☠ Román Medina-Heigl Hernández
14.5K posts
☠ Román Medina-Heigl Hernández
@roman_soft
CyberSecurity junkie since 1993. Manager, strategist/advisor and engineer. CTF player (#int3pids). Occasional researcher. Ex-Founder #RootedCon. Always learning



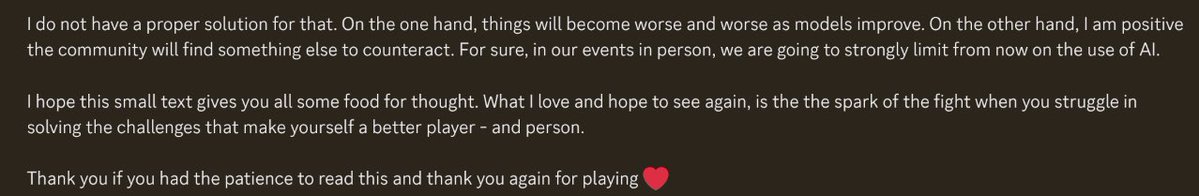
Software horror: litellm PyPI supply chain attack. Simple `pip install litellm` was enough to exfiltrate SSH keys, AWS/GCP/Azure creds, Kubernetes configs, git credentials, env vars (all your API keys), shell history, crypto wallets, SSL private keys, CI/CD secrets, database passwords. LiteLLM itself has 97 million downloads per month which is already terrible, but much worse, the contagion spreads to any project that depends on litellm. For example, if you did `pip install dspy` (which depended on litellm>=1.64.0), you'd also be pwnd. Same for any other large project that depended on litellm. Afaict the poisoned version was up for only less than ~1 hour. The attack had a bug which led to its discovery - Callum McMahon was using an MCP plugin inside Cursor that pulled in litellm as a transitive dependency. When litellm 1.82.8 installed, their machine ran out of RAM and crashed. So if the attacker didn't vibe code this attack it could have been undetected for many days or weeks. Supply chain attacks like this are basically the