Sabitlenmiş Tweet
Arminius
58 posts


Arminius
@rawsec
Your friendly infosec fanboy. I do bug bounty hunting, CTFs, some FOSS, subpar chess. HoF: Google, Chromium, Firefox, Facebook, Paypal et al
In the wild Katılım Ekim 2013
1.2K Takip Edilen1.1K Takipçiler

@rawsec Hi! I love Semshi. I was wondering if you still work on it or accept pull requests. Wanted to know if it's worth doing the work to add docstring hightlighting support.
English

Well, seems like @kucoincom didn't take their security that seriously in the first place #KuCoinHack #KuCoin
Arminius@rawsec
Sigh. It's 2020. Crypto exchange @kucoincom just awarded me a $28.49 bounty for an unconditional XSS vuln on their main domain. (via 3rd party component but still...) A little deceitful to call that a #bugbounty program 🤷 @gan_chun $KCS
English

@rawsec Hi Arminius, Our security team did get your report and we are contacting them again to find out what the status of it is.
English

Hey @krakenfx @krakensupport. I reported a major security vulnerability on your exchange 74 days ago. It's still open, and both your support and security team are ghosting me. Any help? #bugbounty $btc
English

Sigh. It's 2020. Crypto exchange @kucoincom just awarded me a $28.49 bounty for an unconditional XSS vuln on their main domain. (via 3rd party component but still...) A little deceitful to call that a #bugbounty program 🤷 @gan_chun $KCS
English

@krakensupport I reported a security vulnerability on @krakenfx a week ago, but you did not reply. Could you have another look?
English

Arbitrary code execution vulnerability in Vim < 8.1.1365 and Neovim < 0.3.6 via modelines. 😬 Also, why you should not use Vim with default config, or cat without -v. github.com/numirias/secur…
GIF
English

@Rhynorater Spending more time on potential param pollution bugs like messing with bad encoding is a great point
English

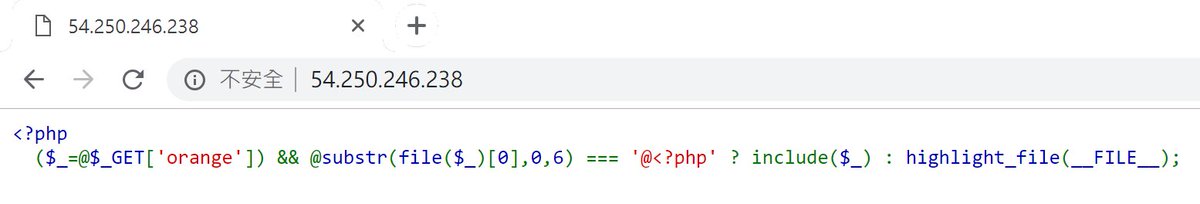
@LLNSPay Like, say, php://filter/string.strip_tags/convert.base64-decode/resource=/proc/self/environ with a crafted "Accept:" header, hoping Apache sets HTTP_ACCEPT in env. (using strip_tags so that a payload ending with <x cuts off rest). But my blind attempts didn't get me anywhere.
English

@LLNSPay I was thinking stream filters (php://filter/...) on a local file that reflects parts of the request (maybe /proc/self/environ or logfiles). Chaining some filters cleverly (base64-decode, etc.), the local file wouldn't even need to start with `@<?php`. But had no success.
English

@orange_8361 I want my weekend back. And my sanity. :-) Gonna dream of PHP filters tonight...
English

HITCON CTF(also the first DEFCON pre-qualify CTF) is now running! I designed several web challenges and here is the one -
One Line PHP Challenge!
ctf2018.hitcon.org
English

My write-up for Hackover CTF "cyberware" challenge. Using dir trav and manually obtaining packfiles from git meta dir. Was a nice little peek into git internals. security.meta.stackexchange.com/a/3087/9538
English

Where's Bobby Tables when you need him
StackExchange Status@StackStatus
We're investigating a database overload and working to resolve it ASAP.
English

@StackStatus "He Joel, our Microsoft Access trial is expiring in October" - "Make it a P4 ticket then, still plenty of time"
English