SBOM-Tools
38 posts


SBOM-Tools
@sbom_tools
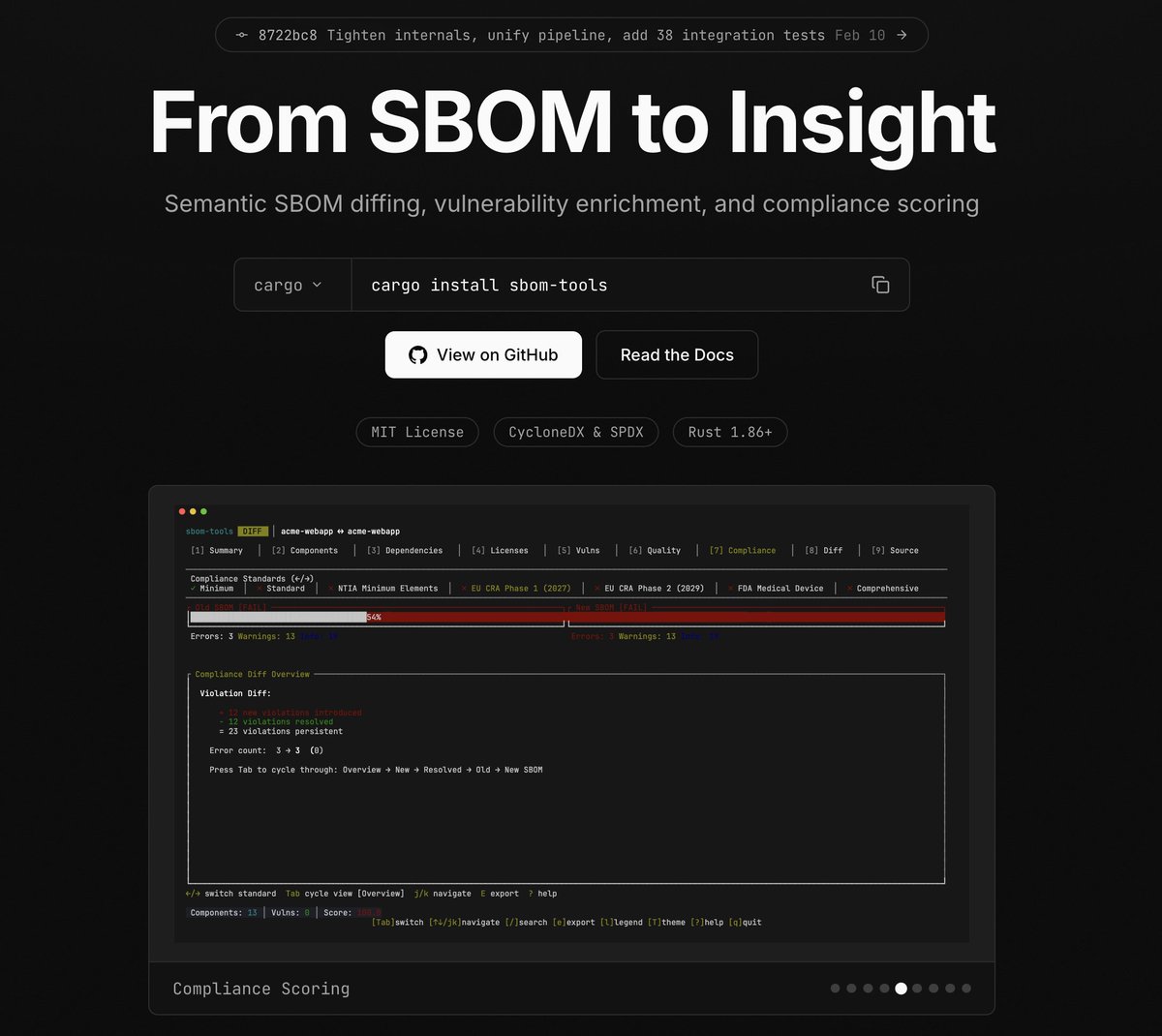
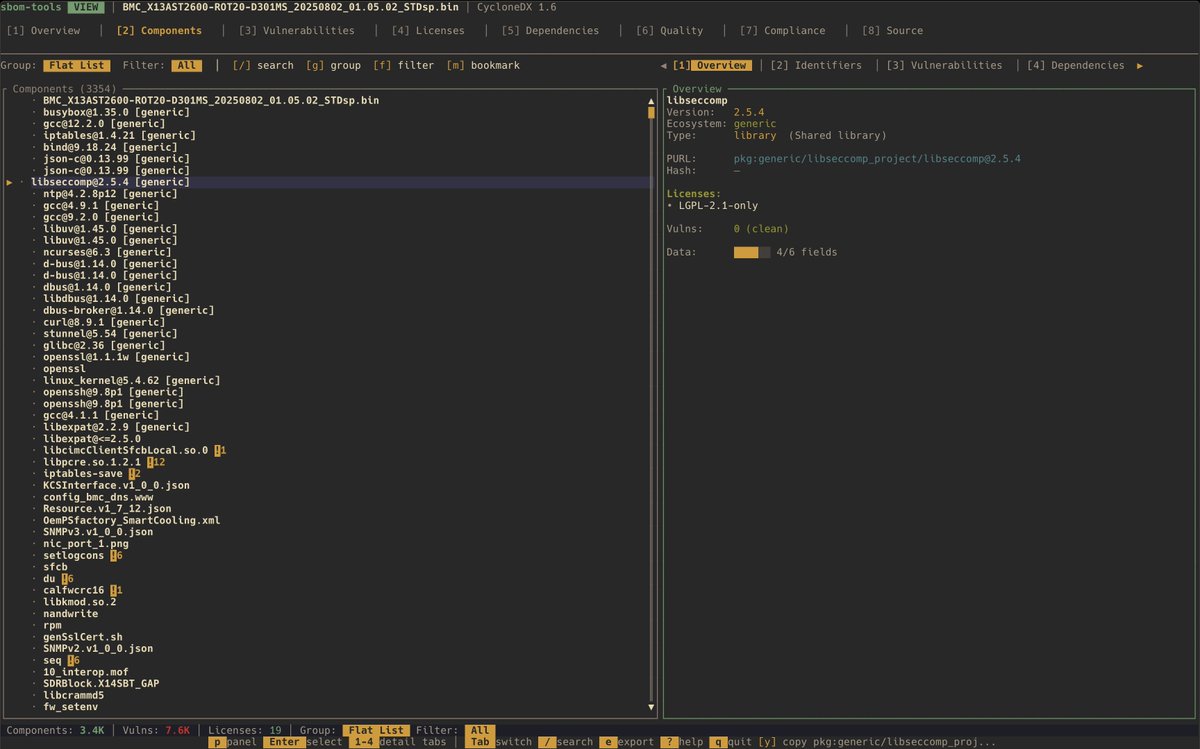
OSS Semantic SBOM diff and TUI analysis tool. Compares CycloneDX/SPDX files to component changes, dependency shifts, license conflicts, and vulnerabilities.