scariest thing imaginable in modern software. Every time you install any depedency you could be pulling in a poisoned package anywhere deep inside its entire depedency tree. This is especially risky with large projects that might have lots and lots of dependencies. The credentials that do get stolen in each attack can then be used to take over more accounts and compromise more packages. Classical software engineering would have you believe that dependencies are good (we're building pyramids from bricks), but imo this has to be re-evaluated, and it's why I've been so growingly averse to them, preferring to use LLMs to "yoink" functionality when it's simple enough and possible.



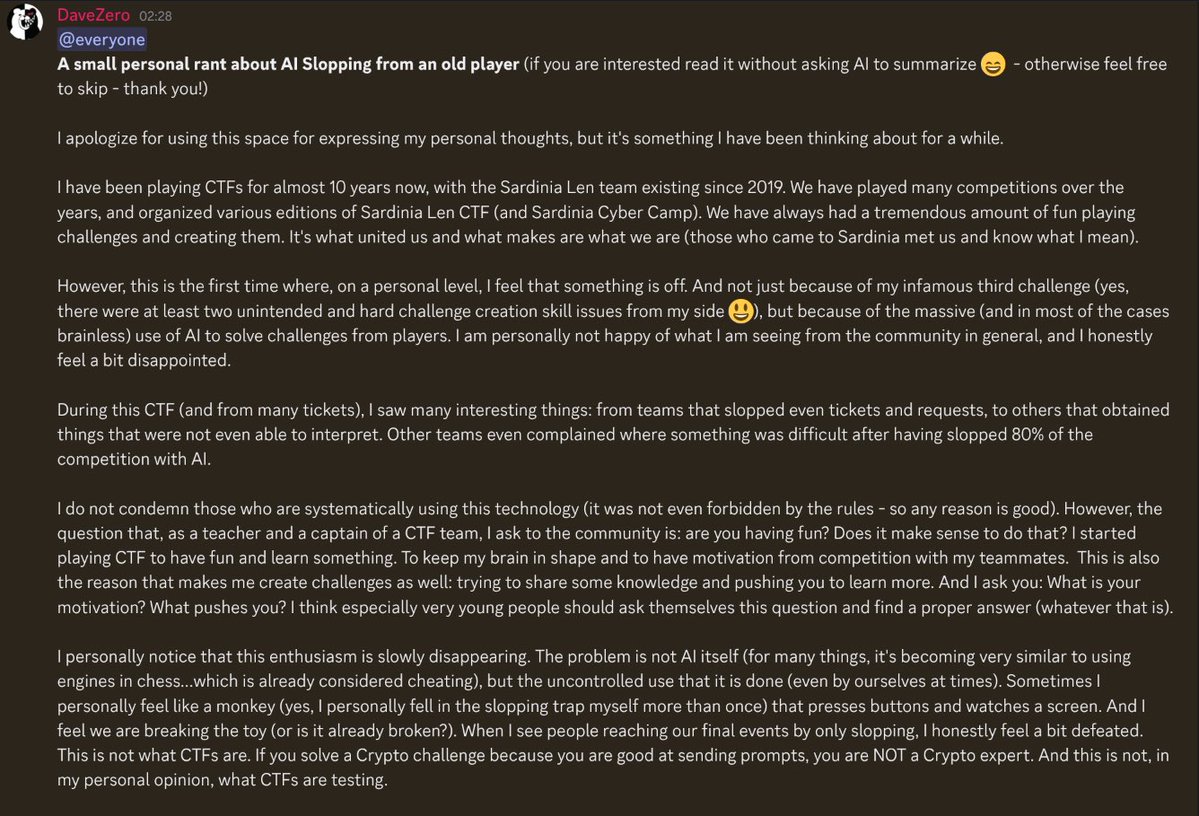
I started playing CTFs in 2022, and LLMs definitely changed the **competitive** CTF scene a lot, especially since mid-2025. I also started using LLMs in late 2025. Yes, those models did one-shot many challenges, but what's the fun of slopping them? I learned absolutely nothing 🥲
Remembering memories with my friend Felix ‘FX’ Lindner @41414141, hacker extraordinaire with a huge heart, who passed away last week. Whether in Berlin, San Francisco, or Sao Paulo, hanging out with FX was never dull. FX was prophiled in @phrack #68 phrack.org/issues/68/2
![[NN2ed] s4ur0n](https://pbs.twimg.com/profile_images/2012464407930900480/5i0P7zfp.jpg)

