xerxes
16 posts

xerxes
@rip_xerxes
noob hacker full time student 日本語勉強している
Katılım Mart 2025
95 Takip Edilen120 Takipçiler

After DefCon, I started bug bounty hunting, made $5,200 on @Bugcrowd and completed an @intigriti CTF.
Looking back, I’m proud of what I accomplished in 2025.
I’m taking 2 weeks off.
See you all next year! 🥳
English
xerxes retweetledi

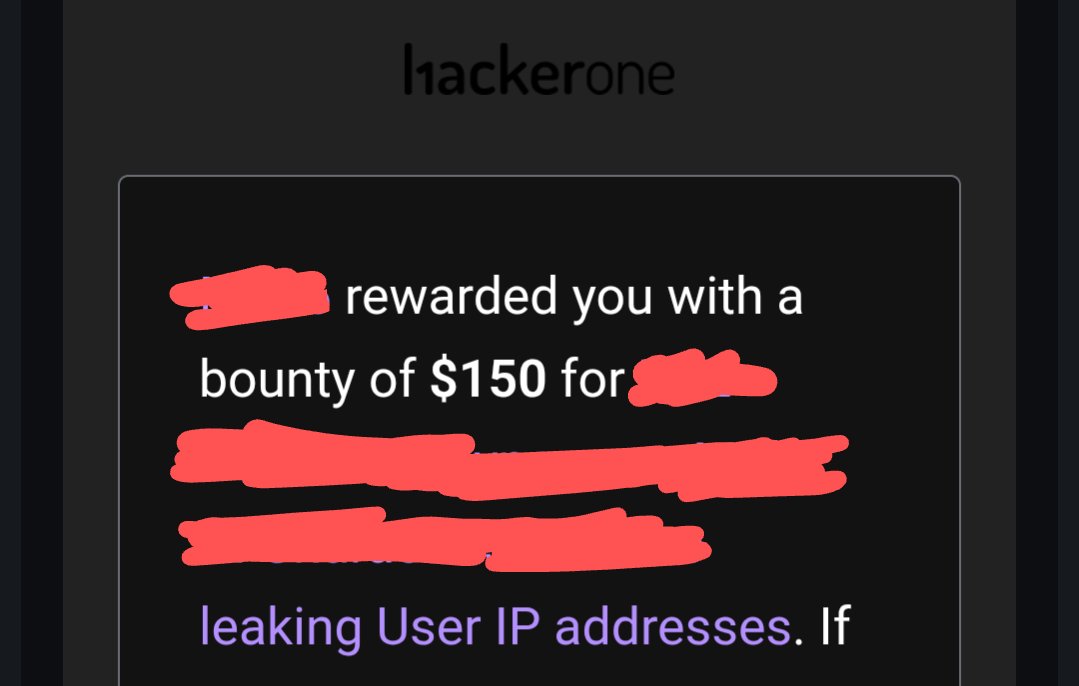
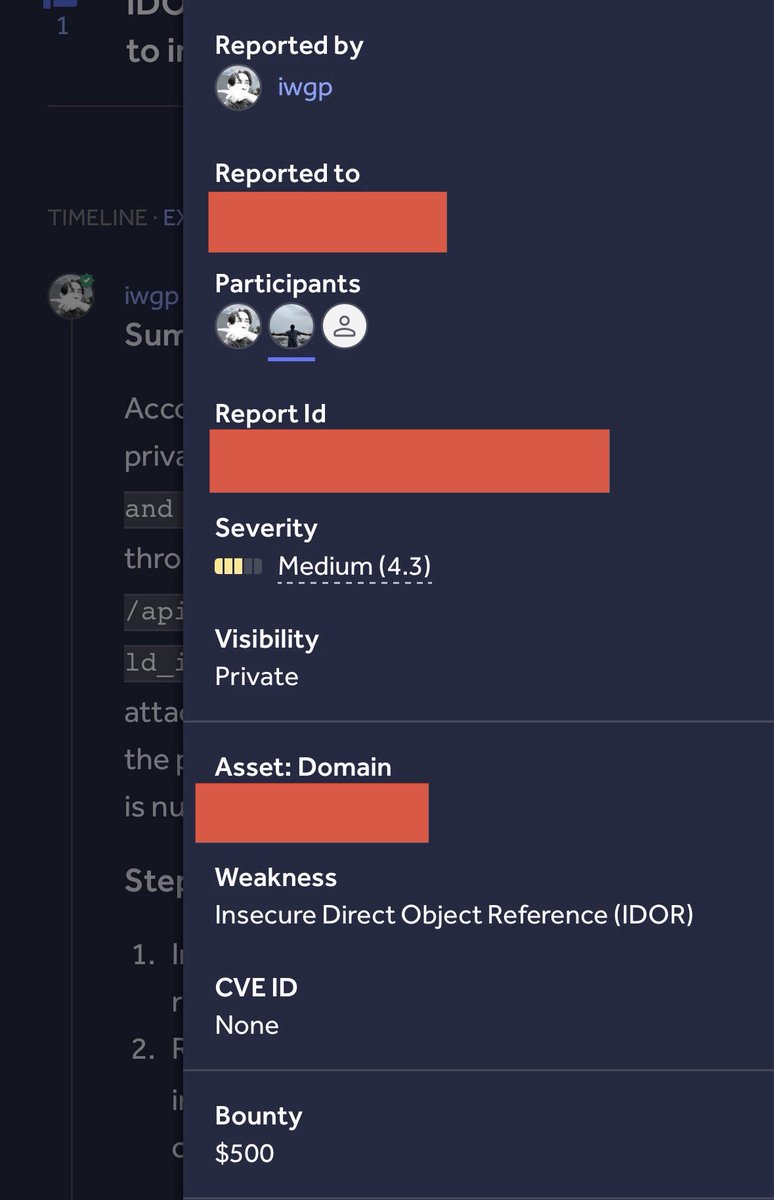
Yay, I and @rip_xerxes were awarded a $500 bounty on @Hacker0x01! hackerone.com/xlsize0bruh #TogetherWeHitHarder
English
xerxes retweetledi

