Erwan Chevalier retweetledi

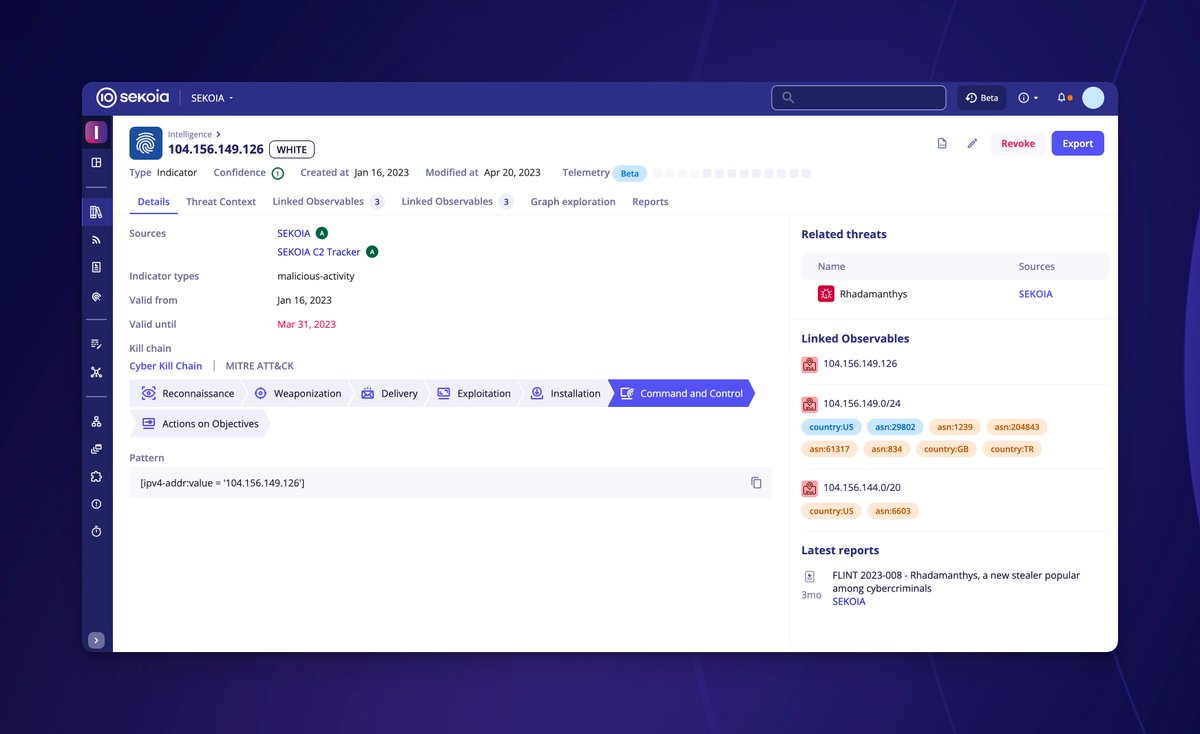
At #VB2023 Sekoia.io's Guillaume Couchard & @r1chev will outline the infection chains used by commodity malware, common detection methods used against them, & how generic detection rules on these chains can help in the fight against botnets. virusbulletin.com/conference/vb2…

English