🪄✨Announcing sbom-tools v0.1.16 — open-source SBOM analysis that helps you spot supply chain gaps faster. This release adds broader CycloneDX/SPDX + VEX support, OSV/CISA KEV enrichment, semantic diffing, quality scoring, and compliance checks. Try it: github.com/sbom-tool/sbom…





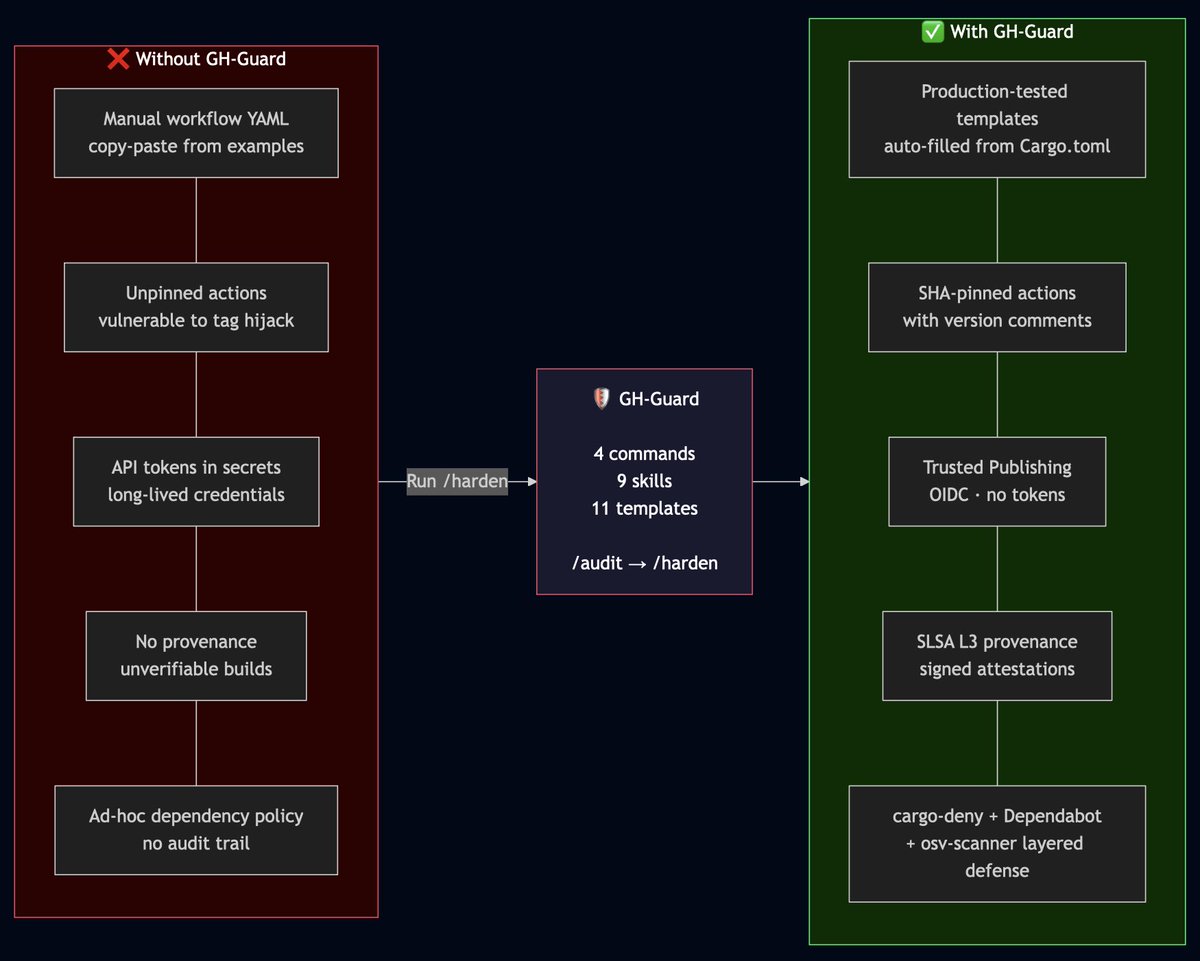
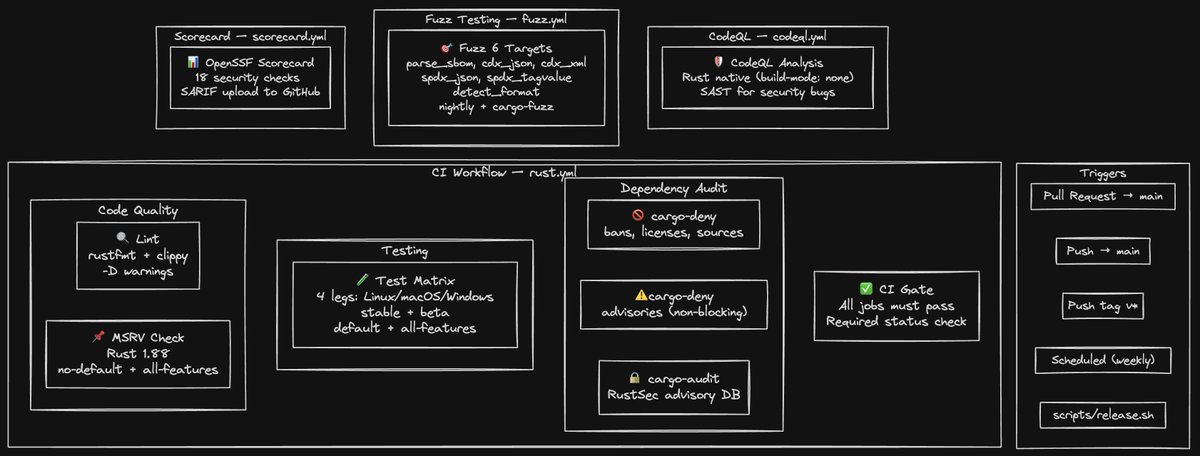
I’m building gh-guard (Claude plugin) because secure OSS release engineering is still way too hard, and recent incidents only confirm that this problem exists at scale. After hardening the release pipeline for @sbom_tools, I realized the same thing keeps happening across open source: maintainers are forced to rebuild the same supply chain security controls from scratch, repo by repo. The problem is not that we don’t know what “good” looks like. The problem is that doing it well is still too manual, too fragmented, and too easy to get wrong. So I built gh-guard — a Claude Code plugin for Rust projects that helps audit and harden CI/CD and release pipelines with secure defaults. It focuses on the following controls: - SHA-pinned GitHub Actions - least-privilege workflow permissions - trusted publishing with OIDC - SLSA provenance - release and tag guardrails - dependency and workflow drift checks github.com/sbom-tool/gh-g…