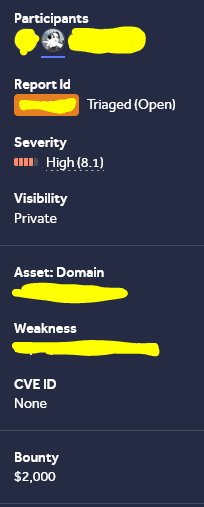
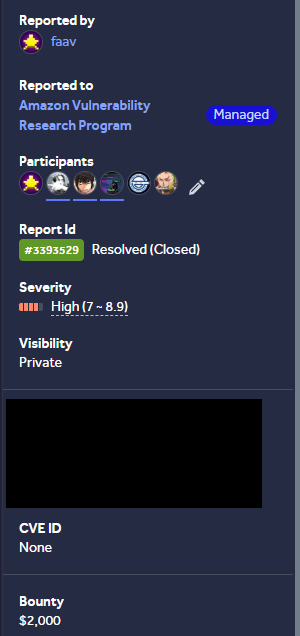
$2,000 for Amazon vulnerability collab with @davi1337_ @0daystolive and @rip_xerxes on @Hacker0x01 :)
hackerone.com/faav
#TogetherWeHitHarder #BugBounty (Forgot to post this)
English

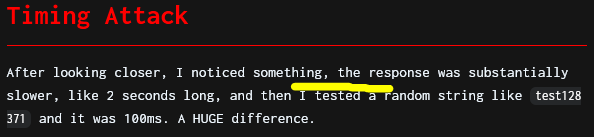
Part II: I found a bypass to Microsoft's fix using a Timing Attack to leak the Microsoft Event Registration database again! Here's the writeup: blog.faav.top/microsoft-even… #BugBounty #bugbountytips
Faav@efaav
I found another vulnerability to leak the Microsoft Events Registration and Waitlist databases, this could've leaked tons of PII. Here's the writeup: blog.faav.top/microsoft-even… #BugBounty #bugbountytips After this, I found a bypass to Microsoft’s fix and will be releasing Part II in a few days.
English
xerxes retweetledi

Earlier this year, @infosec_au and I discovered multiple vulnerabilities that allowed us to access the back office admin panel of ClubWPT Gold (the World Poker Tour's website) where we could manage customer data, KYC, and more.
Read the writeup here:
samcurry.net/hacking-clubwp…
English
xerxes retweetledi