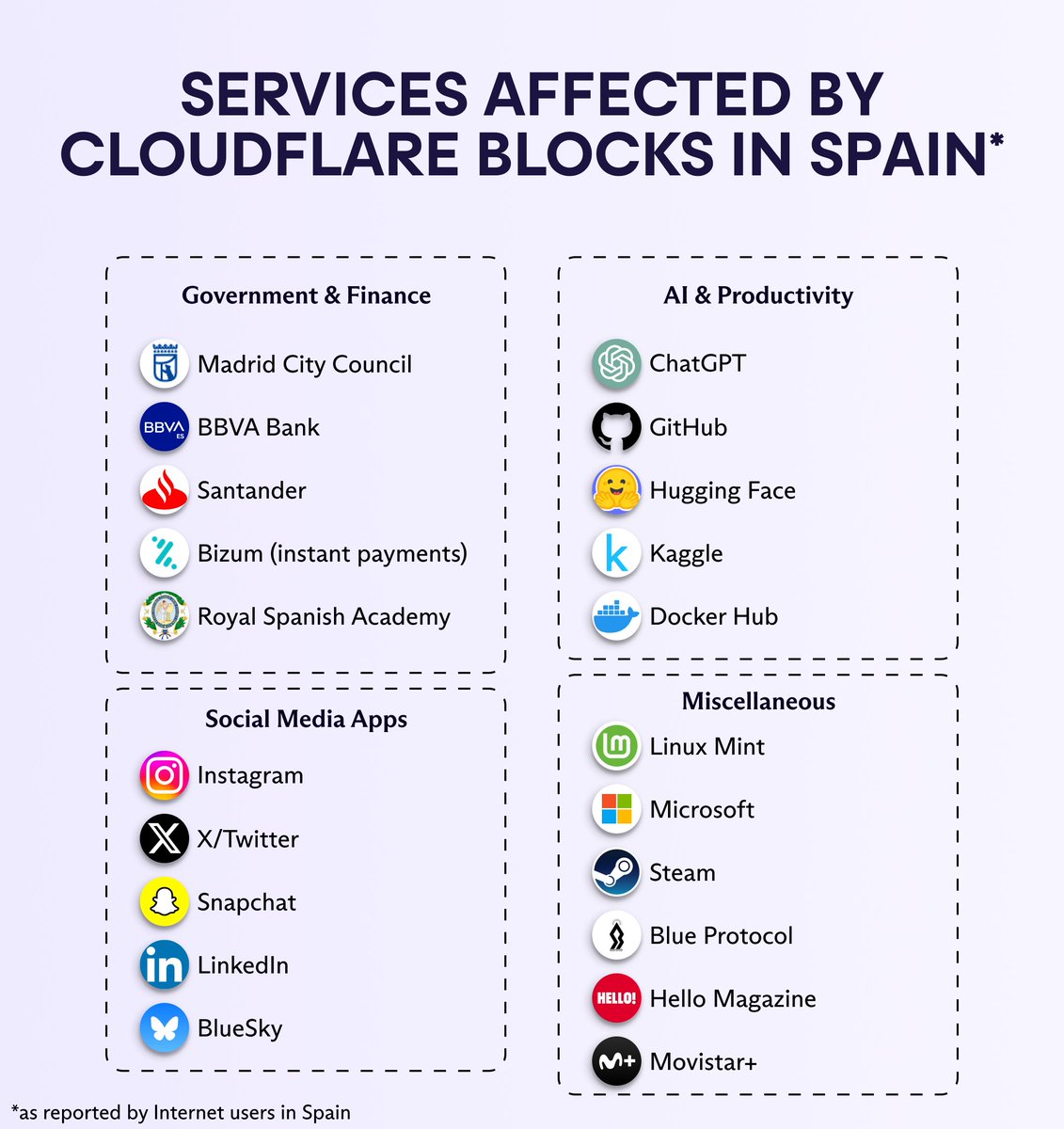
i genuinely think everyone in this space should immediately switch to using Vim. DPRK started abusing VS Code hooks that run _automatically_ in the background when you open a folder. ZERO fucking user interaction required _after_ trusting the repo (the trusting part is important here). Yes, read it again. ZERO. INTERACTION. REQUIRED. so what happens is the following: they (in the usual case the Contagious Interview group, meaning some fake recruiting guy) share GitHub, Bitbucket, and GitLab repos containing a `.vscode/` subdirectory with malicious hooks. the one example I share here executes a fake font that's actually heavily-obfuscated JS and will absolutely rek you. all your fancy software that feels "convenient" makes tradeoffs. those tradeoffs are now being abused to silently rek your devices. use Vim. and use Qubes. Thx.
![[NN2ed] s4ur0n](https://pbs.twimg.com/profile_images/2012464407930900480/5i0P7zfp.jpg)
![[NN2ed] s4ur0n tweet media](https://pbs.twimg.com/media/G9rNAO-X0AAeiRs.jpg)
![[NN2ed] s4ur0n](https://pbs.twimg.com/profile_images/2012464407930900480/5i0P7zfp.jpg)
![[NN2ed] s4ur0n tweet media](https://pbs.twimg.com/media/G82SMbQXYAAdala.jpg)
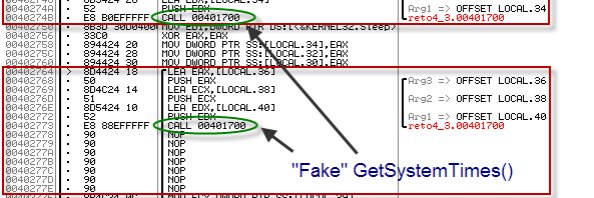
preview: ida-cyberchef #idapro #cyberchef