Satar retweetledi

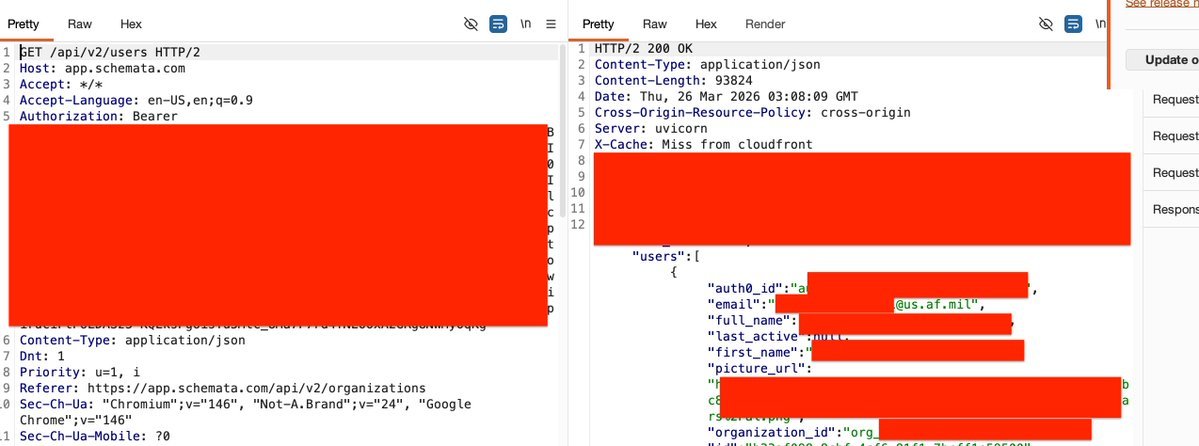
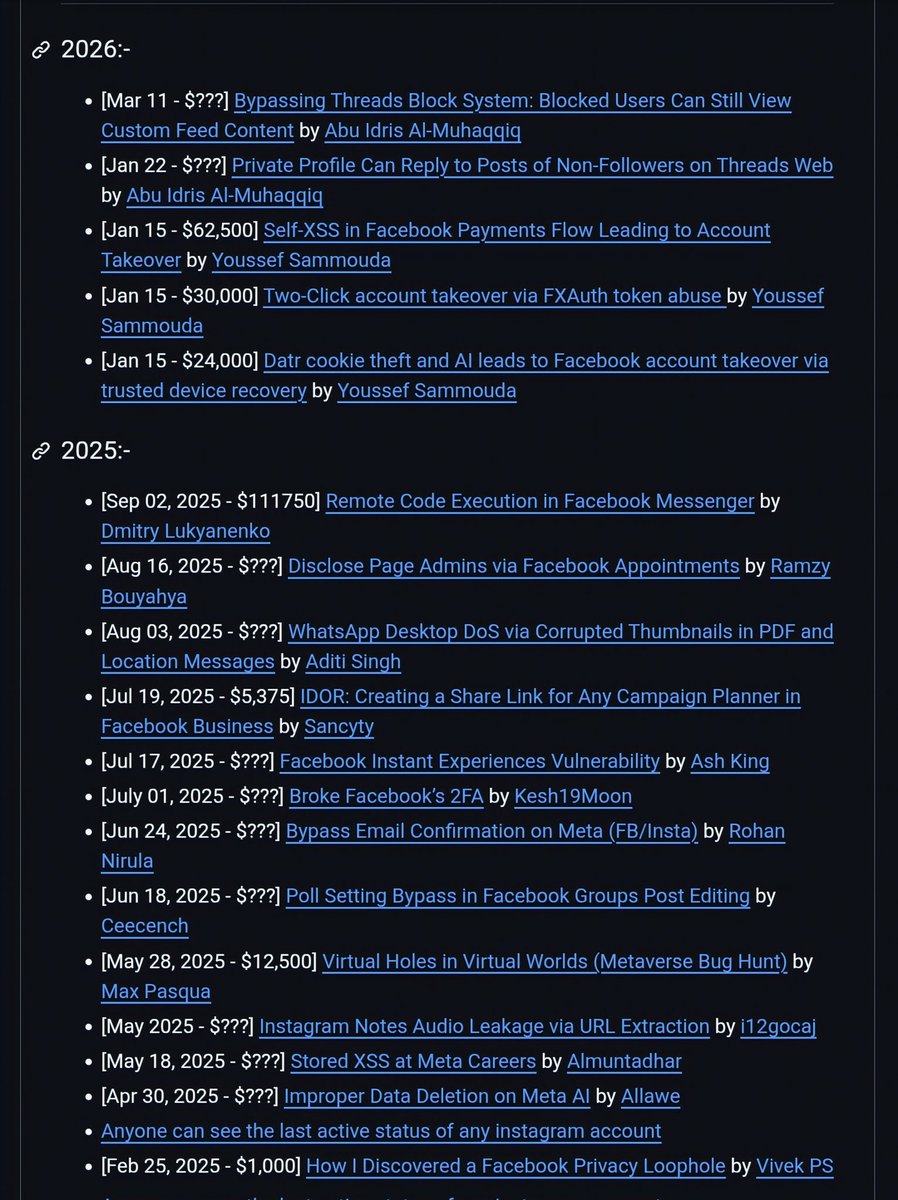
📉 𝐂𝐲𝐛𝐞𝐫 𝐬𝐢𝐠𝐧𝐚𝐥 𝐢𝐬 𝐝𝐫𝐨𝐩𝐩𝐢𝐧𝐠.
📈 𝐀𝐈 𝐧𝐨𝐢𝐬𝐞 𝐢𝐬 𝐫𝐢𝐬𝐢𝐧𝐠.
To help, I created a list of active cybersecurity blogs written by people who still publish real research.
If you follow any of these already (or have gems I should add), let me know.
📌github.com/netbiosX/Cyber…
English