Sabitlenmiş Tweet
retrage
8K posts
retrage
@retrage
UEFI/Rust Hypervisor Firmware/VMM/Container Runtime/aarch64/RISC-V/未踏2017/スパクリ
Tokyo, Japan Katılım Kasım 2008
434 Takip Edilen994 Takipçiler
retrage retweetledi

retrage retweetledi

Lenovo acquires Phoenix Technologies’ BIOS business
videocardz.com/newz/lenovo-ac…
Lietuvių
retrage retweetledi
retrage retweetledi
Kernel/VM探検隊@つくば No3 に参加を申し込みました! kernelvm.connpass.com/event/381371/?… #kernelvm
日本語
カーネルバイパスによる通信高速化の基本 に参加を申し込みました! iijlab-seminars.connpass.com/event/385113/?…
日本語
Daniel is stepping down as a GRUB maintainer GRUBで長いことメンテナやっていたDaniel Kiperさんやめるそうです lists.gnu.org/archive/html/g…
日本語
retrage retweetledi

my talk at fosdem kernel devroom (usermode linux without MMU)
speakerdeck.com/thehajime/user…
English
retrage retweetledi
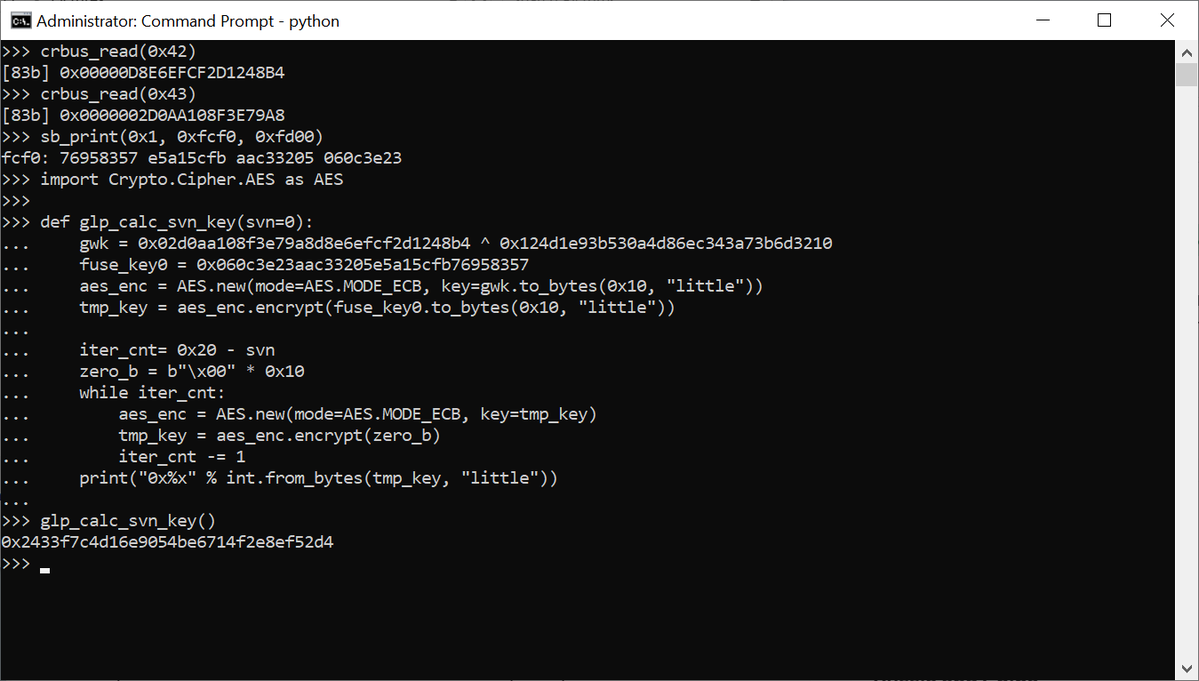
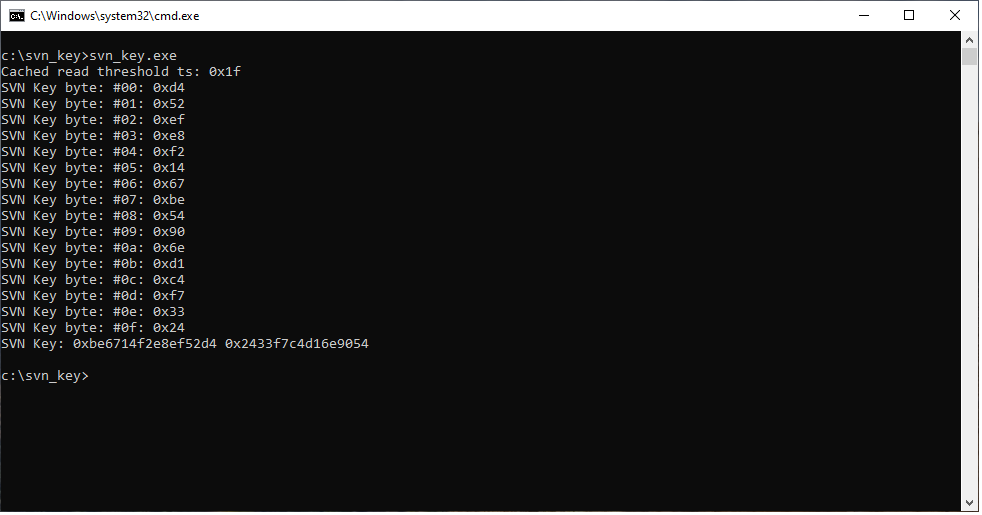
🛡️勉強会×生成AI×責任ある検証で脆弱性を発見🛡️
社内のセキュリティ勉強会での学びをきっかけに、生成AIを活用した調査手法でハイパーバイザの脆弱性を発見しました。
調査に生成AIをうまく使いつつ、最後は人が責任を持って検証と報告を行った実践記録をぜひご覧ください。
ricercasecurity.blogspot.com/2026/01/blog-p…

