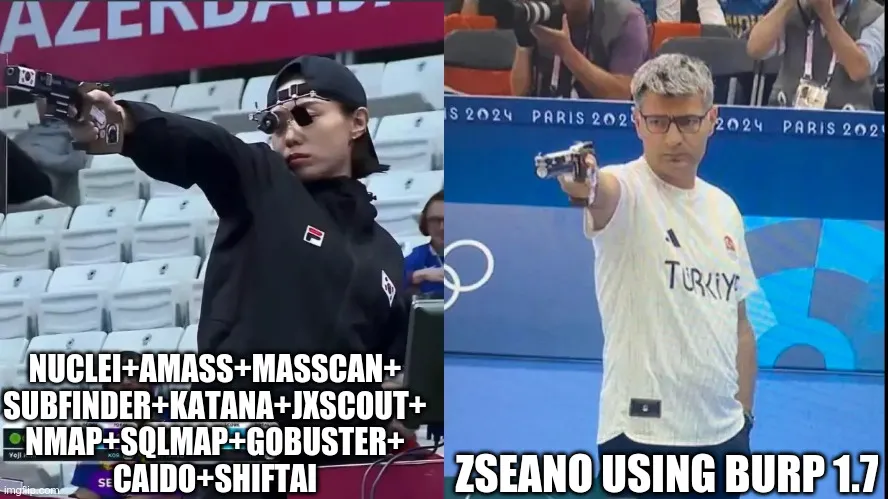
Day 4 - Bug Bounty
- Did more recon on target using new tools
- Found more subdomains but not interesting
- 1 more day recon and I'm going to start manual hunting.
- Just an update for myself: found 10 vuln in a day in office pentest for client.
2 were critical:)
#BugBounty
English

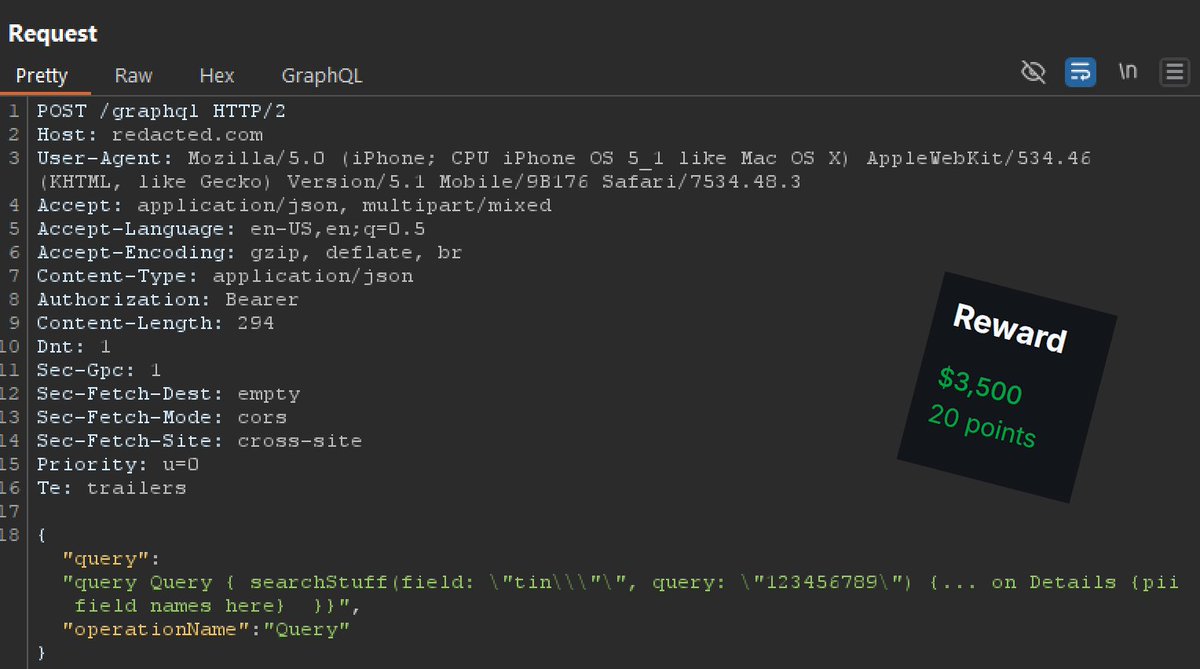
Weird graphQL IDOR / access control bypass:
In this one, graphQL would check the "tin" (tax identification number), if supplied, against the Bearer token. If the Bearer did not have access to the tin, you would get access denied. Normal stuff there. So my thought was, how could I make the server still lookup the tin value without the access check?
It regularly expected:
\"tin\"
This causes the server, since "tin" is present, to check access control prior to returning data.
What worked was:
\"tin\\\"\"
So adding \\\" after tin bypassed the access control logic (for some reason), meanwhile the graphQl query still ran and sent back the PII for any TIN I sent it.
#bugbounty is just strange sometimes. Some of the battle is finding neat endpoints and places, and some of it is endless tinkering.
English