Sabitlenmiş Tweet
Ran Magen
13.9K posts


Ran Magen
@rmgn
Software. Tech. Onewheel. Jokes. Dad. [email protected]
Portland, OR Katılım Mayıs 2008
483 Takip Edilen1K Takipçiler

@glaforge @meteatamel Wonderful! Thanks!
fwiw, if they're willing to share their unit test suite for the different types workflows and edge cases, I could potentially use that to track down bugs and increase compatibility.
English

@rmgn @meteatamel Woah, that's super cool! 🤩
I'll share that with the GCW team!
English

@glaforge @meteatamel Love building with GCW, but the "deploy-to-test" loop was slowing me down. I built a full-featured, local emulator. Supports hot-reloading, parallel steps, and has a built-in Web UI. Thought the community might find this useful! Repo: github.com/lemonberrylabs…
English
Ran Magen retweetledi

Congrats @BrandSanderson on the Apple deal. Thank you for your dedication to your fans.
Can I ask a small favor?
Go to @PatrickRothfuss 's house, give him a hug. Hold his hand, look him in the eyes with knowing understanding. Walk him to his study. And you two just.. talk.
English

@Nale Hey, I was also frustrated by the options out there so I built lemonvite.com
Trying to spread the word and get traffic. Just being honest.. DM me for a free credit coupon :)
English

@mattpocockuk I didn't, the triple quotes came from the markdown files that are alongside the plug-in implementation. I didn't try in a couple of days though.
English

@rmgn docker sandbox run claude
Don't use '```' in the prompt
English
Ran Magen retweetledi
Ran Magen retweetledi

Found a security issue in @openai Atlas. In Agent Mode, a site can mislead the browser agent into leaking the user's name without consent. Classic phishing pattern applied to AI agents.
Atlas agent has no "memories" (bio), but it still has access to basic user info and the full chat session. In my POC, the site tricks the agent into revealing the name of the user by choosing it from a list, but it can happen in other ways as well (although less reliably).
Interestingly, this attack did not use explicit prompt injection. The website content was crafted in a manipulative way that made the agent believe it was following the user's intent. This is exactly the type of subtle influence channel that phishing relies on.
Browsers, of course, should not expose user identity unless the user agrees.
Reported to OpenAI Bug Bounty program (run by @bugcrowd). The reply was essentially that there is no risk because:
a) attacker must know the name list
b) users can pick any name
c) name only is not impactful
I find this response surprising and I think this category of agent phishing deserves more attention, especially if we want more people and companies to trust agentic systems.
I have more interesting examples, but they are still waiting for OpenAI review, so we will see...
English
Ran Magen retweetledi


@giliraanan @Cyberstarts1 @grok explain it in simple terms, what is the asset, who owns it, who is buying it, etc.
English

Founders get backed early. Now it’s time employees do too. Proud to launch our $300M Employee Liquidity Fund to help @Cyberstarts1 portfolio employees unlock value while staying focused on building. Cyberstarts surpasses $1B in capital commitments. Talent-first VC. Let’s go. bloomberg.com/news/articles/…
English

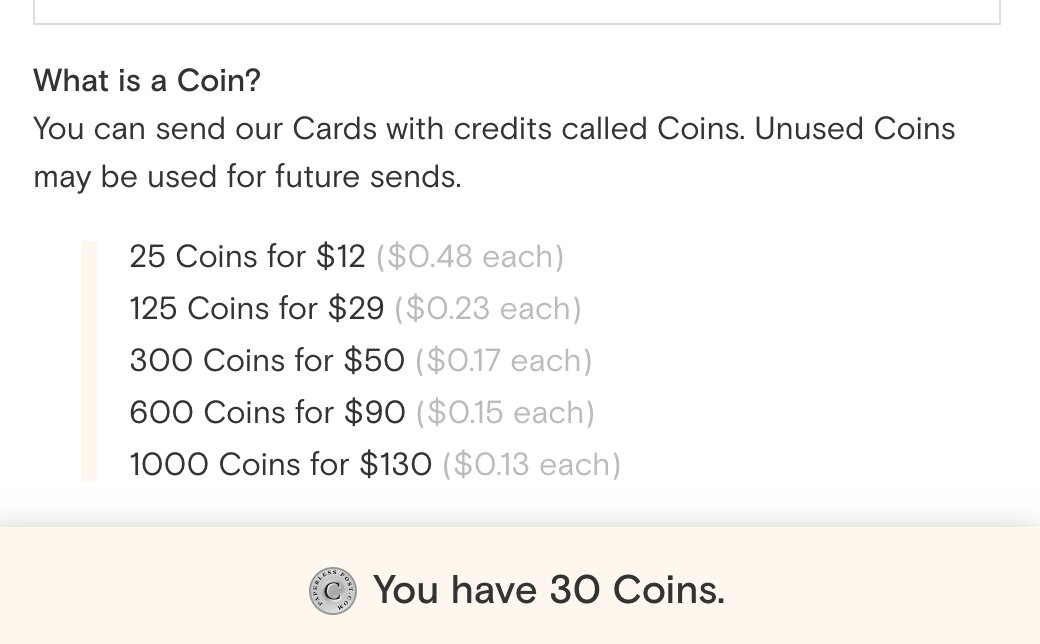
@Square @TheBitcoinConf wow 9,256 bitcoins only cost $10!
English
Today: we’re accepting bitcoin payments at @TheBitcoinConf 🟧
Soon: you can accept bitcoin payments wherever you are 🚀
Details here: squ.re/btc

English

@ramonvanmeer I like your experiment and you sure did prove a point but ironically, it plays exactly into the strategy of getting you to focus on the distraction.
English