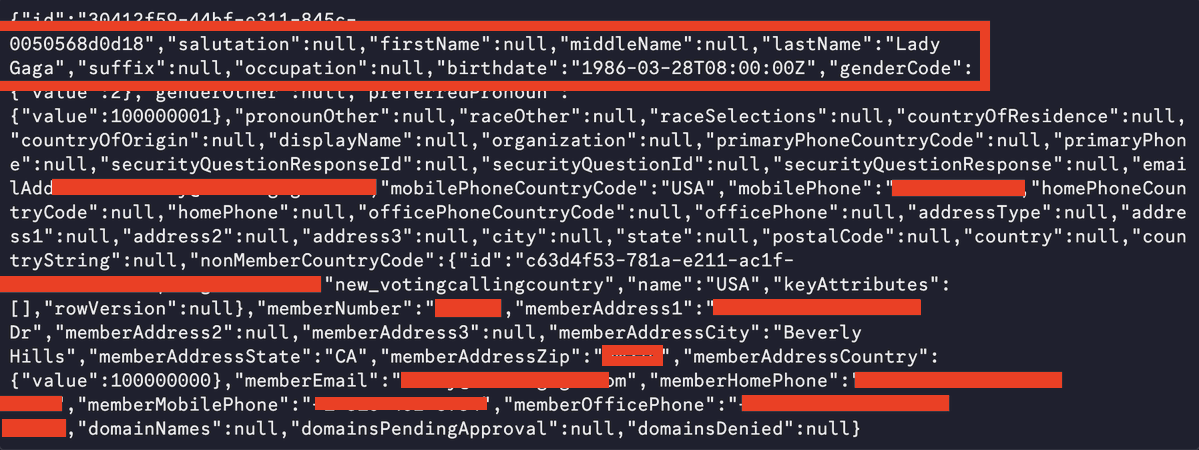
We accidentally got access to every Academy Award nominee's home address and phone number.
Before last year's Oscars Ceremony, together with @iangcarroll and @samwcyo, we found a way to leak every nominee's PII, including phone numbers and home addresses of the biggest actors around the world - from @ladygaga to @JaredLeto.
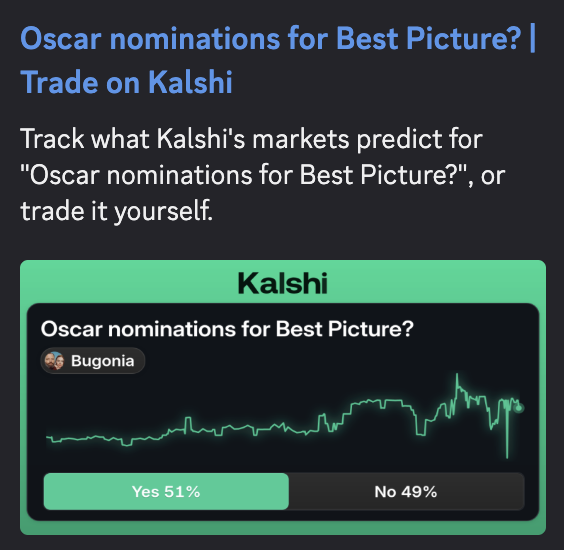
We were interested in the security of award ceremony shows, especially with the rise of @Kalshi and @Polymarket betting on winners. We wanted to check if it would be possible for an attacker to leak the winner before the official announcement.
While we didn't find evidence of that, we did notice that two of the Academy Awards' primary services had their APIs publicly facing without any authentication.
One offered general information about the ceremony, and the other allowed nominees to sign up and vote.
The first one - globalservices.oscars.org/Payments/GetHi… - allowed us to fetch every transaction made to sign up as a nominee for the Academy Awards, including member IDs and last four digits of credit cards.
With one request, we could get hundreds of contact IDs which could be chained with another API to correlate them to actual Hollywood actors via submissionsapi.oscars.org/api/Report/Get…{ID}
Randomly skimming through the results, we saw they leaked full names, home addresses, phone numbers, email addresses of famous Hollywood stars.
We responsibly disclosed the findings to the Academy Awards on January 14th, which were promptly fixed.


English