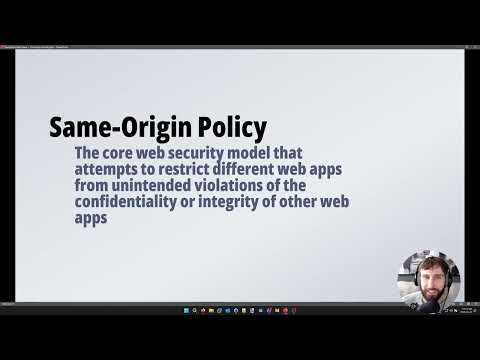
@OreoB1scuit This is a solid series. You may also be interested in my related YouTube series: youtube.com/watch?v=JVNDAe…
YouTube
English
Ryan Armstrong
12.4K posts


@ryarmst
Public health advocate. PhD Biomedical Eng. AppSec professional. Teach @fanshwecollege. AppSec YouTube: https://t.co/S9qqPmSHI0