日本語
retrage retweetledi
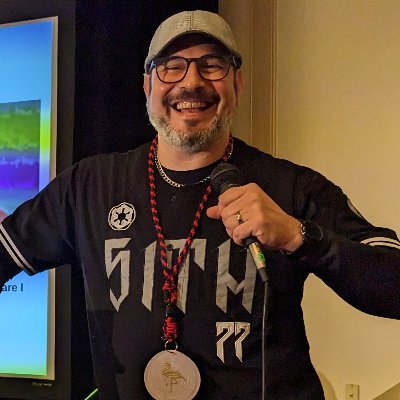
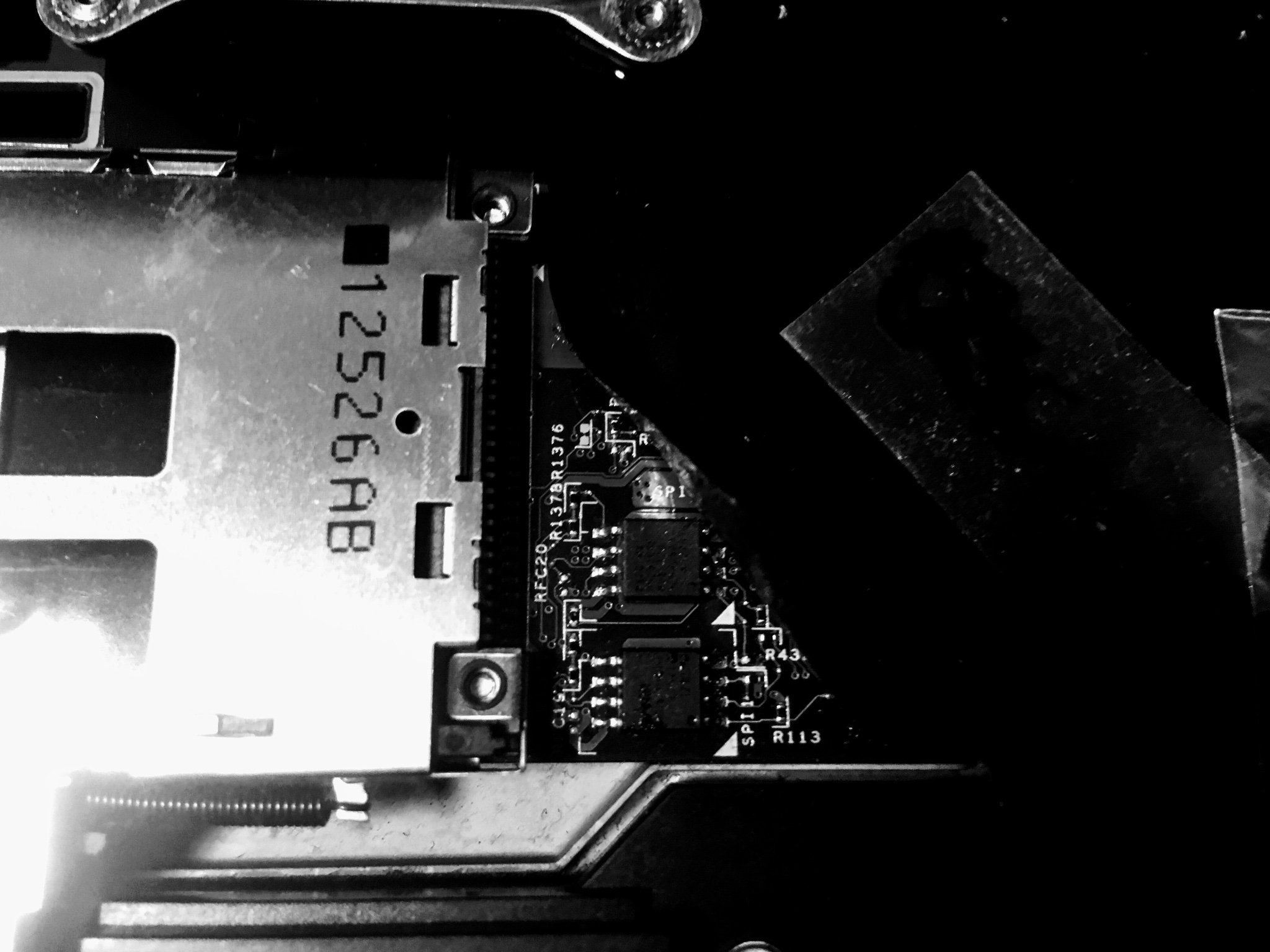
This week’s reporting on the alleged Everest ransomware breach of ASRock Rack should be a wake-up call for anyone relying on modern server, storage, and cloud hardware. When an enterprise vendor’s internal repositories of firmware, BIOS, BMC code, diagnostic tools, and drivers are exposed, supply chain integrity is in jeopardy.
Adversaries gain insight into board layouts, update mechanisms, and secure boot flows, which accelerates vulnerability discovery and makes it easier to craft implants that look “authentic”. Implants come in many shapes and forms,s including repackaged drivers, UEFI images, and recovery media. In the worst case, compromise at this level undermines the hardware root of trust itself: if attackers can subvert firmware signing, update channels, or UEFI components, they can persist below the operating system, survive reimaging, and silently bypass many controls.
Incidents like this underscore that supply-chain attacks targeting firmware and UEFI are now strategic targets, not edge cases. Defenders need to assume that detailed knowledge of platform internals is in adversary hands and respond by monitoring below the OS as a first-class requirement. Measuring firmware integrity at boot, continuously attesting critical components (UEFI, BMC, NICs, RAID controllers), and watching out-of-band management paths for anomalous behavior is important. The trust model for infrastructure is shifting, and security programs that do not include firmware and UEFI telemetry are already behind the curve.
Article: cyberdaily.au/security/13120…

English