This year at @REverseConf, we’re dropping something special, a project we’ve been heads-down on for a while that boosts semantic-level binary detection with reachability + taint analysis. Like CodeQL/Semgrep, but for binaries. VulHunt use cases: Vuln REsearch: binarly.io/blog/vulnerabi… Detection Eng: binarly.io/blog/vulhunt-i… VH Intro: binarly.io/blog/vulhunt-i…

I’m building gh-guard (Claude plugin) because secure OSS release engineering is still way too hard, and recent incidents only confirm that this problem exists at scale. After hardening the release pipeline for @sbom_tools, I realized the same thing keeps happening across open source: maintainers are forced to rebuild the same supply chain security controls from scratch, repo by repo. The problem is not that we don’t know what “good” looks like. The problem is that doing it well is still too manual, too fragmented, and too easy to get wrong. So I built gh-guard — a Claude Code plugin for Rust projects that helps audit and harden CI/CD and release pipelines with secure defaults. It focuses on the following controls: - SHA-pinned GitHub Actions - least-privilege workflow permissions - trusted publishing with OIDC - SLSA provenance - release and tag guardrails - dependency and workflow drift checks github.com/sbom-tool/gh-g…






Here is the demo of @sbom_tools by the OG legend @matrosov (IQ 999999)

Legendary @matrosov talks supply chain security, binary analysis, and demo's his new OSS tool @sbom_tools He is one of the authors of Rootkits and Bootkits @REhints and is the founder of @binarly_io youtube.com/watch?v=hzb22T…