Danijel Grah retweetledi

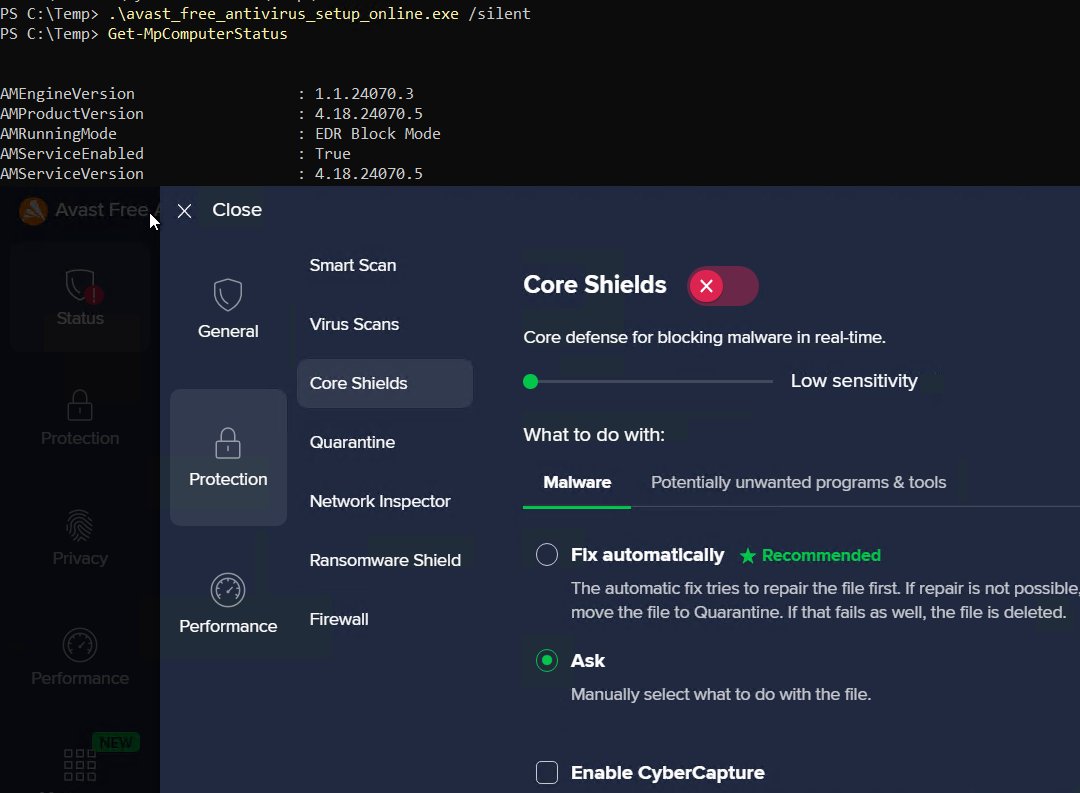
Attackers don’t need stolen certificates. They only need 8 bytes. By flipping 4 bytes in the PE checksum and 4 in the certificate padding, they generate 2⁶⁴ unique driver hashes while keeping Microsoft’s digital signature valid.
Why it matters:
- Those 8 bytes sit outside the region Windows verifies.
- Every variant looks “signed and trusted.”
- Hash-based blocking becomes useless overnight.
That’s how TrueSightKiller evolved into 2,500+ signed variants. All trusted by Windows, all capable of killing EDRs in seconds.
Check out: magicsword.io/blog/truesight…

English