Sabitlenmiş Tweet

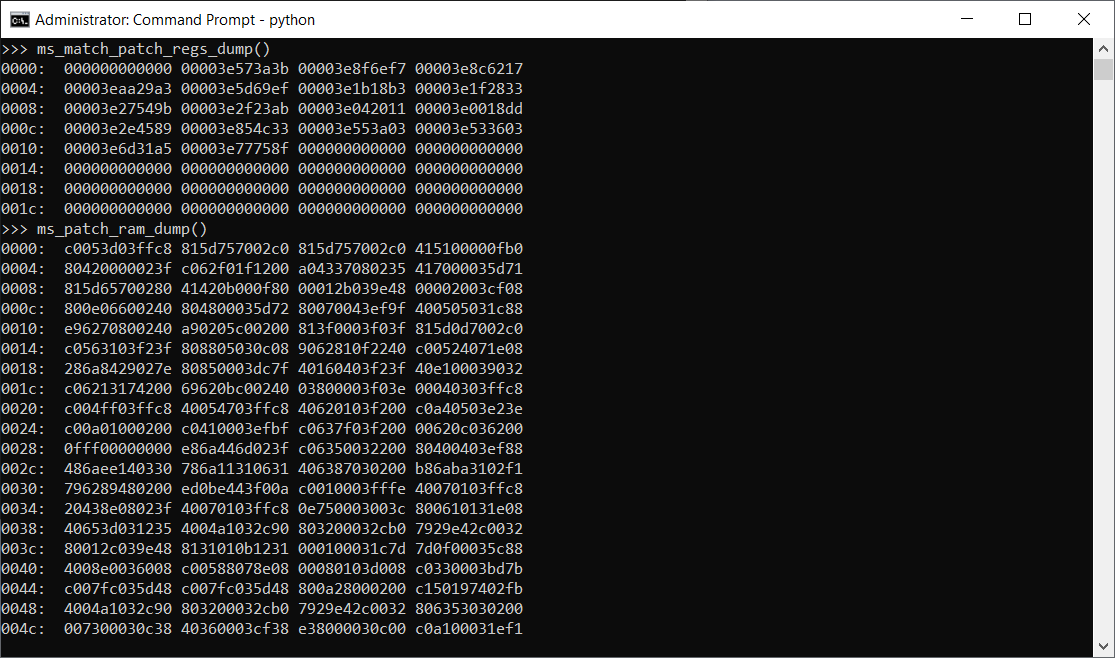
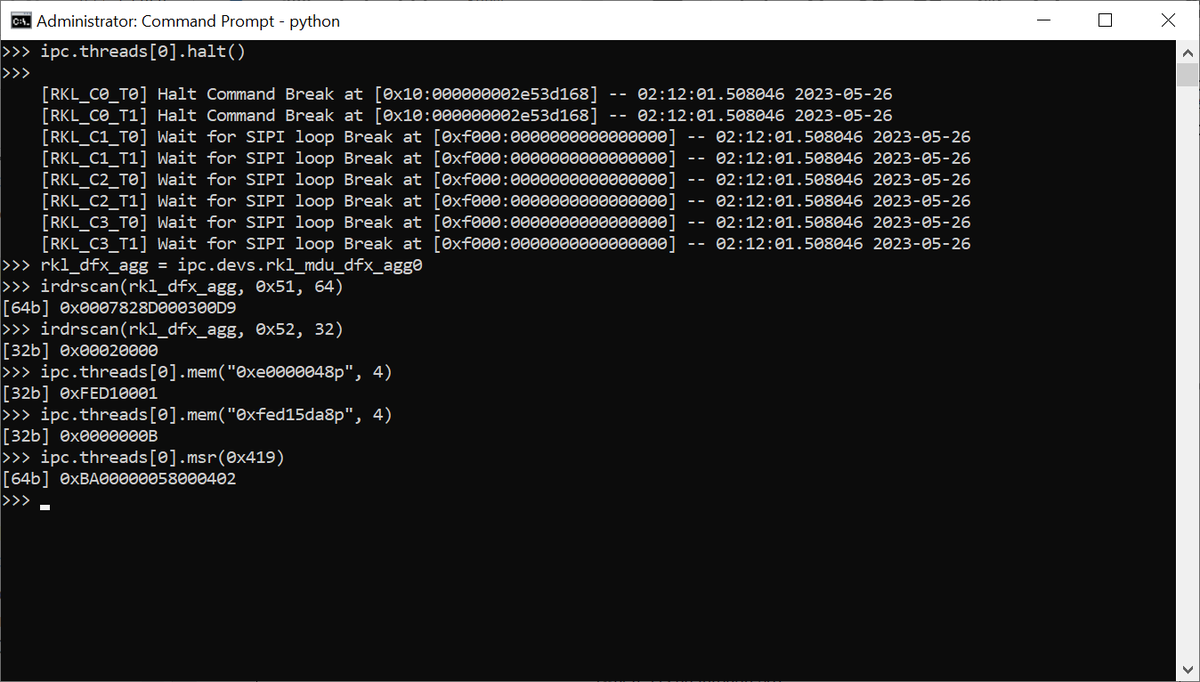
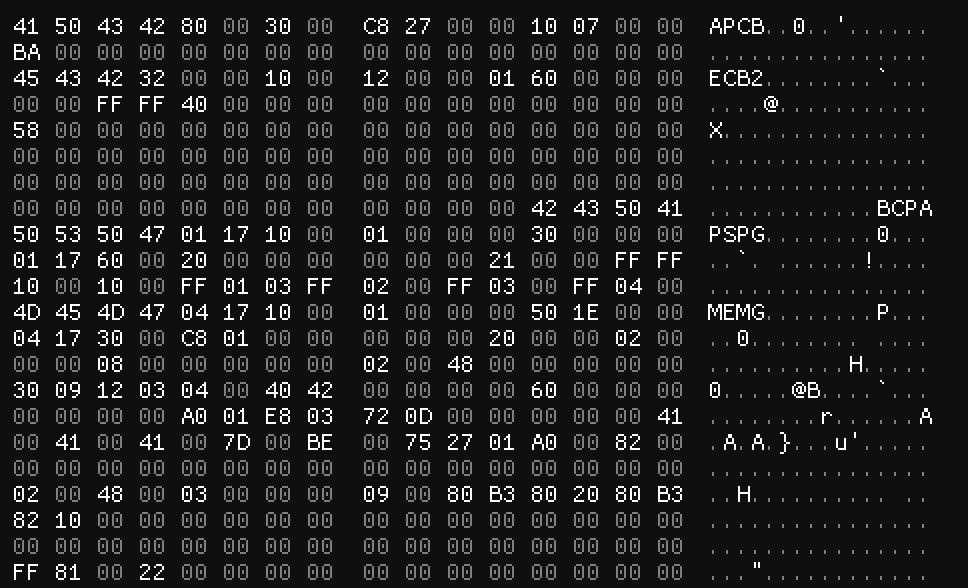
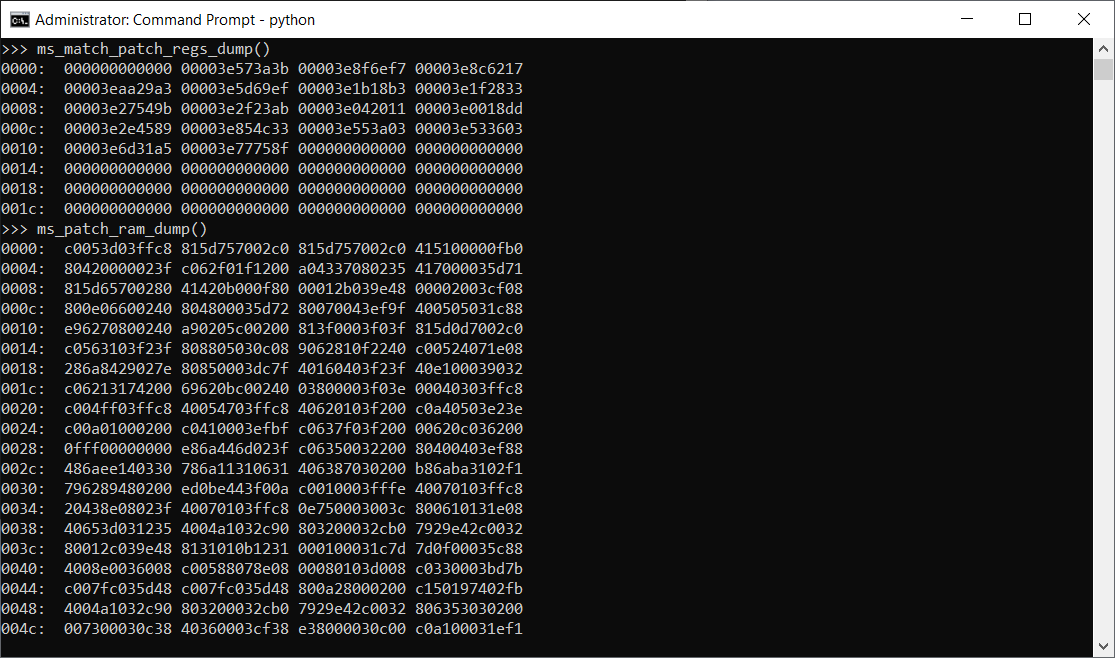
Finally, the casket is opened: we (+@h0t_max and @_Dmit) have extracted Intel x86 microcode! One more Intel "top secret" information gets revealed...
github.com/chip-red-pill/…

English
Mark Ermolov
1.6K posts


@_markel___
I research security of Intel platforms. I don't work for Intel